- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Security Policy
- LIVEcommunity
- Discussions
- Network Security
- Next-Generation Firewall Discussions
- Security Policy
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-03-2023 10:21 AM
Hello,
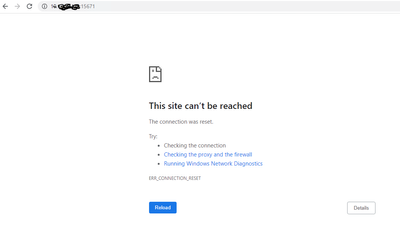
I have created a security policy with the below details. I am the hitting following URL https://10.x.x.x:15671 and I see the 'connection is reset' in the browser. I see traffic is hitting the policy (Hit count) but it's not logging. When I set the action to Deny/Drop/reset-client\reset-server the traffic is logging when hits the rule. What could be the reason why traffic is not logging for action 'Allow' and why traffic is not passing through?
Application - Any
Services - Application default
Action - Allow
Logging - Log st session start and end
Thanks,
Srikar
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-04-2023 05:43 AM
Your service is set to application default while you're using port 15671 for ssl traffic (default port 443)
This means you will not be using this security rule to handle the traffic. You're most likely dropping down to the default intrazone deny rule, which has logging disabled
reason you're seeing the hit counter increase is when the SYN paxcket arrives there's no app-id yet, so no default port to enforce, the policy match goes by the 6tuple (source zone, source ip, destination zone, destination ip, destination port, protocol)
since you have an any any rule, the syn packet is allowed through until app-id kicks in, the rulebase is chcked again, this rule no longer matches and the next best match is de default rule
PANgurus - Strata & Prisma Access specialist
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-04-2023 05:43 AM
Your service is set to application default while you're using port 15671 for ssl traffic (default port 443)
This means you will not be using this security rule to handle the traffic. You're most likely dropping down to the default intrazone deny rule, which has logging disabled
reason you're seeing the hit counter increase is when the SYN paxcket arrives there's no app-id yet, so no default port to enforce, the policy match goes by the 6tuple (source zone, source ip, destination zone, destination ip, destination port, protocol)
since you have an any any rule, the syn packet is allowed through until app-id kicks in, the rulebase is chcked again, this rule no longer matches and the next best match is de default rule
PANgurus - Strata & Prisma Access specialist
- 1 accepted solution
- 2753 Views
- 2 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- CVE-2026-0261 PAN-OS_ Authenticated Admin Command Injection Vulnerability in Next-Generation Firewall Discussions
- EDL Performance and Refresh Handling in Panorama in Next-Generation Firewall Discussions
- GlobalProtect, Release Notes, Build Numbers, CVE ?!?! in GlobalProtect Discussions
- [FIREWALL] - Commit Issue in Next-Generation Firewall Discussions
- Rename security zones on panorama and push it to the firewalls in Panorama Discussions