- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Skype manager custom application
- LIVEcommunity
- Discussions
- General Topics
- Skype manager custom application
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Skype manager custom application
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-23-2014 12:29 AM
Hello,
I'm actually blocking skype application but I would like to allow skype manager web site (https://manager.skype.com/).
The web site manager.skype.com is blocked because recognized as skype application.
The idea is to build a application that allow skype with hostname https://manager.skype.com/
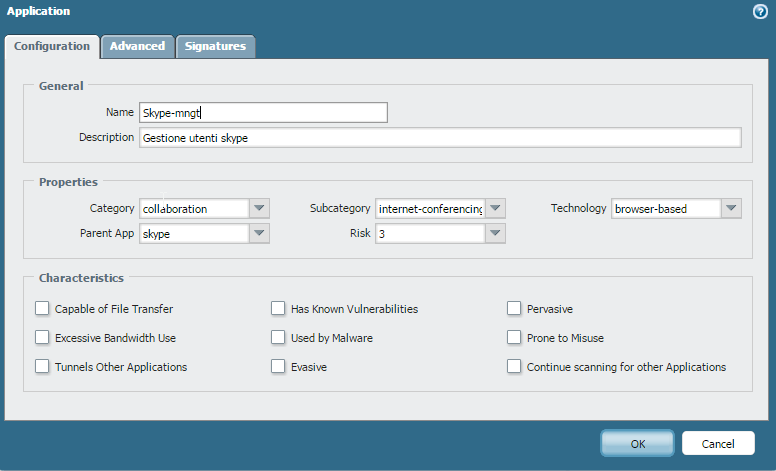
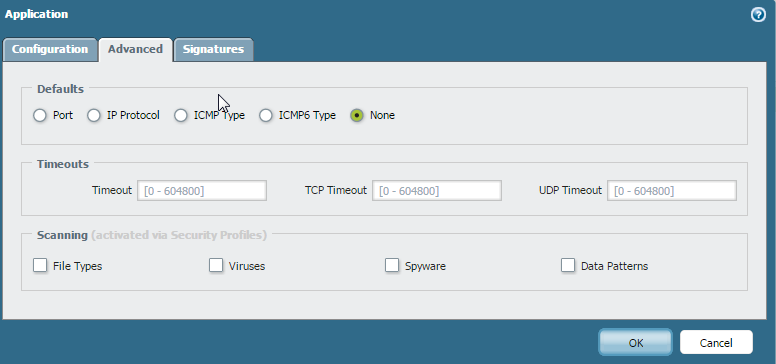
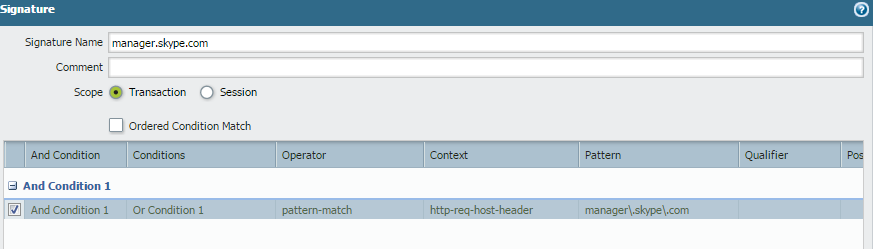
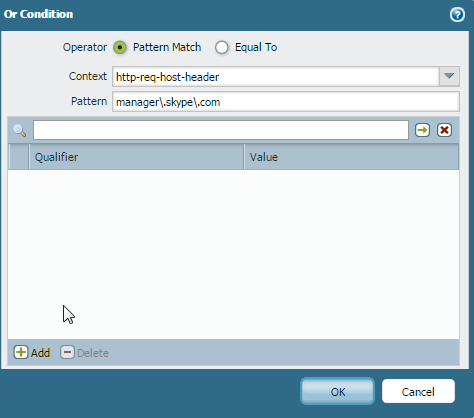
The custom app I created is here below but it doesn't work, any idea why ? where I'm wrong ?
- Labels:
-
App-ID
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-23-2014 02:51 AM
Hi Helenio,
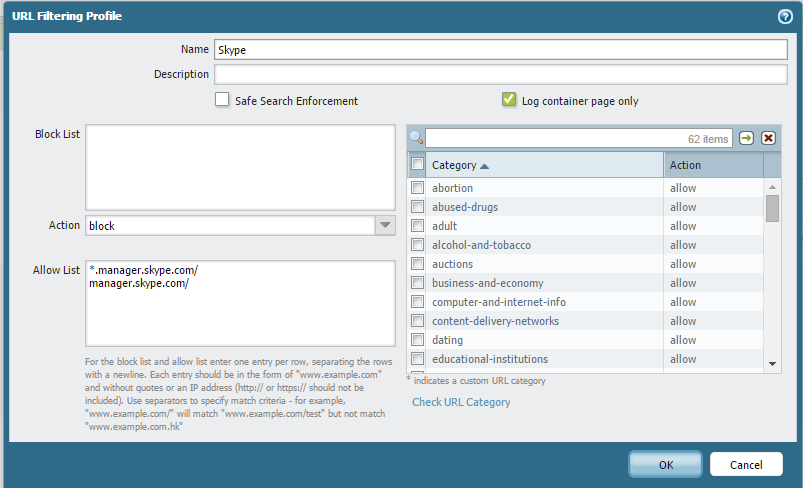
Easier thing would be to create one policy on the top of skype block, and while list manager.skype.com. Let me know if that helps.
