- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
No traffic logs in PA-VM
- LIVEcommunity
- Discussions
- General Topics
- No traffic logs in PA-VM
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
No traffic logs in PA-VM
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-27-2015 06:41 PM
I just deployed a PAN-VM and everything is working except I don't have any traffic logs for some reason but I do have ACC, System and Conguration logs. The only thing I can think that may cause issues is the fact that the box is not licensed yet as I'm just testing it out. Is this why? An unregistered PA-200 logs traffic data though so I find this really odd.
Anyone can confirm if this is due to license or is it due to the PAN-VM configuration? I used thin provisioning for the disk. I can try redeploying with thick provisioning but wanted to ask here first.
Thanks so much!
- Labels:
-
Configuration
-
Troubleshooting
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-27-2015 06:46 PM
Hello x,
The license would not force the device to stop logging traffic. Could you please check the security rule, whether logging option is enabled there..?
Example:
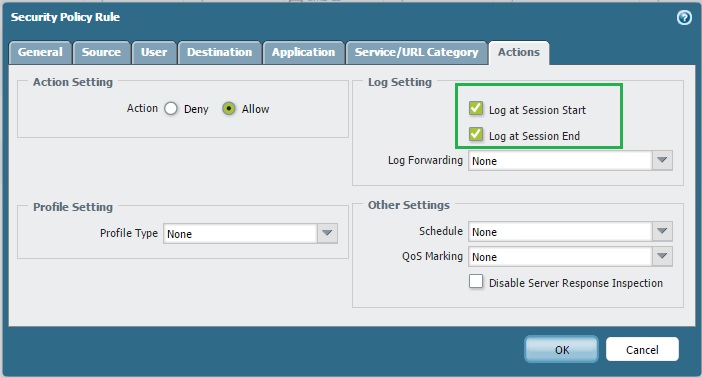
Hope this helps.
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-27-2015 06:53 PM
Hello X,
Without licensing PANW-VM can transfer only first 200 connection, sub-sequent sessions will not be processes.
In either case licensing is important. I would also suggest to check "Log at asession start" and "Log at asession End" option.
Regards,
Hardik Shah
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-27-2015 07:22 PM
Thanks guys. Yup logging is enabled and I'm aware of the license restrictions although I'm not seeing any effects on traffic so far. Session is below 200 since it's just me and still there are no logs. Really weird.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-27-2015 07:25 PM
Hi X,
Please provide output for "show session info".
Regards,
Hardik Shah
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-28-2015 02:22 AM
There's quite a few threads with the same topics - all of the have the same suggestions as above, which haven't helped anyone yet.
It appears the VM series require a license deployed, in order to view the live monitoring traffic - however I have yet to encounter this anywhere in official documentation.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-28-2015 07:57 AM
Unlicensed VM series do not provide logging, at least that's how it works in my lab as well. See attached:
admin@pa61-unlic-test> show system info
hostname: pa61-unlic-test
ip-address: 10.2.1.220
netmask: 255.255.255.0
default-gateway: 10.2.1.1
ipv6-address: unknown
ipv6-link-local-address: fe80::250:56ff:fe82:672f/64
ipv6-default-gateway:
mac-address: 00:50:56:82:67:2f
time: Wed Jan 28 07:48:52 2015
uptime: 0 days, 0:02:20
family: vm
model: PA-VM
serial: unknown <<<<<----- UNLICENSED
vm-mac-base: BA:DB:EE:FB:AD:00
vm-mac-count: 255
vm-uuid: 4202ACA4-07A0-CCDD-2881-F8D8B2418E3D
vm-cpuid: D2060200FFFBAB1F
vm-license: none
vm-mode:
sw-version: 6.1.0
global-protect-client-package-version: 0.0.0
app-version: 451-2337
app-release-date: unknown
av-version: 0
av-release-date: unknown
threat-version: 0
threat-release-date: unknown
wf-private-version: 0
wf-private-release-date: unknown
url-db: paloaltonetworks
wildfire-version: 0
wildfire-release-date: unknown
url-filtering-version: 0000.00.00.000
global-protect-datafile-version: 0
global-protect-datafile-release-date: unknown
logdb-version: 6.1.3
platform-family: vm
vpn-disable-mode: off
multi-vsys: off
operational-mode: normal
admin@pa61-unlic-test>
admin@pa61-unlic-test> show interface all
total configured hardware interfaces: 2
name id speed/duplex/state mac address
--------------------------------------------------------------------------------
ethernet1/1 16 10000/full/up ba:db:ee:fb:ad:10
ethernet1/2 17 10000/full/up ba:db:ee:fb:ad:11
aggregation groups: 0
total configured logical interfaces: 2
name id vsys zone forwarding tag address
------------------- ----- ---- ---------------- ------------------------ ------ ------------------
ethernet1/1 16 1 wan vr:default 0 50.xxx.xxx.xxx/29 <<<---- PUBLIC IP ADDRESS (obfuscated)
ethernet1/2 17 1 lan vr:default 0 10.1.1.2/24 <<<--- INTERNAL IP ADDRESS
admin@pa61-unlic-test> ping source 10.1.1.2 host 4.2.2.1
PING 4.2.2.1 (4.2.2.1) from 10.1.1.2 : 56(84) bytes of data.
