- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Using MineMeld with MISP
- LIVEcommunity
- Community Legacy Content
- Automation / API
- Automation/API Discussions
- Re: Using MineMeld with MISP
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Using MineMeld with MISP
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-12-2018 08:25 PM
How can I pull the IOCs from MISP to MinMeld Plattform ?
Exist any extension to get the IOCs from MISP ?
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-24-2019 09:59 AM
Hi there,
try:
in SYSTEM > EXTENSIONS install the extension using git button (https://github.com/PaloAltoNetworks/minemeld-misp.git)
more details in: https://github.com/PaloAltoNetworks/minemeld-misp
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-22-2019 12:39 PM
Excellent, Tks a Lot
@TiagoSantos84 wrote:
Hi there,
try:
in SYSTEM > EXTENSIONS install the extension using git button (https://github.com/PaloAltoNetworks/minemeld-misp.git)
more details in: https://github.com/PaloAltoNetworks/minemeld-misp
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-16-2019 07:14 AM
Hello,
I'm trying to integrate Minemeld with MISP.
I followed https://github.com/PaloAltoNetworks/minemeld-misp
Which URL of MISP (public) do I need to provide on the Prototype parameter ?
Regards,
HA
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-16-2019 07:34 AM
Hi @slp-security ,
I don't know if I understand your question, but you need to use your MISP url.
Prototype parameters
# source name, to identify the origin of the indicators inside MineMeld
source_name: misp.test
# URL of MISP
url: https://misp.example.coPlease be more specific.
Kind regards,
Tiago
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-17-2019 12:07 AM
Hi,
First, thanks for your help.
OK I solved the issue.
The API key was not correct...
Regards,
HA
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-23-2020 12:44 PM
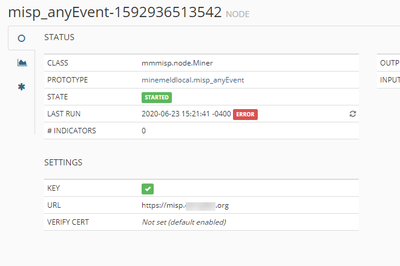
Have you ever had this issue ?
- i clone this prototype as a new node : misp.anyEvent
- added the url and the API key from the GUI
Do i missed something ?
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-23-2020 01:25 PM
Hi @papham,
Try to confirm your auth key..
Certificates installed on misp? Do you have a self signed certificate?
But it should be straight forward.
Kind Regards.
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-07-2020 02:15 AM
My MISP miner seems to work OK, i'm using the IDS check box as the filter to block IoC's - How do I unblock an IoC, is it as simple as unchecking the IDS box in MISP, will that update the EDL?
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-07-2020 03:17 AM
Hi @Tony101
It really depends on how the receiver deal with data. There is some platforms that will update the list of IoCs after some amount of time. On the other hand you can try to disable IDS flag on the MISP and delete the IoC on the destination that already receive the IoC as black list.
However, you just need to remove IDS flag if you don't have the enforcewarninglist flag active on the query and if you don't have any warninglist feed active.
Please take a look on this:
- https://github.com/MISP/misp-warninglists
- like this example (credits from Dev Team MISP):
https://your.misp/attributes/restSearch/returnFormat:suricata/publish_timestamp:15d/enforceWarninglist:1
Hope that you can manage it. It's really hard to deal with false positives!
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-23-2020 07:19 AM
Hi thanks for the previous answer, it was really helpful.. I have another question re the output FEED BASE URL:
appending ?v=mwg&t=regex to the feed base url gives me the format i require e.g..
type=regex
"hxxp://badsite[.]biz/malware.html" "comment"
But what i really want to achieve is an * wildcard at the end of the string e.g.
"hxxp://badsite[.]biz/malware.html*" "comment"
Any ideas if this is do-able?
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-17-2020 09:51 AM
Hi
we have recently installed MineMeld on our Linux server and after adding the MISP extension on MineMeld, I don't understand what it means by add your MISP URL. Is this URL found from MISP website or is it a URL we get after installing MISP. Between we haven't installed MISP as well. Is it required for the miner to work ?
Another question I have is regarding the dynamic lists on MISP website. Do we add them with MISP miner or regular miners can pull them too?
I'm very new to MineMeld and I don't quite understand how to configure nodes. So I would appreciate if you could provide me a sample of a configuration for MISP feeds.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-17-2020 10:17 AM
Hi,
MISP url is the address of you MISP instance. So you need to install it, create a sync user and put the key of that user in the miner.
Please follow the links provided in previous posts.
Kind regards,
Tiago
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-20-2021 08:57 AM
Hi guys, but
source name, to identify the origin of the indicators inside MineMeldSource name is generic? Can i choose every name?
- 18998 Views
- 13 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Minemeld pre-built VMs in Automation/API Discussions
- Split Minemeld Feed in Automation/API Discussions
- Do not decrypt SSL traffic for Office 365 and ZOOM in Automation/API Discussions
- Account role read/write Minemeld - DAG in Automation/API Discussions
- Issues registering custom prototype and custom miner in Automation/API Discussions