Please refer following URL Profile for the same.
Regards,
Hardik Shah
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-23-2014 03:41 AM
Hi Helenio,
The best way to achiaive the goal through URL filtering profiles, instead of creating a custom application signature. Since this is an HTTPS connection. SSL traffic will be encrypted and the PAN firewall will not be able to identify the actual URL, instead it will categorize traffic ( URL) based on it's certificate common name. For the mentioned URL :https://manager.skype.com/ the certificate common name is "login.skype.com".
I have tested below the mentioned filtering profile on my PAN firewall and it seems to be working fine. ( you may fine tuned it)
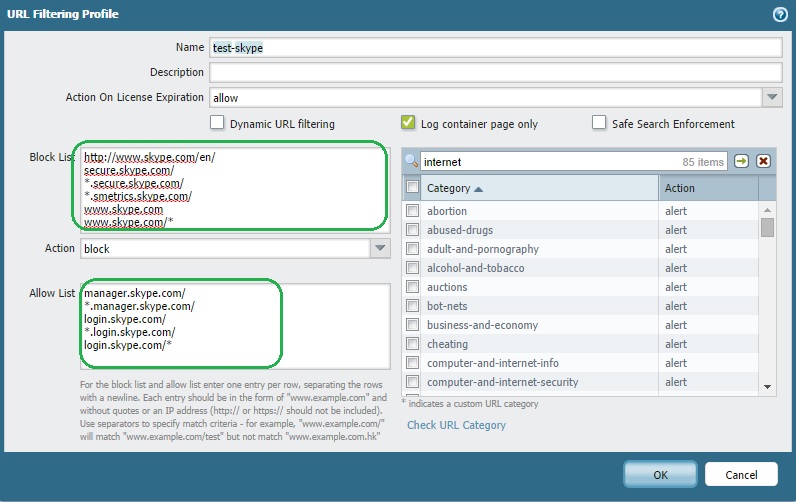
A related doc for your reference: Controlling Skype
Hope this helps.
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-23-2014 05:02 PM
Hello,
Please try below suggestion for custom application to allow manager skype
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-23-2014 05:33 PM
Hi Helenio,
I tried in lab, it seems manager.skype.paloaltonetworks.com depends on url apps.skypeassets.com.
Its not just one URL, its calling info from other URL. May be thats creating problem.
Regards,
Hardik Shah
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-23-2014 11:10 PM
I can't work with URL profiles because I have a top rule with application skype blocked and rule with URL profile are below this rule.
I have to bypass skype application detection before the rule that block skype application therefore I have to bypass the skype application detection with a rule on top of it with a matching and not a policy.
The only way in may case is custom application. I tried suggestion from hyadavalli but i didn't manage to work.
There is some detailed guide how to build custom application ?
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-23-2014 11:18 PM
Below mentioned document will help you to build custom application signature: Custom Application Signatures
Related DOC: Creating Custom Application Signatures
Hope this helps.
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-24-2014 12:45 AM
Using a custom signature to override the application identification performed by the firewall is limited to when the traffic is identified as only a base application which has a decoder.
Some examples of base applications with decoders:
web-browsing (http context)
ssl
ftp
dns
smtp
.. and others..
You can find the decoder list current as of content 424 in the Custom Application Signaturesdocument on page 7.
What this means in practice is that a session which is identified as one of the apps listed above can utilize custom signatures to further identify the traffic. In your case, once the firewall identifies the application as skype there is no decoder being utilized on the session, so custom signatures would not be applied. The custom signature can not override the built-in signatures for other applications which only have a dependency on one of these base apps (skype has a dependency on ssl).
Like others have mentioned, I believe your only option is to utilize URL filtering to not apply the skype block when the URL matches "manager.skype.com", or explicitly allow any traffic to that URL.
- 6433 Views
- 7 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- host-insights apps refresh in Cortex XDR Discussions
- Address Group and Tag limitations in General Topics
- Get Application Tags via API in Strata Cloud Manager
- New articles about how to create signatures without or with AI (ChatGPT/OpenAI) in Custom Signatures
- Global Protect Blank Screen on Windows 11 in GlobalProtect Discussions




