- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
ipsec-esp / Protocol 50 invisible in vwire mode ?
- LIVEcommunity
- Discussions
- General Topics
- ipsec-esp / Protocol 50 invisible in vwire mode ?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
ipsec-esp / Protocol 50 invisible in vwire mode ?
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-27-2013 08:01 AM
We have a Vwire configuration with a paloalto (5.0.6) between a third-party router and the wan port.
Security policy is allow any - any for both directions/security zones, log at session start an end.
Everything works (as expected), all VPN Tunnels on the third party device are up and running, but we dont see any ipsec-esp traffic in the traffic monitor, or ACC stats.
If we make a packet capture on the paloalto we do see that the ipsec-esp packets are passing through the vwire.
We already tried du define two additional rules with ipsec as application - but that does not change anything.
Any hints ?
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-29-2013 11:22 AM
Can you paste the o/p of the following commands:-
debug log-receiver statistics
show system logdb-quota
show system disk-space
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-29-2013 11:31 AM
It is possible that the traffic for the ipsec-udp is minimal and the criteria you have set it does not show in that.
Also keep in mind the data is logged at the session end.
Verify that the setting are expanded as per need for Time, sort by and top
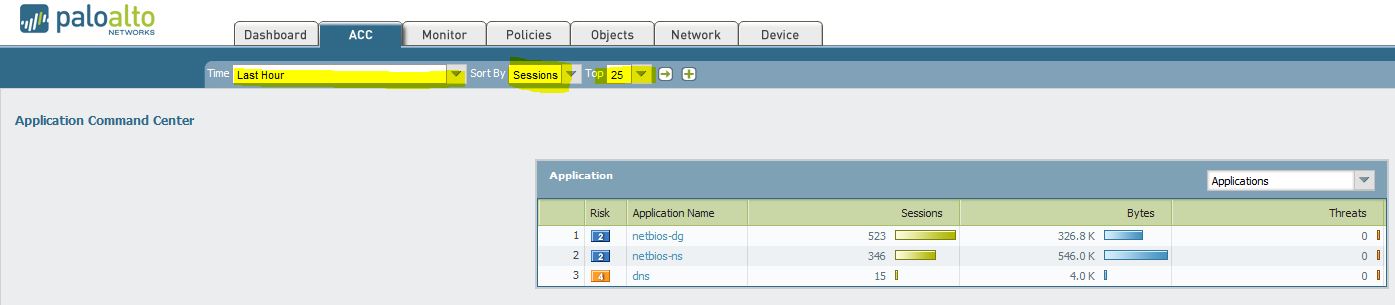
Also anther thing you can do is check in the traffic logs to verify if you have logs for it by using the filter.
You can use following filter ( app eq ipsec-esp-udp ) and ( app eq ipsec-esp )
If nothing shows up here then do it based on the traffic rule e.g ( rule eq rule_name )
If the traffic shows up now. Then verify what is the application it is showing. If it is showing up undecided or the actual applicaiton name.
If it is showing up as actual application name then as mentioned above it is just possible that you have minimal traffic for it and it is just now showing up in ACC tab.
Hope this helps.
Thanks
Numan
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-29-2013 11:13 PM
Perhaps enable logging on session start to check if you see the logs then? When logging on session end, you will only see the log when the session end, so if there are keep alive packets send through the tunnel, you won't see a log.
- 5288 Views
- 5 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- How to make Router BGP ping into IP inside Palo Alto in Next-Generation Firewall Discussions
- PA1420 IKE packet disappear between receive (ingress) and firewall session state in General Topics
- Why do the same Windows Server data collected using XDRC and WEC agents show different statuses in the following fields? in Cortex XSIAM Discussions
- PA-415-5G not working with fresh T-Mobile SIM in General Topics
- GRPC status UNAVAILABLE in intelligent offload in VM-Series in the Private Cloud




