- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
VPN Tunnel down - Troubleshoot
- LIVEcommunity
- Discussions
- General Topics
- Re: VPN Tunnel down - Troubleshoot
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
VPN Tunnel down - Troubleshoot
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-23-2014 12:58 AM
Hi Admins,
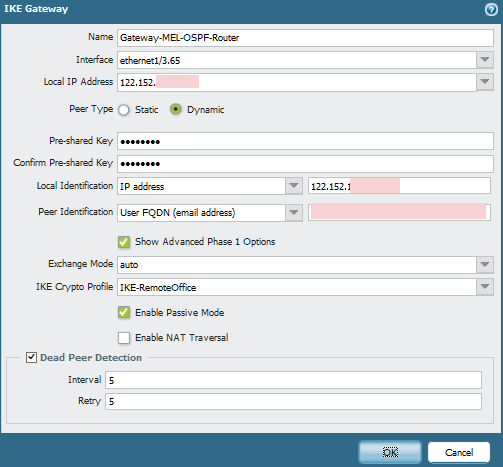
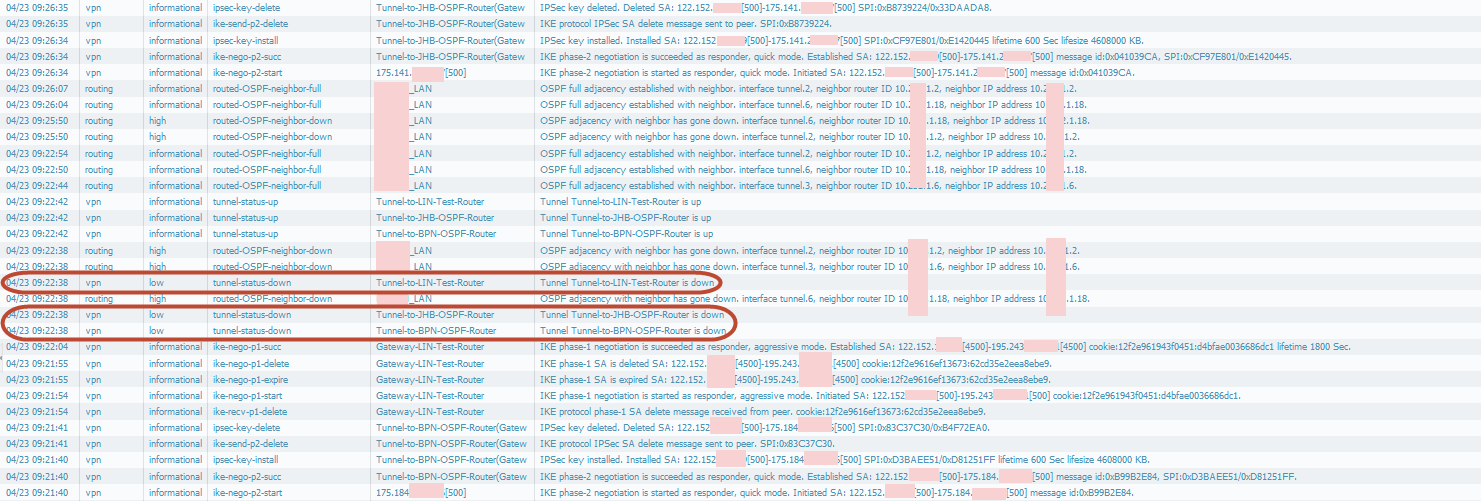
I need some help to troubleshoot our problem with the VPN Tunnels. We installed a Cisco to PaloAlto VPN tunnel. The PA in passive mode. But constantly the tunnels go down.
Here are some log outputs:
less mp-log ikemgr.log
2014-04-23 09:21:54 [DEBUG]: sockmisc.c:335:sendfromto(): sockname 122.152.XX.XX[500]
2014-04-23 09:21:54 [DEBUG]: sockmisc.c:337:sendfromto(): send packet from 122.152.XX.XX[500]
2014-04-23 09:21:54 [DEBUG]: sockmisc.c:339:sendfromto(): send packet to 195.243.XX.XX[500]
2014-04-23 09:21:54 [DEBUG]: sockmisc.c:524:sendfromto(): 1 times of 200 bytes message will be sent to 195.243.XX.XX[500]
2014-04-23 09:21:54 [DEBUG]: sockmisc.c:528:sendfromto():
12f2e961 943f0451 d4bfae00 36686dc1 84100400 00000000 000000c8 000000ac
00010201 2ab0d308 1a8e3074 18626886 1234948e 17dc58a4 57f2de84 1578afda
102d83be 0d000044 5b623b9b 2c433c3f 179fdd48 904deb9c 6858a3cc 08a3ddfe
246b2fa2 ea51bbfe 48febd37 f445bbc7 194dd9f2 eee1b306 6b1a70b1 c9a4ca81
ab580dbf 8454f5c4 0d000018 4048b7d5 6ebce885 25e7de7f 00d6c2d3 80000000
0d000014 afcad713 68a1f1c9 6b8696fc 77570100 00000014 a9b9b103 4f7e50a2
513b47b1 00bb85a9
2014-04-23 09:21:54 [DEBUG]: ikev1.c:1672:isakmp_ph1resend(): resend phase1 packet 12f2e961943f0451:d4bfae0036686dc1
2014-04-23 09:21:54 [DEBUG]: isakmp_agg.c:1354:agg_r1send(): PH1 state changed: 2 to 3 [PHASE1ST_MSG1SENT] @agg_r1send
2014-04-23 09:21:55 [INFO]: ikev1.c:2488:log_ph1expired(): ====> PHASE-1 SA LIFETIME EXPIRED <====
====> Expired SA: 122.152.XX.XX[4500]-195.243.XX.XX[4500] cookie:12f2e9616ef13673:62cd35e2eea8ebe9 <====
2014-04-23 09:21:55 [DEBUG]: ikev1.c:1778:isakmp_ph1expire(): PH1 state changed: 14 to 14 [PHASE1ST_EXPIRED] @isakmp_ph1expire
2014-04-23 09:21:55 [INFO]: ikev1.c:2471:log_ph1deleted(): ====> PHASE-1 SA DELETED <====
====> Deleted SA: 122.152.XX.XX[4500]-195.243.XX.XX[4500] cookie:12f2e9616ef13673:62cd35e2eea8ebe9 <====
2014-04-23 09:21:55 [DEBUG]: oakley.c:3088:oakley_delivm(): IV freed
Apr 23 09:21:55 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:21:55 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:21:55 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
Apr 23 09:21:55 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
2014-04-23 09:21:55 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:21:55 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:21:55 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:21:55 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:21:55 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:21:55 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
2014-04-23 09:21:56 [DEBUG]: ikev1.c:2978:isakmp_send(): 676 bytes from 122.152.XX.XX[500] to 195.243.XX.XX[500]
2014-04-23 09:21:56 [DEBUG]: ikev1.c:2978:isakmp_send(): 548 bytes from 122.152.XX.XX[500] to 195.243.XX.XX[500]
2014-04-23 09:21:56 [DEBUG]: sockmisc.c:335:sendfromto(): sockname 122.152.XX.XX[500]
2014-04-23 09:21:56 [DEBUG]: sockmisc.c:337:sendfromto(): send packet from 122.152.XX.XX[500]
2014-04-23 09:21:56 [DEBUG]: sockmisc.c:339:sendfromto(): send packet to 195.243.XX.XX[500]
2014-04-23 09:21:56 [DEBUG]: sockmisc.c:524:sendfromto(): 1 times of 548 bytes message will be sent to 195.243.XX.XX[500]
2014-04-23 09:21:56 [DEBUG]: sockmisc.c:528:sendfromto():
12f2e961 943f0451 d4bfae00 36686dc1 84100400 00000000 00000224 00000208
00010100 12f2e961 943f0451 d4bfae00 36686dc1 01100400 00000000 000002a4
04000038 00000001 00000001 0000002c 01010001 00000024 01010000 80010007
800e0100 80020006 8004000e 80030001 800b0001 800c0708 0a000104 56939011
c3d52772 6e02adab c4c0d526 db830833 d8dce02f 44c3bed9 97c8bb8a 314fb461
7ac98c13 321ee2ff 6494bed1 5f770831 bd307330 4a0b312e aae14037 2e7858c3
15032d22 4ae547c1 cfafbcf3 0a529a4c 010d34d7 91559795 57a1b4f8 e8e8be28
674538d5 ecac7b67 7f9b1adf 54d342c1 c60a17bb d68ed488 58e99359 0a3a22f9
c0407827 146adc07 08df768c ba6edc47 fd2d571a 1456b0b0 296cbe46 857fbf4c
8329884f 32b683a6 899617d2 4c10331c 5ea538bb edf73f4b e3b7007b 1690c7ef
3f4ea8b1 099cc8c0 b5f7c6dd 5b8e4d6a d4b67916 638f2daa fcc93d4f 404fc47d
ac0036f0 e58da5fa e4ed00de df3d02fa 20deaa25 bce3d9c2 337c35e2 05000014
fc3831ea 28df553b 1409e4fa 55fdcc28 0800000c 01000000 7a98911d 0d000044
75c0339f fddf9c29 17ee2f57 52014-04-23 09:21:56 [DEBUG]: ikev1.c:2978:isakmp_send(): 200 bytes from 122.152.XX.XX[500] to 195.243.XX.XX[500]
2014-04-23 09:21:56 [DEBUG]: sockmisc.c:335:sendfromto(): sockname 122.152.XX.XX[500]
2014-04-23 09:21:56 [DEBUG]: sockmisc.c:337:sendfromto(): send packet from 122.152.XX.XX[500]
2014-04-23 09:21:56 [DEBUG]: sockmisc.c:339:sendfromto(): send packet to 195.243.XX.XX[500]
2014-04-23 09:21:56 [DEBUG]: sockmisc.c:524:sendfromto(): 1 times of 200 bytes message will be sent to 195.243.XX.XX[500]
2014-04-23 09:21:56 [DEBUG]: sockmisc.c:528:sendfromto():
12f2e961 943f0451 d4bfae00 36686dc1 84100400 00000000 000000c8 000000ac
00010201 2ab0d308 1a8e3074 18626886 1234948e 17dc58a4 57f2de84 1578afda
102d83be 0d000044 5b623b9b 2c433c3f 179fdd48 904deb9c 6858a3cc 08a3ddfe
246b2fa2 ea51bbfe 48febd37 f445bbc7 194dd9f2 eee1b306 6b1a70b1 c9a4ca81
ab580dbf 8454f5c4 0d000018 4048b7d5 6ebce885 25e7de7f 00d6c2d3 80000000
0d000014 afcad713 68a1f1c9 6b8696fc 77570100 00000014 a9b9b103 4f7e50a2
513b47b1 00bb85a9
2014-04-23 09:21:56 [DEBUG]: ikev1.c:1672:isakmp_ph1resend(): resend phase1 packet 12f2e961943f0451:d4bfae0036686dc1
Apr 23 09:21:59 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:21:59 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:21:59 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:21:59 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:21:59 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
2014-04-23 09:21:59 [DEBUG]: ikev1.c:2978:isakmp_send(): 676 bytes from 122.152.XX.XX[500] to 195.243.XX.XX[500]
2014-04-23 09:21:59 [DEBUG]: ikev1.c:2978:isakmp_send(): 548 bytes from 122.152.XX.XX[500] to 195.243.XX.XX[500]
2014-04-23 09:21:59 [DEBUG]: sockmisc.c:335:sendfromto(): sockname 122.152.XX.XX[500]
2014-04-23 09:21:59 [DEBUG]: sockmisc.c:337:sendfromto(): send packet from 122.152.XX.XX[500]
2014-04-23 09:21:59 [DEBUG]: sockmisc.c:339:sendfromto(): send packet to 195.243.XX.XX[500]
2014-04-23 09:21:59 [DEBUG]: sockmisc.c:524:sendfromto(): 1 times of 548 bytes message will be sent to 195.243.XX.XX[500]
2014-04-23 09:21:59 [DEBUG]: sockmisc.c:528:sendfromto():
12f2e961 943f0451 d4bfae00 36686dc1 84100400 00000000 00000224 00000208
00010100 12f2e961 943f0451 d4bfae00 36686dc1 01100400 00000000 000002a4
04000038 00000001 00000001 0000002c 01010001 00000024 01010000 80010007
800e0100 80020006 8004000e 80030001 800b0001 800c0708 0a000104 56939011
c3d52772 6e02adab c4c0d526 db830833 d8dce02f 44c3bed9 97c8bb8a 314fb461
7ac98c13 321ee2ff 6494bed1 5f770831 bd307330 4a0b312e aae14037 2e7858c3
15032d22 4ae547c1 cfafbcf3 0a529a4c 010d34d7 91559795 57a1b4f8 e8e8be28
674538d5 ecac7b67 7f9b1adf 54d342c1 c60a17bb d68ed488 58e99359 0a3a22f9
c0407827 146adc07 08df768c ba6edc47 fd2d571a 1456b0b0 296cbe46 857fbf4c
8329884f 32b683a6 899617d2 4c10331c 5ea538bb edf73f4b e3b7007b 1690c7ef
3f4ea8b1 099cc8c0 b5f7c6dd 5b8e4d6a d4b67916 638f2daa fcc93d4f 404fc47d
ac0036f0 e58da5fa e4ed00de df3d02fa 20deaa25 bce3d9c2 337c35e2 05000014
fc3831ea 28df553b 1409e4fa 55fdcc28 0800000c 01000000 7a98911d 0d000044
75c0339f fddf9c29 17ee2f57 52014-04-23 09:21:59 [DEBUG]: ikev1.c:2978:isakmp_send(): 200 bytes from 122.152.XX.XX[500] to 195.243.XX.XX[500]
2014-04-23 09:21:59 [DEBUG]: sockmisc.c:335:sendfromto(): sockname 122.152.XX.XX[500]
2014-04-23 09:21:59 [DEBUG]: sockmisc.c:337:sendfromto(): send packet from 122.152.XX.XX[500]
