- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
unable to block exe files after using File blocking Profile
- LIVEcommunity
- Discussions
- General Topics
- Re: unable to block exe files after using File blocking Profile
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-07-2020 03:48 AM
I have followed https://docs.paloaltonetworks.com/pan-os/8-1/pan-os-admin/threat-prevention/set-up-file-blocking and created a file blocking profile to block Downloads of exe format while browsing. But it still does not block the exe downloads on the server i applied the file blocking profile.
Please check and suggest the fix.
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-07-2020 10:31 PM - edited 10-07-2020 10:37 PM
Hi
All of the items in the Objects tab do not have any affect on traffic if they are not attached to Policies. This includes Decryption Profile/s.
1. So - the File Blocking (FB) Profile must be attached to a security rule.
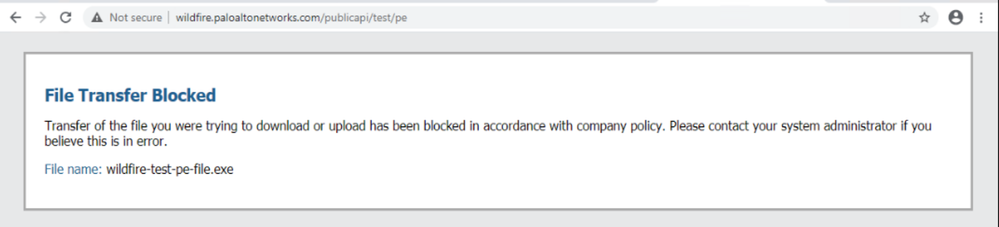
2. I highly recommend splitting your issue into two parts, get FB working then tackle Decryption. For FB I would recommend you try to download this test file from Palo Alto as it uses the HTTP protocol hence no need for decryption, yet.
http://wildfire.paloaltonetworks.com/publicapi/test/pe
(This is an anti-virus test file, it will probably get blocked by AV software but it does not matter as all we want is for it to download or get blocked by the filewall)
If you see it blocked and logged under Monitor-> Data Filtering - it means FB is working for non-encrypted traffic. Continue to enable Decryption:
3. For Decryption you really should read the above mentioned articles and notes by @BPry as enabling it requires:
3a. Generating Decryption Certificates on the firewall, self-signed for testing or Corporate CA signed (much preferred)
3b. Having them in all computers, trusted root certificate store
3c. Creating a Decryption Policy under Policies->Decryption: for testing start with:
Source Zone Internal (or whatever you named it)
Dest Zone External (or whatever you named it)
Service: service_http + service_https
Action: Decrypt
Type: SSL Forward Proxy
Decryption Profile: is optional
3d. In some older PANOS versions you must also allow in Security rules Application=web-browsing & service=service_https (this is not the default, hence needs adding).
* This might look like easy 4 steps but trust me - it isn't.
Lastly, log into the learning center at:
http://education.paloaltonetworks.com/learningcenter
Search for EDU-110, register for it for free and start watching this online training about the NGFW, but note that the training center is being moved you might be redirected to the new training site in a few days.
Shai
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-07-2020 04:19 AM
Hi
Here are a few tips I hope will help:
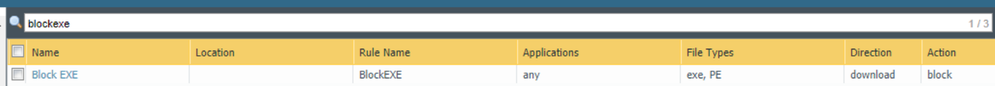
1. In the blocking profile put EXE & PE together (portable-executable), direction=download, action=block, application=any (test then change as needed) make sure this is the only rule in the file blocking profile, or the top rule if other file blocking-alert rules exist.
2. Try to use a non-https protocol either FTP or HTTP as HTTPS will require you to use SSL decryption that you did not state if you were using or not.
3. I assume you checked traffic was hitting the rule that has this profile attached to it.
Shai
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-07-2020 05:12 AM
Hi ShaiW,
Thanks for the Quick Reply.
1.Yes i made sure file blocking profile is created as suggested.
2. The requirement in general we want is that all our users to be blocked from downloading install files like .exe files when they do browsing from internet - so please suggest how to setup SSL decryption if that is needed to achieve for HTTPS as well.
