- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Configuring local and LDAP source users in Policies
- LIVEcommunity
- Discussions
- General Topics
- Re: Configuring local and LDAP source users in Policies
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-02-2015 12:32 PM
I have internal employees using VPN and also outside vendors with VPN accounts. In creating the policies (ex. allow employees to all internal servers while only allowing vendor VPN access to specific hosts) it appears that I can only choose LDAP users/groups as the source user. The drop-down only shows AD groups/users. I want to be able to select from the local users database as well. How can I go about this? Any given policy would be for either LDAP or local user authentication. I do have separate authentication profiles for both employee VPN (using LDAP) and vendor VPN (using local user database).
Thanks,
Ken
- Labels:
-
Configuration
-
Networking
-
Set Up
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-03-2015 11:27 AM
As a follow up- Palo Alto support responded stating that local users/groups can be used in policies but need to be manually entered into the User/Select field. I've tested this and it appears to do the trick. I can now control access to a local database VPN user via policy.
Thanks for the quick responses.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-02-2015 12:42 PM
Hi Ken,
On the drop down list for the source user, you should also be able to see local users. If that is not populating make sure you have committed the configuration and also try to search for the local user in question. Thank you.
Hope this helps.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-02-2015 12:52 PM
Thanks for the response. I have committed the configuration and when I type in the dropdown list for users, only my LDAP users are shown with the <domain>\<username> format. None of my local users appear. I'm sure there's something simple I'm overlooking as I'm new to PAN devices, but I sure can't determine what it may be.
Thanks,
Ken
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-02-2015 01:00 PM
Hi Ken,
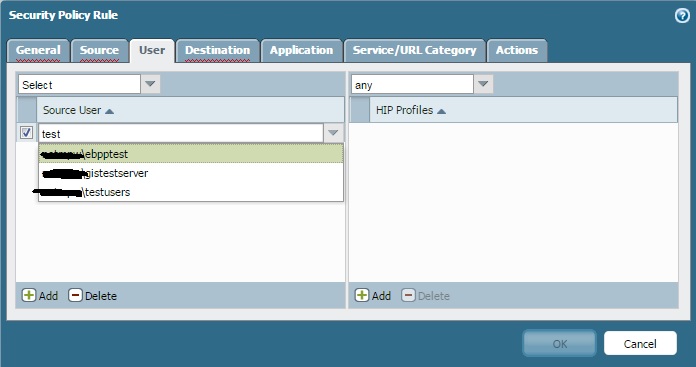
Create a test user name test, enable the user commit the changes. Then go to security policy and under user, search for test. Please attach the snap shot like I have done. Thank you.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-03-2015 06:23 AM
I've created the local account test and it is enabled.
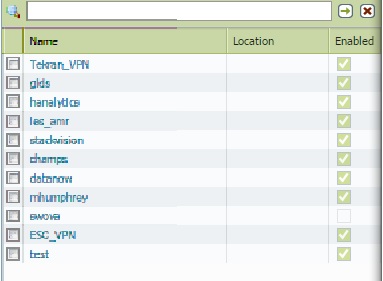
And here is the search results for a security policy. The only user names that appear are from LDAP. Searching on any of the other local users shows no results either.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-03-2015 06:45 AM
Authd process is handled by management server. Could you restart the management-server on the device, this will not affect the dataplane traffic. If restarting still does not help, then I will suggest opening a case with palo alto.
>debug software restart management-server
Let me know if that helps. Thank you.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-03-2015 07:41 AM
Thanks for your response, however the problem still exists. I'll open a ticket with Palo Alto and see what I can find out.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-03-2015 11:27 AM
As a follow up- Palo Alto support responded stating that local users/groups can be used in policies but need to be manually entered into the User/Select field. I've tested this and it appears to do the trick. I can now control access to a local database VPN user via policy.
Thanks for the quick responses.
- 1 accepted solution
- 10260 Views
- 7 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Palo Alto Site to Site VPN ipsec tunnel up but unable to ping Source to destination in Next-Generation Firewall Discussions
- [SOLVED] GPUDATE /FORCE DOESN'T WORK WITH GLOBAL PROTECT in GlobalProtect Discussions
- EDL Capacity Reached but Lists Show Empty / Default Entry (0.0.0.0/32) – Panorama Multi-VSYS Setup Post: in General Topics
- Handling voip behind ION 1200S in Prisma SD-WAN Discussions
- NAT Policy Zone Selection for DNAT (and DNAT+SNAT) — Is My Understanding Correct? in Next-Generation Firewall Discussions




