- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
SSL Decryption - Firefox error: "sec_error_reused_issuer_and_serial"
- LIVEcommunity
- Discussions
- General Topics
- Re: SSL Decryption - Firefox error: "sec_error_reused_issuer_and_serial"
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
SSL Decryption - Firefox error: "sec_error_reused_issuer_and_serial"
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-23-2014 10:42 PM
After turning on the SSL-Decryption, firefox tells me every moring after restart this error "sec_error_reused_issuer_and_serial", after deleleting the whole history and a restart of firefox it works, but that workaround every morning couldn't be the solution.
Anybody some suggestions??
thx
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-24-2014 12:54 AM
Hi,
when you get this message? when open any https websites or open the PA-WebGui?
if you get it with any https websites, please check the Trusted and Untrusted Certificates. Take a look:
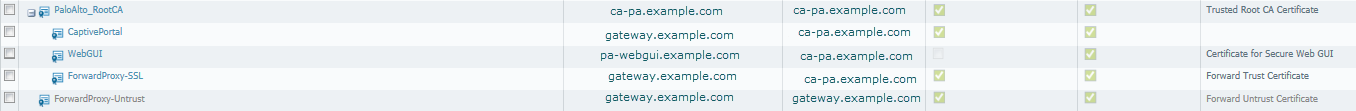
The Certificates are generated all from PA.
gateway.example.com = DNS entry with the IP of your internet breakout at your PA
pa-webgui.example.com = DNS entry with the IP of your MGT from your PA
Export the RootCA certificate and import it in your firefox. And if you having more PAs with the same RootCA and WebGui certificates generated from you will always get the problem with FF when opening the WebGui. Try Chrome or IE.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-24-2014 04:06 AM
Hi Hithead,
i had only one certificate for all purposes signed as a Subordinate-CA from my Organisation-CA??? IE has no problems with that, only FF.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-24-2014 04:46 AM
hi,
FF has a problem with it. FF call it a "security feature" and IE ignore the usage of the same CA on different sites. Difficult to explain.
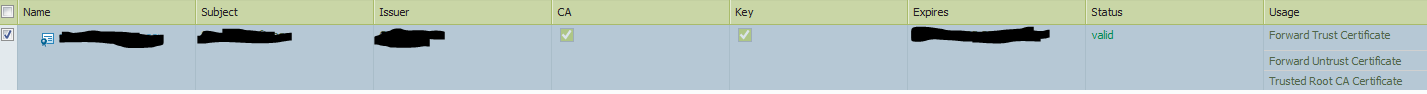
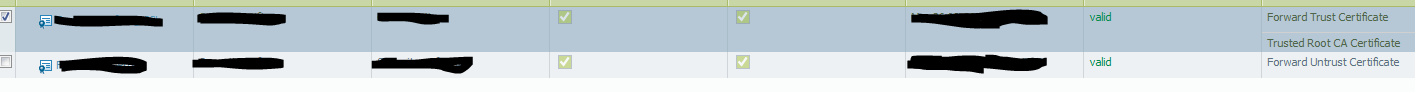
But by the way: Do not use a trusted certificate with the option "forward trusted certificate". If a page is recognized as untrusted by the PA, the user will not be promoted with a certificate error. It will trust it. Generate a new certificate with PA, with the same values but do not choose an issuer (signed by) and select the usage "untrusted Certificate" for it.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-24-2014 05:22 AM
"Do not use a trusted certificate with the option "forward trusted certificate".
Sorry I didn't really understand.
You mean "Do not use a trusted certificate with the option "forward untrusted certificate"?
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-24-2014 05:40 AM
oh, you are right 😃
I mean untrusted ![]()
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-24-2014 07:02 AM
Okay :smileygrin:. I have tested it and it looks good with the untrusted certificates.
And for the "security feature" in FF, i will look for a workaround ![]() .
.
But I have one more question: Do you mean it's useful to work with OCSP-Responder or CRL-Lists? Any Ideas or best practice, because there are different meanings about that?

- Mark as New
- Subscribe to RSS Feed
- Permalink
04-25-2014 01:16 AM
we don't activated that, because of a bug. But we will enable it soon again (with 6.0.2). Only crl . After enable it, you have to check the system logs, if your PA can download the crl .
BTW: read this https://live.paloaltonetworks.com/thread/8984
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-25-2014 01:31 AM
This has been fixed in 6.0.2 which has been released yesterday.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-28-2014 01:49 AM
hi again,
okay i will test the OCSP with the new PAN-OS Version soon, but now I have another problem with the selfsigned certificate for the untrusted Certificates, because I get many certificate errors because the most intermediate CA's are not in the default trusted certificate list on the PA.
So what is the best way to solve the problem. It seems to be a little bit difficult to import all possible certificates for the Sub-CA's??
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-09-2014 06:53 AM
hi,
check your system and traffic logs (traffic logs from your MGT IP of PA). may you will find the some information what cannot be downloaded. Allow your PA to download the resources.
- 7795 Views
- 10 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Multi-VSYS 11.2.8 - How to assign a dedicated Forward Trust Certificate per VSYS for SSL Decryption in Next-Generation Firewall Discussions
- Foward Trust Cert and MacBook Pro in General Topics
- Strata Cloud Manager does not display devices with Firefox in Strata Cloud Manager
- Restrict access via GlobalProtect to permit access to only a specific Google Drive Account/Folder in GlobalProtect Discussions
- Decryption policies and Short-Lived Certificates in Next-Generation Firewall Discussions