2014-04-23 09:21:59 [DEBUG]: sockmisc.c:339:sendfromto(): send packet to 195.243.XX.XX[500]
2014-04-23 09:21:59 [DEBUG]: sockmisc.c:524:sendfromto(): 1 times of 200 bytes message will be sent to 195.243.XX.XX[500]
2014-04-23 09:21:59 [DEBUG]: sockmisc.c:528:sendfromto():
12f2e961 943f0451 d4bfae00 36686dc1 84100400 00000000 000000c8 000000ac
00010201 2ab0d308 1a8e3074 18626886 1234948e 17dc58a4 57f2de84 1578afda
102d83be 0d000044 5b623b9b 2c433c3f 179fdd48 904deb9c 6858a3cc 08a3ddfe
246b2fa2 ea51bbfe 48febd37 f445bbc7 194dd9f2 eee1b306 6b1a70b1 c9a4ca81
ab580dbf 8454f5c4 0d000018 4048b7d5 6ebce885 25e7de7f 00d6c2d3 80000000
0d000014 afcad713 68a1f1c9 6b8696fc 77570100 00000014 a9b9b103 4f7e50a2
513b47b1 00bb85a9
2014-04-23 09:21:59 [DEBUG]: ikev1.c:1672:isakmp_ph1resend(): resend phase1 packet 12f2e961943f0451:d4bfae0036686dc1
Apr 23 09:21:59 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:21:59 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:21:59 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:21:59 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:21:59 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
2014-04-23 09:22:00 [DEBUG]: ikev1_natt.c:348:natt_keepalive_send(): KA: 122.152.XX.XX[4500]->195.243.XX.XX[4500]
2014-04-23 09:22:00 [DEBUG]: sockmisc.c:335:sendfromto(): sockname 122.152.XX.XX[4500]
2014-04-23 09:22:00 [DEBUG]: sockmisc.c:337:sendfromto(): send packet from 122.152.XX.XX[4500]
2014-04-23 09:22:00 [DEBUG]: sockmisc.c:339:sendfromto(): send packet to 195.243.XX.XX[4500]
2014-04-23 09:22:00 [DEBUG]: sockmisc.c:524:sendfromto(): 1 times of 1 bytes message will be sent to 195.243.XX.XX[4500]
2014-04-23 09:22:00 [DEBUG]: sockmisc.c:528:sendfromto():
ff
2014-04-23 09:22:04 [DEBUG]: isakmp.c:944:isakmp_handler(): ===
2014-04-23 09:22:04 [DEBUG]: isakmp.c:945:isakmp_handler(): 548 bytes message received from 195.243.XX.XX[500]
2014-04-23 09:22:04 [DEBUG]: isakmp.c:948:isakmp_handler():
12f2e961 943f0451 00000000 00000000 01100400 00000000 00000224 0d000038
00000001 00000001 0000002c 01010001 00000024 01010000 80010007 800e0100
80020006 8004000e 80030001 800b0001 800c0708 0d000014 4a131c81 07035845
5c5728f2 0e95452f 0d000014 439b59f8 ba676c4c 7737ae22 eab8f582 0d000014
7d9419a6 5310ca6f 2c179d92 15529d56 04000014 90cb8091 3ebb696e 086381b5
ec427b1f 0a000104 7273d78a efa09af6 a945fe1a 1b38a728 f2f7af2b 991697fc
68754405 d5461382 87282931 2c813c92 87894734 c0db0b03 907cf85c 8a39e128
45c7d89e 2c2fa9d7 19a27248 4c9d6fb3 f0a58fc6 d7179729 0c20a685 cc870a13
1f14734e 58a7c512 6af79365 e02d43b1 b6302371 4a4c312a bc5e0df3 f4f247ac
3883ed09 ee1be047 a7f55741 bdb7818b c32e8113 a9432a8c 6ae25ca0 21390e6c
e9c1728c 7f33102f c8865034 48752c8e 290c51db 75724b72 61743046 20bf7370
4970e1df 5a8507ed 0a6a4154 0ccfda99 8660b6ed 610ba01a c1e232c1 00ce0c6a
b4744f6a 4ae7b048 650f52a0 a2ec5441 6cef8788 4416ac8b 3bc806cd 4cae5d20
7c6fb1a0 05e7905c 050000182014-04-23 09:22:04 [DEBUG]: sockmisc.c:335:sendfromto(): sockname 122.152.XX.XX[500]
2014-04-23 09:22:04 [DEBUG]: sockmisc.c:337:sendfromto(): send packet from 122.152.XX.XX[500]
2014-04-23 09:22:04 [DEBUG]: sockmisc.c:339:sendfromto(): send packet to 195.243.XX.XX[500]
2014-04-23 09:22:04 [DEBUG]: sockmisc.c:524:sendfromto(): 1 times of 676 bytes message will be sent to 195.243.XX.XX[500]
2014-04-23 09:22:04 [DEBUG]: sockmisc.c:528:sendfromto():
12f2e961 943f0451 d4bfae00 36686dc1 01100400 00000000 000002a4 04000038
00000001 00000001 0000002c 01010001 00000024 01010000 80010007 800e0100
80020006 8004000e 80030001 800b0001 800c0708 0a000104 56939011 c3d52772
6e02adab c4c0d526 db830833 d8dce02f 44c3bed9 97c8bb8a 314fb461 7ac98c13
321ee2ff 6494bed1 5f770831 bd307330 4a0b312e aae14037 2e7858c3 15032d22
4ae547c1 cfafbcf3 0a529a4c 010d34d7 91559795 57a1b4f8 e8e8be28 674538d5
ecac7b67 7f9b1adf 54d342c1 c60a17bb d68ed488 58e99359 0a3a22f9 c0407827
146adc07 08df768c ba6edc47 fd2d571a 1456b0b0 296cbe46 857fbf4c 8329884f
32b683a6 899617d2 4c10331c 5ea538bb edf73f4b e3b7007b 1690c7ef 3f4ea8b1
099cc8c0 b5f7c6dd 5b8e4d6a d4b67916 638f2daa fcc93d4f 404fc47d ac0036f0
e58da5fa e4ed00de df3d02fa 20deaa25 bce3d9c2 337c35e2 05000014 fc3831ea
28df553b 1409e4fa 55fdcc28 0800000c 01000000 7a98911d 0d000044 75c0339f
fddf9c29 17ee2f57 53d978fc c4e55e61 0b1028b8 b329fd1b 2409a27d 17d0a259
499cd9c9 9ce6ced9 7e353c05 32014-04-23 09:22:04 [INFO]: ikev1.c:318:ikev1_main(): the packet is retransmitted by 195.243.XX.XX[500].
2014-04-23 09:22:04 [DEBUG]: ikev1.c:2978:isakmp_send(): 676 bytes from 122.152.XX.XX[500] to 195.243.XX.XX[500]
2014-04-23 09:22:04 [DEBUG]: ikev1.c:2978:isakmp_send(): 548 bytes from 122.152.XX.XX[500] to 195.243.XX.XX[500]
2014-04-23 09:22:04 [DEBUG]: sockmisc.c:335:sendfromto(): sockname 122.152.XX.XX[500]
2014-04-23 09:22:04 [DEBUG]: sockmisc.c:337:sendfromto(): send packet from 122.152.XX.XX[500]
2014-04-23 09:22:04 [DEBUG]: sockmisc.c:339:sendfromto(): send packet to 195.243.XX.XX[500]
2014-04-23 09:22:04 [DEBUG]: sockmisc.c:524:sendfromto(): 1 times of 548 bytes message will be sent to 195.243.XX.XX[500]
2014-04-23 09:22:04 [DEBUG]: sockmisc.c:528:sendfromto():
12f2e961 943f0451 d4bfae00 36686dc1 84100400 00000000 00000224 00000208
00010100 12f2e961 943f0451 d4bfae00 36686dc1 01100400 00000000 000002a4
04000038 00000001 00000001 0000002c 01010001 00000024 01010000 80010007
800e0100 80020006 8004000e 80030001 800b0001 800c0708 0a000104 56939011
c3d52772 6e02adab c4c0d526 db830833 d8dce02f 44c3bed9 97c8bb8a 314fb461
7ac98c13 321ee2ff 6494bed1 5f770831 bd307330 4a0b312e aae14037 2e7858c3
15032d22 4ae547c1 cfafbcf3 0a529a4c 010d34d7 91559795 57a1b4f8 e8e8be28
674538d5 ecac7b67 7f9b1adf 54d342c1 c60a17bb d68ed488 58e99359 0a3a22f9
c0407827 146adc07 08df768c ba6edc47 fd2d571a 1456b0b0 296cbe46 857fbf4c
8329884f 32b683a6 899617d2 4c10331c 5ea538bb edf73f4b e3b7007b 1690c7ef
3f4ea8b1 099cc8c0 b5f7c6dd 5b8e4d6a d4b67916 638f2daa fcc93d4f 404fc47d
ac0036f0 e58da5fa e4ed00de df3d02fa 20deaa25 bce3d9c2 337c35e2 05000014
fc3831ea 28df553b 1409e4fa 55fdcc28 0800000c 01000000 7a98911d 0d000044
75c0339f fddf9c29 17ee2f57 52014-04-23 09:22:04 [DEBUG]: ikev1.c:2978:isakmp_send(): 200 bytes from 122.152.XX.XX[500] to 195.243.XX.XX[500]
2014-04-23 09:22:04 [DEBUG]: sockmisc.c:335:sendfromto(): sockname 122.152.XX.XX[500]
2014-04-23 09:22:04 [DEBUG]: sockmisc.c:337:sendfromto(): send packet from 122.152.XX.XX[500]
2014-04-23 09:22:04 [DEBUG]: sockmisc.c:339:sendfromto(): send packet to 195.243.XX.XX[500]
2014-04-23 09:22:04 [DEBUG]: sockmisc.c:524:sendfromto(): 1 times of 200 bytes message will be sent to 195.243.XX.XX[500]
2014-04-23 09:22:04 [DEBUG]: sockmisc.c:528:sendfromto():
12f2e961 943f0451 d4bfae00 36686dc1 84100400 00000000 000000c8 000000ac
00010201 2ab0d308 1a8e3074 18626886 1234948e 17dc58a4 57f2de84 1578afda
102d83be 0d000044 5b623b9b 2c433c3f 179fdd48 904deb9c 6858a3cc 08a3ddfe
246b2fa2 ea51bbfe 48febd37 f445bbc7 194dd9f2 eee1b306 6b1a70b1 c9a4ca81
ab580dbf 8454f5c4 0d000018 4048b7d5 6ebce885 25e7de7f 00d6c2d3 80000000
0d000014 afcad713 68a1f1c9 6b8696fc 77570100 00000014 a9b9b103 4f7e50a2
513b47b1 00bb85a9
2014-04-23 09:22:04 [DEBUG]: ikev1.c:1672:isakmp_ph1resend(): resend phase1 packet 12f2e961943f0451:d4bfae0036686dc1
2014-04-23 09:22:04 [DEBUG]: isakmp.c:944:isakmp_handler(): ===
2014-04-23 09:22:04 [DEBUG]: isakmp.c:945:isakmp_handler(): 236 bytes message received from 195.243.XX.XX[4500]
2014-04-23 09:22:04 [DEBUG]: isakmp.c:948:isakmp_handler():
12f2e961 943f0451 d4bfae00 36686dc1 08100401 00000000 000000ec e4dbb809
54a345f3 b12ae425 003af9b6 50ae163b a725e1ed c21dca9f eddc1773 72d58341
1e4ef0fe b5d1f919 8a865c1a 4d6395c7 75b847b0 c4536db5 a834c6f9 d5caf038
c415d8ec 9fce1745 d5beab5f a9091b95 5b01c874 995bfc1d 9479753b 5798a3bf
d894e440 448fb2b4 e48db1b2 27409d83 9bd70217 f8dbdb19 012e2111 c5b85733
f81ce2b7 fa26dbc9 bb4d03fa 7978aa77 a746dab6 c708ee49 69eed67a 1a310978
97b729a4 f51fd168 15e5c979 53201cd4 1046132a 8b89744f d1655226 932ea3a6
46bac677 74b0a410 9ca00acd
2014-04-23 09:22:04 [DEBUG]: oakley.c:3109:oakley_do_decrypt(): begin decryption.
