- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
block gmail personal ID and allow gmail official ID in palo alto
- LIVEcommunity
- Discussions
- General Topics
- Re: block gmail personal ID and allow gmail official ID in palo alto
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
block gmail personal ID and allow gmail official ID in palo alto
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-05-2015 12:11 AM
Hi Friends,
please suggest,block gmail personal ID and allow gmail official ID in palo alto.
Regards
Satish
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-05-2015 05:47 AM
Hi Satish,
I don't think that is possible with current design. Unless you can verify if the URL you navigate to for both personal and official are unique. If that is the case the case then you can configure ssl decryption on device and allow or deny specific URLs. Which I think is highly unlikely. Hope this helps. Thank you.
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-05-2015 06:18 PM
Hi,
Google is suggesting as below
Block access to consumer accounts - Google Apps Help
PAN device can decrypt ssl traffic, though it can't insert HTTP header X-GoogApps-Allowed-Domains.
This means PAN device can't handle such a case.
If you have proxy server, you can do it on the proxy.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-26-2015 04:25 AM - edited 10-26-2015 04:26 AM
Hello Friends,
Please try this one :-
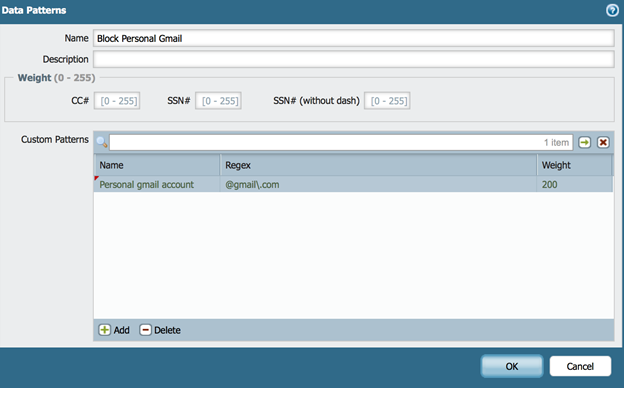
Create a Custom Data Pattern
Objects - custom-objects - data-patterns
match regex pattern @gmail\.com
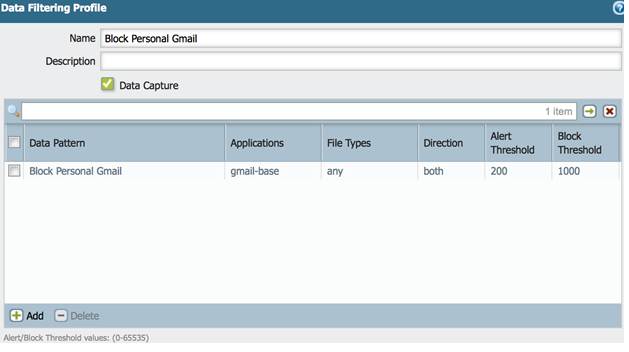
Create a Data Filtering profile
Objects - security-profiles - data-filtering
Match the previously created custom data pattern in the Data filtering profile and application as gmail-base.
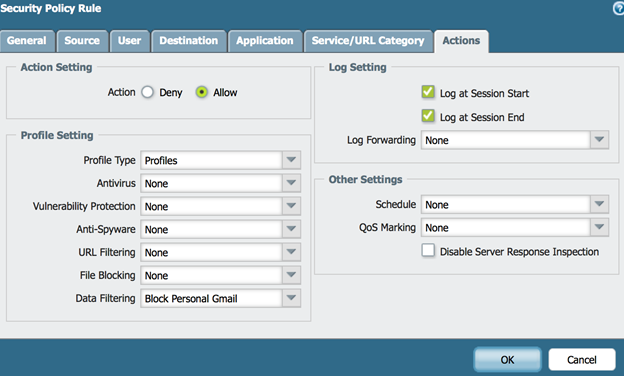
Create a rule allowing all apps with the data security profile attached to it.
Policies – security – rulebase
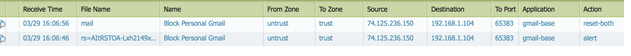
Data Filtering log: note the first log as it matches the data pattern
Thnaks
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-26-2015 04:27 AM
Have a look at PA Aperture:
https://www.paloaltonetworks.com/products/aperture.html
This might be your solution. But so far there isn't much info about it yet.
