- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
How to SSL Bypass based on application
- LIVEcommunity
- Discussions
- General Topics
- How to SSL Bypass based on application
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
How to SSL Bypass based on application
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-09-2017 02:15 AM - edited 08-09-2017 02:59 AM
Hello,
I wanted to share a solution I have implemented recntly.
Bypassing SSL Decryption based on applications was a request I had from many customers.
I know there is an FR for that. but until then, with PAN-OS 8, it is possible to achieve differently.
I had a specific scenario where one of my customers had to connect to his customer's Pulse Secure SSL VPN device (collaboration feature).
When using SSL Decryption on his PAN NGFW, the connection was failing and he had to manualy add the IP address of his customer to a bypass rule.
when you have hundreds of customers using that solution, and you need to add their IP address manualy, it is becoming problematic.
The idea is, dynamically adding the destination address to an SSL Bypass rule.
Here is how it goes...
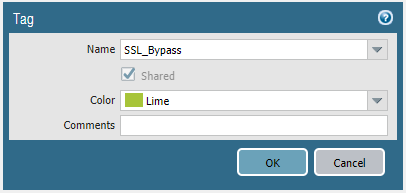
Create a tag - Objects --> Tags:
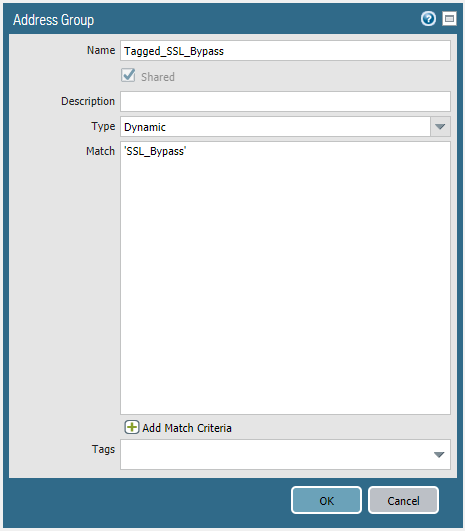
Create a Dynamic Address Group - Objects --> Address Groups
Add the previously created tag's name as a match
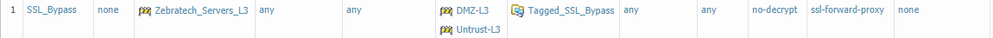
Create a decryption rule with the new Address Group object as a destination with a 'no-decrypt' action. (pay attention to rules order)
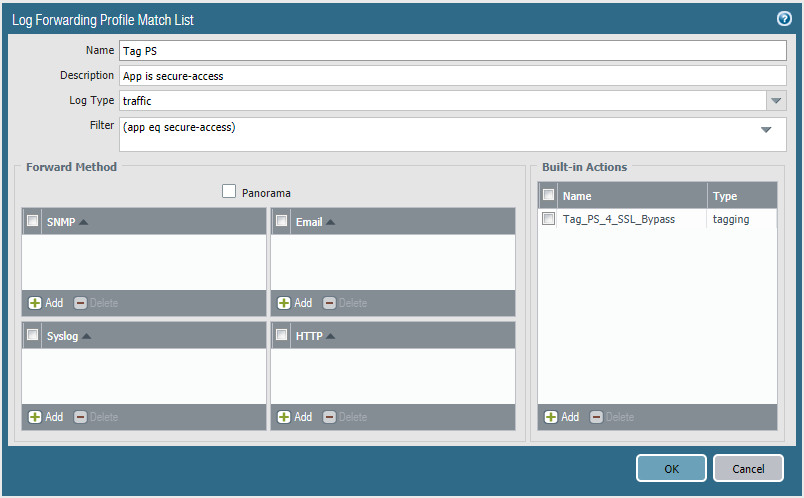
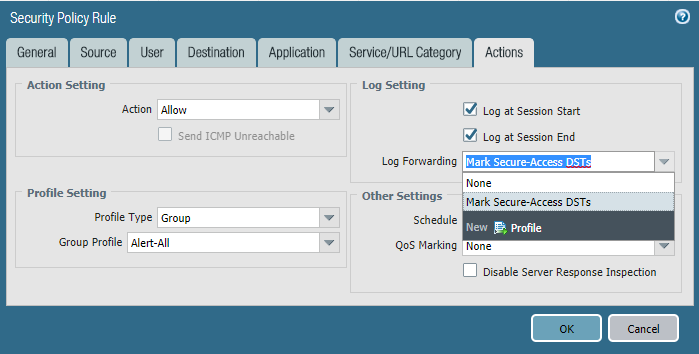
Create a Log Forwarding profile with a filter that will catch a specific application ('secure-access' for my scenario). Use Traffic as the log type.
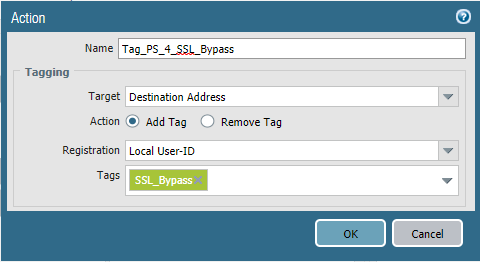
Add a Built-in Action to tag the destination address
Add the Log forwarding profile to the security rule that permitted the desired application originally.
Commit
Access the desired website (application), and verify the address has successfully been dynamically registered to the dynamic address group (click 'more'), and successfully SSL Bypassed.
Please share your thoughts..
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-09-2017 03:40 AM - edited 08-09-2017 03:41 AM
Another really nice and creative way of using the awesome Log Forwarding Profile feature in PAN-OS 8!
- 8923 Views
- 2 replies
- 8 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Does Prisma Browser support device-based Conditional Access (device ID / compliance)? in Prisma Access Discussions
- Avaya ports Blocking in General Topics
- Cortex XDR Tenant Auto-Upgrade 3.17 → 5.0: UI mixed theme, AI pages stuck loading, Marketplace/Playbook Catalog empty + ingestion quota warning in Cortex XDR Discussions
- [SOLVED] - NGFW The Connection To Global Protect On The IPads Times Out!! in GlobalProtect Discussions
- How to Handle High-Volume Email Events in XSOAR Without Overloading the System in Cortex XSOAR Discussions