2014-04-23 09:22:04 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-04-23 09:22:04 [DEBUG]: oakley.c:3123:oakley_do_decrypt(): IV was saved for next processing:
2014-04-23 09:22:04 [DEBUG]: oakley.c:3125:oakley_do_decrypt():
932ea3a6 46bac677 74b0a410 9ca00acd
2014-04-23 09:22:04 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-04-23 09:22:04 [DEBUG]: oakley.c:3148:oakley_do_decrypt(): with key:
2014-04-23 09:22:04 [DEBUG]: oakley.c:3149:oakley_do_decrypt():
d7337258 41d74255 31c70f8c 9ae72620 b9ee228c b7980138 e1b75316 2c09557b
2014-04-23 09:22:04 [DEBUG]: oakley.c:3154:oakley_do_decrypt(): decrypted payload by IV:
2014-04-23 09:22:04 [DEBUG]: oakley.c:3155:oakley_do_decrypt():
50ef6279 69418f9d fbb71d85 6004e297
2014-04-23 09:22:04 [DEBUG]: oakley.c:3157:oakley_do_decrypt(): decrypted payload, but not trimed.
2014-04-23 09:22:04 [DEBUG]: oakley.c:3159:oakley_do_decrypt():
14000044 cd36c3ec 34b15f85 41e51527 2e79d792 baea14a1 9fd5a7aa a8ec81c1
ed0b9b67 730dd327 50ac4057 2361ab39 a679e498 85bc9e60 e3cbed02 3c5c1001
a6f01bba 14000044 72858507 8dab0396 3378e3c3 7cb86661 8d9beb5e cd2d8a5f
edaaed6e 39b7437f 489d3204 a0ef6c83 15149c0a c0875931 0b3b0006 24660f70
ac15ded2 c273efb0 00000044 c3859723 b92ca3e9 9a609c0f fd774c2a 19db5b46
0ff102aa 8d16932c ee5dfcd4 7a86612f 64ed729a 6aedc20c c992aa63 edeb78f0
191bf313 99ba6b14 fd569527 00000000
2014-04-23 09:22:04 [DEBUG]: oakley.c:3168:oakley_do_decrypt(): padding len=0
2014-04-23 09:22:04 [DEBUG]: oakley.c:3199:oakley_do_decrypt(): decrypted.
2014-04-23 09:22:04 [DEBUG]: oakley.c:3200:oakley_do_decrypt():
12f2e961 943f0451 d4bfae00 36686dc1 08100401 00000000 000000ec 14000044
cd36c3ec 34b15f85 41e51527 2e79d792 baea14a1 9fd5a7aa a8ec81c1 ed0b9b67
730dd327 50ac4057 2361ab39 a679e498 85bc9e60 e3cbed02 3c5c1001 a6f01bba
14000044 72858507 8dab0396 3378e3c3 7cb86661 8d9beb5e cd2d8a5f edaaed6e
39b7437f 489d3204 a0ef6c83 15149c0a c0875931 0b3b0006 24660f70 ac15ded2
c273efb0 00000044 c3859723 b92ca3e9 9a609c0f fd774c2a 19db5b46 0ff102aa
8d16932c ee5dfcd4 7a86612f 64ed729a 6aedc20c c992aa63 edeb78f0 191bf313
99ba6b14 fd569527 00000000
2014-04-23 09:22:04 [DEBUG]: ikev1.c:2831:isakmp_parsewoh(): begin.
2014-04-23 09:22:04 [DEBUG]: ikev1.c:2858:isakmp_parsewoh(): seen nptype=8(hash)
2014-04-23 09:22:04 [DEBUG]: ikev1.c:2858:isakmp_parsewoh(): seen nptype=20(nat-d)
2014-04-23 09:22:04 [DEBUG]: ikev1.c:2858:isakmp_parsewoh(): seen nptype=20(nat-d)
2014-04-23 09:22:04 [DEBUG]: ikev1.c:2897:isakmp_parsewoh(): succeed.
2014-04-23 09:22:04 [INFO]: ikev1_natt.c:136:ikev1_natt_hash_addr(): Hashing 122.152.XX.XX[4500] with algo #6
2014-04-23 09:22:04 [DEBUG]: algorithm.c:386:alg_oakley_hashdef(): hash(sha512)
2014-04-23 09:22:04 [INFO]: isakmp_agg.c:1493:agg_r2recv(): NAT-D payload #0 verified
2014-04-23 09:22:04 [INFO]: ikev1_natt.c:136:ikev1_natt_hash_addr(): Hashing 195.243.XX.XX[4500] with algo #6
2014-04-23 09:22:04 [DEBUG]: algorithm.c:386:alg_oakley_hashdef(): hash(sha512)
2014-04-23 09:22:04 [INFO]: isakmp_agg.c:1493:agg_r2recv(): NAT-D payload #1 doesn't match
2014-04-23 09:22:04 [INFO]: isakmp_agg.c:1516:agg_r2recv(): NAT detected: PEER
2014-04-23 09:22:04 [DEBUG]: oakley.c:1323:oakley_validate_auth(): HASH received:
2014-04-23 09:22:04 [DEBUG]: oakley.c:1324:oakley_validate_auth():
cd36c3ec 34b15f85 41e51527 2e79d792 baea14a1 9fd5a7aa a8ec81c1 ed0b9b67
730dd327 50ac4057 2361ab39 a679e498 85bc9e60 e3cbed02 3c5c1001 a6f01bba
2014-04-23 09:22:04 [DEBUG]: oakley.c:801:oakley_ph1hash_common(): HASH with:
2014-04-23 09:22:04 [DEBUG]: oakley.c:802:oakley_ph1hash_common():
7273d78a efa09af6 a945fe1a 1b38a728 f2f7af2b 991697fc 68754405 d5461382
87282931 2c813c92 87894734 c0db0b03 907cf85c 8a39e128 45c7d89e 2c2fa9d7
19a27248 4c9d6fb3 f0a58fc6 d7179729 0c20a685 cc870a13 1f14734e 58a7c512
6af79365 e02d43b1 b6302371 4a4c312a bc5e0df3 f4f247ac 3883ed09 ee1be047
a7f55741 bdb7818b c32e8113 a9432a8c 6ae25ca0 21390e6c e9c1728c 7f33102f
c8865034 48752c8e 290c51db 75724b72 61743046 20bf7370 4970e1df 5a8507ed
0a6a4154 0ccfda99 8660b6ed 610ba01a c1e232c1 00ce0c6a b4744f6a 4ae7b048
650f52a0 a2ec5441 6cef8788 4416ac8b 3bc806cd 4cae5d20 7c6fb1a0 05e7905c
56939011 c3d52772 6e02adab c4c0d526 db830833 d8dce02f 44c3bed9 97c8bb8a
314fb461 7ac98c13 321ee2ff 6494bed1 5f770831 bd307330 4a0b312e aae14037
2e7858c3 15032d22 4ae547c1 cfafbcf3 0a529a4c 010d34d7 91559795 57a1b4f8
e8e8be28 674538d5 ecac7b67 7f9b1adf 54d342c1 c60a17bb d68ed488 58e99359
0a3a22f9 c0407827 146adc07 08df768c ba6edc47 fd2d571a 1456b0b0 296cbe46
857fbf4c 8329884f 32014-04-23 09:22:04 [DEBUG]: algorithm.c:469:alg_oakley_hmacdef(): hmac(hmac_sha2_512)
2014-04-23 09:22:04 [DEBUG]: oakley.c:811:oakley_ph1hash_common(): HASH (resp) computed:
2014-04-23 09:22:04 [DEBUG]: oakley.c:813:oakley_ph1hash_common():
cd36c3ec 34b15f85 41e51527 2e79d792 baea14a1 9fd5a7aa a8ec81c1 ed0b9b67
730dd327 50ac4057 2361ab39 a679e498 85bc9e60 e3cbed02 3c5c1001 a6f01bba
2014-04-23 09:22:04 [DEBUG]: oakley.c:1355:oakley_validate_auth(): HASH for PSK validated.
