- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
policy is clear yet traffic is still DENIED
- LIVEcommunity
- Discussions
- General Topics
- Re: policy is clear yet traffic is still DENIED
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-13-2020 07:40 PM
hi all, we have a policy that clearly states FROM and TO objects and SMB_override (custom app, I presume, created earlier) as the application. The service is configured as Application-default. As per Monitor, it goes straight through to the deny rule ignoring our Allow rule. The application is correctly identified, the port is right. all looks good. Yet it's being denied. It's not the first time PA does it. It's very frustrating. People now want ANY to ANY because PA works half the time
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-14-2020 12:03 AM
If the rule isn't there on the firewall, that means it hasn't been pushed down from Panorama yet, which would explain why the traffic is hitting the deny rule
PANgurus - Strata & Prisma Access specialist
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-13-2020 08:59 PM
What version of PAN-OS are you running? It doesn't give a lot of confidence that you are talking about using a custom app-id entry and you're presuming how it was configured if I'm being honest. How was the custom app-id configured? Are you using an application-override policy to override the traffic to your custom SMB_override app-id entry, or are you relying on a signature to identify the traffic?
When you log into the CLI and run the test security-policy-match command and enter the traffic exactly as displayed in one of the denied log entries is it showing a match in your security rulebase? If you can, share a few copies of the log that isn't matching the target security rulebase entry and the actual entry; chances are something is just improperly configured.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-13-2020 09:19 PM
Thank you, appreciate your help. We are running 9.0.9
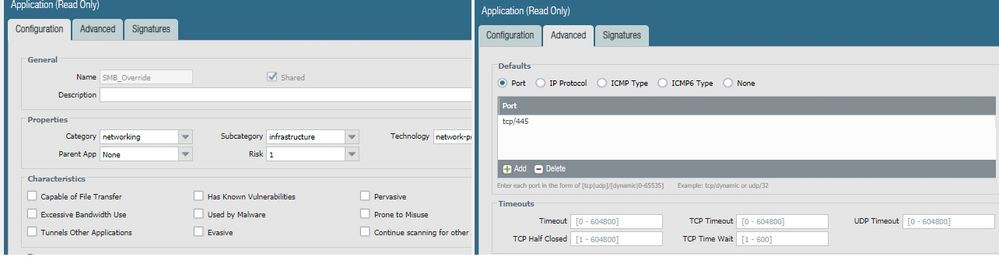
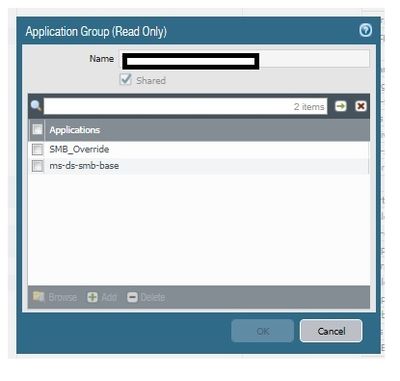
Just a basic policy with a custom application. Basic custom app (SMB_Override) with a port (tcp/445). PA correctly recognizes it. I can do screenshot. I can see in the logs it's tcp 445. Yet it just does not work. It's not the first time.
I just had a look and the policy is set to "universal". all the rest are Interzone.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-13-2020 09:27 PM
Screenshots would help a lot in this case. The issue with the custom app-id is really more to do with how it, and associated rulebase entries, have been configured. Does your SMB_override have a default port of tcp/445 listed so that your application-default on the service will actually function? Are you using a signature to identify the traffic or an application-override entry? I would assume with something named SMB_override you are simply using an application-override entry to disable layer7 processing on SMB traffic.
Generally speaking, the firewall won't simply skip processing the traffic properly. More than likely, the denied traffic isn't actually 100% matching something within the security rulebase entry. That could have something to do with how the application-override (assuming there is an entry) is setup, or how the security rulebase entry itself is setup. Something however is causing the firewall to think that traffic doesn't match anymore.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-13-2020 09:53 PM - edited 12-13-2020 09:57 PM
no signature. A strict default port. That is hard set in the app.
it is logical that it shouldn't just skip.
new update: I am looking at the firewall direct and the rule is missing all together, whereas in Panorama it's there. It could be that when new policy was created and was not pushed?
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-14-2020 12:03 AM
If the rule isn't there on the firewall, that means it hasn't been pushed down from Panorama yet, which would explain why the traffic is hitting the deny rule
PANgurus - Strata & Prisma Access specialist
- 1 accepted solution
- 8085 Views
- 5 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- XFF IP Address Logging clarification and impact in General Topics
- IPSEC to Azure establish but cannot use traceroute in General Topics
- Cloud NGFW: Mandatory Panorama Upgrade to 11.2.7-h4 or higher for managing Cloud NGFW Firewalls. in General Topics
- Intrazone-default Rule in Next-Generation Firewall Discussions
- Prisma Access Explicit Proxy — Anti‑Spyware behavior when DNS bypasses Prisma (logging subtype + test methodology) in Prisma Access Discussions