- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Custom report analyse trafic on object
- LIVEcommunity
- Discussions
- General Topics
- Custom report analyse trafic on object
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Custom report analyse trafic on object
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-07-2021 07:22 AM - edited 09-07-2021 07:28 AM
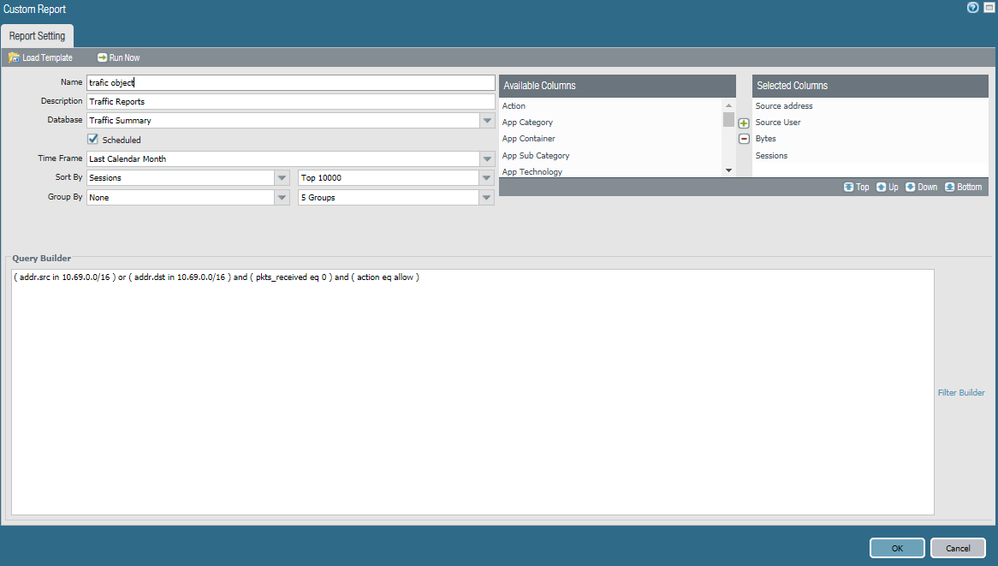
I want to check all my object addresses with zero traffic to clean up my flow rules.
Can I replace my sources and destination IP with an "all IP" setting ?
Can you help me ?
section "Query Builder" does not work (see image)
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-07-2021 07:46 AM
To filter for any IP on the custom report, remove the src and dst filters. That report is a traffic report and is only going to report traffic over the last calendar month, it will not show unhit objects.
If you're looking at cleaning up rules, why not use the policy optimizer and look at unused rules?
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-08-2021 05:39 AM - edited 09-08-2021 07:31 AM
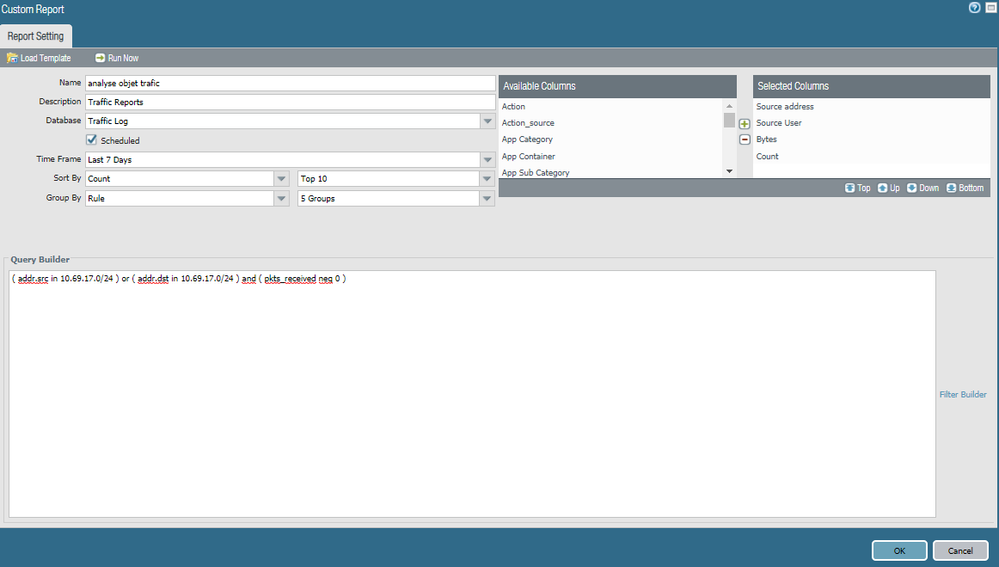
I want to see the unused objects
in my object groups
the policy optimizer does not allow me that.
