- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
AWS NAT not coming back
- LIVEcommunity
- Discussions
- Network Security
- VM-Series in the Public Cloud
- AWS NAT not coming back
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-13-2019 07:07 PM - edited 11-13-2019 07:24 PM
Hello,
I tried to setup the nat, I can see my NAT and Security rule are being hit, but traffic is not flowing
Bundle 1
Interface Swap (tested this with no swap too, and it didn;t work)
All of the 3 interfaces disabled src destination
all of them same sg, 0.0.0.0./0
eth0 and eth1 are on the same subnet (public) with a route 0.0.0.0/0 to igw
eth0 and eth1 both have a elastic ip attached
eth2 is on the private subnet, route 0.0.0.0/0 points to eth2
Server is on the same subnet as eth2
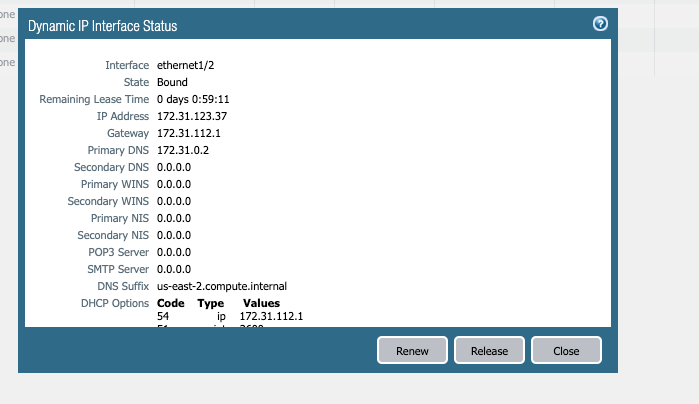
DHCP seems to pick up the proper IPs (internal ips)
My nat rule
Source: Trust -> Untrust
Destination ethernet1.1
source: any
destination: any
service any
Source Translation: dynamic ip and port <<PRIVATE IP ADDRESS of eth1>>
Hit count: over 2000+
For my security rule
Universal, any, any, any .. any, allow. Hit count 3000+
Monitor shows "aged out", allowed, so it the traffic flows one way, but it doesn't come back!
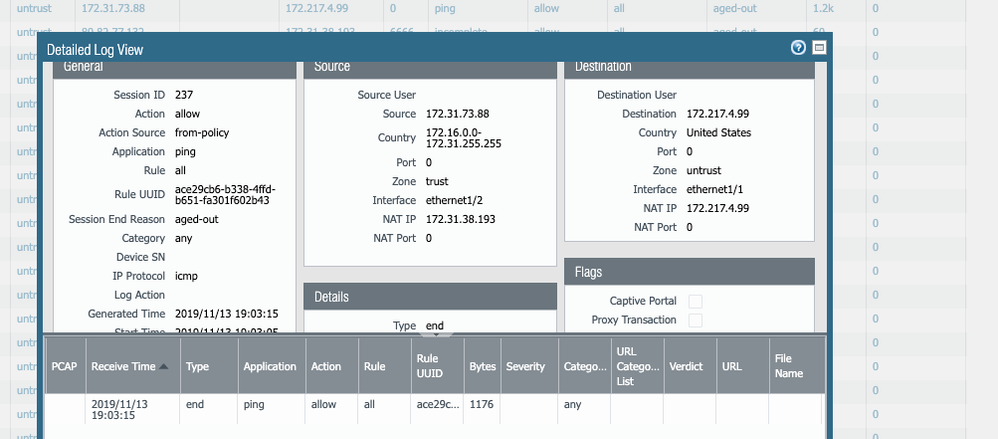
Attached is a screenshot, the internal machine (172.31.73.88 pings google 172.217.4.99
172.31.38.193 is my eth1 "untrust"
Thanks in advance
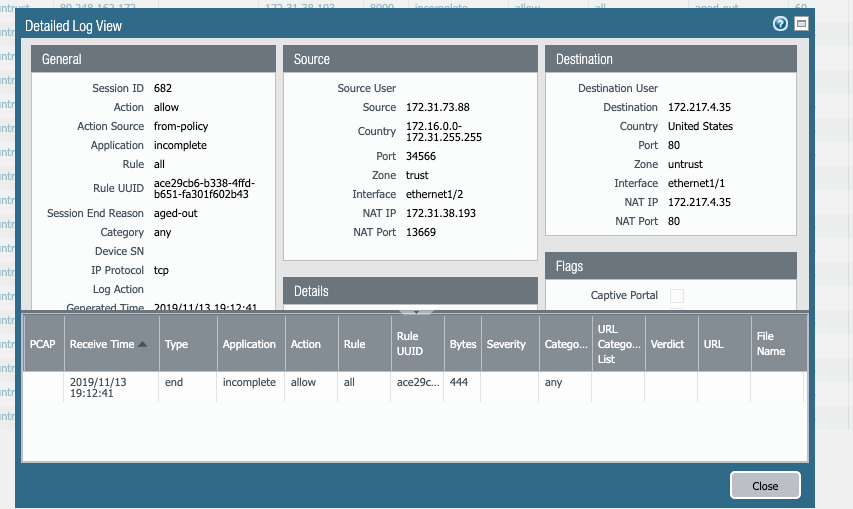
Here's a request to google port 80
nat rule
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-14-2019 05:44 AM
Rather than specifying your Trust side IP of the firewall as the next hop in that route. Set the next-hop IP to the first IP of the Trust subnet which is the AWS router IP.