2014-04-23 09:22:04 [DEBUG]: isakmp_agg.c:1542:agg_r2recv(): PH1 state changed: 3 to 5 [PHASE1ST_MSG2RECEIVED] @agg_r2recv
2014-04-23 09:22:04 [DEBUG]: ikev1.c:1023:ph1_main(): ===> PHASE-1 SEND PACKET <===
2014-04-23 09:22:04 [DEBUG]: isakmp_agg.c:1614:agg_r2send(): PH1 state changed: 5 to 12 [PHASE1ST_ESTABLISHED] @agg_r2send
2014-04-23 09:22:04 [PROTO_NOTIFY]: ikev1.c:2446:log_ph1established(): ====> PHASE-1 NEGOTIATION SUCCEEDED AS RESPONDER, AGGRESSIVE MODE <====
====> Established SA: 122.152.XX.XX[4500]-195.243.XX.XX[4500] cookie:12f2e961943f0451:d4bfae0036686dc1 lifetime 1800 Sec <====
2014-04-23 09:22:04 [DEBUG]: ikev1.c:921:ph1_established(): ===
Apr 23 09:22:06 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:22:06 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:22:06 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:22:06 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:22:06 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:22:06 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:22:06 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:22:06 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:22:06 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:22:06 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:22:10 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:22:10 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:22:10 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:22:10 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:22:10 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:22:10 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:22:10 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:22:10 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:22:10 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:22:10 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:22:16 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:22:16 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:22:16 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:22:16 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:22:16 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:22:16 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:22:16 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:22:16 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:22:16 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:22:16 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:22:20 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:22:20 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:22:20 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:22:20 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:22:20 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
2014-04-23 09:22:20 [DEBUG]: ikev1_natt.c:348:natt_keepalive_send(): KA: 122.152.XX.XX[4500]->195.243.XX.XX[4500]
2014-04-23 09:22:20 [DEBUG]: sockmisc.c:335:sendfromto(): sockname 122.152.XX.XX[4500]
2014-04-23 09:22:20 [DEBUG]: sockmisc.c:337:sendfromto(): send packet from 122.152.XX.XX[4500]
2014-04-23 09:22:20 [DEBUG]: sockmisc.c:339:sendfromto(): send packet to 195.243.XX.XX[4500]
2014-04-23 09:22:20 [DEBUG]: sockmisc.c:524:sendfromto(): 1 times of 1 bytes message will be sent to 195.243.XX.XX[4500]
2014-04-23 09:22:20 [DEBUG]: sockmisc.c:528:sendfromto():
ff
Apr 23 09:22:20 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:22:20 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:22:20 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:22:20 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:22:20 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:22:24 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:22:24 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:22:24 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:22:24 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:22:24 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:22:24 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:22:24 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:22:24 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:22:24 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:22:24 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:22:28 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:22:28 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:22:28 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:22:28 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:22:28 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:22:28 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:22:28 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:22:28 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:22:28 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:22:28 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:22:35 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:22:35 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:22:35 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:22:35 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:22:35 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:22:35 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:22:35 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:22:35 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:22:35 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:22:35 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:22:38 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:22:38 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:22:38 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:22:38 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BPN-OSPF-Router(Gateway-BPN-OSPF-Router)_out
2014-04-23 09:22:38 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BPN-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:22:38 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:22:38 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:22:38 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:22:38 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-JHB-OSPF-Router(Gateway-JHB-OSPF-Router)_out
2014-04-23 09:22:38 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-JHB-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:22:38 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:22:38 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:22:38 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:22:38 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-LIN-Test-Router(Gateway-LIN-Test-Router)_out
2014-04-23 09:22:38 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-LIN-Test-Router passive mode specified for IKEv1, dropping acquire request
2014-04-23 09:22:39 [DEBUG]: isakmp.c:944:isakmp_handler(): ===
2014-04-23 09:22:39 [DEBUG]: isakmp.c:945:isakmp_handler(): 140 bytes message received from 195.243.XX.XX[4500]
2014-04-23 09:22:39 [DEBUG]: isakmp.c:948:isakmp_handler():
12f2e961 943f0451 d4bfae00 36686dc1 08100501 5e629d7c 0000008c 0adf805b
ebc9ac9b dc52e49f a468e974 eb83e889 9bf0d06c 78069290 bb5c3a8d ea73c3f5
0eecacae 0c8979ce 29ef7e0a b7be6a8a b8107dcf ed3a3453 ada584cb 7fe4f203
492cd6f2 59ea09fd e63db4b6 6ce187d1 e0d4591e d7f2c17d 6c27f82f 61e8221f
2741dbe6 be29f24e 485cf731
2014-04-23 09:22:39 [DEBUG]: isakmp_inf.c:147:isakmp_info_recv(): receive Information.
2014-04-23 09:22:39 [DEBUG]: oakley.c:3028:oakley_newiv2(): compute IV for phase2
2014-04-23 09:22:39 [DEBUG]: oakley.c:3029:oakley_newiv2(): phase1 last IV:
2014-04-23 09:22:39 [DEBUG]: oakley.c:3030:oakley_newiv2():
932ea3a6 46bac677 74b0a410 9ca00acd 5e629d7c
2014-04-23 09:22:39 [DEBUG]: algorithm.c:386:alg_oakley_hashdef(): hash(sha512)
2014-04-23 09:22:39 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-04-23 09:22:39 [DEBUG]: oakley.c:3063:oakley_newiv2(): phase2 IV computed:
2014-04-23 09:22:39 [DEBUG]: oakley.c:3064:oakley_newiv2():
988f1d5c 66fa67ac 1b3acfb7 64322e39
2014-04-23 09:22:39 [DEBUG]: oakley.c:3109:oakley_do_decrypt(): begin decryption.
2014-04-23 09:22:39 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-04-23 09:22:39 [DEBUG]: oakley.c:3123:oakley_do_decrypt(): IV was saved for next processing:
2014-04-23 09:22:39 [DEBUG]: oakley.c:3125:oakley_do_decrypt():
61e8221f 2741dbe6 be29f24e 485cf731
2014-04-23 09:22:39 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-04-23 09:22:39 [DEBUG]: oakley.c:3148:oakley_do_decrypt(): with key:
2014-04-23 09:22:39 [DEBUG]: oakley.c:3149:oakley_do_decrypt():
d7337258 41d74255 31c70f8c 9ae72620 b9ee228c b7980138 e1b75316 2c09557b
2014-04-23 09:22:39 [DEBUG]: oakley.c:3154:oakley_do_decrypt(): decrypted payload by IV:
2014-04-23 09:22:39 [DEBUG]: oakley.c:3155:oakley_do_decrypt():
988f1d5c 66fa67ac 1b3acfb7 64322e39
2014-04-23 09:22:39 [DEBUG]: oakley.c:3157:oakley_do_decrypt(): decrypted payload, but not trimed.
2014-04-23 09:22:39 [DEBUG]: oakley.c:3159:oakley_do_decrypt():
0b000044 cb13c1e2 a2e93462 6d17ef17 f82f6bf7 d55200cc 685d79bb d571495e
c589d673 5fafda7e e8dbc9d4 cce007fd 808ddea5 273ed15e c62f9425 be2643b8
b88cf965 00000020 00000001 01108d28 12f2e961 943f0451 d4bfae00 36686dc1
2dc4edaa 00000000 00000000 00000000
2014-04-23 09:22:39 [DEBUG]: oakley.c:3168:oakley_do_decrypt(): padding len=0
2014-04-23 09:22:39 [DEBUG]: oakley.c:3199:oakley_do_decrypt(): decrypted.
2014-04-23 09:22:39 [DEBUG]: oakley.c:3200:oakley_do_decrypt():
12f2e961 943f0451 d4bfae00 36686dc1 08100501 5e629d7c 0000008c 0b000044
cb13c1e2 a2e93462 6d17ef17 f82f6bf7 d55200cc 685d79bb d571495e c589d673
5fafda7e e8dbc9d4 cce007fd 808ddea5 273ed15e c62f9425 be2643b8 b88cf965
00000020 00000001 01108d28 12f2e961 943f0451 d4bfae00 36686dc1 2dc4edaa
00000000 00000000 00000000
2014-04-23 09:22:39 [DEBUG]: oakley.c:3088:oakley_delivm(): IV freed
2014-04-23 09:22:39 [DEBUG]: oakley.c:682:oakley_compute_hash1(): HASH with:
2014-04-23 09:22:39 [DEBUG]: oakley.c:683:oakley_compute_hash1():
5e629d7c 00000020 00000001 01108d28 12f2e961 943f0451 d4bfae00 36686dc1
2dc4edaa
2014-04-23 09:22:39 [DEBUG]: algorithm.c:469:alg_oakley_hmacdef(): hmac(hmac_sha2_512)
2014-04-23 09:22:39 [DEBUG]: oakley.c:692:oakley_compute_hash1(): HASH computed:
2014-04-23 09:22:39 [DEBUG]: oakley.c:693:oakley_compute_hash1():
cb13c1e2 a2e93462 6d17ef17 f82f6bf7 d55200cc 685d79bb d571495e c589d673
5fafda7e e8dbc9d4 cce007fd 808ddea5 273ed15e c62f9425 be2643b8 b88cf965
2014-04-23 09:22:39 [DEBUG]: isakmp_inf.c:262:isakmp_info_recv(): hash validated.
2014-04-23 09:22:39 [DEBUG]: ikev1.c:2831:isakmp_parsewoh(): begin.
2014-04-23 09:22:39 [DEBUG]: ikev1.c:2858:isakmp_parsewoh(): seen nptype=8(hash)
2014-04-23 09:22:39 [DEBUG]: ikev1.c:2858:isakmp_parsewoh(): seen nptype=11(notify)
2014-04-23 09:22:39 [DEBUG]: ikev1.c:2897:isakmp_parsewoh(): succeed.
2014-04-23 09:22:39 [DEBUG]: isakmp_inf.c:1540:isakmp_info_recv_r_u(): DPD R-U-There received
2014-04-23 09:22:39 [DEBUG]: oakley.c:3028:oakley_newiv2(): compute IV for phase2
2014-04-23 09:22:39 [DEBUG]: oakley.c:3029:oakley_newiv2(): phase1 last IV:
2014-04-23 09:22:39 [DEBUG]: oakley.c:3030:oakley_newiv2():
932ea3a6 46bac677 74b0a410 9ca00acd 7e2c384e
2014-04-23 09:22:39 [DEBUG]: algorithm.c:386:alg_oakley_hashdef(): hash(sha512)
2014-04-23 09:22:39 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-04-23 09:22:39 [DEBUG]: oakley.c:3063:oakley_newiv2(): phase2 IV computed:
2014-04-23 09:22:39 [DEBUG]: oakley.c:3064:oakley_newiv2():
fd2056f1 08c1f970 4fadd442 fbd2b948
2014-04-23 09:22:39 [DEBUG]: oakley.c:682:oakley_compute_hash1(): HASH with:
2014-04-23 09:22:39 [DEBUG]: oakley.c:683:oakley_compute_hash1():
7e2c384e 00000020 00000001 01108d29 12f2e961 943f0451 d4bfae00 36686dc1
2dc4edaa
2014-04-23 09:22:39 [DEBUG]: algorithm.c:469:alg_oakley_hmacdef(): hmac(hmac_sha2_512)
2014-04-23 09:22:39 [DEBUG]: oakley.c:692:oakley_compute_hash1(): HASH computed:
2014-04-23 09:22:39 [DEBUG]: oakley.c:693:oakley_compute_hash1():
fae65715 660f096d ce69ec97 fea02f69 8bf245d1 9a53f584 15e82061 16dc6f0a
a24fc45d 5239aa11 673d9e69 5e2fc9e3 9b44d3b1 ca2acfd1 d03af7fe 279e79ef
2014-04-23 09:22:39 [DEBUG]: oakley.c:3234:oakley_do_encrypt(): begin encryption.
2014-04-23 09:22:39 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-04-23 09:22:39 [DEBUG]: oakley.c:3250:oakley_do_encrypt(): pad length = 12
2014-04-23 09:22:39 [DEBUG]: oakley.c:3280:oakley_do_encrypt():
0b000044 fae65715 660f096d ce69ec97 fea02f69 8bf245d1 9a53f584 15e82061
16dc6f0a a24fc45d 5239aa11 673d9e69 5e2fc9e3 9b44d3b1 ca2acfd1 d03af7fe
279e79ef 00000020 00000001 01108d29 12f2e961 943f0451 d4bfae00 36686dc1
2dc4edaa 4dd98aac 1e91986a c2db620c
2014-04-23 09:22:39 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-04-23 09:22:39 [DEBUG]: oakley.c:3290:oakley_do_encrypt(): with key:
2014-04-23 09:22:39 [DEBUG]: oakley.c:3291:oakley_do_encrypt():
d7337258 41d74255 31c70f8c 9ae72620 b9ee228c b7980138 e1b75316 2c09557b
2014-04-23 09:22:39 [DEBUG]: oakley.c:3296:oakley_do_encrypt(): encrypted payload by IV:
2014-04-23 09:22:39 [DEBUG]: oakley.c:3297:oakley_do_encrypt():
fd2056f1 08c1f970 4fadd442 fbd2b948
2014-04-23 09:22:39 [DEBUG]: oakley.c:3303:oakley_do_encrypt(): save IV for next:
2014-04-23 09:22:39 [DEBUG]: oakley.c:3304:oakley_do_encrypt():
78a153a3 9e30e989 5bfdd060 6c992d74
2014-04-23 09:22:39 [DEBUG]: oakley.c:3320:oakley_do_encrypt(): encrypted.
