- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Output detailed HIP logs to syslog
- LIVEcommunity
- Discussions
- General Topics
- Output detailed HIP logs to syslog
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Output detailed HIP logs to syslog
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-11-2019 08:20 AM
Does anybody know how to output the detailed HIP match logs to syslog?
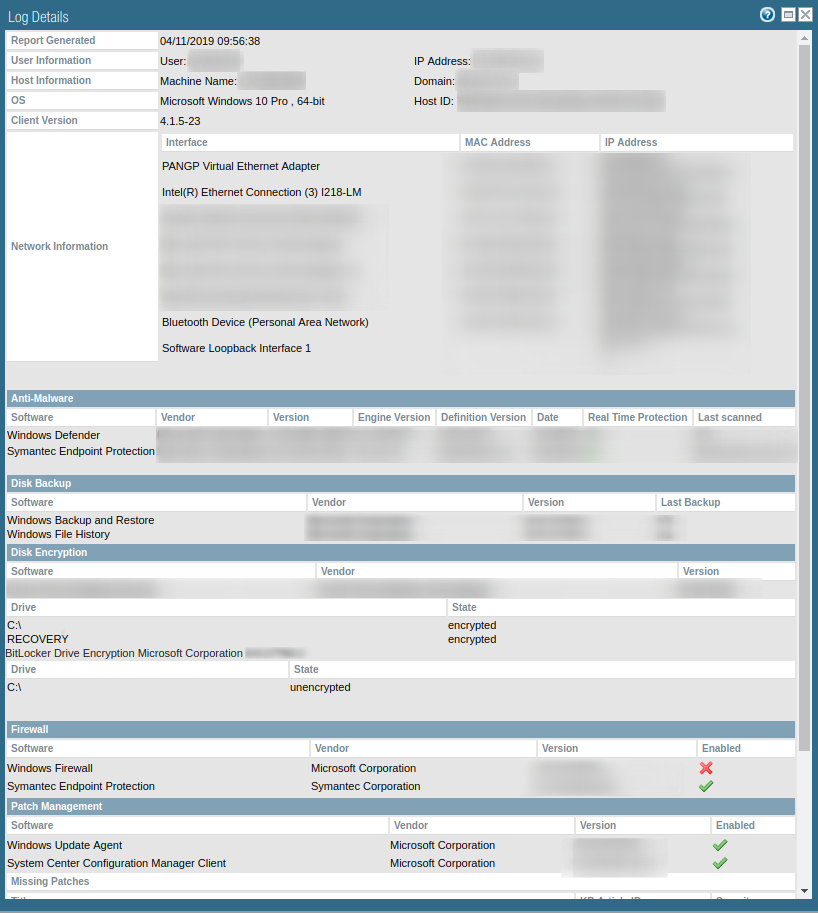
As it stands, we've got to go to Monitor > HIP Match > Magnifying Glass Icon to see them.
We'd like to send this rich data set to Splunk or another tool to write reports against.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-11-2019 08:49 AM
I use HIP myself and only log to panorama but there is a setting in device\log settings for HIP, have you tried this, it only displays a match and what you called the HIP check so may not be enough information.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-11-2019 08:54 AM
I'm already sending Hip Match logs off via syslog, but it is only summary logs. It does not have the rich data that you get when you hit the magnifying glass.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-19-2020 11:52 AM
I have the same question as starting to implement this.
Is there a back end database or a CLI command that will output the rich info that magnifier glass provides ? I am guessing there is a way to do it since the data is there and available. Creating the HIP Objects and Profiles is good but is just basic info and is mostly on/off for example if a system has antivirus or not, if installed or not, does not give specific info with the version and version number.
Looking on how to pull the rich info that the magnifier glass provides.
Help appreciated.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-19-2020 12:00 PM
Have a look here...
https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000ClshCAC
Not had chance myself as the wine doth floweth at a somewhat rapid pace...
a bit of scripting or api call may be required for automation.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-19-2020 08:47 PM
As @Mick_Ball's KB article states, this is kept in a local database and isn't really exposed in an easy format to get it exported off of the firewall. The firewall's own API isn't going to be very handy in this type of situation either, given the nature of the command required to access information held in that local database.
I would actually look at pulling in the client's GlobalProtect logs instead of dumping them from the firewall's database. That's easier to maintain and will give you the information in the exact same format if it's desired.
- 7487 Views
- 5 replies
- 1 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Parsing and Mapping 3rd party log source logs in Cortex XDR Discussions
- Prisma Access: Log Forwarding CEF Syslog in Strata Logging Service Discussions
- Firewall is not forwarding logs to the Syslog server in General Topics
- How to Set Different Source IPs for Specific Syslog Servers in Next-Generation Firewall Discussions
- error: azure marketplace vm-series do not bootstrap in VM-Series in the Public Cloud