- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
ISP failover with Path Monitoring help? Incomplete Aged-out traffic issue. PA 3020
- LIVEcommunity
- Discussions
- General Topics
- ISP failover with Path Monitoring help? Incomplete Aged-out traffic issue. PA 3020
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
ISP failover with Path Monitoring help? Incomplete Aged-out traffic issue. PA 3020
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-18-2019 08:56 PM - edited 01-18-2019 09:54 PM
I am using a PA 3020.
We have an ISP1 which is our main corp internet.
We have an ISP2 which is also our active Guest network.
I'm trying to configure ISP1 virtual router with Path Monitoring so that if fails pinging a group of IP's it fails over to ISP2 virtual router.
Well I have configured Path Monitoring and can trigger it accordingly by monitoring a dead IP.
However I cannot get to the internet after this kicks in.
From monitor tab I check my test laptop and the From Zone is till the same, and To Zone has changed. But everything says "aged-out" in the "Session End Reason" column.
Any ideas if there is another issue I need to check?
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-21-2019 09:09 AM
Why do you have 2 virtual routers?
Easier to have 1 virtual router.
Your could use PBF to route Guest network out from ISP2 link.
Check SNAT IP on outgoing traffic.
Does outgoing traffic match correct NAT rule and it is sourcing from ISP2 public IP?
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-21-2019 09:24 AM
The 2 Virtual Routers existed before I inherited the management of the PA (inherited by network admin leaving, which hopefully explains my newbiness).
I am not sure I can swap out everything with 1 single Virtual Router and a PBF right now.
I was hoping to just get Path Monitoring setup with current setup to get ISP redundancy soon, and then have some cushion later to play around with 1 VR and PBF.
When I tested the ISP failover with how it is setup now, enabling Path Monitorign to ping a phantom IP (32.32.32.32), it just disconencted my laptop and I couldn't ping or get to websites.
When I checked the traffic log, I could see my requests going to new destiation zone and interface of ISP2, and ISP2's NAT IP.
But on my laptop I just got errors in my browser when trying websites, and no reply when pinging 8.8.8.8 in cmd prompt.
The "General" application log says "incomplete" though for that traffic.
PA support advised maybe it is another switch, that the PA is handing traffic back into our network but my laptop is not getting it? I am not sure what to check to troubleshoot this. we do have 2 HP switches in the MDF
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-21-2019 09:31 AM
If VR1 routes traffic to VR2 and VR2 to internet.
Does VR2 have route back towards VR1 for return traffic?
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-21-2019 09:34 AM
Well I'm not sure. Would this be established via a Static Route within the VR?
As far as VR2 route back to VR1, this could be setup so only when it is failed over? Because on a normal day to day basis, VR2 with ISP2 is used all day as a guest network and functions fine.
It's just trying to leverage it as a failover for our ISP1 and corp zone when ISP1 goes down.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-21-2019 10:04 AM
Let's assume that internal network is 10.0.0.0/24 and guest network is 192.168.1.0/24
In this case you need to have static route in VR2 to send traffic towards 10.0.0.0/24 towards VR1.
It will not affect traffic from VR2 to internet because this has default route 0.0.0.0/0 and it would not allow guest traffic to internal becvause Security Policy will take care of that part.
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-21-2019 10:19 AM
Ahhh ok that makes sense. I will try that. So that would still be require if I did Policy Based forwarding too?
But if i consolidated to one VR it would make it easier ?
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-21-2019 10:43 AM
With 2VRs you still need routes between them.
PBF is checked before VR.
So if there is route in PBF then this will take precedence.
If no matching PBF then Palo falls back to routes in VR.
This allows you to have 1 VR and PBF that has logic "if traffic comes from Guest zone then send it towards ISP2 and monitor ISP2. If ISP2 is not available then fall back VR"
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-21-2019 11:47 AM
Well I will definitely first try the route setup next. I'm excited that it makes sense and am motivated to try this at the next earliest, possible maintenance window overnight versus weekend.