2014-04-23 09:22:39 [DEBUG]: ikev1.c:2953:isakmp_send(): Adding NON-ESP marker
2014-04-23 09:22:39 [DEBUG]: ikev1.c:2978:isakmp_send(): 144 bytes from 122.152.XX.XX[4500] to 195.243.XX.XX[4500]
2014-04-23 09:22:39 [DEBUG]: sockmisc.c:335:sendfromto(): sockname 122.152.XX.XX[4500]
2014-04-23 09:22:39 [DEBUG]: sockmisc.c:337:sendfromto(): send packet from 122.152.XX.XX[4500]
2014-04-23 09:22:39 [DEBUG]: sockmisc.c:339:sendfromto(): send packet to 195.243.XX.XX[4500]
2014-04-23 09:22:39 [DEBUG]: sockmisc.c:524:sendfromto(): 1 times of 144 bytes message will be sent to 195.243.XX.XX[4500]
2014-04-23 09:22:39 [DEBUG]: sockmisc.c:528:sendfromto():
00000000 12f2e961 943f0451 d4bfae00 36686dc1 08100501 7e2c384e 0000008c
155e3936 3811b27e 09fe878d bde40f74 95acc6b5 ab19921a f02536d5 0eac9836
3a79c57d 54550695 7b950f40 b1bee109 6c16352f e410d9d6 68282cac ff94f8f3
28aced65 d21701f5 4a5de24f a194a208 1f603261 9e998250 f0745426 361ed488
78a153a3 9e30e989 5bfdd060 6c992d74
2014-04-23 09:22:39 [DEBUG]: isakmp_inf.c:805:isakmp_info_send_common(): sendto Information notify.
2014-04-23 09:22:39 [DEBUG]: oakley.c:3088:oakley_delivm(): IV freed
2014-04-23 09:22:39 [DEBUG]: isakmp_inf.c:1569:isakmp_info_recv_r_u(): received a valid R-U-THERE, ACK sent
2014-04-23 09:22:39 [PROTO_NOTIFY]: isakmp_inf.c:1159:isakmp_info_recv_n(): notification message 36136:R-U-THERE, doi=1 proto_id=1 spi=12f2e961943f0451 d4bfae0036686dc1 (size=16).
Apr 23 09:22:39 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:22:39 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:22:39 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
Apr 23 09:22:39 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
2014-04-23 09:22:39 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:22:39 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:22:39 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:22:39 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:22:39 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:22:39 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
2014-04-23 09:22:40 [DEBUG]: ikev1_natt.c:348:natt_keepalive_send(): KA: 122.152.XX.XX[4500]->195.243.XX.XX[4500]
2014-04-23 09:22:40 [DEBUG]: sockmisc.c:335:sendfromto(): sockname 122.152.XX.XX[4500]
2014-04-23 09:22:40 [DEBUG]: sockmisc.c:337:sendfromto(): send packet from 122.152.XX.XX[4500]
2014-04-23 09:22:40 [DEBUG]: sockmisc.c:339:sendfromto(): send packet to 195.243.XX.XX[4500]
2014-04-23 09:22:40 [DEBUG]: sockmisc.c:524:sendfromto(): 1 times of 1 bytes message will be sent to 195.243.XX.XX[4500]
2014-04-23 09:22:40 [DEBUG]: sockmisc.c:528:sendfromto():
ff
Apr 23 09:22:46 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:22:46 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:22:46 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:22:46 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:22:46 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:22:46 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:22:46 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:22:46 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:22:46 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:22:46 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:22:53 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:22:53 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:22:53 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:22:53 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:22:53 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:22:53 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:22:53 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:22:53 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:22:53 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:22:53 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:22:57 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:22:57 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:22:57 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:22:57 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:22:57 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:22:57 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:22:57 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:22:57 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:22:57 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:22:57 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
2014-04-23 09:23:00 [DEBUG]: ikev1_natt.c:348:natt_keepalive_send(): KA: 122.152.XX.XX[4500]->195.243.XX.XX[4500]
2014-04-23 09:23:00 [DEBUG]: sockmisc.c:335:sendfromto(): sockname 122.152.XX.XX[4500]
2014-04-23 09:23:00 [DEBUG]: sockmisc.c:337:sendfromto(): send packet from 122.152.XX.XX[4500]
2014-04-23 09:23:00 [DEBUG]: sockmisc.c:339:sendfromto(): send packet to 195.243.XX.XX[4500]
2014-04-23 09:23:00 [DEBUG]: sockmisc.c:524:sendfromto(): 1 times of 1 bytes message will be sent to 195.243.XX.XX[4500]
2014-04-23 09:23:00 [DEBUG]: sockmisc.c:528:sendfromto():
ff
Apr 23 09:23:04 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:23:04 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:23:04 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:23:04 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:23:04 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:23:04 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:23:04 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:23:04 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:23:04 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:23:04 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:23:10 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:23:10 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:23:10 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:23:10 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:23:10 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:23:10 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:23:10 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:23:10 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:23:10 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:23:10 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:23:15 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:23:15 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:23:15 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:23:15 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:23:15 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:23:15 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:23:15 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:23:15 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:23:15 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:23:15 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:23:20 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:23:20 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:23:20 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:23:20 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:23:20 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
2014-04-23 09:23:20 [DEBUG]: ikev1_natt.c:348:natt_keepalive_send(): KA: 122.152.XX.XX[4500]->195.243.XX.XX[4500]
2014-04-23 09:23:20 [DEBUG]: sockmisc.c:335:sendfromto(): sockname 122.152.XX.XX[4500]
2014-04-23 09:23:20 [DEBUG]: sockmisc.c:337:sendfromto(): send packet from 122.152.XX.XX[4500]
2014-04-23 09:23:20 [DEBUG]: sockmisc.c:339:sendfromto(): send packet to 195.243.XX.XX[4500]
2014-04-23 09:23:20 [DEBUG]: sockmisc.c:524:sendfromto(): 1 times of 1 bytes message will be sent to 195.243.XX.XX[4500]
2014-04-23 09:23:20 [DEBUG]: sockmisc.c:528:sendfromto():
ff
Apr 23 09:23:20 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:23:20 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:23:20 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:23:20 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:23:20 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:23:25 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:23:25 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:23:25 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:23:25 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:23:25 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:23:25 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:23:25 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:23:25 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:23:25 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:23:25 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:23:29 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:23:29 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:23:29 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:23:29 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:23:29 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:23:29 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:23:29 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:23:29 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:23:29 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:23:29 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:23:33 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:23:33 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:23:33 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:23:33 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:23:33 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:23:33 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:23:33 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:23:33 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:23:33 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:23:33 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:23:39 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:23:39 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:23:39 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:23:39 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:23:39 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:23:39 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:23:39 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:23:39 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:23:39 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:23:39 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
2014-04-23 09:23:40 [DEBUG]: ikev1_natt.c:348:natt_keepalive_send(): KA: 122.152.XX.XX[4500]->195.243.XX.XX[4500]
2014-04-23 09:23:40 [DEBUG]: sockmisc.c:335:sendfromto(): sockname 122.152.XX.XX[4500]
2014-04-23 09:23:40 [DEBUG]: sockmisc.c:337:sendfromto(): send packet from 122.152.XX.XX[4500]
2014-04-23 09:23:40 [DEBUG]: sockmisc.c:339:sendfromto(): send packet to 195.243.XX.XX[4500]
2014-04-23 09:23:40 [DEBUG]: sockmisc.c:524:sendfromto(): 1 times of 1 bytes message will be sent to 195.243.XX.XX[4500]
2014-04-23 09:23:40 [DEBUG]: sockmisc.c:528:sendfromto():
ff
Apr 23 09:23:46 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:23:46 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:23:46 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:23:46 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:23:46 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:23:46 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:23:46 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:23:46 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:23:46 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:23:46 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:23:53 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:23:53 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:23:53 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:23:53 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:23:53 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:23:53 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:23:53 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:23:53 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:23:53 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:23:53 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:23:57 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:23:57 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:23:57 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:23:57 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:23:57 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:23:57 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:23:57 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:23:57 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:23:57 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:23:57 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
2014-04-23 09:24:00 [DEBUG]: ikev1_natt.c:348:natt_keepalive_send(): KA: 122.152.XX.XX[4500]->195.243.XX.XX[4500]
2014-04-23 09:24:00 [DEBUG]: sockmisc.c:335:sendfromto(): sockname 122.152.XX.XX[4500]
2014-04-23 09:24:00 [DEBUG]: sockmisc.c:337:sendfromto(): send packet from 122.152.XX.XX[4500]
2014-04-23 09:24:00 [DEBUG]: sockmisc.c:339:sendfromto(): send packet to 195.243.XX.XX[4500]
2014-04-23 09:24:00 [DEBUG]: sockmisc.c:524:sendfromto(): 1 times of 1 bytes message will be sent to 195.243.XX.XX[4500]
2014-04-23 09:24:00 [DEBUG]: sockmisc.c:528:sendfromto():
ff
Apr 23 09:24:01 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:24:01 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:24:01 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:24:01 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:24:01 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:24:01 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:24:01 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:24:01 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:24:01 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:24:01 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:24:05 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:24:05 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:24:05 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:24:05 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:24:05 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:24:05 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:24:05 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:24:05 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:24:05 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:24:05 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:24:09 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:24:09 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:24:09 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:24:09 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:24:09 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:24:09 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:24:09 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:24:09 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:24:09 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:24:09 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:24:13 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:24:13 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:24:13 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:24:13 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:24:13 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:24:13 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:24:13 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:24:13 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:24:13 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:24:13 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:24:20 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:24:20 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:24:20 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:24:20 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:24:20 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
2014-04-23 09:24:20 [DEBUG]: ikev1_natt.c:348:natt_keepalive_send(): KA: 122.152.XX.XX[4500]->195.243.XX.XX[4500]
2014-04-23 09:24:20 [DEBUG]: sockmisc.c:335:sendfromto(): sockname 122.152.XX.XX[4500]
2014-04-23 09:24:20 [DEBUG]: sockmisc.c:337:sendfromto(): send packet from 122.152.XX.XX[4500]
2014-04-23 09:24:20 [DEBUG]: sockmisc.c:339:sendfromto(): send packet to 195.243.XX.XX[4500]
2014-04-23 09:24:20 [DEBUG]: sockmisc.c:524:sendfromto(): 1 times of 1 bytes message will be sent to 195.243.XX.XX[4500]
2014-04-23 09:24:20 [DEBUG]: sockmisc.c:528:sendfromto():
ff
