- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Rule with Deny action Allowing traffic
- LIVEcommunity
- Discussions
- General Topics
- Rule with Deny action Allowing traffic
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Rule with Deny action Allowing traffic
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-08-2019 01:07 AM
Hi,
We facing an strange issue regarding filtering to some destinations.
We have a rule with 2 kinds of destination address:
1. Static Group Address defined in Palo Alto
2. External dynamic list (2 of them)
Those address are attached to a deny rule because are malicious url.
When take a look to the traffic log, we see that traffic hits the rule but the action is allow. We are running version 8.X
Any suggestion about that behaviour?
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-08-2019 02:23 AM
Can you provide a bit more info?
i'm assuming the traffic being allowed is not actually hitting that policy rule in the logs?
also just to clarify:
you have 1 rule: containing a address group object. and 2 dynamic lists. not 2 sepearate rules?
Mind sharing the EDL url's?
also if the EDL uses url's, domains. make sure when to see if in monitoring tab the traffic being allowe dyou can resolve the url( checkbox at bottom of the page)
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-08-2019 02:37 AM - edited 03-08-2019 02:39 AM
Hi Tommie,
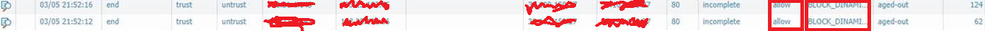
It's hitting the deny rule as you can see in the screenshoots below.
Regards,
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-08-2019 02:43 AM
Hi @nanukanu ,
My guess is that the traffic is allowed because the application isn't fully identified yet ...
It's normal for the firewall to allow some packets through to allow it to identify the application as seen in this article :
https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000CliLCAS
Once the application is identified correctly it should block.
Hope this helps.
-Kiwi.
Cheers,
Kiwi
Please help out other users and “Accept as Solution” if a post helps solve your problem !
Read more about how and why to accept solutions.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-08-2019 02:58 AM
But it's Just destination IP. I want to deny from any source to X destination IP block. Just layer 3.
I think the problem is related with external dynamic list. What happens if cannot reach the EDL? Block all traffic or allow? And what about if in the same rule we have edl and static? Which has more preference?
By the way are added to destination field in the ruleta, maybe must be added to URL field?
Thank you,
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-08-2019 04:59 AM
Hi @nanukanu ,
If you can't reach the EDL then there will not be anything to match on.
As for having both static and dynamic in one policy ... my guess it will process top down like a normal policy check. Static IPs are listed on top so they are checked first. If there's no match then it will process further down to the EDL lists. I haven't confirmed this but this seems logical to me.
Depending on what EDL you have configured you are limited on where you can use it :
You can use an IP address list as an address object in the source and destination of your policy rules;
you can use a URL List in Objects > Security Profiles > URL Filtering or as a match criteria in Security policy rules;
you can use a domain list in Objects > Security Profiles > Anti-Spyware Profile for sinkholing specified domain names.
Cheers !
-Kiwi
Cheers,
Kiwi
Please help out other users and “Accept as Solution” if a post helps solve your problem !
Read more about how and why to accept solutions.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-08-2019 06:11 AM
Hi Kiwi,
Thank you for your response but not seems to clarify this behaviour.
Why action allow if rule says block? There's nothing to evaluate, just if you are trying to go to any address inside the EDL or static addres group just deny.
I understand what you say about identify application, but in this case it's just IP to IP decision.
Thank you!
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-18-2019 08:00 AM
HI,
Any suggestion in this case?
After separate the rules (one with EDL and other with static group) seems that all is working fine, so it's something related about how PAN treat EDL and Static Groups in the same rule. Any new suggestion on that?
Regards!
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-18-2019 11:24 AM
Can you share screenshots of the rule?
Just looking at the logs, I only see 3 62-byte packets, and the traffic is incomplete. It looks like 3 SYN packets that go nowhere.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-18-2019 11:45 AM
Hi @nanukanu,
What type are the EDLs? You mentioned that they are d URL list type, is that correct?
It is also possible that the firewall is allowing some traffic in order to get the actual URLs from the data. Once it retriefs the URLs it will evaluate the rules again to see if the this traffic is stil matching this rule (before that it is potential match, that is why some packets are allowed).
You should be easy to confirm if you filter the logs by address and not by rule name - that should give you all the rules that this traffic has hit.
But if you are right and the reason is that EDL is being used with static group in the same rule...This looks weard, not sure that the FW should act like that.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-05-2019 05:59 AM
Hi, finally the rules are separated and works correctly. We will remain in this configuration because is working, but I think a problem exists mixing static and dynamic url.
Thanks to all for your help,
- 9619 Views
- 10 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- IPSEC to Azure establish but cannot use traceroute in General Topics
- Cloud NGFW: Mandatory Panorama Upgrade to 11.2.7-h4 or higher for managing Cloud NGFW Firewalls. in General Topics
- PAC Retention and URL Category Priority Behavior in Prisma Access in Strata Cloud Manager
- Discord voice chat no longer connecting after PA-440 install in General Topics
- Security Policy with Destination Criteria in Strata Cloud Manager