- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
SYN-Flood packets dropped by unknown rule
- LIVEcommunity
- Discussions
- General Topics
- Re: SYN-Flood packets dropped by unknown rule
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-30-2014 01:49 AM
Hi everybody,
we got a lot of syn-packets which were dropped by the rule any-allow. But we haven't this rule, so is it a inbuilt rule and
why do i need a DoS-Rule to be protected against Syn-Floods if there is a builtin rule.
Cheers klaus
- Labels:
-
Configuration
-
Content-ID
-
Troubleshooting
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-31-2014 06:33 AM
So it should be a bug.
Maybe restarting some services will solve this but I can't say you'll not see same behaviour then, or not.
Best; I advice an upgrade to 5.0.11
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-30-2014 08:06 AM
Hello Sir,
Do you have a DOS protection profile configured on your PAN firewall..? As per my knowledge, PAN is not having such inbuilt rule on it. Could you please expand the session details as mentioned below and update here.
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-30-2014 08:13 AM
did you check zone protection ?
if no zone protection or dos protection is used then better to open a case.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-30-2014 08:14 AM
Maybe you have flood protection turned on in a network profile? That might do it.
Mike
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-30-2014 08:38 AM
Hello kdd,
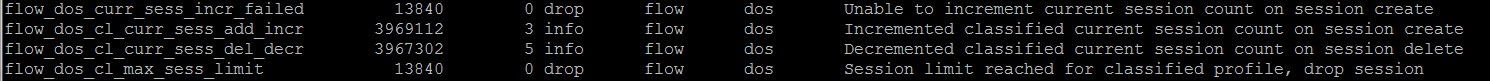
From the description we see that the inbuilt rule has taken charge. What we will have to look is at the time of issue did we see any DOS or zone protection profile counters triggered.(If they are configured )
This can be seen by " less dp0-log dp-monitor.log" Also we can check the commands to see the triggers for the syn flood
show dos-protection rule <rule name>
show zone-protection zone <zone name>
Example for Dos counters:
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-31-2014 03:05 AM
Thx for your comments.
to make it more visible and comprehensible what the zero point is:
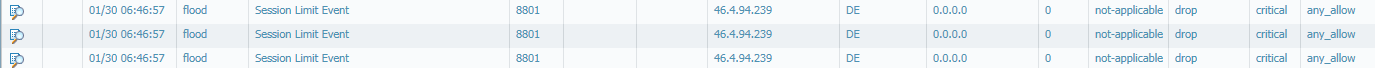
- log entry
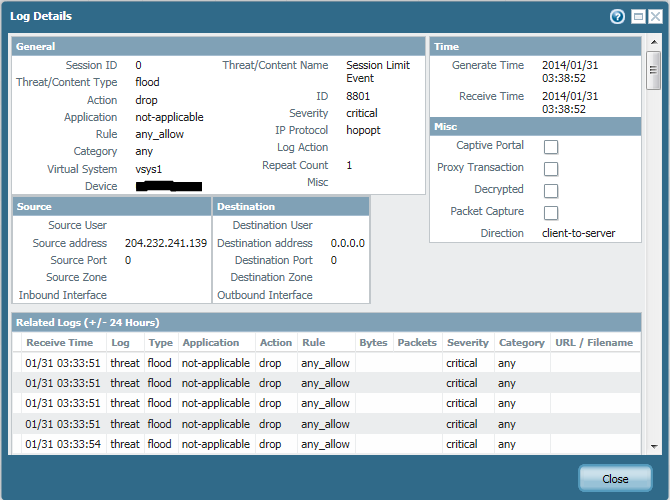
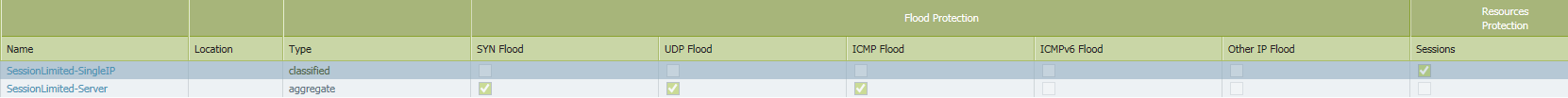
- DoS rule
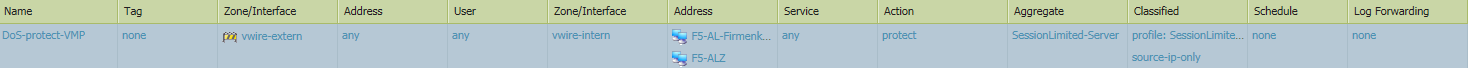
- DoS protection profil
- DoS global counters
what i understood so far is that there seems to be a inbuilt rule which was taken in advance because the limitation of our own DoS-protection rule isn't as narrow as the default
where can i get information about the settings of the any-allow rule ? it sounds also strange to me to call a rule any-allow and then drop the packets. anywhere,
but there should be a clue to the inbuilt rule
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-31-2014 05:43 AM
Since it says "Session limit event" and your rule name is different, this is not normal.
What os version you are using ?
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-31-2014 06:17 AM
I am not sure if this is an unlisted bug but if you have time to upgrade it will be better.
There are some Dos related issues (49337—Traffic was blocked even though the DoS Protection policy was configured to allow it. - but written that fixed with 5.0.5)
Have you ever used "any_allow" name for a rule ?
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-31-2014 06:28 AM
yes, as we started with new zones there was a "any-allow" rule but not yet
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-31-2014 06:33 AM
So it should be a bug.
Maybe restarting some services will solve this but I can't say you'll not see same behaviour then, or not.
Best; I advice an upgrade to 5.0.11
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-31-2014 06:49 AM
thx for your assistance unfortunately there is still another problem with this version
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-10-2014 12:06 AM
after upgrade to 5.0.10 this behavior is completely disappeared. Thanks to all for your support
Regards Klaus
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-10-2014 05:53 AM
kdd if you're running HA you might want to move to 5.0.11 ASAP.... there are some huge HA bugs (dataplane restarts....) in 5.0.10
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-10-2014 07:36 AM
we wanna upgrade to 5.0.11. it is also an advice of panos but thank you too and is also done fast
- 1 accepted solution
- 8201 Views
- 14 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- PA-415-5G not working with fresh T-Mobile SIM in General Topics
- Tunnel Traffic from ISP2 IP Working Despite Default Route on ISP1 – Need Insights? in Next-Generation Firewall Discussions
- Global Protect Product IDEA ! in GlobalProtect Discussions
- Chromium-based traffic issue in Next-Generation Firewall Discussions
- Pre Processing script for dropping multiple similar incidents in Cortex XSOAR Discussions