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-23-2020 05:54 AM
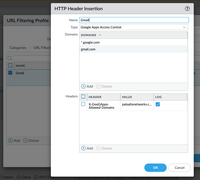
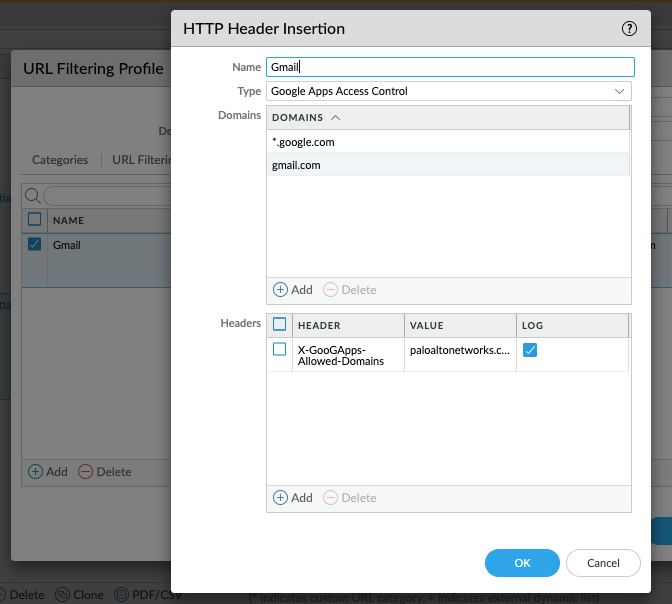
Step1: Add HTTP Header Insertion under URL Filtering Profile
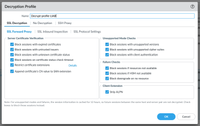
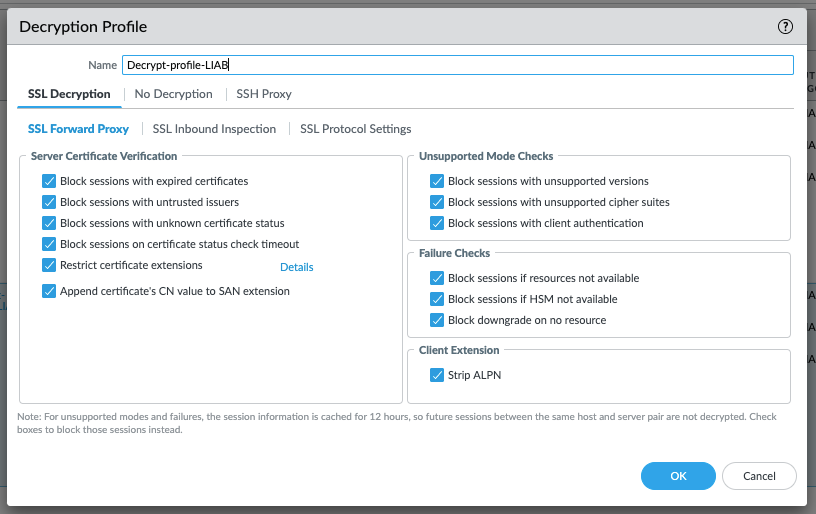
Step2: Create Decryption Profile and enable "Strip ALPN" Under Client Extension
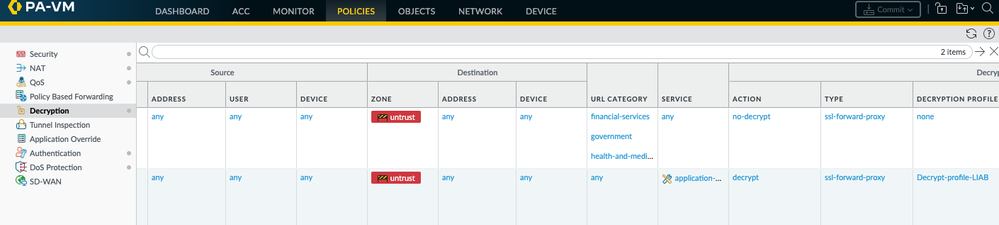
Step3: Add Decryption Profile in your Decryption Policy
Step4: Make Sure the URL Filtering is added in your Security Policy
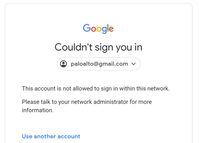
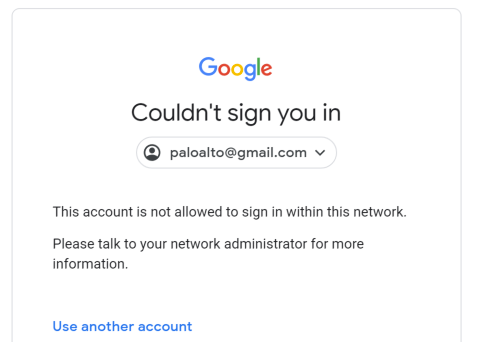
Result: Personal Gmail is blocked
FOLLOW MY FACEBOOK GROUP - Palo Alto Networks Q/A
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-23-2020 06:20 AM
Step1: Add HTTP Header Insertion under URL Filtering Profile
Step2: Create Decryption Profile and enable "Strip ALPN" Under Client Extension
Step3: Add Decryption Profile in your Decryption Policy
Step4: Make Sure the URL Filtering profile is added in your Security Policy
Result: Personal Gmail is blocked
Cheers,
Faizan Sheikh
FOLLOW MY FACEBOOK GROUP - Palo Alto Networks Q/A
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-26-2021 08:02 AM
Thank you so much for the "how to" it really works so well. However I having a particular situation, if a add a a second header, only the first one created works, any suggest?
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-21-2022 08:29 AM
just simple.
follow google.com example
input 111.com, 222.com in value
Example: X-GoogApps-Allowed-Domains: mydomain1.com, mydomain2.com
mydomain1.com, mydomain2.com
- 21520 Views
- 8 replies
- 1 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Request for Documentation on VPN and Routing Log Events in General Topics
- Error in Outlook Email Server Profile in Next-Generation Firewall Discussions
- PAN-GPLimiter: Limit Concurrent GlobalProtect Sessions/Connections Per Unique User in General Topics
- Unable to Block Personal Gmail on Ubuntu Machines. in Next-Generation Firewall Discussions
- Want to block personal gmail and allow corporated gmail in General Topics