Apr 23 09:24:20 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:24:20 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:24:20 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:24:20 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:24:20 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:24:23 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:24:23 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:24:23 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:24:23 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:24:23 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:24:23 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:24:23 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:24:23 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:24:23 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:24:23 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:24:27 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:24:27 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:24:27 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:24:27 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:24:27 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:24:27 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:24:27 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:24:27 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:24:27 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:24:27 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:24:31 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:24:31 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:24:31 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:24:31 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:24:31 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:24:31 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:24:31 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:24:31 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:24:31 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:24:31 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:24:35 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:24:35 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:24:35 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:24:35 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:24:35 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:24:35 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:24:35 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:24:35 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:24:35 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:24:35 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:24:39 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:24:39 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:24:39 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:24:39 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:24:39 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:24:39 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:24:39 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:24:39 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:24:39 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:24:39 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
2014-04-23 09:24:40 [DEBUG]: ikev1_natt.c:348:natt_keepalive_send(): KA: 122.152.XX.XX[4500]->195.243.XX.XX[4500]
2014-04-23 09:24:40 [DEBUG]: sockmisc.c:335:sendfromto(): sockname 122.152.XX.XX[4500]
2014-04-23 09:24:40 [DEBUG]: sockmisc.c:337:sendfromto(): send packet from 122.152.XX.XX[4500]
2014-04-23 09:24:40 [DEBUG]: sockmisc.c:339:sendfromto(): send packet to 195.243.XX.XX[4500]
2014-04-23 09:24:40 [DEBUG]: sockmisc.c:524:sendfromto(): 1 times of 1 bytes message will be sent to 195.243.XX.XX[4500]
2014-04-23 09:24:40 [DEBUG]: sockmisc.c:528:sendfromto():
ff
Apr 23 09:24:43 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:24:43 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:24:43 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:24:43 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:24:43 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:24:43 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:24:43 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:24:43 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:24:43 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:24:43 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:24:49 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:24:49 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:24:49 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:24:49 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:24:49 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:24:49 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:24:49 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:24:49 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:24:49 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:24:49 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:24:53 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:24:53 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:24:53 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:24:53 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:24:53 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:24:53 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:24:53 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:24:53 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:24:53 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:24:53 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:24:57 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:24:57 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:24:57 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:24:57 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:24:57 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:24:57 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:24:57 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:24:57 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:24:57 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:24:57 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
2014-04-23 09:25:00 [DEBUG]: ikev1_natt.c:348:natt_keepalive_send(): KA: 122.152.XX.XX[4500]->195.243.XX.XX[4500]
2014-04-23 09:25:00 [DEBUG]: sockmisc.c:335:sendfromto(): sockname 122.152.XX.XX[4500]
2014-04-23 09:25:00 [DEBUG]: sockmisc.c:337:sendfromto(): send packet from 122.152.XX.XX[4500]
2014-04-23 09:25:00 [DEBUG]: sockmisc.c:339:sendfromto(): send packet to 195.243.XX.XX[4500]
2014-04-23 09:25:00 [DEBUG]: sockmisc.c:524:sendfromto(): 1 times of 1 bytes message will be sent to 195.243.XX.XX[4500]
2014-04-23 09:25:00 [DEBUG]: sockmisc.c:528:sendfromto():
ff
Apr 23 09:25:01 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:25:01 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:25:01 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:25:01 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:25:01 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:25:01 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:25:01 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:25:01 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:25:01 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:25:01 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:25:08 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:25:08 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:25:08 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:25:08 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:25:08 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:25:08 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:25:08 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:25:08 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:25:08 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:25:08 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:25:12 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:25:12 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:25:12 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:25:12 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:25:12 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:25:12 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:25:12 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:25:12 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:25:12 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:25:12 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:25:16 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:25:16 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:25:16 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:25:16 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:25:16 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:25:16 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:25:16 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:25:16 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:25:16 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:25:16 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:25:20 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:25:20 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:25:20 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:25:20 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:25:20 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
2014-04-23 09:25:20 [DEBUG]: ikev1_natt.c:348:natt_keepalive_send(): KA: 122.152.XX.XX[4500]->195.243.XX.XX[4500]
2014-04-23 09:25:20 [DEBUG]: sockmisc.c:335:sendfromto(): sockname 122.152.XX.XX[4500]
2014-04-23 09:25:20 [DEBUG]: sockmisc.c:337:sendfromto(): send packet from 122.152.XX.XX[4500]
2014-04-23 09:25:20 [DEBUG]: sockmisc.c:339:sendfromto(): send packet to 195.243.XX.XX[4500]
2014-04-23 09:25:20 [DEBUG]: sockmisc.c:524:sendfromto(): 1 times of 1 bytes message will be sent to 195.243.XX.XX[4500]
2014-04-23 09:25:20 [DEBUG]: sockmisc.c:528:sendfromto():
ff
Apr 23 09:25:20 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:25:20 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:25:20 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:25:20 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:25:20 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:25:24 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:25:24 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:25:24 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:25:24 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:25:24 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:25:24 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:25:24 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:25:24 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:25:24 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:25:24 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:25:29 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:25:29 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:25:29 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:25:29 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:25:29 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:25:29 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:25:29 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:25:29 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:25:29 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:25:29 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:25:33 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:25:33 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:25:33 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:25:33 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:25:33 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:25:33 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:25:33 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:25:33 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:25:33 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:25:33 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:25:37 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:25:37 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:25:37 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:25:37 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:25:37 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:25:37 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:25:37 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:25:37 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:25:37 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:25:37 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
2014-04-23 09:25:40 [DEBUG]: ikev1_natt.c:348:natt_keepalive_send(): KA: 122.152.XX.XX[4500]->195.243.XX.XX[4500]
2014-04-23 09:25:40 [DEBUG]: sockmisc.c:335:sendfromto(): sockname 122.152.XX.XX[4500]
2014-04-23 09:25:40 [DEBUG]: sockmisc.c:337:sendfromto(): send packet from 122.152.XX.XX[4500]
2014-04-23 09:25:40 [DEBUG]: sockmisc.c:339:sendfromto(): send packet to 195.243.XX.XX[4500]
2014-04-23 09:25:40 [DEBUG]: sockmisc.c:524:sendfromto(): 1 times of 1 bytes message will be sent to 195.243.XX.XX[4500]
2014-04-23 09:25:40 [DEBUG]: sockmisc.c:528:sendfromto():
ff
Apr 23 09:25:41 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:25:41 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:25:41 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:25:41 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:25:41 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:25:41 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:25:41 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:25:41 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:25:41 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:25:41 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:25:46 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:25:46 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:25:46 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:25:46 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:25:46 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:25:46 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:25:46 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:25:46 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:25:46 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:25:46 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:25:50 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:25:50 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:25:50 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:25:50 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:25:50 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:25:50 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:25:50 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:25:50 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:25:50 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:25:50 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:25:56 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:25:56 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:25:56 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:25:56 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:25:56 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:25:56 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:25:56 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:25:56 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:25:56 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:25:56 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:26:00 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:26:00 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:26:00 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:26:00 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:26:00 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
2014-04-23 09:26:00 [DEBUG]: ikev1_natt.c:348:natt_keepalive_send(): KA: 122.152.XX.XX[4500]->195.243.XX.XX[4500]
2014-04-23 09:26:00 [DEBUG]: sockmisc.c:335:sendfromto(): sockname 122.152.XX.XX[4500]
2014-04-23 09:26:00 [DEBUG]: sockmisc.c:337:sendfromto(): send packet from 122.152.XX.XX[4500]
2014-04-23 09:26:00 [DEBUG]: sockmisc.c:339:sendfromto(): send packet to 195.243.XX.XX[4500]
2014-04-23 09:26:00 [DEBUG]: sockmisc.c:524:sendfromto(): 1 times of 1 bytes message will be sent to 195.243.XX.XX[4500]
2014-04-23 09:26:00 [DEBUG]: sockmisc.c:528:sendfromto():
ff
Apr 23 09:26:00 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:26:00 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:26:00 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:26:00 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:26:00 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
2014-04-23 09:26:01 [DEBUG]: isakmp.c:944:isakmp_handler(): ===
2014-04-23 09:26:01 [DEBUG]: isakmp.c:945:isakmp_handler(): 108 bytes message received from 175.184.XX.XX[500]
2014-04-23 09:26:01 [DEBUG]: isakmp.c:948:isakmp_handler():
145d0809 aa26336e 51486f01 4c369834 08100501 c7e67393 0000006c b63fd7df
b58f6f7b d91b1cbd ae369f74 fbea485a 2ba1f3f1 e0947ecd 97b2cfe0 886aadff
4b3dd069 a6c4e7bd cf6906a6 ee9bc4c0 9aa69a9a 9db1fad5 3fba7791 f9f34d69
23fb36d0 613eb03f 51d3e456
2014-04-23 09:26:01 [DEBUG]: isakmp_inf.c:147:isakmp_info_recv(): receive Information.
2014-04-23 09:26:01 [DEBUG]: oakley.c:3028:oakley_newiv2(): compute IV for phase2
2014-04-23 09:26:01 [DEBUG]: oakley.c:3029:oakley_newiv2(): phase1 last IV:
2014-04-23 09:26:01 [DEBUG]: oakley.c:3030:oakley_newiv2():
f48759f0 6611810f 1ee2b6c3 8429842c c7e67393
2014-04-23 09:26:01 [DEBUG]: algorithm.c:386:alg_oakley_hashdef(): hash(sha256)
2014-04-23 09:26:01 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-04-23 09:26:01 [DEBUG]: oakley.c:3063:oakley_newiv2(): phase2 IV computed:
2014-04-23 09:26:01 [DEBUG]: oakley.c:3064:oakley_newiv2():
3caa6faa ac5a2ae9 82a80c9d 40921597
2014-04-23 09:26:01 [DEBUG]: oakley.c:3109:oakley_do_decrypt(): begin decryption.
2014-04-23 09:26:01 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-04-23 09:26:01 [DEBUG]: oakley.c:3123:oakley_do_decrypt(): IV was saved for next processing:
2014-04-23 09:26:01 [DEBUG]: oakley.c:3125:oakley_do_decrypt():
f9f34d69 23fb36d0 613eb03f 51d3e456
2014-04-23 09:26:01 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-04-23 09:26:01 [DEBUG]: oakley.c:3148:oakley_do_decrypt(): with key:
2014-04-23 09:26:01 [DEBUG]: oakley.c:3149:oakley_do_decrypt():
ee9ab0b8 45683e6c 2d4acc33 c75e88b1 19b2305d 7dc6bbe8 a1a58893 c00d708d
2014-04-23 09:26:01 [DEBUG]: oakley.c:3154:oakley_do_decrypt(): decrypted payload by IV:
2014-04-23 09:26:01 [DEBUG]: oakley.c:3155:oakley_do_decrypt():
3caa6faa ac5a2ae9 82a80c9d 40921597
2014-04-23 09:26:01 [DEBUG]: oakley.c:3157:oakley_do_decrypt(): decrypted payload, but not trimed.
2014-04-23 09:26:01 [DEBUG]: oakley.c:3159:oakley_do_decrypt():
0b000024 75f0efed 34de1dbe f03b8207 16ef4958 b7648e53 01f3e15f c7f19a3b
a8817710 00000020 00000001 01108d28 145d0809 aa26336e 51486f01 4c369834
13adfd18 00000000 00000000 00000000
2014-04-23 09:26:01 [DEBUG]: oakley.c:3168:oakley_do_decrypt(): padding len=0
2014-04-23 09:26:01 [DEBUG]: oakley.c:3199:oakley_do_decrypt(): decrypted.
