- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Alternatives to Panorama for log collecting?
- LIVEcommunity
- Discussions
- General Topics
- Re: Alternatives to Panorama for log collecting?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Alternatives to Panorama for log collecting?
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-15-2014 03:42 PM
Hi.
After a recent failure HD on my normally active firewall, it appears I'm going to lose close on 12 months of logs because Palo Alto has no defined process to get the logs off a failed hard drive (where the log partition is still accessible) onto the replaced drive.
Yes, I have tried scp log export/import - I've swapped the old HD in and gotten it to the point I can get an export, but I can't re-import it.
Anyway, that's not the point of this.
My boss wanted an alternate solution to keeping the logs on the device, so as to avoid this in future - Panorama of course came up, but the pricing for it is *completely* ridiculous, so it's out of the question.
Does anyone have suggestions to an alternate, external log collection point which can give me meaningful data/reports? I don't mind if it costs a bit - but my boss baulked at the much higher amount we were quoted for the VM version of Panorama, so I'd like to keep the costs down to maybe $2-3k if I can.
I've heard Splunk mentioned, but a quick perusal looks like it's *way* overkill for what I want.
Anyone else got a solution/suggestion?
Cheers.
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-15-2014 04:50 PM
I would say that if you are looking for long term archive referral of firewall information you do want a tool on the caliber of Splunk security or another professional SIEM platform like Qradar. These tools go beyond basic syslog storage to allow you to correlate and find the information you need when doing an investigation or troubleshooting.
The other advantage they have is they scale well and allow the correlations to server, switch and router infrastructure in addition to the firewalls. And they are easy to expand storage for longer archive terms as needed.
https://www.splunk.com/view/it-security/SP-CAAAAKD
Splunk also offers a basic free version that supports 500 meg logging per day that would cover the syslog fundamentals if you don't want to go for a SIEM solution.
Free vs. Enterprise | Splunk License Comparison Table | Splunk
ACE PanOS 6; ACE PanOS 7; ASE 3.0; PSE 7.0 Foundations & Associate in Platform; Cyber Security; Data Center
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-15-2014 06:51 PM
Steven.
Thanks for the reply.
