- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
GlobalProtect behind NAT/PAT Cetificate Issue.
- LIVEcommunity
- Discussions
- General Topics
- GlobalProtect behind NAT/PAT Cetificate Issue.
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-11-2017 08:16 AM
Hi,
I'm configuring my GlobalProtect VPN and Agent keep saying "CN name mismatch".
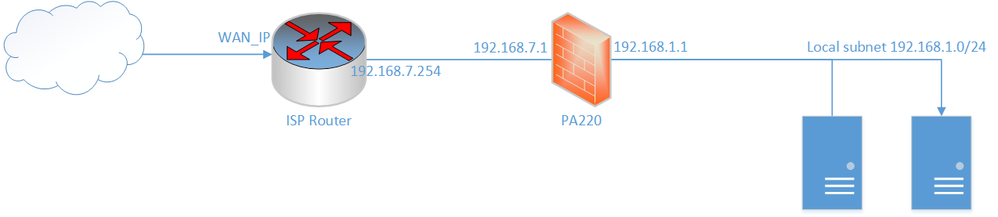
Here's my infrastructure :
The PA220 is behind the NAT of the ISP and all connexions on WAN_IP (that is the public IP) are translated to the address 192.168.7.1. As port 443 is already used, we're using WAN_IP:10443 that translates to 192.168.7.1:443 for the GlobalProtect.
Here's situated the problem. For the GP gateway certificate I must specify the CN that has to be WAN_IP:10443.
The Agent keeps prompting "The certificate CN name mismatch. The certificate is not issued to WAN_IP:10443". But when I open the certificate, it is issued to WAN_IP:10443...
I can continue ignoring this warning but it can't connect and prompts "my gateway : server certificate verification failed"
Any help please ?
BR,
Nael
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-11-2017 08:30 AM - edited 08-11-2017 08:32 AM
Hi @Naelwan
From your post I assume you created a self signed CA and certificate on your PA220. Is that correct?
If yes: did you import the root CA cert into your clients certificate trust store? And in addition you also need to specify the Root CA cert as trusted root CA in your global protect portal configuration.
And: How exactly did you create the certificate? Did you also add the wan IP as "IP" attribute in the certificate?
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-11-2017 08:30 AM - edited 08-11-2017 08:32 AM
Hi @Naelwan
From your post I assume you created a self signed CA and certificate on your PA220. Is that correct?
If yes: did you import the root CA cert into your clients certificate trust store? And in addition you also need to specify the Root CA cert as trusted root CA in your global protect portal configuration.
And: How exactly did you create the certificate? Did you also add the wan IP as "IP" attribute in the certificate?
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-11-2017 08:44 AM
Hi @Remo
Self signed CA on the PA220, yes.
Root CA cert is imported and specified in the portal conf.
I created the certificate with only the Wan IP in the Subject, just tried with the IP attribute with the WAN IP, It now works.
Thanks for your very reactive answers and your knowledge. Really appreciate it.
BR
Nael
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-16-2017 01:37 AM - edited 08-16-2017 03:13 AM
Well, @Remo, it worked only one time. from second try to now on : no more warning prompt but after network and config detection, i have the same error "gateway : server certificate verification failed"
There has been no modification made to the PA220 config between 1st and 2nd tries.
EDIT :
All I can see in the logs are :
Failed to connect to 192.168.7.1 on 443 (error: 0)
So obviously, agent-side gateway was misconfigured as it was pointing the PA220 interface and not the Public IP Address.
- 1 accepted solution
- 5060 Views
- 3 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- GlobalProtect, Release Notes, Build Numbers, CVE ?!?! in GlobalProtect Discussions
- GlobalProtect 6.3.3 + Duo SAML MFA loop after normal Windows login (works only via GP Credential Provider at Windows logon) in GlobalProtect Discussions
- [SOLVED] GPUDATE /FORCE DOESN'T WORK WITH GLOBAL PROTECT in GlobalProtect Discussions
- Globalprotect Client 6.2.7 disconnects multiple times in GlobalProtect Discussions
- Global Protect count current users not match statistics in GlobalProtect Discussions