- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Captive Portal for more than one security zone
- LIVEcommunity
- Discussions
- General Topics
- Captive Portal for more than one security zone
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Captive Portal for more than one security zone
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-06-2013 02:34 AM
Hi
Few months ago I sucessfully configured CaptivePortal (in redirect mode) with SSL certyficate from StartSSL for one of my local network connected to PA200.
Now I need to do the same for another local network, but on PAN I can only make one CP configuration, with one SSL cert.
I have SSL cert for host cp1.mydomain.com. This dns entry pointing to 192.168.110.1 that is a gateway for network where I have CP.
Until now evertything is clear for me, but when I enable CP to another network (with 192.168.30.1 gateway) its working too - why?
My networks are in separate security zones without policy that could enable traffic beetwen this zones/network.
So I tryed to put cp1.mydomain.com to one of my public IP (not used at the moment) but reachable from PAN. I changed entry in DNS, but its broken CP because users cant get CP webpage because this public IP isnt reachable without authenticate.
My CP looks like:
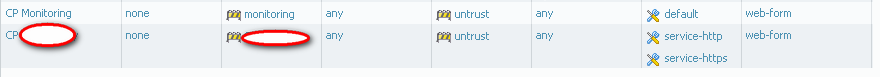
and Security Policy:
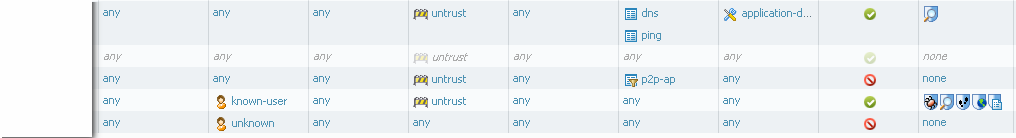
and hear I'm not sure that this configuration is optimal and made according to best practices.
I'd like to block p2p traffic, let DNS and ping and let all authenticated users access to internet.
I forgot .. I have one samll issue with SSL cert. Evertytime I started browser (ie. IE7) I get warning that browser has't information about cert issuer. Similar problem is described
but I have cert from StartSSL. Where I can find IPs that I need to add to be reachable without CP policy?
I searched this community, read How to Configure Captive Portal.pdf but I cant find information about CP for two networks.
Please help me in such configuration.
With regards
Slawek
- Labels:
-
Configuration
-
Troubleshooting
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-09-2013 09:35 AM
yes, I have exactly the same config.
In my opinion cert warning is because web browser cant verify ssl cert issuer. But how (or where) to find list of server that I need to exclude from CP roule - I don't know.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-09-2013 09:51 AM
We use a cert issued by a public certificate authority. Certificate revocation checks to local domains could be the issue? If you use a commercial cert then just watch the log traffic for the CRL check and add that as an allowed destination.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-11-2013 12:44 AM
I using public certificate too. I'm using free StartSSL certs.
I tryed to find such informations from logs but I havnt such connections in log from this particular zone to Untrust zone.
I catched interesting screen shoot:
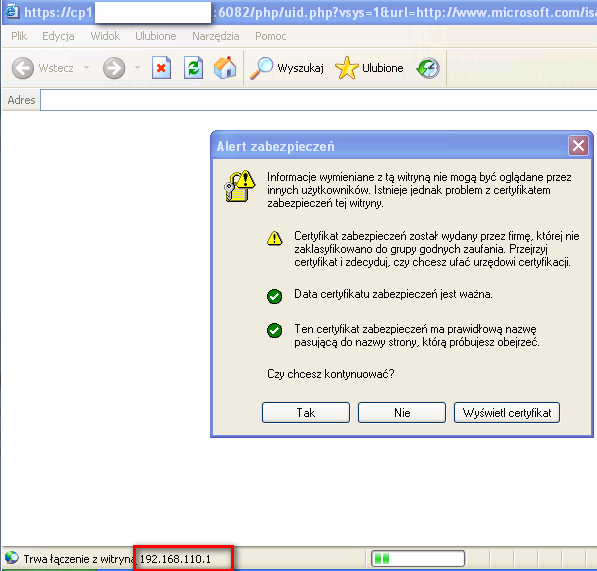
As you can see, IE is trying to connect to 192.168.110.1 - this is because cp1.mydomain.com is pointing to it. This computer has 192.168.3.38 IP at the moment, and is UNABLE to communicate to 192.168.110.1 (for security reason, 192.168.3.x must only have access to untrust or 192.168.3.1 because it's a getaway from PAN).
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-11-2013 06:32 PM
slv
The web browser may not have a root cert. Check like this:
The other issue may be the certification revocation check.
Phil
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-11-2013 11:43 PM
Hitssec
I know that one way is to have root cert in local Cert store, but he second way is to give to browser information abaout intermidiate cert StartSSL™ Certificates & Public Key Infrastructure
Also IE uses windows cert store, but FF uses their own store so I prefer to make universal solution ("glue" cert with intermidiate cert).
I havent ability to put root cert into personal computer of my students.
On Windows IE6 complaining about ability to verify root cer, on the same computer FF 20.1 doesnt. Latest (but maybe not the last) FF on Linux complaining too.
The same complaining is from 192.168.3.x as from 192.168.110.x network
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-13-2013 07:42 AM
Slv,
Since I can't read the warning message you posted (I only read english - sorry) there are only three possible causes:
Wrong cert being used
Private cert - not being able to validate
Public cert - not being able to validate
Public certs should be able to be validated (may need to select optional updates via windows update to get the root certs on the client. The outher option is to tell them to accept the cert warning.
Sorry if I can't help you more but I think you are on the right path. You can always put a call into support and they can assist.
Phil
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-15-2013 12:43 AM
You where right, problem with this warning is connected to root cert. After updating root cert store with latest package IE doenst show warning message.
Lets back to main question.
- on which one IP I should setup Captive Portal, from which zone? I need to use CP for 3 zones.
- do my security policy are correct?
With regards
Slawek
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-15-2013 12:29 PM
You can apply Captive portal on any and all zones that you wish. Captive config says go to the redirect host identified.
The Captive portal rules determine what traffic patterns will trigger a Captive portal redirection. See the below image:
I hope this helps. Within the rule set you can exclude traffic patterns from being captive portal redirected.
Phil
- 7906 Views
- 10 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Unable to activate Precision AI network security bundles license in General Topics
- GlobalProtect Always-On (6.3.3-c711) – Users Stuck in “Connecting” State but Still Have Internet Access in General Topics
- Windows Clients – Captive Portal Not Triggering with GlobalProtect Always-On Enabled in General Topics
- [SOLVED] - NGFW The Connection To Global Protect On The IPads Times Out!! in GlobalProtect Discussions
- XSOAR IP Forwarding requirement in Cortex XSOAR Discussions




