- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Cortex XDR: Allow list behaviour
- LIVEcommunity
- Discussions
- Security Operations
- Cortex XDR Discussions
- Cortex XDR: Allow list behaviour
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Cortex XDR: Allow list behaviour
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-14-2021 03:22 AM - edited 07-14-2021 03:22 AM
Hi all,
One week ago I added an artifact (hash) to the allow list. This hash was deteced (reported) by the XDR Agent.
Today, I have a new incident, only related with the same artifact(hash) (different host).
I was expecting of not seing any incident related with this artifact if it is the ONLY related to.
Which is the behaviour then of the Allow List functionality?
Thank you,
David.
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-14-2021 05:12 AM
Hi @david.hernandez,
When adding Hash256 values to the Hash Allow List, either via Action Center's "Add to allow list ", or directly from the Incident's Key Artifact, or from the Casualty View, it will be added to the Hash Allow List. This list is then shared among all the XDR agents during the checkin process. If you have added a hash to the Hash Allow list, no further alerting should be generated.
Are you sure that you added the hash to the correct option? Which of the above-mentioned options did you use to add the hash to the allow list?
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-14-2021 10:18 PM - edited 07-14-2021 10:18 PM
Hi @fmoixsante ,
I added it directly from the Incident's Key Artifact, which now has a grey tick button next to it.
Thank you.
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-15-2021 08:31 AM
Hi @david.hernandez The Allow List feature is to allow execution on the endpoint. In this scenario that you described, you should review the alert source (E.g. XDR BIOC, XDR agent...etc) to determine your next steps in the investigation. If XDR BIOC rule is the alert source, and your analysis indicates the process behavior is not a threat in your environment, then you may want to consider adding the process SHA256 to a Rule Exception (XDR App > Rules > Exceptions). Please note, there are two types of exceptions (Global / Profile) that you may leverage to manage the scope.
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-20-2021 07:31 AM - edited 07-20-2021 07:33 AM
The scenario is as follows: I get an incident from a key artifact from the alert Source XDR Agent. A few days later, I get another incident with the same key artifcat, which I added to the allow list. Maybe this is not the expected behaviour? Maybe I should use what you suggest, to use the Rule Exception?
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-20-2021 10:36 AM
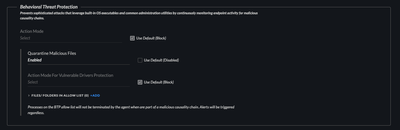
There are two parts to consider in your scenario. The first is file execution (is the file being block / allow on the endpoint) and the second is the cause for alert. The allow/ block list is manage file execution. XDR has multiple layers of protection. I suggest to triage the full context of the alert to understand the cause for the alert. The XDR agent has additional Alert Names associated with the XDR agent alert source. For example, in a Behavioral Threat alert you may need analyze and confirm the initiating process and observed behaviors before making the determination of which process needs to be add to an allow list. In the case of BTP Allow list. The processes on the BTP allow list will not be terminated by the agent when are part of a malicious causality chain. Alerts will be triggered regardless. Reference the Behavioral Threat Protection module within the Malware endpoint security profile:
If you want to exclude alerts for the process in question within the context of BTP, then you will need to create a support ticket in order to obtain a support exception. I hope this information provides you with a path forward.
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-22-2021 10:20 AM
Thank you for your help. I will try to investigate from there.
- 15872 Views
- 6 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Suspicious executable detected Microsoft Store Purchase App in Cortex XDR Discussions
- Redirect URL for Cortex XSOAR integration with DocuSign in Cortex XSOAR Discussions
- bioc not prevent in Cortex XDR Discussions
- How to add exception for known macros detection by cortex XDR in Cortex XDR Discussions
- Consulta de URL in Cortex XDR Discussions