- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
LDAP auth for the WEB UI access clarification
- LIVEcommunity
- Discussions
- General Topics
- Re: LDAP auth for the WEB UI access clarification
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-13-2019 12:20 PM - edited 08-13-2019 12:22 PM
Hi All,
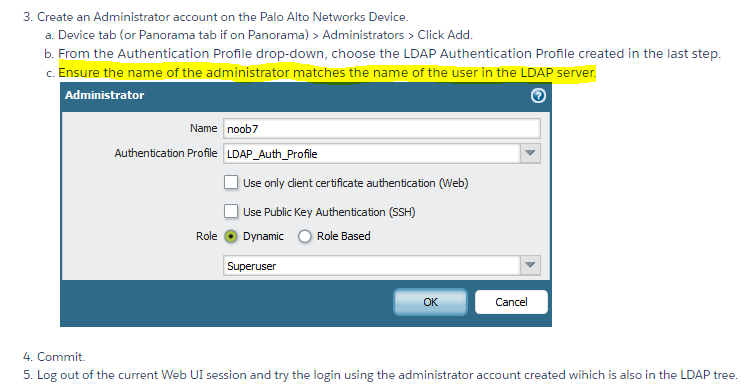
Why do we need step 3 mentioned in the KB below for the WB UI authentication with LDAP?:
https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000ClGuCAK
Why do we need to create a local user? Won't Palo be an LDAP proxy (grabbing username/password and verifying it against LDAP server database)?
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-13-2019 12:37 PM
Its verifying Username(both places), Password, and if you configured a group in your Ldap profile it will do that as well.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-13-2019 12:25 PM
Palo Alto uses a more secure mentality for the Admin users on the firewalls. Calling out the users specificly is a lot more secure they refrenceing an AD group. Anyone with the right AD privlages could modify the AD group and give themselves superuser access to the firewalls.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-13-2019 12:35 PM - edited 08-13-2019 12:37 PM
@Mark_Brook thanks, it makes sense. So what is PA actually verifying, just AD membership group and not username/password?
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-13-2019 12:37 PM
Its verifying Username(both places), Password, and if you configured a group in your Ldap profile it will do that as well.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-13-2019 12:41 PM
Cool, so the local user is another (additional) check as you mentioned earlier. Thanks.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-14-2019 06:54 AM
Palo Alto only has this requirment for LDAP Authentication only when managing the device. You can use a RADIUS server with RADIUS authentication profile to allow management by AD group, and that works fine, so if you have Microsoft IAS, or other RADIUS server, that will work for allowing a group to authenticate to the firewall and/or panorama.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-14-2019 06:58 AM - edited 08-14-2019 06:59 AM
@BrandonWright this now clear as day (but not a typical day in UK 🙂
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-24-2025 12:33 PM
Do you have a reference for this. Why would palo do this only for LDAP? Extremely annoying moving from tacacs to ldap.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-08-2025 05:48 AM
Because LDAP server doesn't send back admin role so you can't do authorization with LDAP server.
- 1 accepted solution
- 9426 Views
- 8 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- GlobalProtect 6.3.3 + Duo SAML MFA loop after normal Windows login (works only via GP Credential Provider at Windows logon) in GlobalProtect Discussions
- HealthCheckServerConfiguration fails with TypeError on XSOAR Cloud v8.13.0 in Cortex XSOAR Discussions
- [SOLVED] Panorama's SAML-Based Administrator Cannot See Other Administrators And Generate TSFs in Panorama Discussions
- PAC Retention and URL Category Priority Behavior in Prisma Access in Strata Cloud Manager
- AI Access Security licensing – concurrent users or named users? in AI Access Security Discussions