- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Palo Alto device is wrongly directing the traffic . DUAL ISP IPSEC VPN issue
- LIVEcommunity
- Discussions
- General Topics
- Palo Alto device is wrongly directing the traffic . DUAL ISP IPSEC VPN issue
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Palo Alto device is wrongly directing the traffic . DUAL ISP IPSEC VPN issue
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-06-2022 02:57 AM
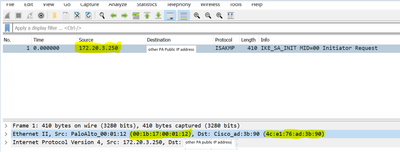
we have two dynamic ISP in single VR with ECMP and we have setup dual IPSEC VPN tunnels towards single public IP to other paloalto . our issue that PA wrongly forwarding traffic , ISP 2 is using MAC address of ISP1 when initiating VPN traffic to public ip address of second FW.
Moreover check the source MAC address !
show interface ethernet1/3 [ ISP1]
--------------------------------------------------------------------------------
Name: ethernet1/3, ID: 18
MAC address:
Port MAC address 00:1b:17:00:01:12
Operation mode: layer3
Interface IP address: 172.20.2.250/24
show interface ethernet1/2 [ ISP2]
MAC address:
Port MAC address 00:1b:17:00:01:11
Operation mode: layer3
Interface IP address: 172.20.3.250/24
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-07-2022 06:28 AM
Are you forcing symmetric return?
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-07-2022 06:32 AM
Yes enabled and also enable strict source path as well same even trying with 2 VR and PBF same issue we are in 10.1.6 which even we upgraded to from 10.1.5
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-08-2022 01:52 PM
Interesting. At least from my end, I would open a ticket so that TAC can review your actual configuration and confirm if something regarding routing is simply setup incorrectly, or if you're running into some undocumented bug. I'm guessing it's not a bug due to this being a regular setup, but maybe it's only present when select features are enabled or something like that.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-28-2024 10:52 AM
hello @mhm_ameen, have you got to the bottom of this? Looking at it from 10.2.x perspective I see that 'strict source path' is working fine on it - VPN traffic is tied to correct physical interfaces, but if you have path monitoring for static route you use as default for ISP1 for example and it will fail and be removed from routing table, then you might expect Palo to initiate VPN1 over different interface.
- 3269 Views
- 4 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Problem with Certificate install on Apple Silicon Laptops and the workaround I found. in GlobalProtect Discussions
- Can you configure multiple prisma access tunnel end points? in Prisma Access Discussions
- TCP 179 BGP port exposed to non direct neighbour or multi-hop neighbor, no rules in place allowing such traffic - still reachable in General Topics
- Static Bi-directional Source NAT not working on incoming traffic in General Topics