- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Instagram allowed in the security policy, but the pictures are not displayed correctly on the website
- LIVEcommunity
- Discussions
- General Topics
- Instagram allowed in the security policy, but the pictures are not displayed correctly on the website
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Instagram allowed in the security policy, but the pictures are not displayed correctly on the website
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-04-2021 05:42 AM
Dear Palo Alto Community Members,
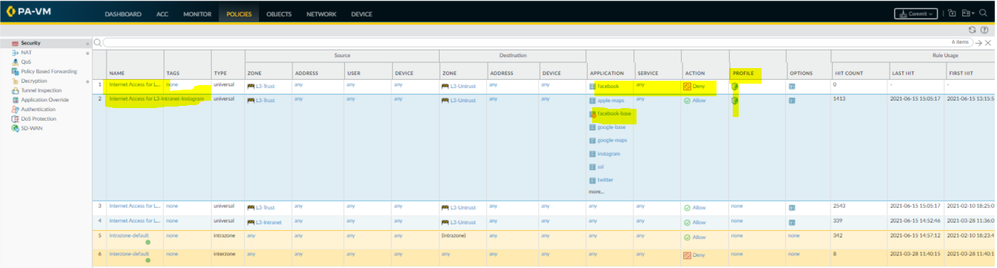
I'm tiring to set up a security policy based on app-ID allowing Instagram but blocking Facebook.
Unfortunately, I can't get it to work, and I'm not sure what I might be missing here.
The security policy allows all the needed applications, and I've double-checked and added all the required application dependencies, but when going to the webpage we've noticed that the pictures are not loading.
After further testing, we could confirm that after allowing facebook-base, the images were loading fine. But if we remove facebook-base, Instagram no longer will load the photos although the website will work fine.
This has been tested in Chrome, Firefox, and Edge, all give the same results and display the same (without the pictures).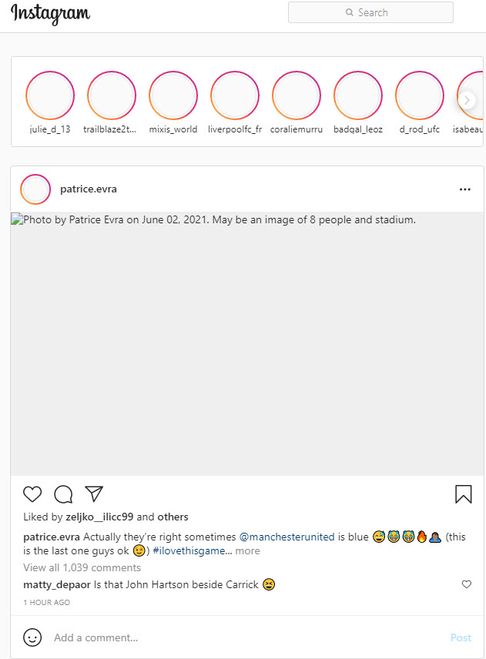
Is it possible this is a restriction due to the fact that Facebook owns Instagram, and they likely share the infrastructure where the images are being hosted?
Is it makes sense to add the "instagram-base" to allowed applications in the policy if Instagram is already listed there?
Is there any known issue that could explain my issue, or I'm just simply miss something in configuration?
Could some please share his thoughts on this issue and advice?
I will really appreciate some help resolving it.
Thank you in advance!
Regards,
Arek
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-04-2021 08:43 AM
Hi @A_Adamski
I assume you are already right with your assumption, that this issue is because instagram is owned by facebook and they probably share some parts of the infrastructure. Adding instagram- base is not required as you have already added instagram.