ie. if the Trust subnet is /24, set the next-hop to 172.31.38.1
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-14-2019 04:30 AM
2 Thoughts.
- Check your default route in the VR. Ideally, you should use DHCP on both interfaces in the firewall and ensure to Uncheck "Automatically create default route..." on the Trust side Interface so that you only inherit the default route on E1/1.
- Change the Source Translation in your NAT rule to:
- Translation Type: DIPP
- Address Type: Interface Address
- Interface: ethernet 1/1
- IP Address: None
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-14-2019 05:03 AM
Thanks
I made those changes
The nat is working if the trust ENI is on the same subnet than the server I'm trying to nat.
is there any way I can point other route tables to this ENI? I made the change but they can't connect to internet.
Thank you
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-14-2019 05:21 AM
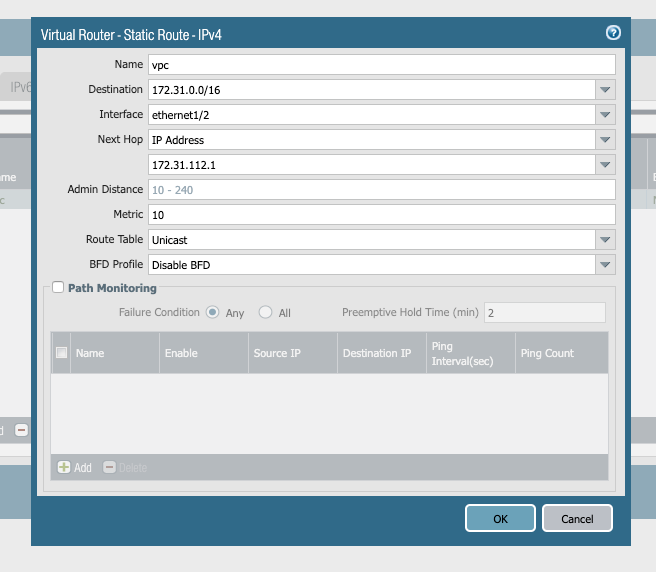
Excellent, that is a step in the right direction. Create a static route on the firewall VR to send all of the VPC subnets that are behind the firewall out of the Eth1/2 interface to the first IP in the firewall's Trust Subnet. AWS will then route it to the Server subnet.
I assume the Server subnet has a 0/0 route point to the Trust side of the firewall?
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-14-2019 05:32 AM - edited 11-14-2019 05:32 AM
Thanks
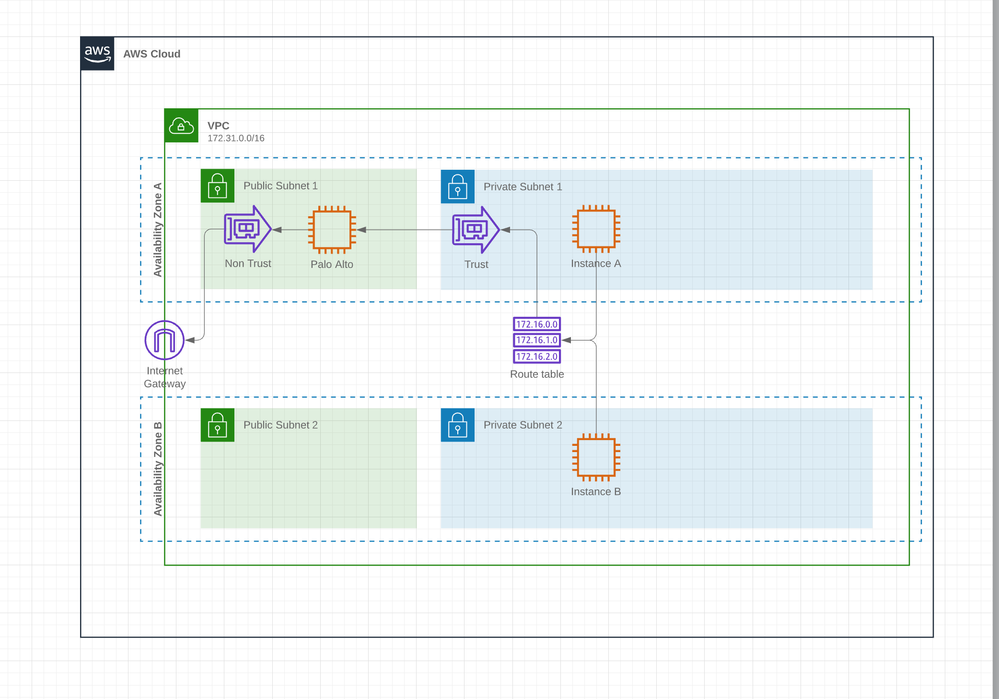
This is how my network looks like
Palo in Public
A same subnet that the trust interface, works fine
B diff subnet, same vpc, same Route Table, pointing to that ENI
