- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Is the behavior in my tests normal or maybe I missed something?
- LIVEcommunity
- Discussions
- General Topics
- Re: Is the behavior in my tests normal or maybe I missed something?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Is the behavior in my tests normal or maybe I missed something?
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-19-2015 11:27 AM
I have a specific question. Our firewalls are able to decompress some files like .zip or gzip and after that we are able to analyze their content and detect some malicious files with threat prevention or WildFire.
For the .cab file, the cabinet file compressed by Windows, which is not cyphered, I saw some tests and I was surprised that the content of a cab file is not analyzed. I created my own cab file with a malicious file inside. I understand that normally the cab files are signed by Microsoft and trust. But recently we have a lot of malware campaigns with some cab files in the emails attachment. I want to know if we are able to protect users from this type of campaign?
Do you know if the behavior in my tests are normal or maybe I missed something?
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-20-2015 07:54 AM
Hello,
Have you tried selecting File type as cab in file blocking profile with action set to Forward to see if wildfire detects malware?
Regards,
Hari Yadavalli
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-20-2015 08:59 AM
Efurtado,
In addition to the above statement, can you confirm that the zip archives were not password protected or zipped into multiple layers?
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-23-2015 02:28 AM
Hi Hari,
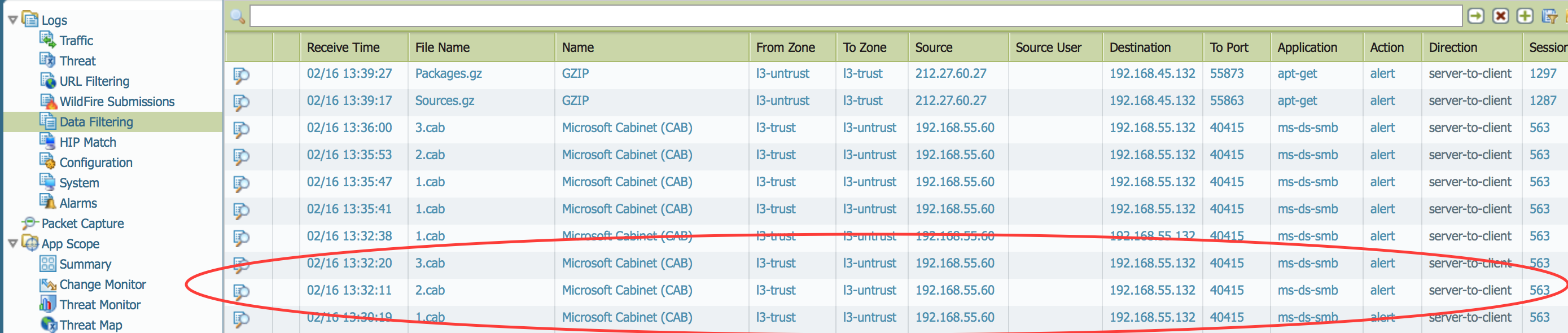
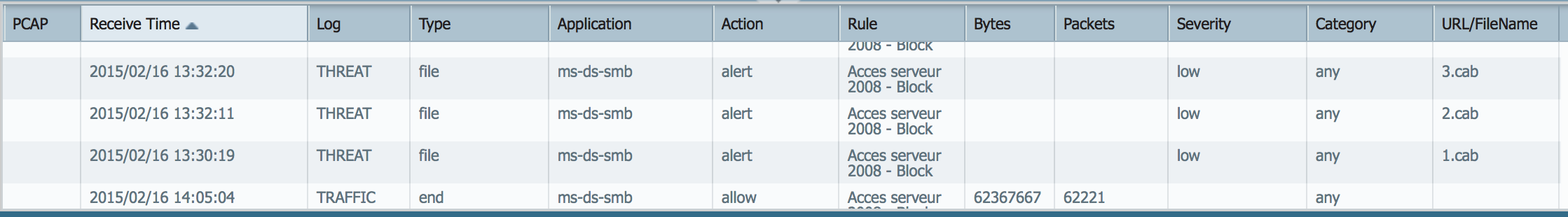
Yes of course, I created a "file blocking profile" with a default action for all files to forward. I created 3 cabinet files with the following command line : makecab.exe. Each cab file contains a malware or virus. I think when you're creating a cab file, there is no protection by password something like that.
In the log file, you can see the status "alert".
Thanks for your help.
Regards,
Arnaud Besnard
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-25-2015 01:11 PM
Hello Arnaud,
What is the action set for 'smb' decoder in antivirus profile?
Regards,
Hari Yadavalli
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-26-2015 12:54 AM
Hi Hari,
In the antivirus profile, the action is "block" for all decoder and even for wildfire.
Regards,
Arnaud BESNARD
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-26-2015 08:57 PM
Hi,
PAN does not support any compressed files except zip/gzip because PAN scans malware by stream-based.
Following KB might be helpful for you even it's talking about IPS.
- 4385 Views
- 6 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Suspicious executable detected Microsoft Store Purchase App in Cortex XDR Discussions
- Regarding existing logs when adding an extended disk to a VMFW using AWS. in VM-Series in the Private Cloud
- CVE-2026-0261 PAN-OS_ Authenticated Admin Command Injection Vulnerability in Next-Generation Firewall Discussions
- EDL MS Intune All URL misses an entry in General Topics
- Cannot add BIOC rule to restriction profiles in Cortex XDR Discussions