I changed the database to "traffic log".
(see picture)
I have a lot of subnet I have to filter by subnet and match "(pkts_received neq 0)
"?
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-10-2021 12:07 PM
I believe you may be able to use the Expedition tool to achieve what you're looking for. I have only briefly used the tool so someone else may be better at answering this but it looks like there is another thread discussing this.
Here is what TomYoung said in regards to this:
"
Expedition can make changes directly on the firewall. It has been a while since I have done it, but I believe you add the device under Devices and make the changes under your project > Export > API Output Manager. You should know the difference between Atomic and SubAtomic changes.
You could also use "show | match <object-name>" in configuration mode (set format) and see where it is used in the configuration. If the only line is the address object, it is not used.
You could also delete the object. If it is used, you will get an error right away. If not, the delete will be accepted in the candidate configuration. UPDATE: I saw this on Reddit, and it works. Select all the objects. (This may not be quick depending upon the number of objects.) Select Delete and Yes. All unused objects are deleted. All used objects produce an error and are kept. Use Device > Config Audit to see which objects were deleted.
Once Expedition is setup, that is the quickest and easiest."
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-10-2021 12:08 PM
Here is the link to the thread and expedition tool.
https://www.paloaltonetworks.com/products/secure-the-network/next-generation-firewall/migration-tool
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-14-2021 02:34 AM
Hello,
Thank you for your answer.
I have already installed and used a palo expedtion virtual machine.
Palo expedition does not allow me to check objects traffic, it only shows unused objects.
I need to know if there is any traffic on the objects ( pkts_received neq 0 ) because some objects are seen as used because they are in object groups.
Can I use a palo alto script to check that or report ?
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-14-2021 04:09 AM - edited 09-14-2021 04:10 AM
Hi @navaro06 ,
- First you have syntactical error in your query. You need to put the or in additional brakets, without them you query is searching for "dst network in 10.69.17.0/24 and zero received bytes" OR "any log where src network is 10.69.17.0/24. In addition you can use "addr" to search for given prefix in source and destination, so it should look like this:
(addr in 10.69.17.0/24) and ( pkts_received eq 0)
it is the same as ((addr.src in 10.69.17.0/24) or (addr.dst in 10.69.17.0/24)) and ( pkts_received eq 0)
- Even tho the above query is correct it still wouldn't provide the result you need. Think for a moment - the reports are generated by quering the traffic logs and aggregating the result in table. If there is object/network, that has never generated traffic, nor it was received traffic (aka unused), you will never see traffic logs for it, right? So searching traffic logs for traffic that never happend is pointless.
I personally also doesn't have much of experiance with Expedition, but as @bafergel suggested it may be your solution. In the latest version of Expedition tool, you have option to forward the traffic logs the tool, that way the analytic engine will be able to gather information which rule, which object and which group have been used (because it now have the actual rulebase and the traffic log, so it can map which object have been seen in the logs and which not). But for that purpose you will need bigger storage for the Expedition - in order to store longer period of logs.
Your other option would be to invest in 3rd party tools like FireMon and Tufin. Couple years ago I was using FireMon and I remember it was very powerfull it can give you very detailed report. Unfortunately I don't believe you can achive the same result with firewall buil-in reporting.
- 5560 Views
- 7 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!