Let me give this a go, and report back. Hopefully you won't mind visiting back to see how it goes.
Thanks very much
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-21-2019 02:23 PM
Definitely let know how it went.
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-24-2019 08:29 AM
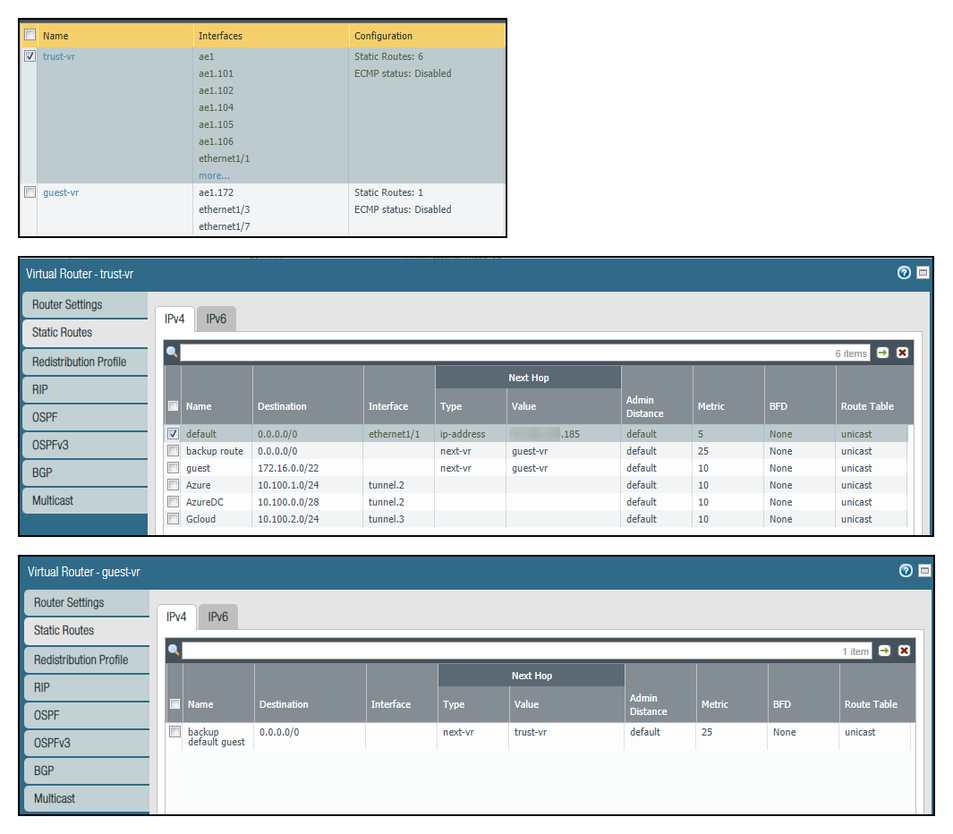
Sorry I meant to include screenshot earlier, if this helps identify any issues you see?
So basically, I need to add a route there on the "Virtual Router - guest-vr" to the subnet of computers that go through the "trust-vr" Virtual Router"?
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-25-2019 05:50 PM
That worked -- just added routes from the secondary VR to subnets of where our workstations were to go through the next vr.
Failover worked flawlessley. Not time to consider Policy based forwarding next.
Hope this helps the next average Joe!
Thanks for guidance, @Raido_Rattameister.
- 10502 Views
- 11 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- HA failover on Acitve Passive concerns in Next-Generation Firewall Discussions
- Tuning Panorama HA Timers to Stop False HA1 Alerts over MPLS in Panorama Discussions
- Conditional Advertisement / BGP Failover with Dual ISP — How to Remove ISP1 Routes on Internet Loss? in Next-Generation Firewall Discussions
- Tunnel Monitoring in Next-Generation Firewall Discussions
- IPSec HA Failover - Feature Request NSFR-I-26043 in General Topics