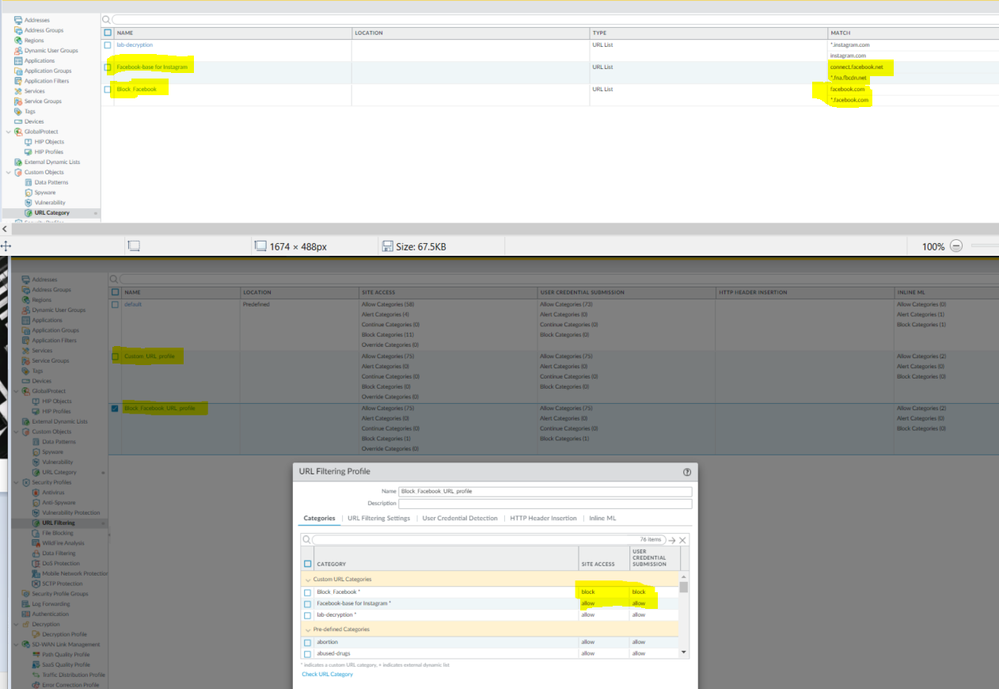
Did you check the urls, that are opened in the sessions where the firewalls detect the application facebook base? With this information you could create a new security policy where you add the application facebook-base together with a custom url category where you specify only the urls required to load the images.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-07-2021 01:12 PM
Hi @A_Adamski ,
@nikoolayy1 has post a very instersting topic a while ago, you may want to check it https://live.paloaltonetworks.com/t5/automation-api-discussions/version-10-no-7-byte-limit-for-sinat...
It sounds like really intersting idea, but I personaly haven't any chance to try it.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-08-2021 03:53 AM
Hi @Remo,
Thank you for your response and the suggestion.
It's kinda strange as I thought that even if the change within Instagram, and moving ownership (and most likely some part of infrastructure and services) to Facebook, should not change how the application is recognized/classified by the firewall.
So I guess there is no way to get it to work when using just the application IDs, right?
*Is this not maybe something for the Palo Alto team to look into internally and update/correct the APP-ID info for Instagram?
I think I do not have many options left here, and I'll need to try and follow your advice and add the custom URL category to the policy.
I wish you a great day ahead!
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-09-2021 04:21 AM
For application request to Palo Alto if needed follow:
https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000Clu2CAC
If they say no you may try to write it youself.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-15-2021 03:53 PM
Hi @vsys_remo,
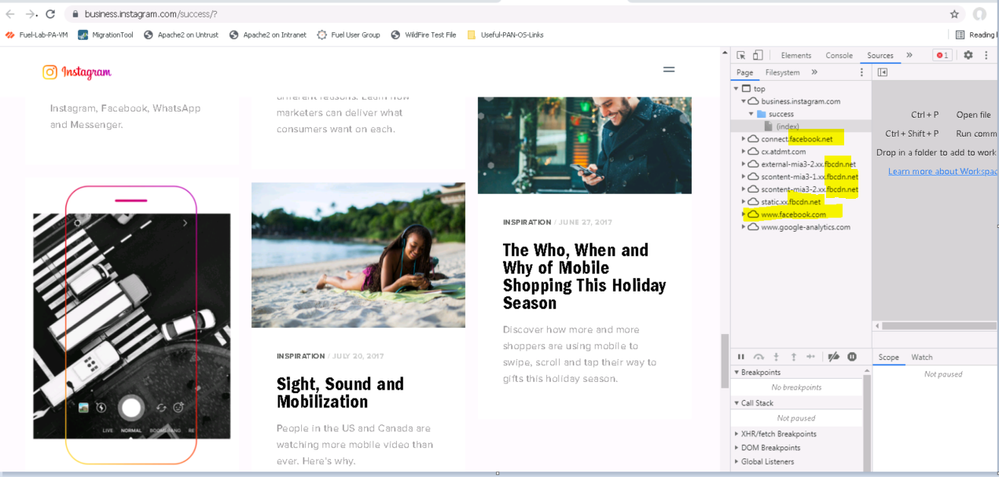
I've tried to create the custom URL category and used the URL profile attached to the security policy allowing the facebook-base and the URLs I've listed in the URL category. During my checks I could see that the Instagram website is connecting to some sites related to Facebook: "connect.facebook.net", "*.fna.fbcdn.net", and the "facebook.com".
