- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Will an On-Demand configuration keep GlobalProtect from notifying me that it did not connect?
- LIVEcommunity
- Discussions
- General Topics
- Re: Will an On-Demand configuration keep GlobalProtect from notifying me that it did not connect?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Will an On-Demand configuration keep GlobalProtect from notifying me that it did not connect?
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-31-2018 07:17 AM
I've deployed GlobalProtect 4.0.3-31 to my lab machines. When I log in, I get notifications that GlobalProtect is connecting, and then that it is not connected. I'm not panicked because my portal is not available from my internal network. Will switching to an On-Demand configuration make these notifications go away?
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-31-2018 07:58 AM
On demand will keep the GP client from logging in automatically, the user will have to open up the client and choose to logon and get connected
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-31-2018 08:47 AM
@jdprovine has answered your question, but can i ask, why have you installed GP to lab devices if not needed.
just curious....
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-31-2018 10:20 PM
Excuse the brevity of my previous post.
had to pop out..
i was going to suggest internal host detection for globalprotect but as in a lab enviroment this may not be possible.
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-01-2018 05:20 AM
That's the behavior I want, but will it eliminate the icon in the system tray reporting an error (not connected)? My users will go bonkers if they see that.
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-01-2018 05:22 AM
It's not that the lab machines don't need it, none of my computers will need it when they're connected to the corporate network. This is strictly to allow corporate-owned computers to connect to our network when they're out in the wild.
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-01-2018 05:42 AM
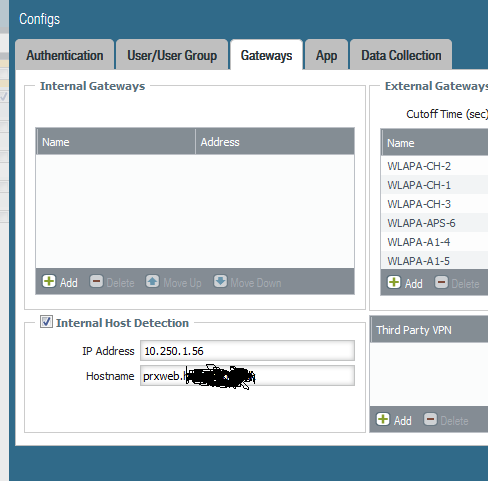
if you configure "internal host detection" in the globalprotect app config on the PA, the user icon will just change to a little house, no errors....
its under network/portals/agent/config/gateways
just choose an internal host and its relevant IP address... bingo. we use it for our always on config.
please note that users will need to connect to the portal to get the new config.
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-01-2018 05:57 AM
also...
we allow access to the portal from our LAN.
only so that users can get the latest config whilst connected to the LAN.
we have 4,500 users with "always on" and "internal host detection" and have had no issues... works well.....
the internal host option will prevent them from connecting to any of your gateway(s). providing the internal host is available.
not sure why PA never gave the option to add 2 or 3 internal hosts for maintenance or similar...
Mick.
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-01-2018 09:23 AM
@Mick_Ball's suggestion is the best option. We are doing the same thing with our domain laptops. This functions fairly well (occasionally a rediscover network is required as users just sleep thier computers between office and home).
Brian
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-01-2018 01:58 PM
@BrianRa, yes noted... when i say we have no issues i of course mean not enough to cause any concern...
we do have the occasional rediscover issue but users are content and familiar with this... our calls have reduced 10 fold since always on was introduced. However... we really dont get many rediscover issues compared to the ammount of users involved and im talking about users who struggle to even open the laptop lid sometimes...
but of course.... if it all ran smoothly... i would be stacking shelves.....
not sure if it makes any difference but in sleep mode, users are logged off and after 15 mins of inactivity the laptop is shut down...
so.... by the time our users have moved site or arrived home the device powers up from scratch...
Laters....
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-01-2018 03:02 PM
Thanks @Mick_Ball, I wasn't trying to argue I was confirming everything you had said.
That is actually a very good differentiation. We allow them to sleep then hibernate. When they come back up the laptop thinks nothing has changed, checks its network and corrects. GP does not always update when the interface updates. This is where the rediscover network comes in.
I am not saying by any means this is a large problem, just one it is better to be aware of. Initially we received quite a few calls because "it takes forever to come back up". The GP VPN works much better than many others I have used.
Brian
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-01-2018 10:32 PM
@BrianRa, no arguement perceived, it was a good post and i was confirming what you said as no matter what configuration you use, it will still have the occasional issue. Sorry for the confusion.
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-02-2018 05:22 AM
We allow internal accessa as well though I have been told that is not a good idea but I have never been given any reason why it is considered a bad idea
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-02-2018 07:06 AM
I can see why this could be an issue...
if you remove the dns entry of your internal host, or, if the internal host changes its IP then always on devices will connect to the gateway via the internet and back again... no big deal but it could max out your 128k isdn...
so, I use an internal host with a fixed IP, damage limitation reduced 50%.
I still would prefer the option of being able to add at least another 1 internal host entry..
having said that,,, you can of course have internal host detection without access from the LAN to portal/gateway.
I have to say that the best point about internal host detection is that users will know if they have a GP issue prior to traveling half way round the world to discover thier auth cert has expired or that thier username has been changed on AD and not updated PKI.
Mick
- 8840 Views
- 18 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- GP with saml authentication always redirects to idp in General Topics
- SAML authentication with cookies won´t work in General Topics
- Assign private IP address failed in GlobalProtect Discussions
- Configuring GlobalProtect via Ansible in GlobalProtect Discussions
- Inquiry regarding the maximum number of HIP Objects (vs HIP Profiles) in GlobalProtect Discussions