2014-04-23 09:26:01 [DEBUG]: oakley.c:3200:oakley_do_decrypt():
145d0809 aa26336e 51486f01 4c369834 08100501 c7e67393 0000006c 0b000024
75f0efed 34de1dbe f03b8207 16ef4958 b7648e53 01f3e15f c7f19a3b a8817710
00000020 00000001 01108d28 145d0809 aa26336e 51486f01 4c369834 13adfd18
00000000 00000000 00000000
2014-04-23 09:26:01 [DEBUG]: oakley.c:3088:oakley_delivm(): IV freed
2014-04-23 09:26:01 [DEBUG]: oakley.c:682:oakley_compute_hash1(): HASH with:
2014-04-23 09:26:01 [DEBUG]: oakley.c:683:oakley_compute_hash1():
c7e67393 00000020 00000001 01108d28 145d0809 aa26336e 51486f01 4c369834
13adfd18
2014-04-23 09:26:01 [DEBUG]: algorithm.c:469:alg_oakley_hmacdef(): hmac(hmac_sha2_256)
2014-04-23 09:26:01 [DEBUG]: oakley.c:692:oakley_compute_hash1(): HASH computed:
2014-04-23 09:26:01 [DEBUG]: oakley.c:693:oakley_compute_hash1():
75f0efed 34de1dbe f03b8207 16ef4958 b7648e53 01f3e15f c7f19a3b a8817710
2014-04-23 09:26:01 [DEBUG]: isakmp_inf.c:262:isakmp_info_recv(): hash validated.
2014-04-23 09:26:01 [DEBUG]: ikev1.c:2831:isakmp_parsewoh(): begin.
2014-04-23 09:26:01 [DEBUG]: ikev1.c:2858:isakmp_parsewoh(): seen nptype=8(hash)
2014-04-23 09:26:01 [DEBUG]: ikev1.c:2858:isakmp_parsewoh(): seen nptype=11(notify)
2014-04-23 09:26:01 [DEBUG]: ikev1.c:2897:isakmp_parsewoh(): succeed.
2014-04-23 09:26:01 [DEBUG]: isakmp_inf.c:1540:isakmp_info_recv_r_u(): DPD R-U-There received
2014-04-23 09:26:01 [DEBUG]: oakley.c:3028:oakley_newiv2(): compute IV for phase2
2014-04-23 09:26:01 [DEBUG]: oakley.c:3029:oakley_newiv2(): phase1 last IV:
2014-04-23 09:26:01 [DEBUG]: oakley.c:3030:oakley_newiv2():
f48759f0 6611810f 1ee2b6c3 8429842c 31e8e8e9
2014-04-23 09:26:01 [DEBUG]: algorithm.c:386:alg_oakley_hashdef(): hash(sha256)
2014-04-23 09:26:01 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-04-23 09:26:01 [DEBUG]: oakley.c:3063:oakley_newiv2(): phase2 IV computed:
2014-04-23 09:26:01 [DEBUG]: oakley.c:3064:oakley_newiv2():
a4590b78 f01d1b55 81e56e66 3a797954
2014-04-23 09:26:01 [DEBUG]: oakley.c:682:oakley_compute_hash1(): HASH with:
2014-04-23 09:26:01 [DEBUG]: oakley.c:683:oakley_compute_hash1():
31e8e8e9 00000020 00000001 01108d29 145d0809 aa26336e 51486f01 4c369834
13adfd18
2014-04-23 09:26:01 [DEBUG]: algorithm.c:469:alg_oakley_hmacdef(): hmac(hmac_sha2_256)
2014-04-23 09:26:01 [DEBUG]: oakley.c:692:oakley_compute_hash1(): HASH computed:
2014-04-23 09:26:01 [DEBUG]: oakley.c:693:oakley_compute_hash1():
b89d3e73 6630d125 9bed3e97 4df40e79 bb5aacb6 69f0e0f4 80320038 f2f07a4b
2014-04-23 09:26:01 [DEBUG]: oakley.c:3234:oakley_do_encrypt(): begin encryption.
2014-04-23 09:26:01 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-04-23 09:26:01 [DEBUG]: oakley.c:3250:oakley_do_encrypt(): pad length = 12
2014-04-23 09:26:01 [DEBUG]: oakley.c:3280:oakley_do_encrypt():
0b000024 b89d3e73 6630d125 9bed3e97 4df40e79 bb5aacb6 69f0e0f4 80320038
f2f07a4b 00000020 00000001 01108d29 145d0809 aa26336e 51486f01 4c369834
13adfd18 442ef4b0 3517fc5a 8f93f30c
2014-04-23 09:26:01 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-04-23 09:26:01 [DEBUG]: oakley.c:3290:oakley_do_encrypt(): with key:
2014-04-23 09:26:01 [DEBUG]: oakley.c:3291:oakley_do_encrypt():
ee9ab0b8 45683e6c 2d4acc33 c75e88b1 19b2305d 7dc6bbe8 a1a58893 c00d708d
2014-04-23 09:26:01 [DEBUG]: oakley.c:3296:oakley_do_encrypt(): encrypted payload by IV:
2014-04-23 09:26:01 [DEBUG]: oakley.c:3297:oakley_do_encrypt():
a4590b78 f01d1b55 81e56e66 3a797954
2014-04-23 09:26:01 [DEBUG]: oakley.c:3303:oakley_do_encrypt(): save IV for next:
2014-04-23 09:26:01 [DEBUG]: oakley.c:3304:oakley_do_encrypt():
e0066987 f85906b4 c20a9788 24beb305
2014-04-23 09:26:01 [DEBUG]: oakley.c:3320:oakley_do_encrypt(): encrypted.
2014-04-23 09:26:01 [DEBUG]: ikev1.c:2978:isakmp_send(): 108 bytes from 122.152.XX.XX[500] to 175.184.XX.XX[500]
2014-04-23 09:26:01 [DEBUG]: sockmisc.c:335:sendfromto(): sockname 122.152.XX.XX[500]
2014-04-23 09:26:01 [DEBUG]: sockmisc.c:337:sendfromto(): send packet from 122.152.XX.XX[500]
2014-04-23 09:26:01 [DEBUG]: sockmisc.c:339:sendfromto(): send packet to 175.184.XX.XX[500]
2014-04-23 09:26:01 [DEBUG]: sockmisc.c:524:sendfromto(): 1 times of 108 bytes message will be sent to 175.184.XX.XX[500]
2014-04-23 09:26:01 [DEBUG]: sockmisc.c:528:sendfromto():
145d0809 aa26336e 51486f01 4c369834 08100501 31e8e8e9 0000006c 6c14a920
58a2bc54 04bb6754 81334668 f9b6fc32 a3c8225f 44560a48 9e043e0a 8c189207
85b7d931 80c9abd7 5c33cc3b c90282f4 674673e9 d306b4d3 e8933eca e0066987
f85906b4 c20a9788 24beb305
2014-04-23 09:26:01 [DEBUG]: isakmp_inf.c:805:isakmp_info_send_common(): sendto Information notify.
2014-04-23 09:26:01 [DEBUG]: oakley.c:3088:oakley_delivm(): IV freed
2014-04-23 09:26:01 [DEBUG]: isakmp_inf.c:1569:isakmp_info_recv_r_u(): received a valid R-U-THERE, ACK sent
2014-04-23 09:26:01 [PROTO_NOTIFY]: isakmp_inf.c:1159:isakmp_info_recv_n(): notification message 36136:R-U-THERE, doi=1 proto_id=1 spi=145d0809aa26336e 51486f014c369834 (size=16).
2014-04-23 09:26:01 [DEBUG]: isakmp.c:944:isakmp_handler(): ===
2014-04-23 09:26:01 [DEBUG]: isakmp.c:945:isakmp_handler(): 140 bytes message received from 195.243.XX.XX[4500]
2014-04-23 09:26:01 [DEBUG]: isakmp.c:948:isakmp_handler():
12f2e961 943f0451 d4bfae00 36686dc1 08100501 f26f1857 0000008c 5928cc6e
944d0f20 0324723b 948bcd45 792478d0 cae22352 5b86c1a1 1d8a818b 780e5866
f8d7a5e4 602155f8 86db954a eef9091f 8f826088 d71eeb50 9ab2eda4 a1cb2b56
655d86f6 3262b197 f8628d10 5d813ae2 abbbdd52 a25d1e1f d899bd0a 671b2ca2
9b617b6a ff675894 c2d4b3f0
2014-04-23 09:26:01 [DEBUG]: isakmp_inf.c:147:isakmp_info_recv(): receive Information.
2014-04-23 09:26:01 [DEBUG]: oakley.c:3028:oakley_newiv2(): compute IV for phase2
2014-04-23 09:26:01 [DEBUG]: oakley.c:3029:oakley_newiv2(): phase1 last IV:
2014-04-23 09:26:01 [DEBUG]: oakley.c:3030:oakley_newiv2():
932ea3a6 46bac677 74b0a410 9ca00acd f26f1857
2014-04-23 09:26:01 [DEBUG]: algorithm.c:386:alg_oakley_hashdef(): hash(sha512)
2014-04-23 09:26:01 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-04-23 09:26:01 [DEBUG]: oakley.c:3063:oakley_newiv2(): phase2 IV computed:
2014-04-23 09:26:01 [DEBUG]: oakley.c:3064:oakley_newiv2():
10099a60 3b69000f b4cc9576 da175cfb
2014-04-23 09:26:01 [DEBUG]: oakley.c:3109:oakley_do_decrypt(): begin decryption.
2014-04-23 09:26:01 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-04-23 09:26:01 [DEBUG]: oakley.c:3123:oakley_do_decrypt(): IV was saved for next processing:
2014-04-23 09:26:01 [DEBUG]: oakley.c:3125:oakley_do_decrypt():
671b2ca2 9b617b6a ff675894 c2d4b3f0
2014-04-23 09:26:01 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-04-23 09:26:01 [DEBUG]: oakley.c:3148:oakley_do_decrypt(): with key:
2014-04-23 09:26:01 [DEBUG]: oakley.c:3149:oakley_do_decrypt():
d7337258 41d74255 31c70f8c 9ae72620 b9ee228c b7980138 e1b75316 2c09557b
2014-04-23 09:26:01 [DEBUG]: oakley.c:3154:oakley_do_decrypt(): decrypted payload by IV:
2014-04-23 09:26:01 [DEBUG]: oakley.c:3155:oakley_do_decrypt():
10099a60 3b69000f b4cc9576 da175cfb
2014-04-23 09:26:01 [DEBUG]: oakley.c:3157:oakley_do_decrypt(): decrypted payload, but not trimed.
2014-04-23 09:26:01 [DEBUG]: oakley.c:3159:oakley_do_decrypt():
0b000044 92aec208 8911826a fbec5ed4 029e8bed a4452500 258eb6bd f9e6c3c4
5f572c22 528aa88c 9050d1b5 3e950c4e bdcb40a2 8fbd2094 bed0ee63 d769cbbb
c325d8f7 00000020 00000001 01108d28 12f2e961 943f0451 d4bfae00 36686dc1
2dc4edac 00000000 00000000 00000000
2014-04-23 09:26:01 [DEBUG]: oakley.c:3168:oakley_do_decrypt(): padding len=0
2014-04-23 09:26:01 [DEBUG]: oakley.c:3199:oakley_do_decrypt(): decrypted.
2014-04-23 09:26:01 [DEBUG]: oakley.c:3200:oakley_do_decrypt():
12f2e961 943f0451 d4bfae00 36686dc1 08100501 f26f1857 0000008c 0b000044
92aec208 8911826a fbec5ed4 029e8bed a4452500 258eb6bd f9e6c3c4 5f572c22
528aa88c 9050d1b5 3e950c4e bdcb40a2 8fbd2094 bed0ee63 d769cbbb c325d8f7
00000020 00000001 01108d28 12f2e961 943f0451 d4bfae00 36686dc1 2dc4edac
00000000 00000000 00000000
2014-04-23 09:26:01 [DEBUG]: oakley.c:3088:oakley_delivm(): IV freed
2014-04-23 09:26:01 [DEBUG]: oakley.c:682:oakley_compute_hash1(): HASH with:
2014-04-23 09:26:01 [DEBUG]: oakley.c:683:oakley_compute_hash1():
f26f1857 00000020 00000001 01108d28 12f2e961 943f0451 d4bfae00 36686dc1
2dc4edac
2014-04-23 09:26:01 [DEBUG]: algorithm.c:469:alg_oakley_hmacdef(): hmac(hmac_sha2_512)
2014-04-23 09:26:01 [DEBUG]: oakley.c:692:oakley_compute_hash1(): HASH computed:
2014-04-23 09:26:01 [DEBUG]: oakley.c:693:oakley_compute_hash1():
92aec208 8911826a fbec5ed4 029e8bed a4452500 258eb6bd f9e6c3c4 5f572c22
528aa88c 9050d1b5 3e950c4e bdcb40a2 8fbd2094 bed0ee63 d769cbbb c325d8f7
2014-04-23 09:26:01 [DEBUG]: isakmp_inf.c:262:isakmp_info_recv(): hash validated.
