- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
New Global Protect 3.0 is not good enough
- LIVEcommunity
- Discussions
- General Topics
- Re: New Global Protect 3.0 is not good enough
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
New Global Protect 3.0 is not good enough
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-06-2016 01:51 PM - edited 04-06-2016 04:21 PM
I was looking forwad to the 'new and improved' Global Protect.
I am still very dissapointed at how it works from a UI standpoint.
When I am connected to the VPN how do I disconnect? Is there a button hiding around in this awful GUI? The only way I know of is to go to the task bar and do it from there. Can anyone please let me know of another way?
Why Am I able to resize the GUI so it's smaller than the minimal size required? It's not a deal breaker but really just signs of shoddy programming.
The user's need 1 button - Connect.
Once the VPN is connected change the button to Disconnect.
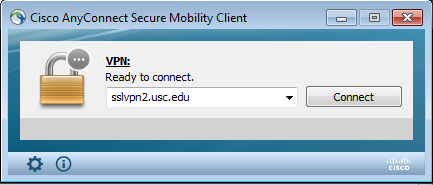
I wish you would hurry up and design it so it's something like Anyconnect:
Here's my post from last year wondering about the same problems, I was hoping that PA engineers were listening but I'm still waiting for a Global Protect application that's as equal quality to the rest of the PA platform.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-27-2016 12:52 PM
GlobalProtect Agent 3.1 is released and incorporates some of the UI functional feedback.
Snippet from the Release Notes ,
Changes to Default Behavior
When you configure the connect method as on‐demand, the options that are available from the
GlobalProtect home panel on Windows and Mac endpoints are now consistent with the options in the
notification area (system tray). GlobalProtect now displays the Connect option until the tunnel is fully
established and, after successfully connecting, displays the option to Disconnect the tunnel. Previously,
you could not toggle between the two options regardless of the connection state. This change does not
apply if the connect method is user‐logon or pre‐logon.
To prevent Windows and Mac users from inadvertently locking their accounts by repeatedly clicking
Connect from the agent home screen (such as when not seeing an immediate response to their request),
after a user initiates a connection request, GlobalProtect now deactivates the button. The button remains
grayed‐out until GlobalProtect establishes the connection or identifies a disconnection or connection
failure (such as a failure to authenticate). If the connection request is unsuccessful or GlobalProtect does
not receive a valid status, the button returns to an active state after 30 seconds. The Rediscover Network
option, which is available from the agent menu in the notification area (system tray), also exhibits the
same behavior.
On Windows and Mac endpoints, the configuration of the Enable Advanced View option now determines
whether the Status and Show Panel options are enabled or disabled (grayed out) in the notification‐area
menu for the agent. When Enable Advanced View is set to Yes, GlobalProtect disables the Status option and
enables the Show Panel option. When Enable Advanced View is set to No, GlobalProtect enables the Status
option and disables the Show Panel option.
When the Show Advanced View option is enabled for Windows and Mac endpoints and a user launches
GlobalProtect from either the Start menu (Windows only) or notification area (system tray), the agent
now always opens to the Home tab. Previously, the agent could open up to a different tab. This change
ensures users always have the same experience every time they launch the app.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-28-2016 11:35 AM
Great, thanks for the update jmenon. It's good to know that the community's voice is being listened to and positive changes are being made. I will test this out shortly.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-30-2016 09:57 AM
Thanks, we are still hoping for a UI graphical uplift, but some of the minor changes and consistency is nice.
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-29-2016 04:35 PM
Is there any way to add the auto reconnect funcationality that anyconnect has. It has happened to me a few times where I have dropped connection on global protect for whatever reason, and the client will still show as connected even though I can no longer reach the remote network. My local network is still ok and can surf the web. The anyconnect client on the other hand will reconnect when this happens, and also recognize when it can no longer reach the remote network. If it happens to me, it will happen to end users.
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-22-2016 11:24 PM
@K12PaloAlto wrote:Is there any way to add the auto reconnect funcationality that anyconnect has. It has happened to me a few times where I have dropped connection on global protect for whatever reason, and the client will still show as connected even though I can no longer reach the remote network. My local network is still ok and can surf the web. The anyconnect client on the other hand will reconnect when this happens, and also recognize when it can no longer reach the remote network. If it happens to me, it will happen to end users.
