- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Newbie setting up URL Filtering... can't find an answer by searching.. :-/
- LIVEcommunity
- Discussions
- General Topics
- Newbie setting up URL Filtering... can't find an answer by searching.. :-/
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-30-2013 08:06 AM
Hi all --
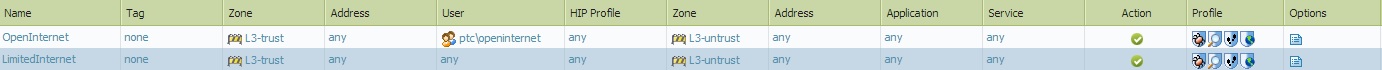
So I was asked by mgmt to block social networking, streaming, etc for all users except administration. I created a custom URL Filtering profile that blocks those categories, as well as several specific sites. Under Policies -> Security, I created a new policy called "LimitedInternet", applied to all users, from the trust to untrust zones, and applied the custom, limited URL Filter. I have another security policy that is only applied to users in our domain's OpenInternet group, which uses the default URL Filter profile. Here's how it looks --
As I understand, the rules are applied top-down, and once a rule matches, it stops searching. So the first rule should apply to anyone in the OpenInternet group; if the user is not in that group, they should use the second, limited rule and have sites blocked. As it is, the LimitedInternet rule is applied to everyone, regardless of their group membership.
Can anyone tell me what I'm missing here? (I apologize if this has been covered elsewhere, I tried searching, honest!)
Thanks -- michael~
- Labels:
-
Configuration
-
Management
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-30-2013 08:21 AM
Hello thatguy,
For the requirement, 1> allowing certain admin users for all categories and sites 2> Block some social categories and some sites for the rest of the users.
The security rules configured and approach is perfect. Group of users are selected in the first rule and they are being allowed for all sites. It is not mentioned here that what URL profile is configured for the first rule ?
Areas to look:
> In the Url filtering logs ( Monitor > Url logs ) pls look for the logs and filter them for what you are looking. If certain users are supposed to be allowed and not allowed to pass traffic or so on select the parameters to be added in filter and we can narrow down the results.
Now click on the magnified icon on the left of each log line to see more details such as security rule, session id, category and so on to understand which rule is taking into effect and there by which url profile.
If you can update us what is the exact issue I can share more details here.
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-30-2013 08:21 AM
Hello thatguy,
For the requirement, 1> allowing certain admin users for all categories and sites 2> Block some social categories and some sites for the rest of the users.
The security rules configured and approach is perfect. Group of users are selected in the first rule and they are being allowed for all sites. It is not mentioned here that what URL profile is configured for the first rule ?
Areas to look:
> In the Url filtering logs ( Monitor > Url logs ) pls look for the logs and filter them for what you are looking. If certain users are supposed to be allowed and not allowed to pass traffic or so on select the parameters to be added in filter and we can narrow down the results.
Now click on the magnified icon on the left of each log line to see more details such as security rule, session id, category and so on to understand which rule is taking into effect and there by which url profile.
If you can update us what is the exact issue I can share more details here.
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-30-2013 08:44 AM
Thank you Phoenix --
I checked the logs and, indeed, the LimitedInternet security rule is being applied to everyone.
From my original image, the OpenInternet rule should apply only to users in the ptc\OpenInternet domain group, and has the default URL filtering profile attached. The second rule applies to all other users, and has the LimitedInternet URL filtering profile attached..
The logs show every user is getting blocked by the LimitedInternet rule.
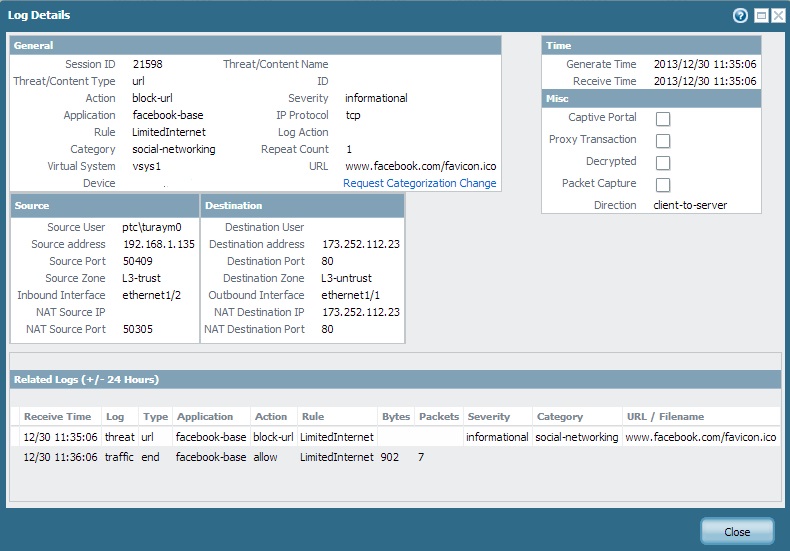
Does that tell anything? Thanks again for the reply.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-30-2013 09:28 AM
Hello,
Good we narrowed the issue. So this points me to the point that in the rule 1 ( Open internet ) we have the User group defined. If for some reason the device is not knowing the users in this group or so it would not take the rule into effect. Now this would direct us towards user identification troubleshooting.
