- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
DNS Signature Lookup Timeout Error
- LIVEcommunity
- Discussions
- General Topics
- Re: DNS Signature Lookup Timeout Error
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
DNS Signature Lookup Timeout Error
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-18-2020 05:01 PM
I'm seeing quite a lot of messages logged in the syslog output from my PA VM-100 running PAN-OS 10.0.0:
Aug 19 07:31:29 firewall-1 1,2020/08/19 07:31:29,007051000047085,SYSTEM,general,2560,2020/08/19 07:31:29,,general,,0,0,general,medium,"DNS signature lookup timed out",1461969,0x0,0,0,0,0,,firewall-1,0,0,1970-01-01T10:00:00.000+10:00
What exactly does "DNS signature lookup timed out" mean?
My VM has two local DNS servers configured, which are functioning well and the PA VM has access to do direct external lookups as well if it needs to do so. It is located on the end of a quiet 250/100M internet fibre connection here in Australia, so connectivity and congestion is not an issue.
The DNS Signature Lookup Timeout (ms) value is set to 300 - far far above what should be necessary.
Can anyone explain the traffic flow that might cause this (do these DNS queries go direct, or via configured resolver, and over what transport) ?
If this is an error, how do I go about debugging it to find the root cause?
Thanks,
Reuben
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-18-2020 07:11 PM
Hi Mate,
I would suggest identifying which traffic is causing these errors. Is it legit DNS query being timed out. Worth playing with the timers once more try increasing more, maybe some queries are timing out genuinely.
If it is like hitting a wall again, would suggest getting in touch with Palo TAC. Could be cosmetic bug or genuine misconfiguraton.
Hope that helps,
VR
Thanks & Regards,
Varun Rao
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-27-2020 11:37 PM
Thanks VR.
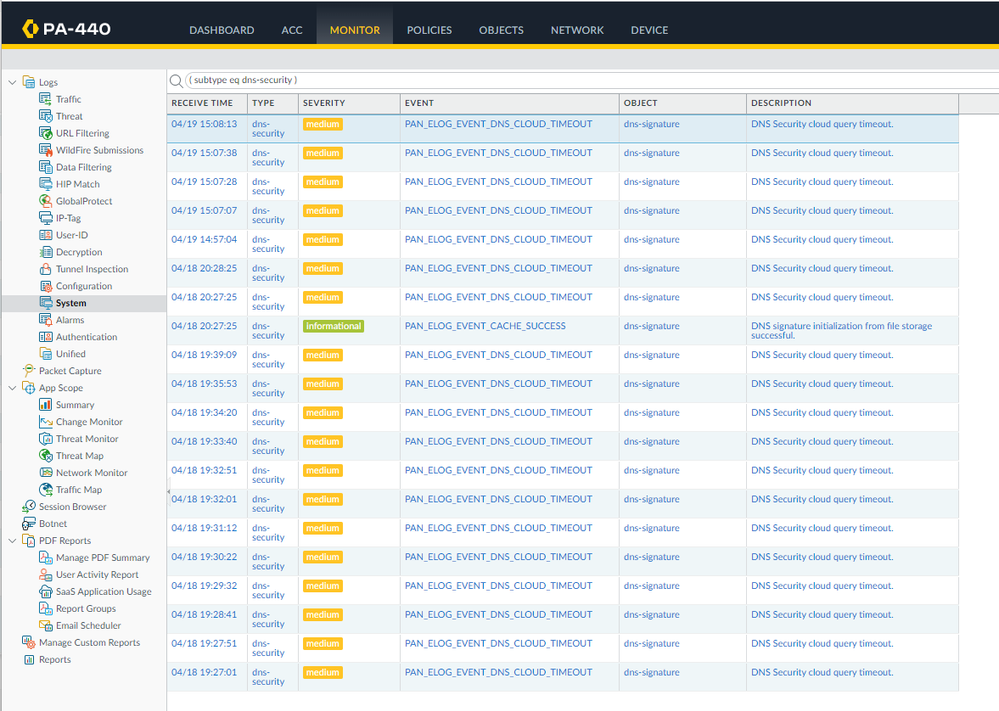
Can you suggest how I would find out what traffic it is? The log message doesn't indicate much other than a DNS query timed out. I'm assuming it is to do with the DNS Security feature.
Can you or anyone else explain the traffic flow behind this feature? I can't find it documented anywhere.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-20-2021 11:01 AM
Any resolution to this?
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-28-2021 03:23 AM - edited 11-28-2021 03:33 AM
Hi all,
I am also getting the same error in Paloalto. I changed the DNS signature lookup timeout to 2000 mseconds but still facing the same issue. Let me know if anyone got a solution or actual root cause of the issue
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-12-2023 04:29 AM
Hi @nevolex ,
In DNS security, there is a DP timeout for waiting for the DNS security verdict. When a DNS response comes after the timeout and the FW does not have a verdict, this response lets through. If the verdict is received later and indicates the previously let-through domain was malicious, this log is generated.
You could disable DNS security or set actions to allow. A permanent fix should be available in PAN-OS 10.0.10.
If you're already running a newer PAN-OS version then you might be hitting a different issue and I would recommend reaching out to support.
Hope this helps,
-Kiwi.
Cheers,
Kiwi
Please help out other users and “Accept as Solution” if a post helps solve your problem !
Read more about how and why to accept solutions.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-13-2023 02:51 AM
Hi @kiwi
I am using version 10.2.4, how do I set actions to allow please?
I currently whitelisted io.dns.service.paloaltonetworks.com, not to use app-id policy for that (I use service routes for palo alto inband traffic) and some of my policies have app-id with no ssl decryption I noticed a few web services stopped working with app-ids, just too hard to fix when you just want to allow all from trust - to untrust zone 🙂
Than you
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-13-2023 03:07 AM
Hi @nevolex ,
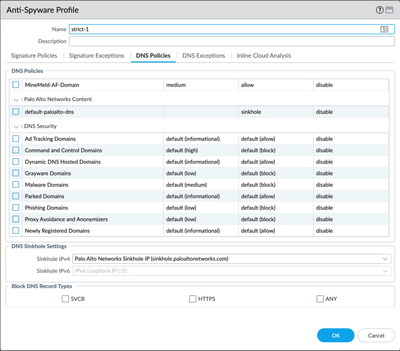
You can change the DNS Security actions in the Anti-Spyware profile:
You might want to reach out to support to see if you're hitting the same issue as seen in PAN-OS 10.0 or if you're hitting a different issue entirely.
Cheers,
Kiwi
Please help out other users and “Accept as Solution” if a post helps solve your problem !
Read more about how and why to accept solutions.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-18-2023 03:03 AM - edited 04-18-2023 08:21 PM
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-20-2023 11:51 PM
the issue was very likely related to app-id (default-app) used in the outbound polices, allowing all the ports/ apps for paloato urls resolved the issue (works for 24 hours already without flapping )
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-22-2023 01:44 AM
not related to app-id (default-app) , still experience the issues
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-05-2023 02:19 PM
it seems like the issue has been finally resolved by changing the mtu size on the wan interface to 1350bytes
thank
- 20404 Views
- 12 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Admin GUI Login Fails on WAN Interface - Slow Load & "Single Sign-On" Error on PA-410 in Panorama Discussions
- high priority 'Behavioral Threat' alert for smss.exe (system)? in Cortex XDR Discussions
- GP - Connect with SSL Only in General Topics
- How to show the auditing process of objects during policy auditing in Next-Generation Firewall Discussions
- Threat Signature Pattern Lookup in Advanced Threat Prevention Discussions