- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Block Access to private Gmail but allow corporate
- LIVEcommunity
- Discussions
- General Topics
- Block Access to private Gmail but allow corporate
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Block Access to private Gmail but allow corporate
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-18-2018 02:49 AM
Hi all.
Im looking for a solution to block user access to private gmail accounts but allow a corporate accounts to be used.
I'm aware that there is a solution involing proxy server and X-forwarder.
Is there any other way to do this without dedicated proxy serever?
Regards
Leo
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-18-2018 04:52 AM
Hi @Leonid.Rozgon,
I haven't tested this myself but you could try the following :
If I'm not mistaken for corporate Gmail access, the usernames have the customer domain name (eg. user@domain.com).
Personal Gmail accounts have usual usernames (eg. user@gmail.com)
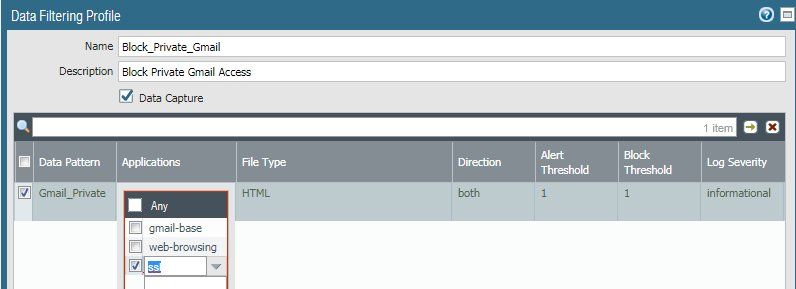
To block personal gmail access, enable ssl-decryption. Next, create a data pattern matching "@gmail.com".
Match this Data pattern on gmail-base app in a Data filtering object.
Apply the Data Filtering object to a policy.
This way you should be able to access corporate gmail accounts and personal gmail access should be blocked.
One caveat I think exists here :
Matching for the regex "@gmail\.com" in the whole page content might also have unwanted matches such as :
-Sending an email to somebody@gmail.com from the corporate account
-Reading an email from somebody@gmail.com on the corporate account
I would think along those lines ... other tips are welcome ^_^
Cheers !
-Kiwi.
Cheers,
Kiwi
Please help out other users and “Accept as Solution” if a post helps solve your problem !
Read more about how and why to accept solutions.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-18-2018 06:21 AM
Thanks for the idea, Kiwi.
Trying to test/implement it, but I think the problem is that there is no option to add ssl or google-base as application in Data filtering profile(whys is that?). Authentication form for gmail is done through accounts.google.com and its not detected as gmail-base application. Will continue testing. If anyone else have any ideas feel free to wite them here.
Regards
Leo
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-09-2020 08:43 AM
Were you able to find anything out? I know Google has a way to block it on Chrome OS devices.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-22-2021 04:54 PM
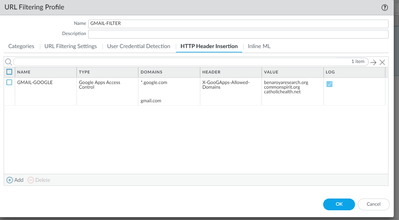
Step 1 Make sure you are decrypting traffic from the inside to the outside
Step 2 Create a custom URL with *.google.com and *.gmail.com
Step 3 Create a URL FILTER
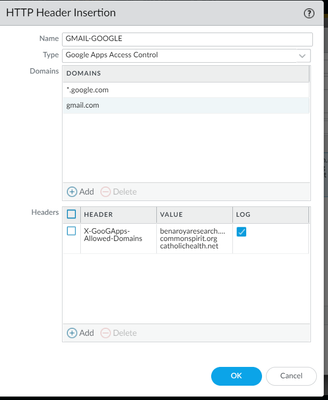
Select HTTP HEADER Insertion
Called it GMAIL-GOOGLE Type Google apps Access control
Under domain add the following *.google.com and gmail.com
Select header X-GooApps-Allowed domain
Under value add your corporate domain example.com paloaltonetworks.com etc
You can add 5 domains
STEP 4 create a policy
INSIDE-2-OUTSIDE Inside outside APPS GOOGLE-APPS service URL Category=GMAIL-COORPORATE Action= allow profile=url Filtering =GMAIL-FILTER
GOOGLE-APPS= GMAIL, Google-BASE, ssl, RTCP,rtp-base,stun,web-browsing vidyo
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-23-2021 04:59 AM - edited 10-23-2021 05:00 AM
Group.. i would recommend that the customer look at HTTP Header Insertion n under the URL Filter Profile section
With the HTTP header insertion and modification feature, you can now manage HTTP header information to disallow SaaS consumer accounts while allowing a specific enterprise account.
- 27152 Views
- 5 replies
- 1 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- PA 445 setup in Next-Generation Firewall Discussions
- Global Protect Internal Detection in GlobalProtect Discussions
- Assign private IP address failed in GlobalProtect Discussions
- Azure to OnPrem Connectivity issue in Next-Generation Firewall Discussions
- URL Category Change Request for www.intusjuntsparlament.com in General Topics