- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Can't browse web pages
- LIVEcommunity
- Discussions
- General Topics
- Can't browse web pages
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-18-2021 02:51 AM
Hello all,
I'm new in Paloalto firewalls, i'm doing a migration from Fortigate to PA220. i configured all interfaces, router... but I'm struggling with Policies
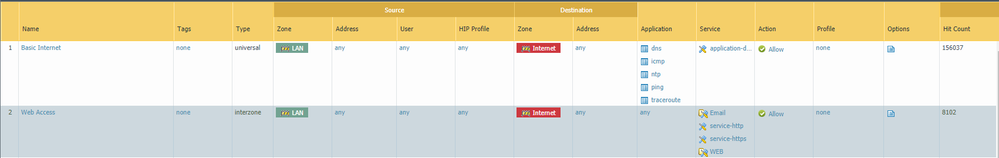
attached the basic policy i created to allow my LAN users to access internet:
After testing the PA:
- users can only ping to internet eg: 8.8.8.8
- users can access website using IP address not with the URL
PS: we have an internal DNS, Activedirectory, but in the PA220 i configured the DNS using 8.8.8.8 "Attached config"
PS: NAT configured "Attached config"
can you please advice if i'm missing something.
Thank you in advance
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-20-2021 02:19 AM
the service route is only used by the management interface of the firewall, it is used when the physical mgmt interface is located in an oob network that has no internet access
if you have any any open in all directions and you can only reach IP addresses, there must be something wrong with how DNS is resolved
can you check which DNS server is on your clients
what if you replace that with 1.1.1.1
in case your clients do dns lookups on your AD, can you see those connections in the firewall sessions and is there packets sent AND received ?
set up wireshark on client and AD to see if both see all packets
then, do the same with AD and it's upstream DNS: do you see dns queries leave and come back? what if you set the upstream ('Forwarders') to 1.1.1.1
PANgurus - Strata & Prisma Access specialist
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-18-2021 06:56 AM
the 8.8.8.8 you show in the screenshot is only used by the management interface of the firewall itself. you do have a security policy that would allow dns coming from your network to go out to the internet
did you add dns servers to your dhcp options so clients are issued with dns servers (your AD)? (and if the AD is being assigned, did you verify the AD has access to the internet?)
PANgurus - Strata & Prisma Access specialist
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-18-2021 07:12 AM
Thank you @reaper for your reply
I didn't configure a policy that would allow dns coming from DMZ" AD+DNS" to ==> Internet, i will configure it.
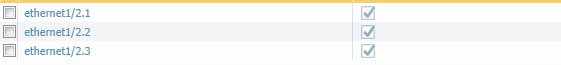
for your second point: the active directory is acting also as an DHCP so i configured a DHCP relay in the PaloAlto.
i have to verify if the AD have access to internet also.
the policies to go out to internet are correct or maybe i have to change something ?
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-18-2021 08:19 AM
Ah ha @wzahri ! With 3 interfaces things get a little more complex 🙂
You'll want the dhcp relay on the LAN interface pointing to the AD
Rules
From lan to dmz "all AD services (dns, smb, netbios, ....)" Allow
From dmz to untrust dns/ntp/ms-updates allow
From lan to untrust "web apps" allow
From lan+dmz to untrust block log
From lan+dmz interzone block log
PANgurus - Strata & Prisma Access specialist
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-18-2021 08:26 AM
Great thanks for your reply.
I will configure those policies, perform a test and back to you tomorrow.
Thanks again.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-20-2021 12:56 AM
hi@reaper
Unfortunately the same issue 😞
i tried to open all services on Any Any to test
Rules
From lan to dmz "all AD services (dns, smb, netbios, ....)" ==> Allow Any Any
From dmz to untrust dns/ntp/ms-updates allow==> Any Any
From lan to untrust "web apps" allow==> Any Any
do i have to configure something in "service routing" ?
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-20-2021 02:19 AM
the service route is only used by the management interface of the firewall, it is used when the physical mgmt interface is located in an oob network that has no internet access
if you have any any open in all directions and you can only reach IP addresses, there must be something wrong with how DNS is resolved
can you check which DNS server is on your clients
what if you replace that with 1.1.1.1
in case your clients do dns lookups on your AD, can you see those connections in the firewall sessions and is there packets sent AND received ?
set up wireshark on client and AD to see if both see all packets
then, do the same with AD and it's upstream DNS: do you see dns queries leave and come back? what if you set the upstream ('Forwarders') to 1.1.1.1
PANgurus - Strata & Prisma Access specialist
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-20-2021 05:23 AM
Thanks @reaper i will keep testing and TS, as you mentioned it's a DNS issue.
I will back to you
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-26-2021 02:51 AM
Hi @reaper
Yes it was a DNS Issue. i changed the DNS config in the AD. it's works fine now.
Thank you for your help.
- 1 accepted solution
- 6674 Views
- 8 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Foward Trust Cert and MacBook Pro in General Topics
- MacOSX Tahoe 26.4.1 (25E253) / Global Protect 6.3.3: Network is unreachable in GlobalProtect Discussions
- What PAN‑OS version should we choose as the recommended release today? in General Topics
- PA-450R ethernet port in Panorama Discussions
- Cortex XDR Tenant Auto-Upgrade 3.17 → 5.0: UI mixed theme, AI pages stuck loading, Marketplace/Playbook Catalog empty + ingestion quota warning in Cortex XDR Discussions