- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
User ID agent going to non- AD servers
- LIVEcommunity
- Discussions
- General Topics
- User ID agent going to non- AD servers
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
User ID agent going to non- AD servers
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-31-2024 10:02 PM
Hi,
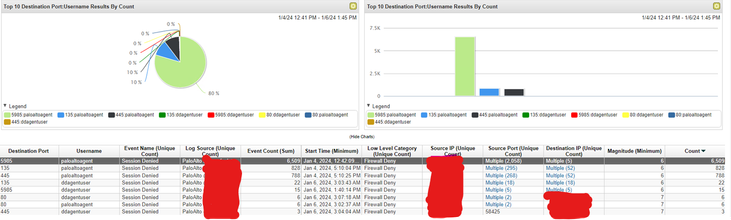
We have a userid_agent installed on our server, our security team noticed the excessive session denies between the userid agent server going to other non-AD servers in our azure firewall, can anyone help me confirm if this traffic from our userid agent server going to non-AD servers are legit traffics?
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-02-2024 10:45 PM
I'd recommend monitoring through Resource Monitor to see what is actually connecting to what on the host, that's the only way to verify what actual process is sending what traffic. Nothing is really shocking from a port aspect outside of it not hitting expected/configured endpoints, however if you weren't the one to configure this agent I'd verify that it's actually been configured properly. AD isn't the only monitorable server for user-ID, it's possible someone added additional nodes that you aren't planning to see.
Additionally I'd take some time to ensure that you have client probing all disabled; that would also account for a large amount of this traffic hitting unexpected nodes.
- 900 Views
- 1 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Prisma Cloud defender agent unable to identify Red Hat back ported patches causing false positives in General Topics
- Cortex XDR Uninstallation in General Topics
- Cortex XDR agent network bandwidth consumption in Cortex XDR Discussions
- Need a similar setting of Global Protect in Prisma Access Agent in Prisma Access Agent Discussions
- Ruckus vsz Syslog and User-ID Agent in General Topics