- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Connecting Firewalls to Azure Log Analytics / Sentinel CEF map log fields
- LIVEcommunity
- Community Legacy Content
- Automation / API
- Automation/API Discussions
- Connecting Firewalls to Azure Log Analytics / Sentinel CEF map log fields
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Connecting Firewalls to Azure Log Analytics / Sentinel CEF map log fields
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-10-2020 04:54 AM - edited 08-10-2020 05:25 AM
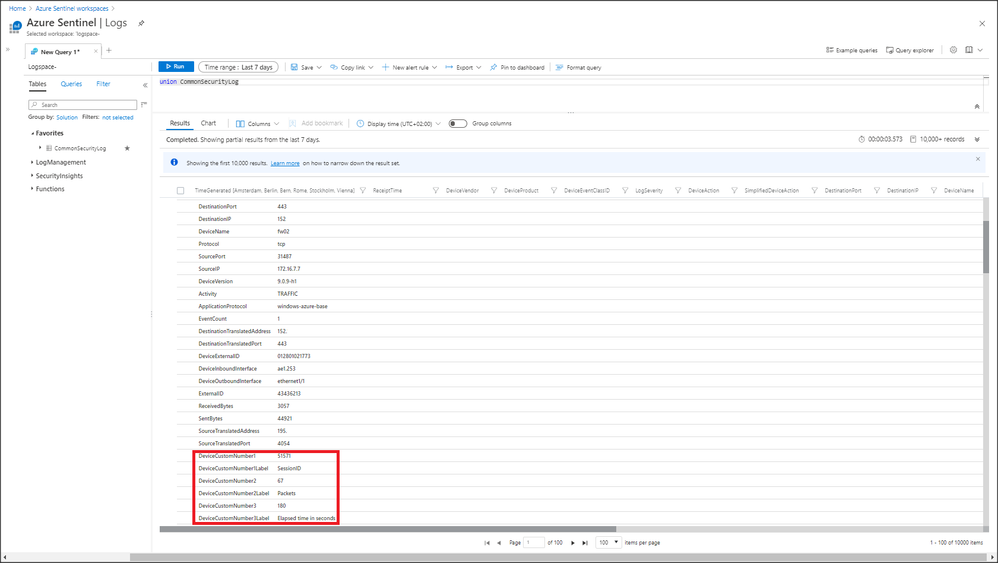
Hi, how can we achieve creating additional fields for logs being processed in "CommonSecurityLog" (https://docs.microsoft.com/en-us/azure/azure-monitor/reference/tables/commonsecuritylog) when sending in logs using the described log connector from Azure Sentinel using Syslog? At the moment incoming data gets mapped to fields like "DeviceCustomString1" or "DeviceCustomString1Label" using CEF. Is it possible creating additional/custom fields in "CommonSecurityLog"?!
We try connecting Palo Alto Networks firewalling infrastructure to Azure Log Analytics / Sentinel exactly following the guide (Azure Sentinel workspaces > Azure Sentinel | Data connectors > Palo Alto Networks) in Sentinel but we see a lot of incoming data being mapped to fields like "DeviceCustomString1" which don't have a characteristic name. (e.g. "Session ID" -> "DeviceCustomString1", Rule Name -> "DeviceCustomString2"). The real field names get stored in the label fields like "DeviceCustomString2Label".
Many thanks and really appreciate your help on that!!
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-17-2020 06:11 AM
For better or worse, this is how CEF works. You can create a better view for your analyst or rule writer in Azure Sentinel by using KQL functions as describe in Using KQL functions to speed up analysis in Azure Sentinel that will rename the relevant fields to your liking.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-23-2020 06:29 AM
Many thanks for your help on renaming relevant fields! That's great!
- 10667 Views
- 2 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Always connect to active firewall in Automation/API Discussions
- Get reachable (not management) IP address of devices from Panorama API in Automation/API Discussions
- Connecting to PAN-OS Firewall Device via SSH and Bypassing HTTPS - Ansible Galaxy (PaloAltoNetwork) in Automation/API Discussions
- Ansible PAN OS Collection - Can not connect to PA firewall. in Automation/API Discussions