*(I assume the second one belongs to Facebook too)
The goal here is to allow access to the Instagram website (along with the pictures which for some reason seems to be hosted at the Facebook site), but at the same time to block access to Facebook.
So I've created an additional security policy on top of the one allowing Instagram traffic in order to block access to the Facebook application and I've used another custom URL where I've listed the "facebook.com" with action to "block".
Unfortunately, this did not work as I've expected and I was still able to access the facebook.com websites. The Instagram website was working correctly and I could see the pictures loading fine, but at the same time, Facebook.com was still not blocked (and that's not what we want).
This should work, so I'm really not sure what I've might be still missing.
Could you please help me understand if I'm doing something wrong? And maybe even point me out in the correct direction?
I will appreciate any help on that matter.
Thank you in advance and kind regards,
Arek
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-16-2021 01:15 AM
I guess, that I've found my mistake. The first security policy (on the top to block facebook.com) should be "allowing" the traffic so then it could be blocked by the URL profile.... but in my case, I've set that policy to "deny" so the profile will never kick in.
But it does not explain why did I not have any hits for that rule. So I will be requesting access to the PA lab so I could play with it a bit more.
Please let me know in case if someone has any additional suggestions
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-16-2021 07:02 AM
Hi Alexander,
I've checked the conversation, but I do not really follow it... I guess it's out of my understanding as I'm not sure how it's connected to my issue nor how it could help me.
I'm sorry but I'm not so experienced and knowledgeable in regards to Palo Alto as I would like to be.
And thanks for your help!
Cheers,
Arek
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-16-2021 07:05 AM
Hi Nicolaj,
Thanks for sharing, this might be useful info and a place to start.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-30-2021 05:04 PM
Are you running SSL decryption? I had this problem with instagram when TLS 1.3 was first implemented but it's been working fine for a while. Just recently instagram stopped working with decryption turned on and the app would just crash when opening. I had to add an SSL decryption exclusion for the following to get it to work again:
*.instagram.com
instagram.*.fna.fbcdn.net
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-07-2021 05:54 AM
Hi M_kallergis,
Thank you for your input.
We've used a generic wildcard to catch and encrypt all the traffic (*.*).
The nature of the problem will not change if we specify other wildcards, as we will still be forced to add facebook-base to get the Instagram page to load fully.
In the meantime, the customer decided to go some other way to achieve this.
It will be nice to know if someone has found a way to get it to work, cuz unfortunately I will not be spending any more time on this issue.
Thank you all for your help!
Cheers,
Arek
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-07-2021 10:33 AM
+1 to SSL decryption here. Some services start using QUIC (are you blocking that at the top of the hierarchy?) which sometimes confuses the APP-ID. If you are able to get it to default to a decrypt-able cipher suite, best shot.
- 14639 Views
- 11 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Why do the same Windows Server data collected using XDRC and WEC agents show different statuses in the following fields? in Cortex XSIAM Discussions
- Configure GlobalProtect to Facilitate Multi-Factor Authentication Notifications in GlobalProtect Discussions
- Why does not "summarize-mobile-user-routes" display on running-config.xml ? Related to PAN-232831. in Prisma Access Discussions
- Problem with viewing and downloading 30-day logs on Panorama server in Panorama Discussions
- Instagram allows but does not display the login page in General Topics