For the route you mention, Unfortunately... I don't know how.. this is above the knowledge I have for this POC
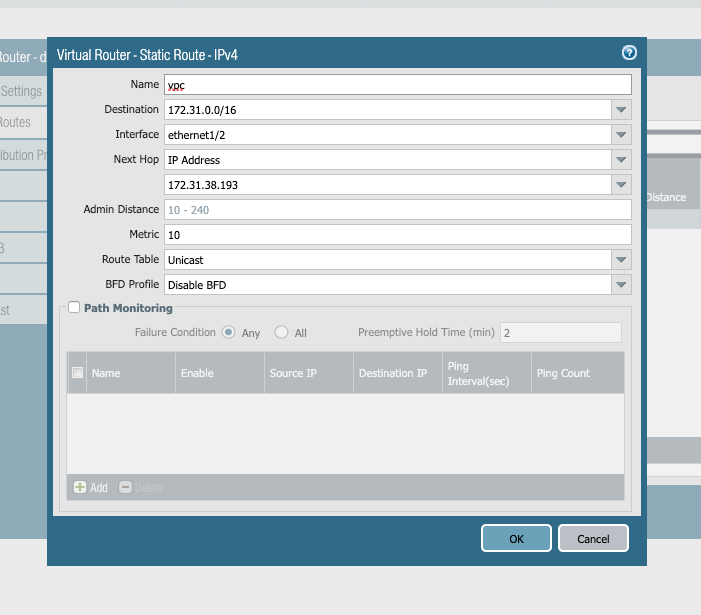
This is why I tried
172.31.0.0/16 is my VPC CIDR
172.31.38.193 is the private IP of the "non trust interface"
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-14-2019 05:44 AM
Rather than specifying your Trust side IP of the firewall as the next hop in that route. Set the next-hop IP to the first IP of the Trust subnet which is the AWS router IP.
ie. if the Trust subnet is /24, set the next-hop to 172.31.38.1
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-14-2019 05:55 AM
what I learning experience!
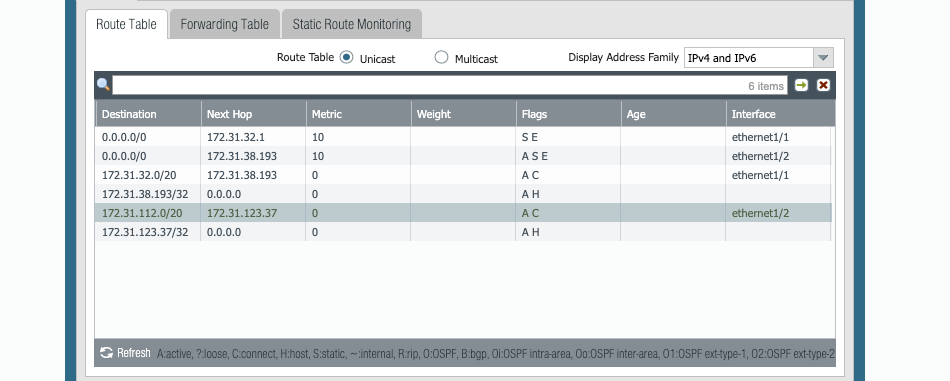
My original routes
Then I added the VPC CIDR pointing to the "gateway of the trust interface" (Trust = 172.31.123.37)
New route
Thanks for all your help, just documenting here if someone is on the same spot
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-13-2023 07:06 AM
Worked for me.
Thank you !
- 1 accepted solution
- 11202 Views
- 7 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- OSPF process crashes after manual HA Failover in Next-Generation Firewall Discussions
- GlobalProtect 6.3.3 + Duo SAML MFA loop after normal Windows login (works only via GP Credential Provider at Windows logon) in GlobalProtect Discussions
- Regarding the migration from HDD to SSD for PA-VM running in the Azure environment in Next-Generation Firewall Discussions
- Regarding the migration from HDD to SSD for PA-VM running in the Azure environment in VM-Series in the Public Cloud
- HA failover on Acitve Passive concerns in Next-Generation Firewall Discussions