- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Website issue.
- LIVEcommunity
- Discussions
- General Topics
- Re: Website issue.
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Website issue.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-14-2018 11:07 PM - edited 10-14-2018 11:07 PM
Hi to everyone!
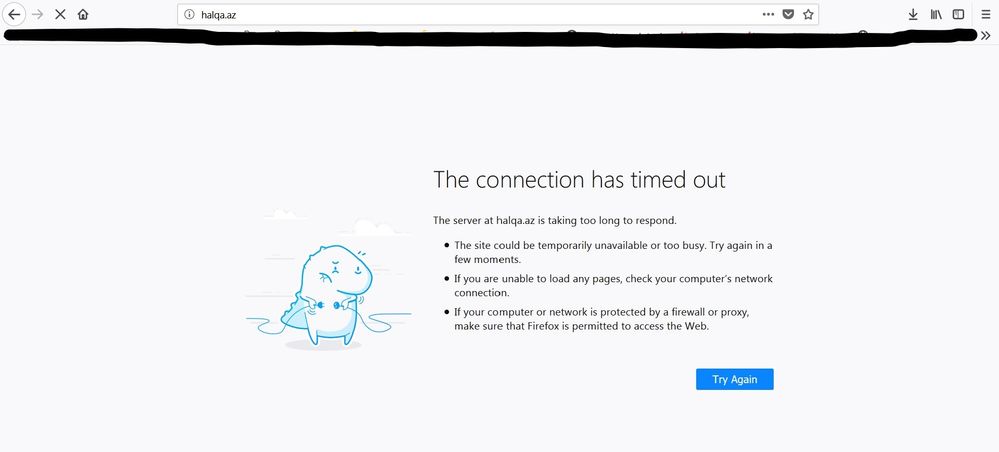
We have one site - halqa.az, which I can't give access to.
I have permitted everything on policies, permitted everything on decryption, still no success.
What should be else permitted? Maybe some of you will be able to help me.
Maybe there is any timeout issue or anything else.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-15-2018 09:26 AM
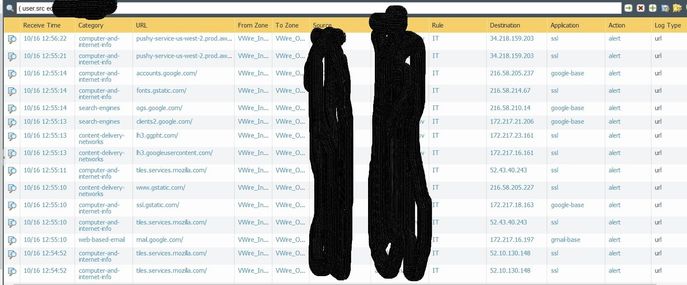
PAN-DB categorizes halqa.az as Insufficient Content (https://urlfiltering.paloaltonetworks.com) - which you may be blocking. Can you check for any blocks in the URL Filtering Log?
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-16-2018 02:01 AM
Good day!
There are no logs. Only timeouts. This site is some kind of test page.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-16-2018 04:05 AM
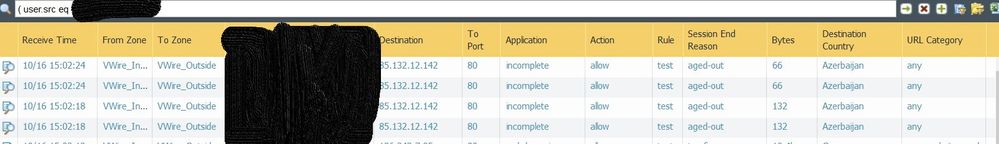
also there are such kind of logs - incomplete and aged-out.
this public ip is an ip of this server(halqa.az).
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-16-2018 09:14 AM
Hello,
Edit the columns to include 'Log Subtype'. I have see that sometimes this will be deny and the action is allow. To adjust the columns view, hover the mouse above one of the title fileds and click the down arrow. Then you can select the one you want.
Regards,
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-17-2018 05:11 AM
Hello ,
I faced a similar issue where the the website was not accessible when the traffic goes via Paloalto device. But the website is accessible from other network without PA.
This may be due to the packets from the web Server not having the window-scale information inside TCP packets. Paloalto will by default drop such TCP packets even though traffic is allowed in security policy.
For this you can check the TCP settings in Device--> Setup--> Session--> TCP Settings, change the Asymmetric path to bypass ( By default it will be drop )
It worked for me..
This will be the mis configuration in Web Server. If the Window-Scale details are not seen in TCP packets from Server reply, paloalto considers it as a asymmetric reply and will drop.
we can configure the Zone protection profile as well on the Untrust zone as well under ZoneProtection profile --> add --> Packet based Attack Protection -- TCP Drop --> Asymmetric Drop --> Bypass. And call this profile in Zone
But as a security best practice this is not recommended as it might give chance to attacks like IP spoofing and sequence number prediction.
We cannot have IP based or URL based bypass for this kind of issue.
Hope this helps... 🙂 🙂
Regards,
Sandeep
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-17-2018 07:04 AM
Are you sure that window-scale information missing is solved by bypassing Assymmetric path? Because asymmetric routing should just be the fact that path from client to server isn't mirrored for the path from server to client (for example traffic from client to server does go through the firewall, but for server to client it doesn't)
When you click in the traffic log on the traffic from your client to the server, do you only see packets received or also sent?
And possibly stupid question, but are you sure your traffic from your public ip isn't being dropped on their end?
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-17-2018 08:26 AM
halqa.az resolves to 85.132.12.14
Monitor > Packet Capture > Manage Filters
Add 2 filters.
One where 85.132.12.14 is source.
One where 85.132.12.14 is destination.
Turn filtering on.
Go to cli.
> show counter global filter delta yes packet-filter yes
Now try to access website.
And then run same command again.
> show counter global filter delta yes packet-filter yes
Other option is to see if anything was dropped with severity drop.
> show counter global filter delta yes packet-filter yes severity drop
Switch off filter and remove 2 filters added before.
Palo Alto Networks certified from 2011
- 5209 Views
- 7 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- PA1420 IKE packet disappear between receive (ingress) and firewall session state in General Topics
- while do the factory reset of pa 5250 showing error: findfs: unable to resolve 'label=sysroot0 in Next-Generation Firewall Discussions
- XSIAM V3.4 upgrade - anyone having issues? in Cortex XSIAM Discussions
- Panorama scheduled export path in Panorama Discussions
- Regarding impoper tagging of node-tar vulnerability with alpine-tar package when using prisma scan tool in Prisma Cloud Discussions