- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
HA traffic through Cisco Switch
- LIVEcommunity
- Discussions
- General Topics
- HA traffic through Cisco Switch
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
HA traffic through Cisco Switch
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-29-2020 06:26 AM
Hi Team ,
Can we route HA traffic between two 3260 firewalls through cisco switch using L2 vlan.
My requirement is to run firewalls in HA and devices will be in different buildings. Buildings are connected with dark fiber. As PAN dedicated HA ports are ethernet i have to use another converter or switch to make them communicate in HA ports.
i did l2 vlan on 9500 switch but HA1 never comes up.
Can we do like this?
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-29-2020 06:49 AM - edited 01-29-2020 07:19 AM
@AvinashKukkapalli wrote:Hi Team ,
Can we route HA traffic between two 3260 firewalls through cisco switch using L2 vlan.My requirement is to run firewalls in HA and devices will be in different buildings. Buildings are connected with dark fiber. As PAN dedicated HA ports are ethernet i have to use another converter or switch to make them communicate in HA ports.
i did l2 vlan on 9500 switch but HA1 never comes up.
Can we do like this?
Technically no, but you can switch the traffic...Ok, I'm done splitting hairs.
You 10000% can do this. As long as both switches participate in the same layer 2 domain it should work without issue. (This would also mean that the link the switches are connected has the access VLAN on the trunk the HA-1 ports are on)
Say you have FW-1 connected to SW-1 with the FW-1 HA-1 with the IP of 10.10.10.1 on an Access VLAN 10 to SW-1
You'd need FW-2 connected to SW-2 with the FW-2 HA-1 configured with the IP of 10.10.10.2 on Access VLAN 10 to SW-2.
You would do the same for HA-2
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-29-2020 06:57 AM
Hi
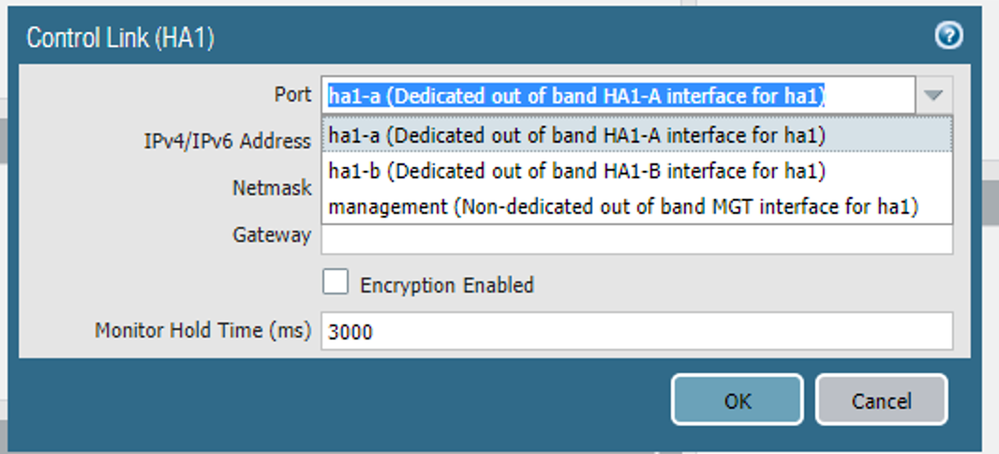
HA1 syncs configuration and heartbeats, it uses dedicated-ha1a/ha1b ports (by default)
HA2 syncs the session table, it uses a dedicated HSCI port (10gb fiber)
You want both up for proper High Availability.