If you set the connect method to user-logon the client will auto reconnect. if the connect method is set to on-demand the client will not auto reconnect for most part. However if the client is still showing as connected even though it is not you will want to open a support case with us and allow our support engineer to investigate the source of disconnect and wrong status
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-23-2016 07:19 AM
@jmenon I've seen this same issue even with Palo Alto IPSEC site-to-site tunnels and after opening a case with TAC they never actually gave me a firm answer to anything. Just that it was a bug and would be fixed, but I haven't actually seen anything in recent release notes to indicate that the issue was ever addressed.
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-23-2016 05:31 PM
@jmenon wrote:
@K12PaloAlto wrote:Is there any way to add the auto reconnect funcationality that anyconnect has. It has happened to me a few times where I have dropped connection on global protect for whatever reason, and the client will still show as connected even though I can no longer reach the remote network. My local network is still ok and can surf the web. The anyconnect client on the other hand will reconnect when this happens, and also recognize when it can no longer reach the remote network. If it happens to me, it will happen to end users.
If you set the connect method to user-logon the client will auto reconnect. if the connect method is set to on-demand the client will not auto reconnect for most part. However if the client is still showing as connected even though it is not you will want to open a support case with us and allow our support engineer to investigate the source of disconnect and wrong status
I am using the on-demand option for connection with split tunnel. I was not able to replicate a local wireless disconnect without the new client (3.1.0) detecting it. That said, there still seems to be an issue if drops are occuring after the laptop. I simulated a AP failure where another AP picked up connection. GP client still showed connected during this time. I am able to ping local router, but unable to ping over VPN tunnel. The first time it did not recover, and I disconnected and reconnected. The second time I tested runing a constant ping of a destination over the VPN, and it did recover. YMMV I used the AP's as an example to introduce slight packet loss. When users are connecting from residential internet connections... I need something reliable and easy for the end user.
A quick search on google found this page from a university. (not affiliated)
http://www.northeastern.edu/its/howto/globalprotect-windows-issues/
"Sometimes on Windows, a dropped network connection will not fully disconnect the GlobalProtect client – the client will keep trying to connect without success, even once the network connection is back."
@jmenon This VPN client is the one thing holding me back from decommissioning our ASA. If we can get the client where it is at least equivalent to Anyconnect, I will be a happy camper. If there is an avenue that would be better for me to offer suggestions, please let me know.
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-27-2016 07:54 AM
@K12PaloAlto personally we chose to continue to use the ASA simply as a VPN gateway and moved all firewall functions over the the Palo Alto. If you already have the equipment maintaining the AnyConnect license (if it isn't perpetual) is very cheap to do; and if your ASA is only going to provide VPN then you can get away with a much smaller unit.
The GlobalProtect client for most of our users was 'good enough', however those that did complain brought up valid reasons to continue to use AnyConnect.
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-27-2016 02:18 PM
@BPry wrote:@K12PaloAlto personally we chose to continue to use the ASA simply as a VPN gateway and moved all firewall functions over the the Palo Alto. If you already have the equipment maintaining the AnyConnect license (if it isn't perpetual) is very cheap to do; and if your ASA is only going to provide VPN then you can get away with a much smaller unit.
The GlobalProtect client for most of our users was 'good enough', however those that did complain brought up valid reasons to continue to use AnyConnect.
@BPry Thank you for your comment. We are also using a similar approach currently, but I guess I'm just disapointed that we have to entertain that option for reliable VPN.
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-27-2016 02:21 PM
We are in the same boat, we moved from ASA to GP, but I wish I made a stand to stick with AnyConnect. Our ASAs are aging, would have to justify buying new ones, but I could probably argue it and use their new 4.x client which is waves ahead of GlobalProtect.
If and when the user population complains more and some function or feature isnt there that Anyconnect has, we'll switch back.
Palo Alto also doesn't support VPN Phones such as Avaya, cisco of course does. Fantastic isnt it?
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-27-2016 02:21 PM
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-29-2016 09:37 PM
If you have on-demand connect method with GlobalProtect and have encountered issues with the app not being resillient , for e.g.
1. Does not detect VPN disconnects fast enough and continue to think its connected
2. Drops connection when there is temproray network glitches
then please unicast me or reach out to your palo alto networks account team or support so that we can better understand the concerns/requirements to evaluate future enhancements.
- 33418 Views
- 41 replies
- 14 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- CVE-2026-0261 PAN-OS_ Authenticated Admin Command Injection Vulnerability in Next-Generation Firewall Discussions
- Cortex XDR Uninstallation in General Topics
- Global Protect MFA login using smtp in General Topics
- Purpose of .prod.reporting.paloaltonetworks.com in Strata Cloud Manager in Strata Cloud Manager
- Need a similar setting of Global Protect in Prisma Access Agent in Prisma Access Agent Discussions