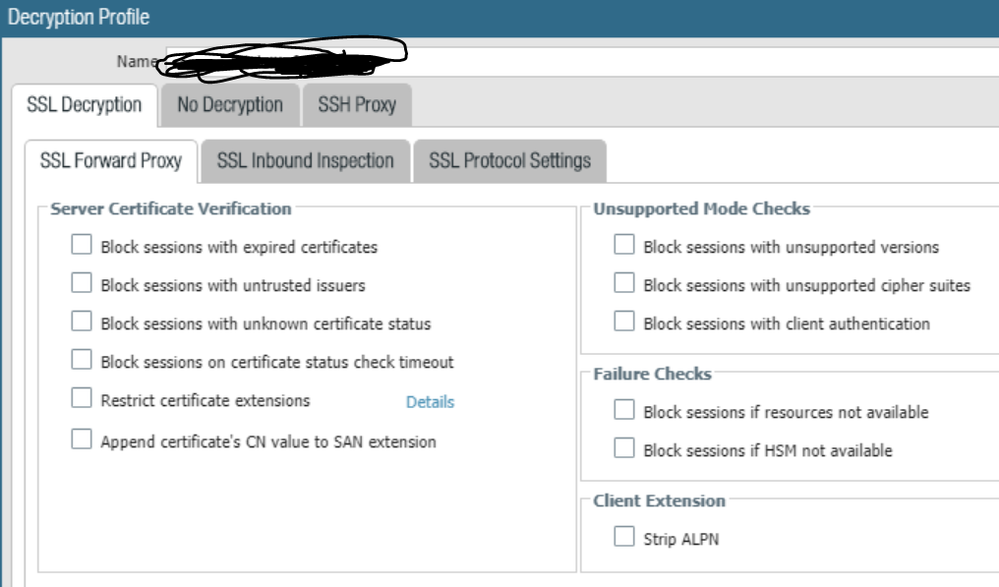
As of we have a Decryption Profile enabled, but i see that under ->SSL Decryption - -No options are selected.
3. Yes I checked that the traffic is hitting the rule that this profile is attached and result is allowed and nothing is getting blocked as of now.
Please let me know if you need me to check anything else.
Note: I'm a Newbie to Palo Alto, so please excuse my knowledge.
Thanks,
Anup
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-07-2020 08:02 AM
There's a lot of documents surrounding setting up SSL Decryption, I'll link a few of them below. The screenshot that you posted just says that you aren't following best practice on the profile, but decryption would actually be "activated" so to speak by setting up a Decryption rulebase policy. You'll definitely want to read up on that prior to activating it; there's client changes you'll need to make so they don't get security warnings and potential legal requirements depending on what regulatory bodies you may fall under and local laws.
The second link has a video that @jdelio made that walks you through the process of getting this setup.
https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000ClEZCA0
https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000ClmyCAC
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-07-2020 08:29 PM
Hi Pry,
Actually this is Non-Prod, so we dont have any users- hence will not affect anybody, I am the User who will test the file blocking.
I am going through the documents you send, will update if any of the settings work to help me block the exe files.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-07-2020 08:59 PM
I tried enabling various options under the Decrypt Profile - SSL Decryption and commit it, But no Luck still cant block the exe files.
The website that I'm testing to download exe file is from https://www.7-zip.org/download.html
Please help me fix the issue and let me know what other options do i need to add to get this File Blocking working.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-07-2020 10:31 PM - edited 10-07-2020 10:37 PM
Hi
All of the items in the Objects tab do not have any affect on traffic if they are not attached to Policies. This includes Decryption Profile/s.
1. So - the File Blocking (FB) Profile must be attached to a security rule.
2. I highly recommend splitting your issue into two parts, get FB working then tackle Decryption. For FB I would recommend you try to download this test file from Palo Alto as it uses the HTTP protocol hence no need for decryption, yet.
http://wildfire.paloaltonetworks.com/publicapi/test/pe
(This is an anti-virus test file, it will probably get blocked by AV software but it does not matter as all we want is for it to download or get blocked by the filewall)
If you see it blocked and logged under Monitor-> Data Filtering - it means FB is working for non-encrypted traffic. Continue to enable Decryption:
3. For Decryption you really should read the above mentioned articles and notes by @BPry as enabling it requires:
3a. Generating Decryption Certificates on the firewall, self-signed for testing or Corporate CA signed (much preferred)
3b. Having them in all computers, trusted root certificate store
3c. Creating a Decryption Policy under Policies->Decryption: for testing start with:
Source Zone Internal (or whatever you named it)
Dest Zone External (or whatever you named it)
Service: service_http + service_https
Action: Decrypt
Type: SSL Forward Proxy
Decryption Profile: is optional
3d. In some older PANOS versions you must also allow in Security rules Application=web-browsing & service=service_https (this is not the default, hence needs adding).
* This might look like easy 4 steps but trust me - it isn't.
Lastly, log into the learning center at:
http://education.paloaltonetworks.com/learningcenter
Search for EDU-110, register for it for free and start watching this online training about the NGFW, but note that the training center is being moved you might be redirected to the new training site in a few days.
Shai
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-08-2020 01:13 AM
Hi Shai,
Thank you, The File Blocking worked once i removed the SSL Decryption and tested it with the http protocol site you gave http://wildfire.paloaltonetworks.com/publicapi/test/pe . But now how do i apply the same for https sites ?
Like you said in Step 3, I need to figure out how to enable Decryption as it does not look easy.
- 1 accepted solution
- 14058 Views
- 7 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Cannot add BIOC rule to restriction profiles in Cortex XDR Discussions
- [SOLVED] Panorama's SAML-Based Administrator Cannot See Other Administrators And Generate TSFs in Panorama Discussions
- Unable to block download and upload for chatgpt and messengers in Next-Generation Firewall Discussions
- What is the Palo Alto recommended standard for Vulnerabilty Profiles, is it to block Critical and High Alerts? or to block medium alerts as well? in Next-Generation Firewall Discussions
- Unable to establish tunnel during Service Connection configuration (Details Added with Screenshot) in Prisma Access Discussions