- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
I'm unable to use Remote desktop from internet to PC in Trust zone
- LIVEcommunity
- Discussions
- General Topics
- I'm unable to use Remote desktop from internet to PC in Trust zone
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-15-2017 07:08 AM - edited 10-15-2017 07:16 AM
Hello all,
I wanna Remote desktop from my PC in home to PC in my company but not success
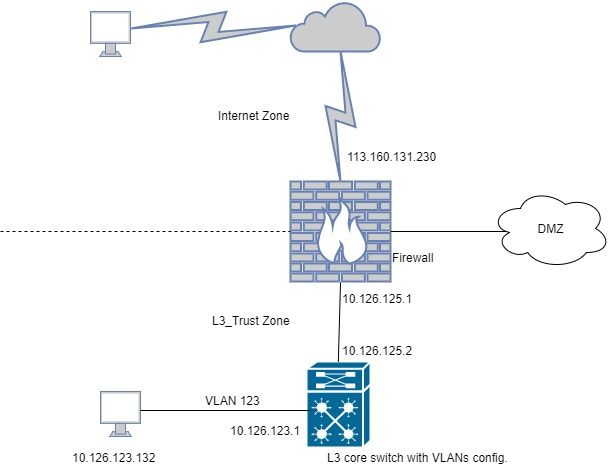
This is my connection diagram
I wanna remote to PC 10.126.123.132 (belong to VLAN 123, I use several VLANs in Core switch) but not success, NAT seems not to work, there's no traffic logs
This is my config..
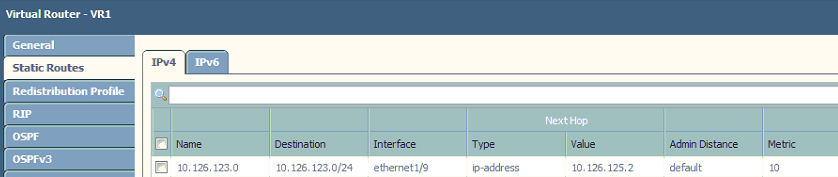

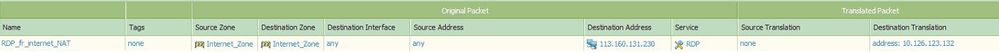
I can remote from internet to a server in DMZ zone successfully but L3_Trust zone, so I think because of using VLAN in core switch, it requires some other config.. Please help me 🙂
P/S: The public IP in the pictures is just an example IP
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-16-2017 02:55 AM
One more think - If you don't see logs for your attempts, please check if you have enabled log for default Intra and Inter zone security policy? If traffic doesn't match any explicit rule is probably being dropped by the default zone rules, and by default they are not logging.
another you can check is run test security-policy-match <fill in the rest> under the CLI
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-17-2017 05:35 PM
the reason there is no session on the firewall because i think it dropping the packet due to security rule . You can confirm this by creating a deny alll rule at the bottom and see if your traffic hits this rule.
The service object rdp that you have created, make sure you just put 3389 in destination port and leave the source port as blank and the protocol is tcp.
If this still does not work, open the rule to allow any service. For security just mention your public ip as source.
Check if you are still hitting the same rule or the default deny.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-17-2017 07:21 PM - edited 10-17-2017 07:55 PM
Yes, I use a "Deny all" rule, I'm sure RDP service is correct with 3389 port 'cause I'm using it to remote to a server in DMZ zone. I create rule with permit access from my PC in internet to any zone and any address in internal network. But it's still not working and there's no any log except ping or telnet (but ping and telnet is not success and destination address is not NATed)
It seems hard to connect directly from internet to L3_trurst zone, so I'll use Globalprotect to setup VPN client to site.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-17-2017 08:06 PM
I am having the same issue exaclty you facing now, All the while is working fine, The issue is onli happen i update the PA to 8.0.5, Are you using the same OS version.
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-17-2017 08:08 PM
I'm using 6.1.16, I think it's not relate to PAN-OS version
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-17-2017 08:12 PM
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-17-2017 09:03 PM
Can you create a ticket support in customer support page? I tried but in step 3, there's no checkbox to select device
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-17-2017 09:37 PM
To open case with PAN Tac, I think you need to engage with your local ASC tReam assist you to create the support ticket.
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-18-2017 06:50 AM
Do you have an active support contract on your device?
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-18-2017 07:41 AM
Hi Hongson -- Think you're looking for a U turn NAT. Since I don't know your network configuration.
Please see this article:
https://live.paloaltonetworks.com/t5/Configuration-Articles/How-to-Configure-U-Turn-NAT/ta-p/61889
Or contact PAN-TAC. Hope that works for you.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-19-2017 06:44 PM
@BPryI got 1 year support contract
Thank you guys, I've setup Globalprotect to establish VPN to my PC in workplace, it's pretty cool 🙂
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-20-2017 12:44 AM
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-20-2017 01:11 AM
Holy sh***!! Yes, you're right, I'm using Dos protection too and forgot about it :))
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-20-2017 01:13 AM
Try to chnage the action on your dos policy from deny to protect
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-20-2017 01:35 AM
Yes, you're right, I got this problem once time before, when setup remote from the internet to DMZ, I also fixed it by changed the Dos protection action from deny to protect. But after along time, I completly forgot about Dos protection
- 20623 Views
- 32 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- New cert GP cert prompt for people testing Yubikeys for windows logon in GlobalProtect Discussions
- False positive (generic.ml): HelpDesk Viewer in VirusTotal
- False Positive request for RemotePC HelpDesk Viewer in VirusTotal
- False positive : HelpDesk Viewer in VirusTotal
- False positive (generic.ml): HelpDesk Viewer in VirusTotal