- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
MineMeld syslog indicator rules
- LIVEcommunity
- Discussions
- General Topics
- MineMeld syslog indicator rules
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-22-2016 03:53 AM
Hi all,
I've successfully connected my firewall to the syslog miner and can see logs arriving. I believe I now need to create a rule to match logs to extract the indicators.
Here's my recieve stats from the miner:
Here's the rule I'm trying to craft to extract the src_ip info..

Additionally, is it possible to extract the attacker IP from the WildFire submissions log? Looks like just threats and traffic. My use-case would be to capture attacker IPs for previously unknown samples where no further samples are seen and therefore the Threat WF sigs are not activated.
Thanks for the help.
Tim
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-22-2016 04:40 AM
Hi Tim,
documentation is lacking on the syslog Miner, I will work on something better. In the meantime this a rule definition for extracing source IP from Wildfire logs. Wildfire logs are logs of type THREAT and subtype wildfire. The misc field contains the name of the file, while the url_idx field contains the hash.
conditions: - type == 'THREAT' - log_subtype == 'wildfire' fields: - misc - url_idx indicators: - src_ip
There are a couple of bugs in the current version of the syslog Miner (0.9.18) I am planning to fix in the next minor.
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-22-2016 04:40 AM
Hi Tim,
documentation is lacking on the syslog Miner, I will work on something better. In the meantime this a rule definition for extracing source IP from Wildfire logs. Wildfire logs are logs of type THREAT and subtype wildfire. The misc field contains the name of the file, while the url_idx field contains the hash.
conditions: - type == 'THREAT' - log_subtype == 'wildfire' fields: - misc - url_idx indicators: - src_ip
There are a couple of bugs in the current version of the syslog Miner (0.9.18) I am planning to fix in the next minor.
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-22-2016 05:32 AM
Working great. Thanks again Luigi. I think I have everything I need for now, so i shouldn't be hassling you for a while 🙂
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-23-2017 10:47 AM
Maybe I am missing something.. however I want to only parse syslogs that have been allowed, where do I go to do this. (like where do I go to add indicator rules)
Did I miss where this was noted?
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-25-2017 05:41 AM
Hi @josev123,
you can do this in 3 ways (in order of performance):
- forward only logs of accepted session to MineMeld
- filter the session logs inside rsyslog config
- create an indicator rule that match on the condition action == "accept"
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-31-2017 08:02 AM
where do I go to add a indicator rule
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-02-2017 12:16 AM
Hi @josev123,
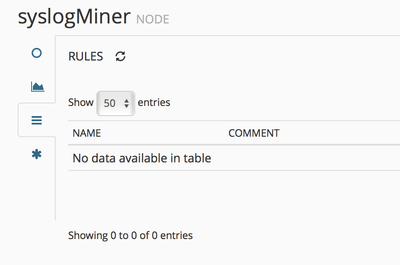
you should go into NODES > <syslog miner node> > RULES to add new indicator rules. Check this forum for examples of rules you can specify:
- 1 accepted solution
- 11639 Views
- 6 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- After pushing content from Dev to Prod, we are seeing lot of errors in XSOAR in Cortex XSOAR Discussions
- DTRH: CIS Benchmarking - 3rd Party Data Ingestion | Data Parsing | Widgets & Dashboards in Cortex XDR Discussions
- Getting the SpeedTest.net servers with MineMeld in General Topics
- How to parse and filter proofpoint list in General Topics
- System - Engine - Logs - CIDR is not a valid IP indicator ERROR in General Topics