- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Globalprotect end users are receiving default route (0.0.0.0) but it is not configured to do that
- LIVEcommunity
- Discussions
- Network Security
- GlobalProtect Discussions
- Globalprotect end users are receiving default route (0.0.0.0) but it is not configured to do that
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Globalprotect end users are receiving default route (0.0.0.0) but it is not configured to do that
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-20-2020 09:58 AM
Hello masters,
I need your help on how to troubleshoot an issue related to global protect.
On our Access routes, no 0.0.0.0 are configured.
We wanted to let users use their local gateway for any traffic destined to the internet.
But they are receiving the 0.0.0.0 in their RoutePrint resulting to traversing their any traffic to the VPN.
This is clogging our network.
I already engaged 3 TAC on this but could not find the issue.
Details:
Software Version8.1.9-h4
GlobalProtect Agent4.1.10
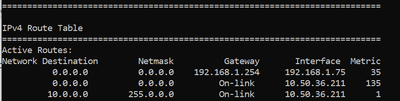
RoutePrint:
Active Routes:
Network Destination Netmask Gateway Interface Metric
0.0.0.0 0.0.0.0 192.168.0.1 192.168.0.199 35
0.0.0.0 0.0.0.0 On-link 10.0.0.201 50
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-01-2020 03:25 AM
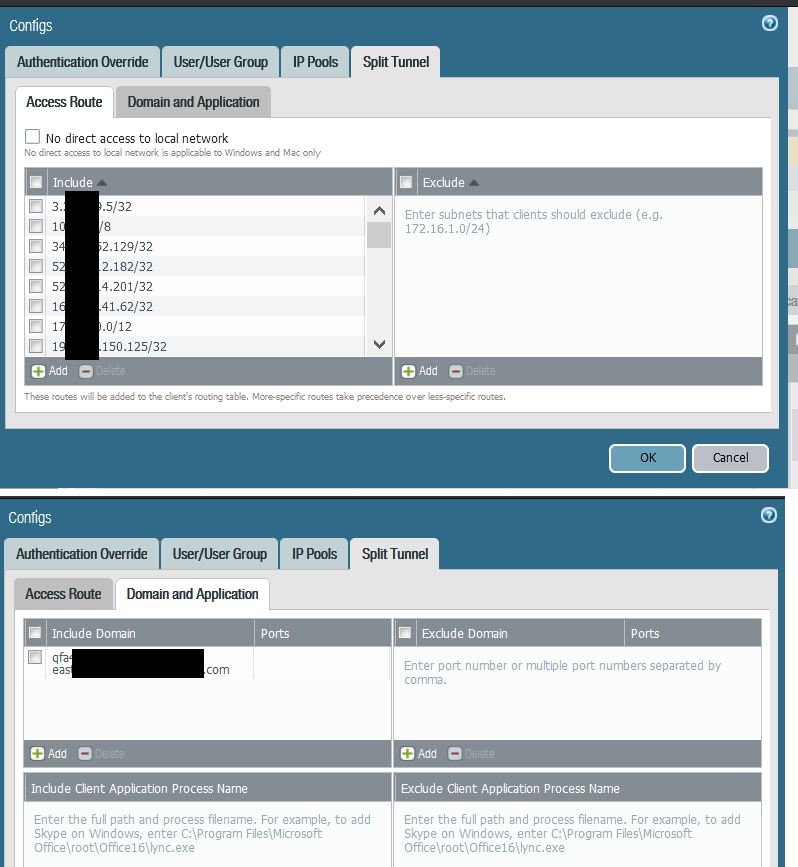
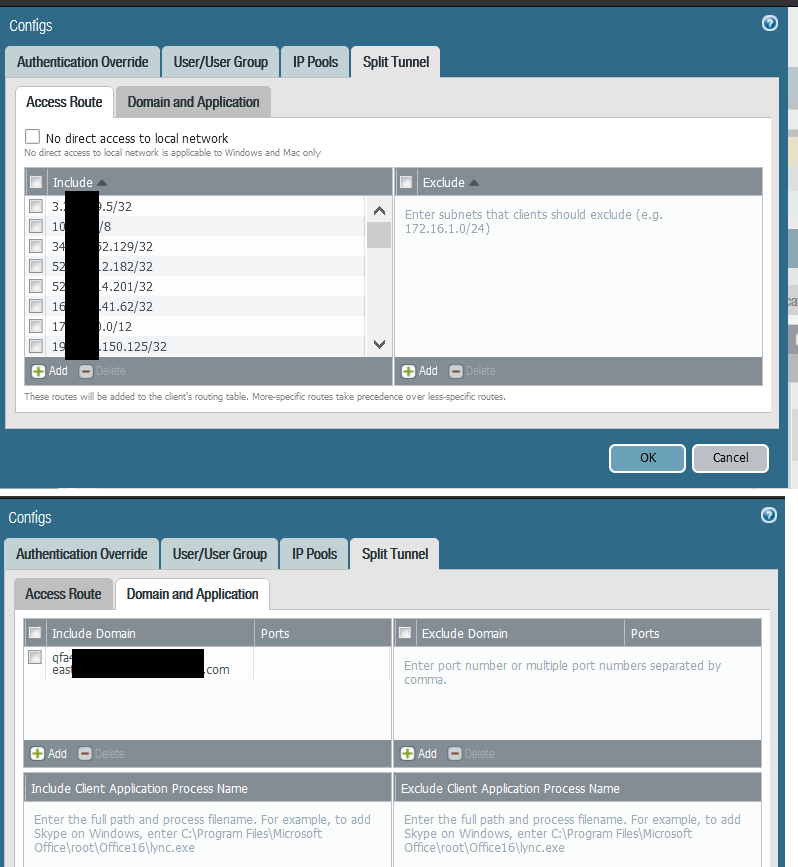
Please see below access route
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-01-2020 09:45 AM
default routes 0.0.0/0 always apply whether using split tunnel or not.
your more specific routes /32 /24/23 etc will take precedence over /0
is there any more information in your route print or have you just left it out.....
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-02-2020 05:03 AM
We have had a similar issue, the workaround for us was to exclude the default route from the split tunnel.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-02-2020 06:22 AM - edited 12-02-2020 06:24 AM
Hmmm there must be something odd with your settings if thats the case...
I have a test gateway that only includes 10.0.0.0/8
route print below...
so any unknown traffic such as 8.8.8.8 has 2 default routes but the local interface has a lower metric (35) so no traffic goes down the tunnel unless its within 10.0.0.0/8.
Perhaps your metric is the other way round for some odd reason, i would only think this would happen if you had just exclude routes in your settings.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-16-2020 12:54 AM
