- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
several IKE Crypto Profiles on the same interface for SITE-to-SITE VPN
- LIVEcommunity
- Discussions
- General Topics
- Re: several IKE Crypto Profiles on the same interface for SITE-to-SITE VPN
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
several IKE Crypto Profiles on the same interface for SITE-to-SITE VPN
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-29-2018 02:56 AM
Hello dear colleagues,
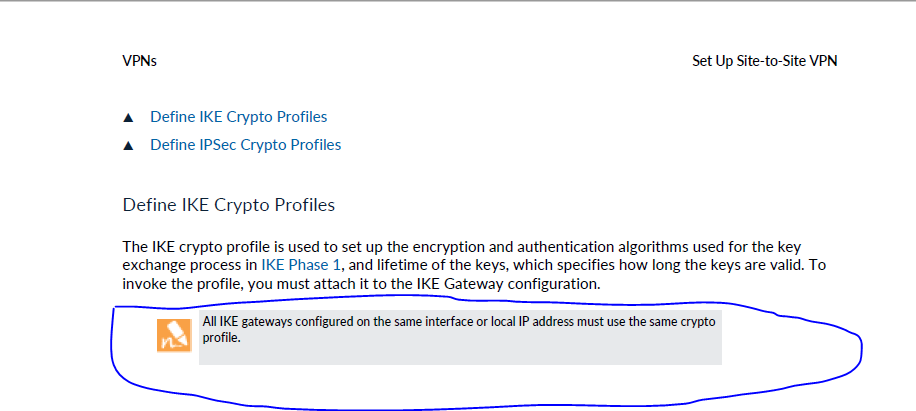
according to the documentation, there is a limitation for IKE gateways:
All IKE gateways configured on the same interface or local IP address must use the same crypto
profile. (c)
The same restriction is mentioned in the PANOS v8.1 course.
First of all, it seems strange that we cannot use different IKE options for different peers. Second, I use different IKE Crypto Profiles for different IKE gateways on the same public interface without any problem. I can see that they do use different algorithms for encrypting, hashing, DH group, etc. So it works.
Is it some obsolete information they just forgot to remove?
Regards,
Vladimir Stepanov
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-29-2018 06:38 AM
Can you point out where it is in documentation?
You can definitely use diferent crypto profiles on same interface in diferent IKE gateways.
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-29-2018 06:56 AM
As @Raido_Rattameister mentioned this is either poorly worded or simply not correct. You can only assign one profile per IKE gateway (obviously), but as long as you use a different IKE gateway you can have multiple profiles assigned regardless of them sharing the same physical interface.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-29-2018 07:35 AM - edited 11-29-2018 07:38 AM
At first I have seen it in the paloalto online course for Pan-OS 8.1, module about Site-to-Site VPN, IKE Gateway configuration. After I started to search and found the same in the PAN-OS Admin Guide 8.0 - Page 691
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-29-2018 02:25 PM
???
I have never seen or heard of this note and since 5.0 I use different profiles for the ike gateways ... also with 8.0
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-29-2018 11:04 PM
Definitelly a mistake. This would make firewall practically useless for VPNs.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-30-2018 01:43 AM
Ok, thanks everybody, I am going to report them about this mistake. Just strange that this is mentioned in several sources.
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-10-2020 08:54 AM
Also on 9.1. Admin Guide site 907.
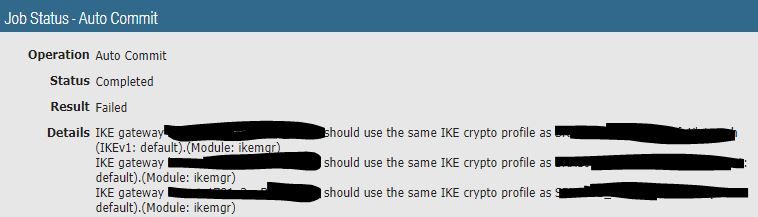
After Upgrading from working 9.0.8 with multiple IKE crypto profiles on same Interface / IP I got an auto commit error.
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-12-2020 08:07 PM
Are your peers configured with dynamic IPs?
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-12-2020 10:41 PM
Yes, my peers configured with dynamic IP's
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-13-2020 05:55 AM
From 9.1 you can't commit unless all dynamic peers have same crypto profile.
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-13-2020 07:11 AM
Sounds like a bad joke. This is an irony that would be funny were it not so tragic.
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-19-2020 11:07 PM
Yes, that sounds like a step backwards in 9.1. What is the logic behind this?
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-22-2020 03:04 AM
Is it mentioned somewhere in the release notes? I didn't found it, so I am afraid that they just broken it occasionally.
It is sad, the paloalto is becoming a really **bleep** product. The support is awful, it needs to explain to support engineers how things should work. During one of my last discussions, I have spent four hours proving with references to the documentation and with tests in the lab I created especially for this. And this ticket is still on the engineering side for 8 months without any estimate.
Another problem unresolved for more than three months and the only feedback is that they may be fix it in 9.0.11, but for now there is even no estimation date for 9.0.10.
GeoIP is not reliable and there is no easy procedure on how to fix errors there, the support proposes to rollback the content database to the old that was a week ago, or just wait, "maybe it will be fixed in some future update".
External dynamic lists from the PaloAlto are abandoned before there were thousands of malicious IPs, not just hundreds.
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-22-2020 04:47 AM
I have had the exact same experience.
And the GeoIP bug hits also the fqdn-Objects. For this bug support needed 12d to find out and publish to me.
- 17487 Views
- 16 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- pa-450 issues and going down 2 days in a row in General Topics
- Cortex XDR triggers Code 10 on USB Audio despite exception - Vendor not selectable, need per-device allow without vendor or something in Cortex XDR Discussions
- Palo Alto QOS configuration question in Next-Generation Firewall Discussions
- Allow OpenVPN while not allowing access to local network in GlobalProtect Discussions
- Planned Migration from PA-820 to PA-445 Firewall in Next-Generation Firewall Discussions