- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Alert from which source/rule?
- LIVEcommunity
- Discussions
- Security Operations
- Cortex XDR Discussions
- Alert from which source/rule?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-04-2022 10:42 AM
Hello!
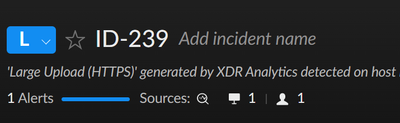
We have some alerts which show us a large upload.
My problem is now, I saw other clients uploading a ton of bytes, but this Alert wasn't fired.
I also cannot find any Rule for this.
Where is it comming from?
BR
Rob
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-04-2022 11:03 AM - edited 08-04-2022 11:05 AM
Hi RFeyertag,
This is an Analytics alert, specifically Large Upload (https). The Analytics engine examines data from the XDR agents which have Pro capabilities enabled as well as NGFW logs if you have a Pro per TB license. The Analytics Engine creates a baseline of normal activity in the environment and then looks for anomalies, each alert has its own baseline period and test period, you can read more in the link above for this specific alert.
The rule does not look only at upload size, it is also looking for sites that clients are not uploading large amounts of data to and that the endpoint in question has not downloaded a large amount of data from. The check is to look for potential data exfiltration from your network.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-05-2022 06:56 AM - edited 08-05-2022 07:00 AM
Hi @RFeyertag
Additionally to what Afurze mentioned (with very good criteria by the way) inspecting the alert on our documentation, please investigate the specific endpoint. And maybe talk to the user and/or manager of the endpoint group to see if this endpoint has changed the role in the organization, maybe now it is used to transfer legit info to a legit site ? (customer of yours, provider, other organization you cooperate with...) check with them and also with XDR if a new app has been installed there a bit earlier than the exfiltration ocurred, if the user logged in by the time of potential exfiltration was a legit one and also if the time of data transfer is "normal business hours??", check the type of loggin of the user by that time, was he sitting on the endpoint ? was it a remote/network login ? the IP of the connection in case of the user was remotely connecting ? is it legit location ?
Maybe investigating the CGO you can find the app/process that is the culprit of the suspicious action ?
Having our Identity Analytics (and so Cloud Identity Engine) enabled will also focus through AD data on the behaviour over time of the suspected user and endpoint.
Just some clues to perform the incident investigation and the determination of the actual root cause of the incident.
Hope this helps,
Luis
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-04-2022 11:03 AM - edited 08-04-2022 11:05 AM
Hi RFeyertag,
This is an Analytics alert, specifically Large Upload (https). The Analytics engine examines data from the XDR agents which have Pro capabilities enabled as well as NGFW logs if you have a Pro per TB license. The Analytics Engine creates a baseline of normal activity in the environment and then looks for anomalies, each alert has its own baseline period and test period, you can read more in the link above for this specific alert.
The rule does not look only at upload size, it is also looking for sites that clients are not uploading large amounts of data to and that the endpoint in question has not downloaded a large amount of data from. The check is to look for potential data exfiltration from your network.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-05-2022 06:56 AM - edited 08-05-2022 07:00 AM
Hi @RFeyertag
Additionally to what Afurze mentioned (with very good criteria by the way) inspecting the alert on our documentation, please investigate the specific endpoint. And maybe talk to the user and/or manager of the endpoint group to see if this endpoint has changed the role in the organization, maybe now it is used to transfer legit info to a legit site ? (customer of yours, provider, other organization you cooperate with...) check with them and also with XDR if a new app has been installed there a bit earlier than the exfiltration ocurred, if the user logged in by the time of potential exfiltration was a legit one and also if the time of data transfer is "normal business hours??", check the type of loggin of the user by that time, was he sitting on the endpoint ? was it a remote/network login ? the IP of the connection in case of the user was remotely connecting ? is it legit location ?
Maybe investigating the CGO you can find the app/process that is the culprit of the suspicious action ?
Having our Identity Analytics (and so Cloud Identity Engine) enabled will also focus through AD data on the behaviour over time of the suspected user and endpoint.
Just some clues to perform the incident investigation and the determination of the actual root cause of the incident.
Hope this helps,
Luis
- 2 accepted solutions
- 3752 Views
- 3 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Es posible bloquear una IP en cortex xdr pro in Cortex XDR Discussions
- Is there a difference between issues and alerts in XQL queries? in Cortex XDR Discussions
- StoreDesktopExtension.exe - Again alerts are generated in Cortex XDR Discussions
- Issue with IOC not blocking MyPDFSwitch executable in Cortex XDR Discussions
- Inconsistent AnyDesk Detection in Cortex XDR in Cortex XDR Discussions