- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Unable to assign Security Policy to Users or Groups
- LIVEcommunity
- Discussions
- General Topics
- Re: Unable to assign Security Policy to Users or Groups
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Unable to assign Security Policy to Users or Groups
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-23-2013 10:33 AM
Hi -
We are using User-ID Agents to create user-to-IP mappings and I've got group mapping configured on the firewall itself and I can browse through my ldap groups. However, when I go to Policies > Security Policy I am unable to select either individual users OR groups to assign the policy to... Nothing populates. Am I missing something somewhere? Seems like it would be straight forward after configuring group mapping. Thanks!
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-23-2013 12:13 PM
you can use
show shared server-profile ldap
in configure mode.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-23-2013 12:19 PM
admin@Ada-PAN-M100(primary-active)# show template "US Lab" config shared server-profile ldap LDAP-Group-Mapping
LDAP-Group-Mapping {
server {
ldap-adam-apps.intranet.local {
port 389;
address ldap-adam-apps.intranet.local;
}
}
ldap-type active-directory;
timelimit 30;
bind-timelimit 30;
ssl no;
domain na;
base ou=groups,o=alticor;
bind-dn cn=ldap-alt-paloalto,ou=users,o=alticor;
bind-password -AQ==ZtJUGAV/ZcKHS4UkVNe1zXA0x2s=uvilr+9UMZiJgEAXcnLCXA==;
}
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-23-2013 05:12 PM
The M-100 (and Panorama in general) will not populate users or groups when creating rules until a rule has been created with that user/group at least once. The reason for this is because of the huge amount of load it would take if you had several hundred firewalls, each with different domains configured with a single Panorama (imagine how long it would take to query each firewall, which would query each domain, and return the full group and user list).
If you create the policy local to the firewall, the group will indeed prepopulate because the scope is limited to that one firewall's set of user and group data.
Once you create a policy which has a user- or group-name on Panorama, that user/group will be available for future rules. Note that there is no integrity check, so a mistake will be allowed through and simply fail to match. I recommend copying the user data from an LDAP browser so you don't have to worry about the syntax.
Hope this helps,
Greg Wesson
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-23-2013 05:21 PM
This sound like a bug...
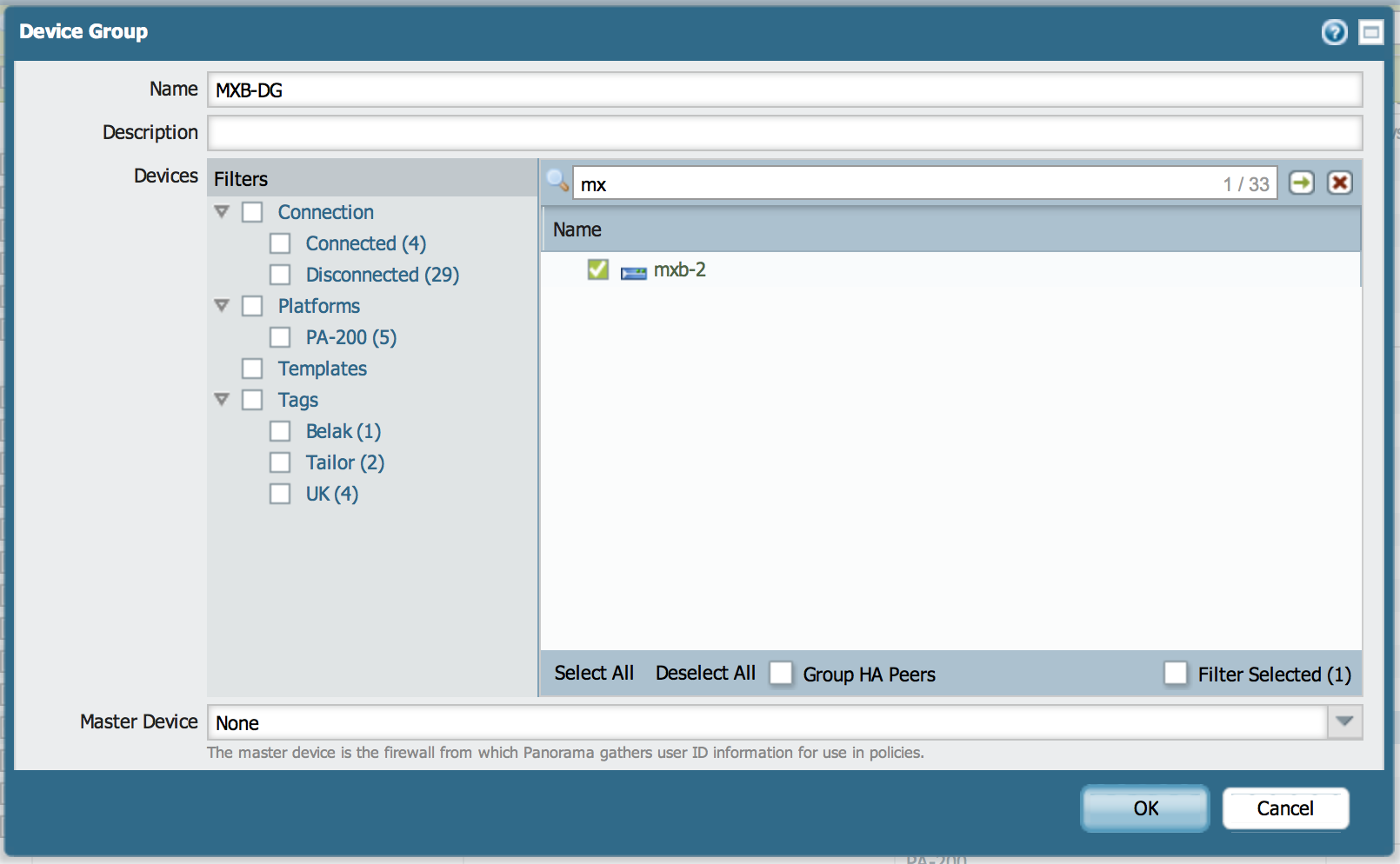
Was the master device selected in the Device Group configuration?
User-ID groups should be pulled from the Master Device for selection in Policy and will also be queried upon search to pull individual users as well.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-04-2013 10:47 AM
Yes there is a master device set. We went ahead and opened a case on this issue.
- 9979 Views
- 19 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- EDL Performance and Refresh Handling in Panorama in Next-Generation Firewall Discussions
- XFF IP Address Logging clarification and impact in General Topics
- [SOLVED] GPUDATE /FORCE DOESN'T WORK WITH GLOBAL PROTECT in GlobalProtect Discussions
- Security Policy Disappears After Commit – Palo Alto in Azure with Panorama in Next-Generation Firewall Discussions
- EDL Scalability & Platform Limits – Best Practices in Next-Generation Firewall Discussions