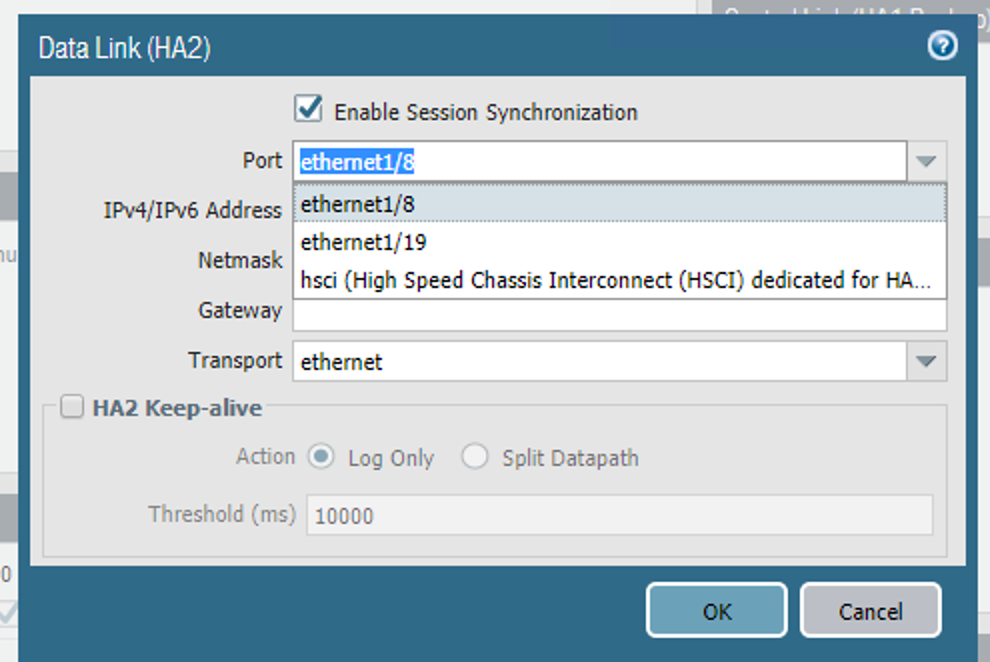
You can assign a Dataplane port to be of type 'HA' and then you can use it instead of the dedicated HA ports (it will be available in the drop down list under HA1/HA1 backup/HA2/HA2 backup).
This can give you the option to use ethernet1/19 as type HA, used by HA1, connected over a fiber link with appropriate GBIC on both sides thus avoiding a converter.
Configuration wise:
Firewall-1
Control Link (HA1) IPv4: 1.1.1.1 / 255.255.255.248
Peer HA1 IP Address (in the Setup page): 1.1.1.2
Firewall-2
Control Link (HA1) IPv4: 1.1.1.2 / 255.255.255.248
Peer HA1 IP Address (in the Setup page): 1.1.1.1
It's a bit tricky to explain all the possible scenarios, I hope it was clear. Just remember that each FW needs to know the IP address of it's peer for HA1 to come up. Lastly, use HA1 backup as management port and put 'Backup Peer HA1 IP Address=MGMT-IP of other FW.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-29-2020 07:55 AM
I changed data port type to HA but i never get that port in dropdown for HA1 , Only for HA2 i am able to select that data port..
So i used L2 vlan but that is not helping
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-29-2020 08:03 AM
Attached screen shots for reference
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-29-2020 08:11 AM
@AvinashKukkapalli wrote:Attached screen shots for reference
I refer you to my posts in this thread. https://live.paloaltonetworks.com/t5/General-Topics/PA-3260-and-using-non-dedicated-as-HA1-interface...
Are you trying to use a different pot for HA-1 because you need fiber? HA-1 has to be used on the dedicated port.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-29-2020 08:30 AM
I am good , i see one typo error for peer ip.
thanks for all help
- 10292 Views
- 6 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- PAC File for Prisma Access China in Prisma Access Discussions
- XQL - Hostfirewall events in Cortex XDR Discussions
- Palo Windows ARP Issue - Windows Hosts Not Installing ARP info in Next-Generation Firewall Discussions
- Existing traffic stops suddenly, and changing of interface MTU resolved it. in General Topics
- Palo Alto 3410 Firewall 100% DP CPU spike in Next-Generation Firewall Discussions