I think QRadar is probably out of the question - looking at the US prices I flinched!
My biggest issue with Splunk is that it appears to be more than I need, and I'm not sure how it integrates with the Palo Alto at all - but I'm also not sure how else I would go about getting log storage and reporting off the devices themselves - yes, I can dump it to Syslog - but getting meaningful analysis out of a Syslog server has always been an exercise in frustration.
Have you actually implemented Splunk in conjunction with the Palo Alto at all, and are able to say how well it works compared to the on-the-box reporting?
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-16-2014 05:31 AM
Darren,
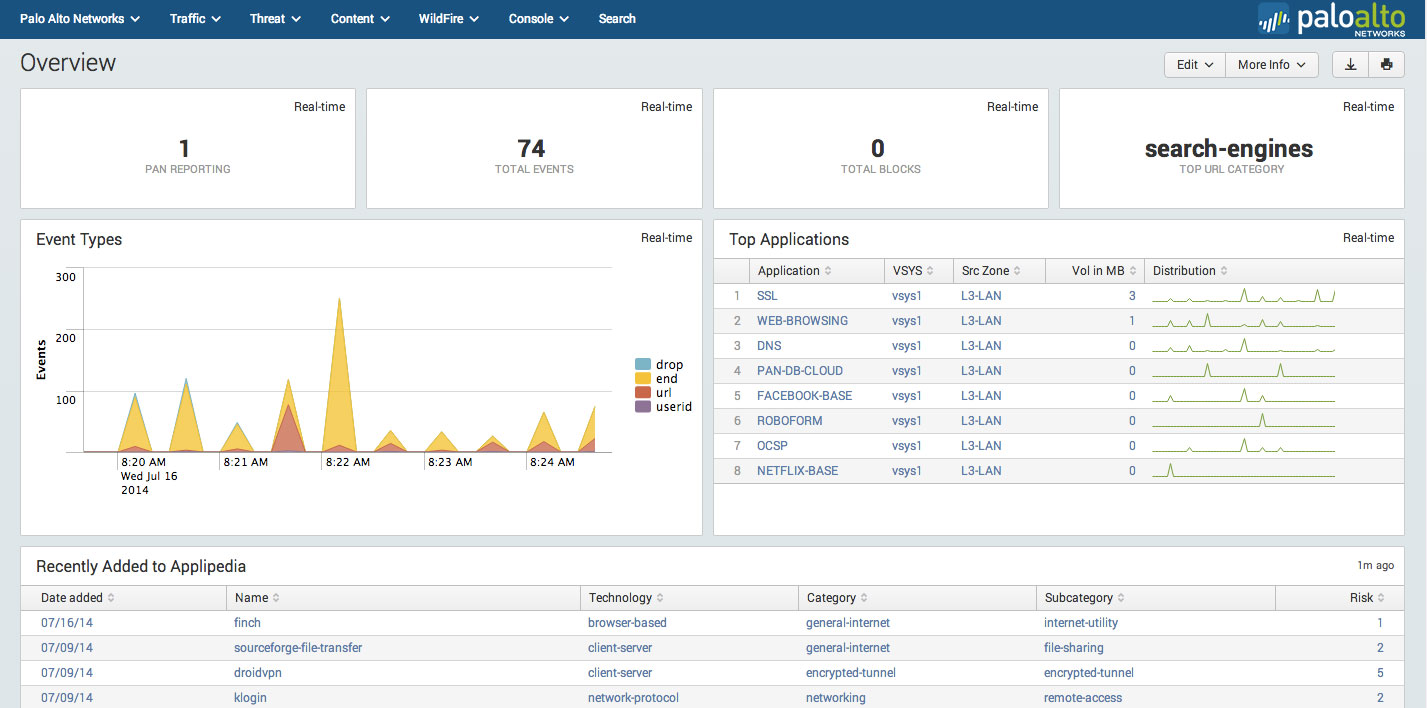
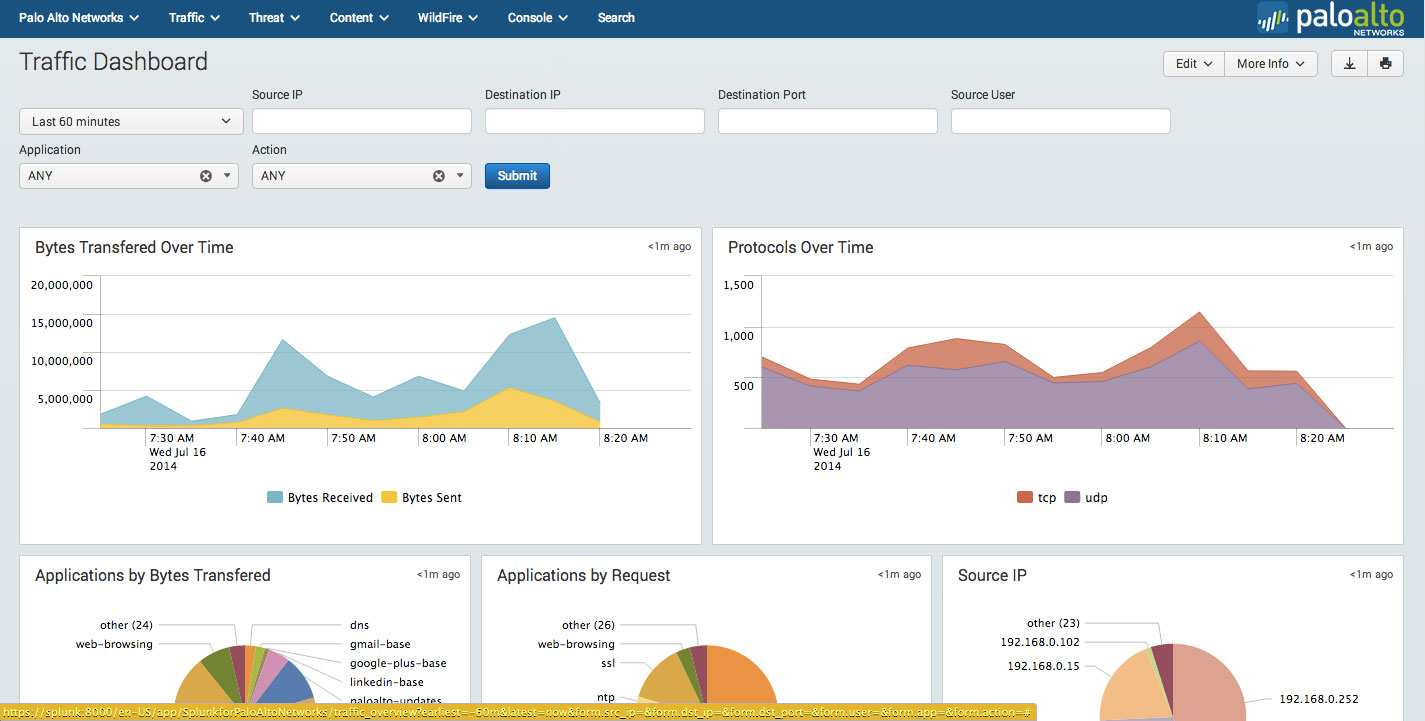
I have Splunk implemented in my lab taking a syslog feed from Panorama that's managing 3 PA firewalls. Palo Alto Networks has a really nice FREE Splunk App to present and analyze the data sent to Splunk from the PA firewalls or in my case, Panorama.
I hope this helps.
Kind regards,
Jeff
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-16-2014 06:25 AM
you can use any syslog server/service you want. enable on each policy the log forwarding to the syslog service and modify also the Log Settings to the syslog server.
we are using arcsight as syslog endpoint, because we creating some special reports and analyses.
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-16-2014 02:51 PM
I've used both Qradar and Splunk and both are strong platforms. I think that Qradar is stronger in customizing reports and fields for security. But Splunk is stronger in ease of use for creating reports on the fly.
Splunk does have an initiative to work more tightly with PA logging. They were an active participant to show the tools they have developed at Ignite this year and they do look good. But I have not used them in production.
I can't speak to implementation or cost, as I've only been a user/consumer of the services not the original installer.
ACE PanOS 6; ACE PanOS 7; ASE 3.0; PSE 7.0 Foundations & Associate in Platform; Cyber Security; Data Center
- 6672 Views
- 5 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Will the panorama log collector collect logs if synchronization with firewalls is disabled? in Panorama Discussions
- error: azure marketplace vm-series do not bootstrap in VM-Series in the Public Cloud
- XSOAR - for an environment of 26 Palo Alto Firewalls + 4 PANORAMA - is it worth it? in General Topics
- Panorama not showing log after upgrade to 10.1.8 in Panorama Discussions
- Setting up log collection in Panorama in Panorama Discussions




