- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
attacking site and PAN
- LIVEcommunity
- Discussions
- General Topics
- Re: attacking site and PAN
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
attacking site and PAN
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-16-2014 12:48 AM
Hello
Few days ago I discovered site with some information about VMware Update Manager. I had a problem with it and I was searching for solution.
This site is www.bourgelat.net/cannot-patch-definitions-vmware-19988
I have PA with all licences but PAN software doesnt detect any bad traffic ![]()
I asked PAN to change categorization to malware site, but today I got email : New category: computer-and-internet-info
This site still trying to hurt Your computer, and PAN doesnt responds to it - is it OK?
I have security policy with thread prevention/av - but it doesnt stops it, hopefully my Symnatec Endpoint protection detecting it and blocking.
You can try to open www.bourgelat.net - this isn't https so in my opinion PAN should react in some way to this traffic.
Do You agree with me?
How it's possible when IE 10 with default configuration recomends to not enter to this site while PAN recategorization is computer-and-internet-info ?
Regards
Slawek
- Labels:
-
Troubleshooting
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-16-2014 05:37 AM
small update, www.bourgelat.net is classified as malware site by BightCloud Service, and it's blocked if You are blocking access by url filter (block malware sites) but if you are using PA url database you are under risk!
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-17-2014 12:19 PM
My symantec endpoint pretection is detecting that this site try to attact my computer using "red export kit redirect" now.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-17-2014 12:45 PM
Are you referring to this threat Web Attack: Red Exploit Kit Redirect: Attack Signature - Symantec Corp. ?
If yes then --> CVE-2009-4324
CVE-2009-4324 is covered with nine Threat ID's
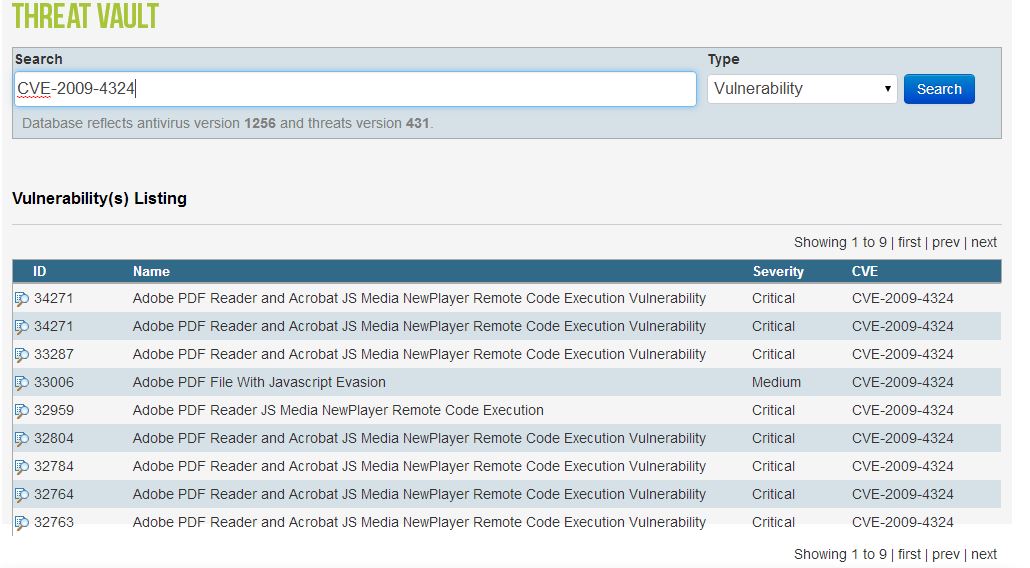
Are these nine Threat ID's all covered in your Vuln. Protection Profile ?
