- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
7.1.2 Unable to reach GlobalProtect portal
- LIVEcommunity
- Discussions
- General Topics
- Re: 7.1.2 Unable to reach GlobalProtect portal
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-24-2017 01:42 PM - edited 01-24-2017 01:46 PM
Hey guys,
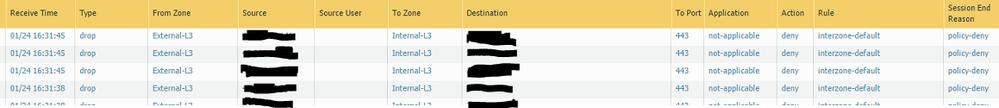
I am trying to get the GlobalProtect piece of the FW to work, I followed word for word from the 7.1 admin guide and still no luck. When I go to monitor I see the source coming from the external-untrust zone (which is correct), but the to zone shows (internal - trust). If I am reading this doc correctly, the VPN should terminate on the tunnel interface it makes you create right?
Page 157 -
Any ideas?
Regards
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-25-2017 01:44 AM - edited 01-25-2017 01:45 AM
Hi Digitaltrance,
If you're trying to web browse to your global protect portal you would ideally host this on your external interface or on a loopback interface. The tunnel interface would be for when you are connecting to the GP VPN and establishing a tunnel rather than web browsing to the portal.
To establish the connection you will need to first allow the external client to access the portal to authenticate then also allow the gateway authentication.
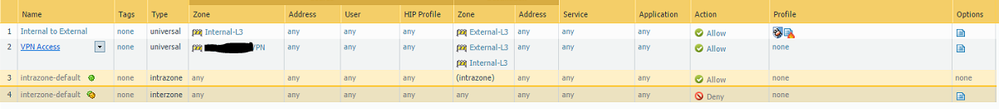
As your log shows external to internal hitting the default interzone deny, rather than say external to external intrazone default allow then it looks like you may be accidentally NATing your traffic destined to your portal to your internal zone? Or you have set up your GP portal for an interface in your internal zone rather than an external zone? As you don't have a policy to allow that I can see in your screenshots.
Check the detailed log view (spyglass on the left of the log) and you can see if your traffic is being NATed incorrectly in the destination panel.
hope this helps,
Ben
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-25-2017 05:36 AM
I think @bmorris1 pretty much nailed the first things to look at and you'll likely find an error with where you have the tunnel as far as the security zone goes or something weird with your NAT policy. I would look at the tunnels security zone first, and then look at the NAT as I think it's actually more likely that you actually set your tunnel interface to your internal zone.
One thing that I might recommend is actually making a GlobalProtect zone. It makes creating access policies and the like a little bit easier if you are looking to lock down your VPN users access, and it helps keep it really simple as far as access rules go.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-25-2017 01:44 AM - edited 01-25-2017 01:45 AM
Hi Digitaltrance,
If you're trying to web browse to your global protect portal you would ideally host this on your external interface or on a loopback interface. The tunnel interface would be for when you are connecting to the GP VPN and establishing a tunnel rather than web browsing to the portal.
To establish the connection you will need to first allow the external client to access the portal to authenticate then also allow the gateway authentication.
As your log shows external to internal hitting the default interzone deny, rather than say external to external intrazone default allow then it looks like you may be accidentally NATing your traffic destined to your portal to your internal zone? Or you have set up your GP portal for an interface in your internal zone rather than an external zone? As you don't have a policy to allow that I can see in your screenshots.
Check the detailed log view (spyglass on the left of the log) and you can see if your traffic is being NATed incorrectly in the destination panel.
hope this helps,
Ben
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-25-2017 05:36 AM
I think @bmorris1 pretty much nailed the first things to look at and you'll likely find an error with where you have the tunnel as far as the security zone goes or something weird with your NAT policy. I would look at the tunnels security zone first, and then look at the NAT as I think it's actually more likely that you actually set your tunnel interface to your internal zone.
One thing that I might recommend is actually making a GlobalProtect zone. It makes creating access policies and the like a little bit easier if you are looking to lock down your VPN users access, and it helps keep it really simple as far as access rules go.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-25-2017 05:46 AM - edited 01-25-2017 05:52 AM
It was a bad NAT policy guys, thanks so much for the help. It is working now.
Now i just need to figure out how to get the routing correct to get to the internet, I can only access internal devices over the VPN atm.
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-15-2017 12:16 PM
@digitaltrance, If everything else is working, you need to take a look at your access route for GlobalProtect.
Check inside of the WebGUI > Network > GlobalProtect > Click configuration for a gateway > Agent tab > click on a config profile > Network Settings - Access route on the right hand side.
This is where the GP client will get its "access route" in order to know where to go.
If you only give it access to your internal network, then that is all it has access to.
If you want it to route all of its traffic over GP, then you can use a 0.0.0.0/0 network. But please be aware, that this can cause local access issues for the GP client.
I hope this helps.
Stay Secure,
Joe
Don't forget to Like items if a post is helpful to you!
- 2 accepted solutions
- 9143 Views
- 4 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- GP with saml authentication always redirects to idp in General Topics
- Global Protect is having issues with newer MACOS version. in Next-Generation Firewall Discussions
- Firwall is uable to send logs to the Panorma (Log collector is showing inactive) in Next-Generation Firewall Discussions
- SAML authentication with cookies won´t work in General Topics
- Request for Assistance: PA-850 Recovery Boot and Support Account Registration in Next-Generation Firewall Discussions