64 bytes from 4.2.2.1: icmp_seq=2 ttl=57 time=24.5 ms
64 bytes from 4.2.2.1: icmp_seq=3 ttl=57 time=24.6 ms
64 bytes from 4.2.2.1: icmp_seq=4 ttl=57 time=27.2 ms
^C
--- 4.2.2.1 ping statistics ---
4 packets transmitted, 3 received, 25% packet loss, time 3009ms
rtt min/avg/max/mdev = 24.568/25.487/27.237/1.244 ms
admin@pa61-unlic-test> show session info
--------------------------------------------------------------------------------
Number of sessions supported: 1248
Number of active sessions: 10
Number of active TCP sessions: 0
Number of active UDP sessions: 6
Number of active ICMP sessions: 4
Number of active BCAST sessions: 0
Number of active MCAST sessions: 0
Number of active predict sessions: 0
Session table utilization: 0%
Number of sessions created since bootup: 13
Packet rate: 16/s
Throughput: 14 kbps
New connection establish rate: 0 cps
--------------------------------------------------------------------------------
Session timeout
TCP default timeout: 3600 secs
TCP session timeout before SYN-ACK received: 5 secs
TCP session timeout before 3-way handshaking: 10 secs
TCP half-closed session timeout: 120 secs
TCP session timeout in TIME_WAIT: 15 secs
TCP session timeout for unverified RST: 30 secs
UDP default timeout: 30 secs
ICMP default timeout: 6 secs
other IP default timeout: 30 secs
Captive Portal session timeout: 30 secs
Session timeout in discard state:
TCP: 90 secs, UDP: 60 secs, other IP protocols: 60 secs
--------------------------------------------------------------------------------
Session accelerated aging: True
Accelerated aging threshold: 80% of utilization
Scaling factor: 2 X
--------------------------------------------------------------------------------
Session setup
TCP - reject non-SYN first packet: True
Hardware session offloading: True
IPv6 firewalling: True
Strict TCP/IP checksum: True
--------------------------------------------------------------------------------
Application trickling scan parameters:
Timeout to determine application trickling: 10 secs
Resource utilization threshold to start scan: 80%
Scan scaling factor over regular aging: 8
--------------------------------------------------------------------------------
Session behavior when resource limit is reached: drop
--------------------------------------------------------------------------------
Pcap token bucket rate : 10485760
--------------------------------------------------------------------------------
admin@pa61-unlic-test> show session all
--------------------------------------------------------------------------------
ID Application State Type Flag Src[Sport]/Zone/Proto (translated IP[Port])
Vsys Dst[Dport]/Zone (translated IP[Port])
--------------------------------------------------------------------------------
7 netbios-ns ACTIVE FLOW 10.1.1.10[137]/lan/17 (10.1.1.10[137])
vsys1 10.1.1.255[137]/lan (10.1.1.255[137])
6 unknown-udp ACTIVE FLOW 10.1.1.201[51439]/lan/17 (10.1.1.201[51439])
vsys1 10.1.1.255[5002]/lan (10.1.1.255[5002])
5 dropbox ACTIVE FLOW 10.1.1.16[17500]/lan/17 (10.1.1.16[17500])
vsys1 10.1.1.255[17500]/lan (10.1.1.255[17500])
4 unknown-udp ACTIVE FLOW 10.1.1.16[49561]/lan/17 (10.1.1.16[49561])
vsys1 10.1.1.255[5002]/lan (10.1.1.255[5002])
12 ping ACTIVE FLOW NS 10.1.1.2[16654]/lan/1 (50.xxx.xxx.xxx[16654]) (obfuscated)
vsys1 4.2.2.1[3]/wan (4.2.2.1[3])
8 undecided ACTIVE FLOW 10.1.1.12[138]/lan/17 (10.1.1.12[138])
vsys1 10.1.1.255[138]/lan (10.1.1.255[138])
9 dropbox ACTIVE FLOW 10.1.1.10[17500]/lan/17 (10.1.1.10[17500])
vsys1 10.1.1.255[17500]/lan (10.1.1.255[17500])
admin@pa61-unlic-test> show session id 12
Session 12
c2s flow:
source: 10.1.1.2 [lan]
dst: 4.2.2.1
proto: 1
sport: 16654 dport: 3
state: INIT type: FLOW
src user: unknown
dst user: unknown
s2c flow:
source: 4.2.2.1 [wan]
dst: 50.xxx.xxx.xxx (obfuscated)
proto: 1
sport: 3 dport: 16654
state: INIT type: FLOW
src user: unknown
dst user: unknown
start time : Wed Jan 28 07:49:03 2015
timeout : 6 sec
total byte count(c2s) : 98
total byte count(s2c) : 98
layer7 packet count(c2s) : 1
layer7 packet count(s2c) : 1
vsys : vsys1
application : ping
rule : permit outbound
session to be logged at end : True <<<---- LOGGING ENABLED
session in session ager : False
session updated by HA peer : False
address/port translation : source
nat-rule : outbound nat(vsys1)
layer7 processing : enabled
URL filtering enabled : False
session via syn-cookies : False
session terminated on host : True
session traverses tunnel : False
captive portal session : False
ingress interface : ethernet1/2
egress interface : ethernet1/1
session QoS rule : N/A (class 4)
tracker stage firewall : null
end-reason : aged-out <<<--- SESSION ENDED
admin@pa61-unlic-test>
admin@pa61-unlic-test> show log traffic
Time App From Src Port Source
Rule Action To Dst Port Destination
Src User Dst User End Reason
===============================================================================
admin@pa61-unlic-test>
(NO LOGS)
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-28-2015 12:31 PM
Thanks! at least I know I'm not going crazy ![]() . Should I dare report this as a bug LOL. Thanks again for sharing.
. Should I dare report this as a bug LOL. Thanks again for sharing.
- 8588 Views
- 7 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Intrazone-default Rule in Next-Generation Firewall Discussions
- Firwall is uable to send logs to the Panorma (Log collector is showing inactive) in Next-Generation Firewall Discussions
- Config/System Logs Not Forwarding to Syslog Server in Next-Generation Firewall Discussions
- Panorama reports not available since the upgrade in Panorama Discussions
- PA1420 IKE packet disappear between receive (ingress) and firewall session state in General Topics