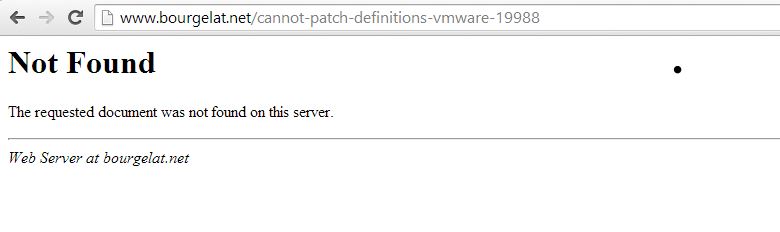
BTW, www.bourgelat.net/cannot-patch-definitions-vmware-19988 does not seem to be accessible at all
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-17-2014 01:22 PM
I can't verify it now, but probably - yes.
Today "www.bourgelat.net/cannot-patch-definitions-vmware-19988" isn't accessable but please try with www.bourgelat.net Please try with it.
I will check my security rules, but I'm sure that I blocing medium and critical threats.
Regards
SLawek
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-17-2014 01:26 PM
I don't see anything threatening on www.bourgelat.net
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-17-2014 01:37 PM
Although a google search for "www.bourgelat.net malware" shows very suspicious results...
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-19-2014 09:04 AM
Here You are report from today (SEP):
is it a false positive?
Regards
Slawek
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-19-2014 04:52 PM
Slawek,
We deal with situation by having two custom URL categories:
1. Temporary-Blocked = this allows you to immediately block it while you wait for a reclassification request to be processed by Palo Alto.
2. Custom-Blocked = This allows you to override the Pan-DB or Brightcloud category. Additionally you can use it to block parts of an otherwise good website.
Hope this provides a way to react quicker. It works quite well for us.
Phil
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-23-2014 05:22 AM
Hi Gafrol
In my opinion I have all this 9 CVE covered. Security policy has:
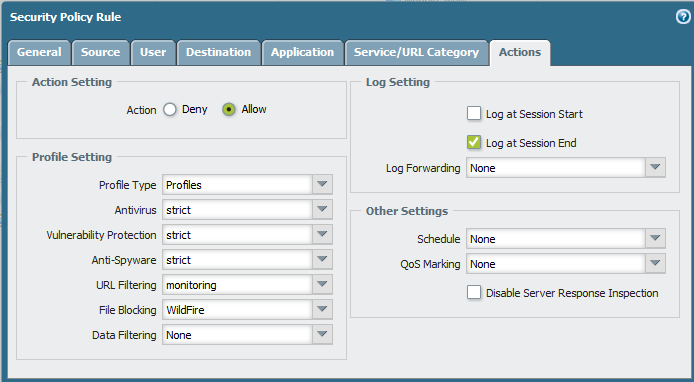
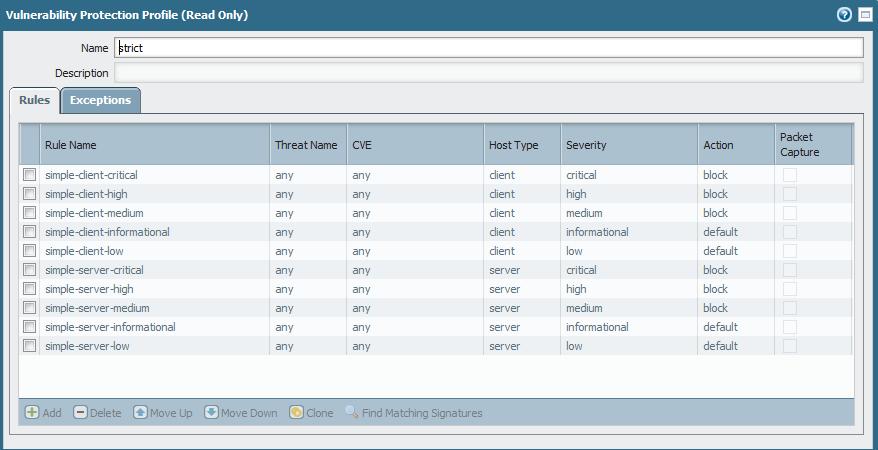
And "strict" thread prevention profile is a default one:
I try today to open "bourgelat.net" and again only SEP blocked this traffic.
