- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
GlobalProtect Authentication failed Error code -1 after PAN-OS update
- LIVEcommunity
- Discussions
- General Topics
- GlobalProtect Authentication failed Error code -1 after PAN-OS update
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
GlobalProtect Authentication failed Error code -1 after PAN-OS update
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-24-2019 06:49 PM
We are on PAN-OS 8.0.6 and have GlobalProtect and SAML w/ Okta setup. It has worked fine as far as I can recall.
However when we went to upgrade to 8.0.19 and any later version (after trying that one first), our VPN stopped working.
The client would just loop through Okta sending MFA prompts.
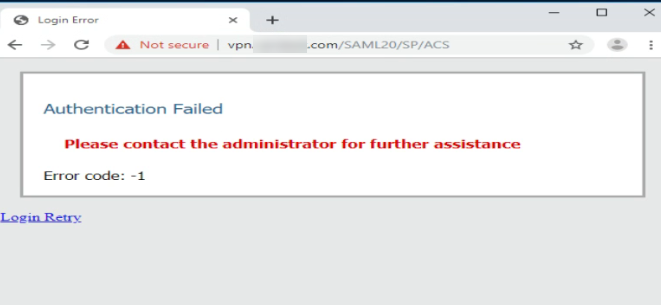
On the web client, we got this error: "Authentication failed Error code -1" with "/SAML20/SP/ACS" appended to the URL of the VPN site (after successfully authenticating with Okta.
When I downgrade PAN-OS back to 8.0.6, everything goes back to working just fine. No changes are made by us during the upgrade/downgrade at all.
Any advice/suggestions on what to do here?
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-09-2023 11:17 PM
Nothing else BiljanaZafirovska
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-14-2023 08:43 AM
Had same issue in setting up Okta. Clock difference was greater than
max_clock_skew 60
Set clock manually resolved "Authentication Failed" error
(active)> set clock date 2023/07/12 time 10:40:00
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-24-2025 04:31 AM
Hello, which certificate are you talking about?
- 49270 Views
- 18 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- GlobalProtect 6.3.3 + Duo SAML MFA loop after normal Windows login (works only via GP Credential Provider at Windows logon) in GlobalProtect Discussions
- [SOLVED] GPUDATE /FORCE DOESN'T WORK WITH GLOBAL PROTECT in GlobalProtect Discussions
- GP with saml authentication always redirects to idp in General Topics
- Global Protect is having issues with newer MACOS version. in Next-Generation Firewall Discussions
- Is It Possible to Distribute Client Certificates to iOS Devices Using GlobalProtect SCEP Without MDM? in General Topics