I have to agree with @Mick_Ball the 0.0.0.0/0 route will still be in the routing table but the host will see this as a backup route, the 0.0.0.0/0 route that is via your home network gateway will be used as its metric is takes precedence over the one through the Global protect tunnel, if you were, for instance, to configure the Global Protect to tunnel all traffic then the metrics would be the other way around.
As it is your include routes are tunnelled and the host will only use the GP default route should the 192 gateway become unavailable, however that would also cut off your connectivity so you would have bigger issues!
My logic behind excluding the 0.0.0.0/0 route was simply that by actively excluding it, it may not find it's way into the routing table at all.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-10-2023 08:47 AM
was there a solution to this problem? apparently, I have run into the same problem where GP installs a default route albeit with a higher metric in the route table. What's weird is this behavior is seen on Windows and a Mac system but not on an Ubuntu OS.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-16-2023 12:34 AM
Hi @szaidi110 ,
Have you tried excluding the route as mentioned in earlier replies ?
Please also clarify which GP version you're experiencing this with.
Kind regards,
-Kim.
Cheers,
Kiwi
Please help out other users and “Accept as Solution” if a post helps solve your problem !
Read more about how and why to accept solutions.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-16-2023 05:41 AM
Hi @kiwi
Excluding the route doesn't work. Evidently, if you have any values configured under the domain and application option (which we did), PAN GP will install a default route for it even if you've excluded it from the access routes. No other way around it.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-20-2025 12:18 AM
Is there any way to avoid/deleted default route when you add any domain in split tunneling?
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-08-2025 06:02 AM
I worked around it by adding:
0.0.0.0/1
128.0.0.0/1
as exclude routes.
- 17309 Views
- 13 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- GlobalProtect 6.3.3 + Duo SAML MFA loop after normal Windows login (works only via GP Credential Provider at Windows logon) in GlobalProtect Discussions
- Rapid7 Insight Agent not showing as vendor in HIP Object Anti-Malware tab despite OPSWAT V4 support in Next-Generation Firewall Discussions
- Global Protect Internal Detection in GlobalProtect Discussions
- Configuring GlobalProtect via Ansible in GlobalProtect Discussions
- GlobalProtect Cert+SAML in GlobalProtect Discussions