> To see users in the group list:
show user group name "Group name"
> To find the groups
show user group list
> To see if the user is part of the group, // Use this command to find the user mapping and the group.
show user ip-user-mapping ip <>
If these are not showing the results right, may be need a troubleshooting call to narrow down the issue.
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-30-2013 09:36 AM
Is the group mapping being configured in user Identification set up ? It is required to pull down the group members from the Ldap and have the mapping between the group and the members of the group . Following link has the document on how to configure group mapping https://live.paloaltonetworks.com/docs/DOC-4994
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-30-2013 10:42 AM
GOT IT!!!
It turns out that I originally misconfigured the LDAP settings.. In the LDAP Server Profile, I had our domain as "ptc.loc" instead of simply "ptc", so the users in the group-mapping were listed as "ptc.loc\username", while the user-mapping listed the users as "ptc\username", so they didn't match up.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-02-2014 08:26 PM
You should consider using "application filters" instead of URL filtering. Social Networking sites is a great example.
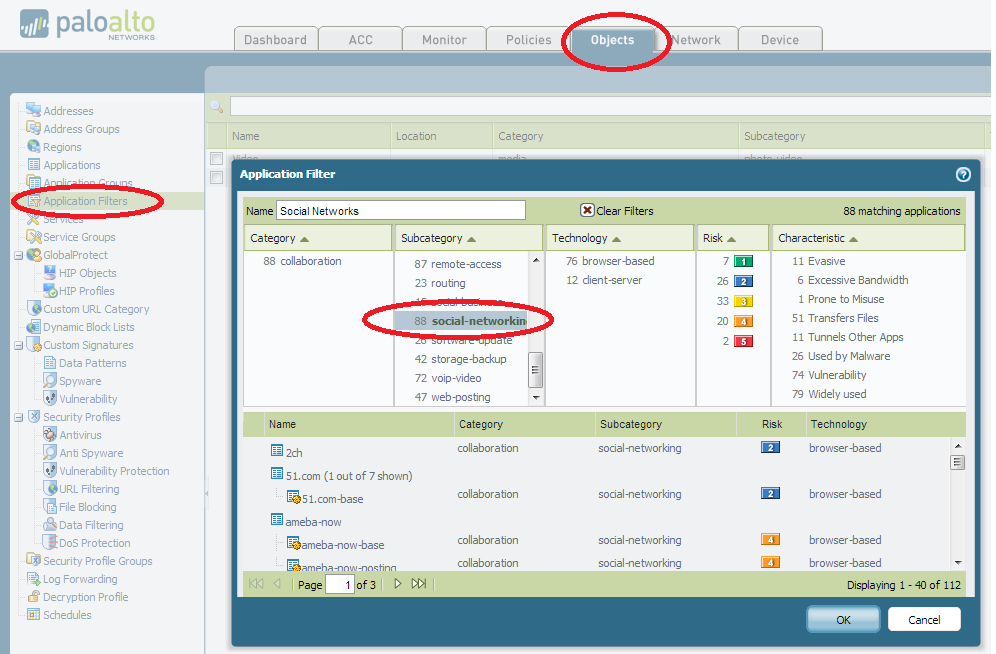
Creating this one App Filter Object named Social Networks, and selecting the subcategory of "social-networking" gives me an object with 88 applications included. If I selected "browser based" as well, the number would reduce to 76 applications. Now I can use this in a security rule to deny or allow sites. The beauty of this is that in a year there may be one or two new sites that pop up and become popular. As soon as they are detected by Paloalto and added to the database, your existing rule will already be in place and include the new sites based on the subcategory.
SKrall
- 1 accepted solution
- 5264 Views
- 6 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Need help on this XSOAR Weird behavior on preprocessing scripts in Cortex XSOAR Discussions
- PA-415-5G not working with fresh T-Mobile SIM in General Topics
- Not able to log XFF (Actual Client IP) in PaloAlto Logs even when we enable XFF and URL filtering profile in Palo's in Next-Generation Firewall Discussions
- When will the Legacy URL Filtering license be transitioned to the A-URL license? in Advanced URL Filtering Discussions
- Newsletter: Cloud Delivered Security Services, Oct-2025 in Advanced Threat Prevention Discussions