- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
V-Wire in VMware.
- LIVEcommunity
- Discussions
- General Topics
- V-Wire in VMware.
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-03-2019 09:16 AM
I am trying to trial V-Wire for an upcoming requirement .
The final goal is to secure a number of VMware VM's on their original IP's [differing subnets ] behind a v-wire.
So I have a VM100 which I have assigned 2 interfaces
one to a vswitch connected to a virtual PC 192.x.x.5
other to a vswtich connected to a virtual server 192.x.x.10
there's rules in both directions to pass all traffic.
But a simple ping either way fails, does not even show up in the log.
I am not sure if it's a VMWare related issue or some thing on the PA.
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-04-2019 12:25 AM
It's not NSX, that would solve my issue full stop.
The VM100 works fine for normal test traffic, been in place for a few years.
Just V-Wire I am having difficulty with.
The SUBNET on the V-Wire is on the same IP range as the management interface, but should that be an issue???
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-03-2019 09:48 AM
Is this an NSX-integrated deployment from Panorama, or just a stand-alone VM? Also, how many virtual interfaces did you add to the VM? The first will go the the management port, the second to first Ethernet interface, third to the second Ethernet interface, etc.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-04-2019 12:25 AM
It's not NSX, that would solve my issue full stop.
The VM100 works fine for normal test traffic, been in place for a few years.
Just V-Wire I am having difficulty with.
The SUBNET on the V-Wire is on the same IP range as the management interface, but should that be an issue???
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-04-2019 04:02 AM
Sorted I think.
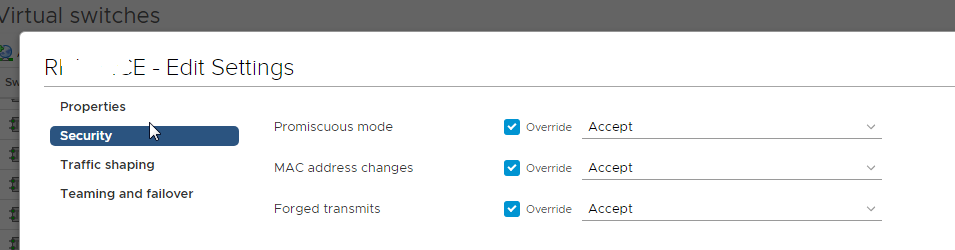
Combination of not having the "promiscuous mode enabled" on the v-switch port group, and one of the two endpoints havign windows firewall on for some obscure reason.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-04-2019 06:30 AM
@RobinClayton wrote:The SUBNET on the V-Wire is on the same IP range as the management interface, but should that be an issue???
No, I've done several VMs where the mgmt inerface is in the same range, though w/ L3 interfaces, not v-wire. I was just assuming it was a new VM, and wanting to make sure you took that into account when adding virtual interfaces. Glad you got it sorted.
- 1 accepted solution
- 6584 Views
- 4 replies
- 1 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Panorama Very Slow on VMware ESXI in Panorama Discussions
- Trying the DNSProxy feature for Static Response in General Topics
- PAN-OS 10.1 with VMWare ESXi 8.0 in Panorama Discussions
- XSOAR virtualization support in General Topics
- Migrate policies from Carbon Black to Cortex XDR in Cortex XDR Discussions