admin@PA-200> show session all filter source 192.168.1.35 destination 91.121.93.111
--------------------------------------------------------------------------------
ID Application State Type Flag Src[Sport]/Zone/Proto (translated IP[Port])
Vsys Dst[Dport]/Zone (translated IP[Port])
--------------------------------------------------------------------------------
19100 web-browsing ACTIVE FLOW NS 192.168.1.35[52183]/Lan_A/6 (x.x.x.x[52427])
vsys1 91.121.93.111[80]/untrust (91.121.93.111[80])
39182 web-browsing ACTIVE FLOW NS 192.168.1.35[52188]/Lan_A/6 (x.x.x.x[35161])
vsys1 91.121.93.111[80]/untrust (91.121.93.111[80])
34969 web-browsing ACTIVE FLOW NS 192.168.1.35[52196]/Lan_A/6 (x.x.x.x[16722])
vsys1 91.121.93.111[80]/untrust (91.121.93.111[80])
56342 web-browsing ACTIVE FLOW NS 192.168.1.35[52193]/Lan_A/6 (x.x.x.x[18863])
vsys1 91.121.93.111[80]/untrust (91.121.93.111[80])
admin@PA-200> show session id 19100
Session 19100
c2s flow:
source: 192.168.1.35 [Lan_A]
dst: 91.121.93.111
proto: 6
sport: 52183 dport: 80
state: ACTIVE type: FLOW
src user: contoso\slawek
dst user: unknown
qos node: ethernet1/1, qos member N/A Qid 0
s2c flow:
source: 91.121.93.111 [untrust]
dst: x.x.x.x
proto: 6
sport: 80 dport: 52427
state: ACTIVE type: FLOW
src user: unknown
dst user: contoso\slawek
qos node: ethernet1/4.1, qos member N/A Qid 0
start time : Wed Apr 23 14:11:42 2014
timeout : 60 sec
time to live : 10 sec
total byte count(c2s) : 621
total byte count(s2c) : 66
layer7 packet count(c2s) : 5
layer7 packet count(s2c) : 1
vsys : vsys1
application : web-browsing
rule : Lan_A NAT - monitoring
session to be logged at end : True
session in session ager : True
session synced from HA peer : False
address/port translation : source + destination
nat-rule : NAT_Lan_A(vsys1)
layer7 processing : enabled
URL filtering enabled : True
URL category : malware-sites
session via syn-cookies : False
session terminated on host : False
session traverses tunnel : False
captive portal session : False
ingress interface : ethernet1/4.1
egress interface : ethernet1/1
session QoS rule : N/A (class 4)
In monitor tab using filter "( threatid eq 34271) or ( threatid eq 34271) or ( threatid eq 33287) or ( threatid eq 33006) or ( threatid eq 32959) or ( threatid eq 32804) or ( threatid eq 32784) or ( threatid eq 32764) or ( threatid eq 32763)" I see nothing in thread logs.
What is wrong with my configuration?
Regards
Slawek
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-23-2014 05:23 AM
Hi Hitsec
Thank for clarification, but the clue is that PA refued to change classification to malware sites.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-24-2014 08:01 AM
Slawek,
I fully understand and have experienced the same situation.
Phil
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-26-2014 12:32 AM
Problem reported to support, I will let You know if we made any progress.
Could someone verify using other NGF than PA and endpoint protetection than Symantec that this site try to hurt your computer and post small report of tests?
Regards
Slawek
- 6554 Views
- 13 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Redirect URL for Cortex XSOAR integration with DocuSign in Cortex XSOAR Discussions
- GlobalProtect, Release Notes, Build Numbers, CVE ?!?! in GlobalProtect Discussions
- How to request review of residual High-Risk rating when category dispute has been resolved? in General Topics
- Palo Alto Site to Site VPN ipsec tunnel up but unable to ping Source to destination in Next-Generation Firewall Discussions
- Existing traffic stops suddenly, and changing of interface MTU resolved it. in General Topics




