- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
LSVPN not working when NAtted via Loopback
- LIVEcommunity
- Discussions
- General Topics
- LSVPN not working when NAtted via Loopback
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-27-2020 01:08 AM
Hi Community,
I got the following problem:
We have a running LSVPN with primary and secondary tunnel, which are connected on the hub on two different VRs, which sync themselves via iBGP - everything fine so far.
One of the satellite sites got two ISP lines, which should be used active/passive for redundancy.
Binding the IPSec tunnel on the physical interface is not possible, because when this link goes down (because provider got a problem or sth else), the down-interface won't try to establish a VPN - I need to use a loopback IP, which is natted and routed to the active ISP line.
I did it, and the first impression was, that this is working, BUT: After 1h, when the IPSec SA dies, the renegotiation is taking too long and the users got problems via VoIP, SAP and so on.
When checking the hub and GW firewall, I noticed, that the SSL connection to Portal was built up from Satellite to Hub (as expected), but the IPSec tunnel was built up from Hub to Satellite.
That's why I'm confused - here I'm in the position of doing the NAT myself and both providers are direct public IPs, the PAN can use, but this wouldn't work, when sitting behind a provider Internet box, which does the Natting for me.
Does anybody know, if it's even supported, to have the LSVPN satellite IPsec sitting on a loopback interface and using an active/passive Internet redundancy?
I'm happy for any inputs here.
Regards
Chacko
Chacko
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-14-2020 12:20 AM
TAC confirmed:
This request is not possible with LSVPN.
When trying to achive ISP redundancy on satellite side, a workaround would be a parallel classical VPN tunnel with different metrics.
A feature request was created for this:
FR ID 12468
Chacko
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-29-2020 01:17 AM
could you please share rough sketch.
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-29-2020 03:35 AM
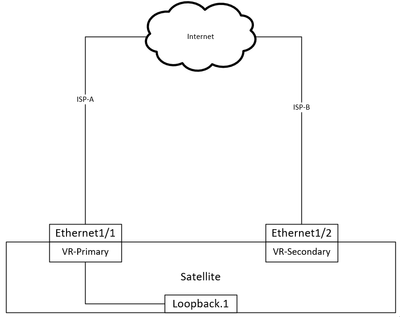
That's the setup.
Default Route is with metric 10 to ISP-A with Path-Monitoring, Default-Route with metric 20 is to next vr vr-secondary.
Loopback.1 is the source interface for lsvpn ipsec tunnel.
When configuring the ipsec tunnel directly on ethernet1/1 without nat - tunnel works.
When configuring the ipsec tunnel on loopback with static-nat to ISP-A, the Portal connection is initiated via Satellite, but the IPSec is initiated via Hub
Chacko
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-29-2020 05:40 AM
how do you check in lsvpn if hub is intiator ?
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-29-2020 05:47 AM
when I have a look at the session table on the sateliite, I can see an outgoing session via SSL to LSVPN-Portal.
But the IPSec tunnel is incoming with source of the LSVPN-GW and that cannot be right.
In this special case, I can do a static nat, but if this is an ISP box with dynamic ip and we are just a box behind it, incoming IPSec is not possible and not by LSVPN design.
Chacko
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-14-2020 12:20 AM
TAC confirmed:
This request is not possible with LSVPN.
When trying to achive ISP redundancy on satellite side, a workaround would be a parallel classical VPN tunnel with different metrics.
A feature request was created for this:
FR ID 12468
Chacko
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-13-2022 07:56 AM
adding to that confusion...
the hub is not the initiator!
it just looks that way because the firewall does not recognize the incoming traffic, not seeing the outgoing traffic in the logs adds to that confusion
anyhow, according to Palo, as everyone can write anything in these forums, it shouldn't be taken seriously if someone writes that palo said something is not supported...
at least we were promised that this is a supported and working feature (at least working under lab conditions), as for the working part... still working with palo TAC on it who also referred me to this thread 🙂
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-17-2023 01:42 PM
Hi, does anyone have any updates? I tried LSVPN using a loopback on the satellite and it doesn't work for me. Packets go into the tunnel but don't come out on the other end.
Did PA ever do the feature request?
-Keith
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-21-2023 06:26 AM
I talked to Palo about this and after understanding how this works, I can say that they do not plan to implement this.
I worked around this by creating two LSVPNs on the same firewall, one as backup in a different virtual router but both times using the actual external interface, not a loopback.
The goal of redundancy was still achieved with that for me.
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-22-2023 08:13 PM
That was a good idea to use 2 VR's. Thanks for the update.
- 1 accepted solution
- 8884 Views
- 9 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!