2014-04-23 09:26:01 [DEBUG]: isakmp_inf.c:262:isakmp_info_recv(): hash validated.
2014-04-23 09:26:01 [DEBUG]: ikev1.c:2831:isakmp_parsewoh(): begin.
2014-04-23 09:26:01 [DEBUG]: ikev1.c:2858:isakmp_parsewoh(): seen nptype=8(hash)
2014-04-23 09:26:01 [DEBUG]: ikev1.c:2858:isakmp_parsewoh(): seen nptype=11(notify)
2014-04-23 09:26:01 [DEBUG]: ikev1.c:2897:isakmp_parsewoh(): succeed.
2014-04-23 09:26:01 [DEBUG]: isakmp_inf.c:1540:isakmp_info_recv_r_u(): DPD R-U-There received
2014-04-23 09:26:01 [DEBUG]: oakley.c:3028:oakley_newiv2(): compute IV for phase2
2014-04-23 09:26:01 [DEBUG]: oakley.c:3029:oakley_newiv2(): phase1 last IV:
2014-04-23 09:26:01 [DEBUG]: oakley.c:3030:oakley_newiv2():
932ea3a6 46bac677 74b0a410 9ca00acd 284714b0
2014-04-23 09:26:01 [DEBUG]: algorithm.c:386:alg_oakley_hashdef(): hash(sha512)
2014-04-23 09:26:01 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-04-23 09:26:01 [DEBUG]: oakley.c:3063:oakley_newiv2(): phase2 IV computed:
2014-04-23 09:26:01 [DEBUG]: oakley.c:3064:oakley_newiv2():
308c5b76 71384e07 31812484 9332c132
2014-04-23 09:26:01 [DEBUG]: oakley.c:682:oakley_compute_hash1(): HASH with:
2014-04-23 09:26:01 [DEBUG]: oakley.c:683:oakley_compute_hash1():
284714b0 00000020 00000001 01108d29 12f2e961 943f0451 d4bfae00 36686dc1
2dc4edac
2014-04-23 09:26:01 [DEBUG]: algorithm.c:469:alg_oakley_hmacdef(): hmac(hmac_sha2_512)
2014-04-23 09:26:01 [DEBUG]: oakley.c:692:oakley_compute_hash1(): HASH computed:
2014-04-23 09:26:01 [DEBUG]: oakley.c:693:oakley_compute_hash1():
570b9980 88291a55 97e58910 e0541ee0 4a47ff96 8c2c4411 09e8056d b4055728
b1705e69 6c2c94e9 6fa26c5a 057eaa89 85acd580 179fc56a 1cba106e 5d4dfd3f
2014-04-23 09:26:01 [DEBUG]: oakley.c:3234:oakley_do_encrypt(): begin encryption.
2014-04-23 09:26:01 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-04-23 09:26:01 [DEBUG]: oakley.c:3250:oakley_do_encrypt(): pad length = 12
2014-04-23 09:26:01 [DEBUG]: oakley.c:3280:oakley_do_encrypt():
0b000044 570b9980 88291a55 97e58910 e0541ee0 4a47ff96 8c2c4411 09e8056d
b4055728 b1705e69 6c2c94e9 6fa26c5a 057eaa89 85acd580 179fc56a 1cba106e
5d4dfd3f 00000020 00000001 01108d29 12f2e961 943f0451 d4bfae00 36686dc1
2dc4edac b1ae0007 a0cd929a c879090c
2014-04-23 09:26:01 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-04-23 09:26:01 [DEBUG]: oakley.c:3290:oakley_do_encrypt(): with key:
2014-04-23 09:26:01 [DEBUG]: oakley.c:3291:oakley_do_encrypt():
d7337258 41d74255 31c70f8c 9ae72620 b9ee228c b7980138 e1b75316 2c09557b
2014-04-23 09:26:01 [DEBUG]: oakley.c:3296:oakley_do_encrypt(): encrypted payload by IV:
2014-04-23 09:26:01 [DEBUG]: oakley.c:3297:oakley_do_encrypt():
308c5b76 71384e07 31812484 9332c132
2014-04-23 09:26:01 [DEBUG]: oakley.c:3303:oakley_do_encrypt(): save IV for next:
2014-04-23 09:26:01 [DEBUG]: oakley.c:3304:oakley_do_encrypt():
f0c7e72d c4897256 aac91fbd d7afea3c
2014-04-23 09:26:01 [DEBUG]: oakley.c:3320:oakley_do_encrypt(): encrypted.
2014-04-23 09:26:01 [DEBUG]: ikev1.c:2953:isakmp_send(): Adding NON-ESP marker
2014-04-23 09:26:01 [DEBUG]: ikev1.c:2978:isakmp_send(): 144 bytes from 122.152.XX.XX[4500] to 195.243.XX.XX[4500]
2014-04-23 09:26:01 [DEBUG]: sockmisc.c:335:sendfromto(): sockname 122.152.XX.XX[4500]
2014-04-23 09:26:01 [DEBUG]: sockmisc.c:337:sendfromto(): send packet from 122.152.XX.XX[4500]
2014-04-23 09:26:01 [DEBUG]: sockmisc.c:339:sendfromto(): send packet to 195.243.XX.XX[4500]
2014-04-23 09:26:01 [DEBUG]: sockmisc.c:524:sendfromto(): 1 times of 144 bytes message will be sent to 195.243.XX.XX[4500]
2014-04-23 09:26:01 [DEBUG]: sockmisc.c:528:sendfromto():
00000000 12f2e961 943f0451 d4bfae00 36686dc1 08100501 284714b0 0000008c
1998db73 f4c0a42c f4be706a c7a016c7 9a68a45c 44a21aba 0b5761fa a1db90e1
f278d71a ce5c5dfa 19a68ee8 6d8d209f 727dc200 dc7215fe 5fffdde8 ac461037
3dc5a14d d508a0f3 3f9ab870 a325ff67 86d51e17 278f9705 2ee1d102 f0a215fd
f0c7e72d c4897256 aac91fbd d7afea3c
2014-04-23 09:26:01 [DEBUG]: isakmp_inf.c:805:isakmp_info_send_common(): sendto Information notify.
2014-04-23 09:26:01 [DEBUG]: oakley.c:3088:oakley_delivm(): IV freed
2014-04-23 09:26:01 [DEBUG]: isakmp_inf.c:1569:isakmp_info_recv_r_u(): received a valid R-U-THERE, ACK sent
2014-04-23 09:26:01 [PROTO_NOTIFY]: isakmp_inf.c:1159:isakmp_info_recv_n(): notification message 36136:R-U-THERE, doi=1 proto_id=1 spi=12f2e961943f0451 d4bfae0036686dc1 (size=16).
2014-04-23 09:26:02 [DEBUG]: isakmp.c:944:isakmp_handler(): ===
2014-04-23 09:26:02 [DEBUG]: isakmp.c:945:isakmp_handler(): 108 bytes message received from 175.141.XX.XX[500]
2014-04-23 09:26:02 [DEBUG]: isakmp.c:948:isakmp_handler():
e83fbd85 4cba7233 621245d3 15bd2379 08100501 0d2e23c4 0000006c 6087262a
54a9993b 7be62b1f 46f23409 39588063 98504ad6 95e7c1b9 1ab39923 5f445250
6867e272 d203f5a0 aa31973d 8ad3d5ea e034893d 4fb926fb 4bd2826d abfcc168
32d2dc92 7a25b6e8 26666f3b
2014-04-23 09:26:02 [DEBUG]: isakmp_inf.c:147:isakmp_info_recv(): receive Information.
2014-04-23 09:26:02 [DEBUG]: oakley.c:3028:oakley_newiv2(): compute IV for phase2
2014-04-23 09:26:02 [DEBUG]: oakley.c:3029:oakley_newiv2(): phase1 last IV:
2014-04-23 09:26:02 [DEBUG]: oakley.c:3030:oakley_newiv2():
01b02da7 af7ffffd 159c73f7 00c1a160 0d2e23c4
2014-04-23 09:26:02 [DEBUG]: algorithm.c:386:alg_oakley_hashdef(): hash(sha256)
2014-04-23 09:26:02 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-04-23 09:26:02 [DEBUG]: oakley.c:3063:oakley_newiv2(): phase2 IV computed:
2014-04-23 09:26:02 [DEBUG]: oakley.c:3064:oakley_newiv2():
bb52a6c1 49925310 bfea1745 1f9f3865
2014-04-23 09:26:02 [DEBUG]: oakley.c:3109:oakley_do_decrypt(): begin decryption.
2014-04-23 09:26:02 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-04-23 09:26:02 [DEBUG]: oakley.c:3123:oakley_do_decrypt(): IV was saved for next processing:
2014-04-23 09:26:02 [DEBUG]: oakley.c:3125:oakley_do_decrypt():
abfcc168 32d2dc92 7a25b6e8 26666f3b
2014-04-23 09:26:02 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-04-23 09:26:02 [DEBUG]: oakley.c:3148:oakley_do_decrypt(): with key:
2014-04-23 09:26:02 [DEBUG]: oakley.c:3149:oakley_do_decrypt():
631a6335 2240d720 6e3977af 7383dd84 ef01871f 7d19c621 24d1228f 20966358
2014-04-23 09:26:02 [DEBUG]: oakley.c:3154:oakley_do_decrypt(): decrypted payload by IV:
2014-04-23 09:26:02 [DEBUG]: oakley.c:3155:oakley_do_decrypt():
bb52a6c1 49925310 bfea1745 1f9f3865
2014-04-23 09:26:02 [DEBUG]: oakley.c:3157:oakley_do_decrypt(): decrypted payload, but not trimed.
2014-04-23 09:26:02 [DEBUG]: oakley.c:3159:oakley_do_decrypt():
0b000024 331c95e2 5bef0111 75f3f2b3 f38ef8a6 389bae63 1e6b46f5 d8ef87b6
3d33151c 00000020 00000001 01108d28 e83fbd85 4cba7233 621245d3 15bd2379
34b57d93 00000000 00000000 00000000
2014-04-23 09:26:02 [DEBUG]: oakley.c:3168:oakley_do_decrypt(): padding len=0
2014-04-23 09:26:02 [DEBUG]: oakley.c:3199:oakley_do_decrypt(): decrypted.
2014-04-23 09:26:02 [DEBUG]: oakley.c:3200:oakley_do_decrypt():
e83fbd85 4cba7233 621245d3 15bd2379 08100501 0d2e23c4 0000006c 0b000024
331c95e2 5bef0111 75f3f2b3 f38ef8a6 389bae63 1e6b46f5 d8ef87b6 3d33151c
00000020 00000001 01108d28 e83fbd85 4cba7233 621245d3 15bd2379 34b57d93
00000000 00000000 00000000
2014-04-23 09:26:02 [DEBUG]: oakley.c:3088:oakley_delivm(): IV freed
2014-04-23 09:26:02 [DEBUG]: oakley.c:682:oakley_compute_hash1(): HASH with:
2014-04-23 09:26:02 [DEBUG]: oakley.c:683:oakley_compute_hash1():
0d2e23c4 00000020 00000001 01108d28 e83fbd85 4cba7233 621245d3 15bd2379
34b57d93
2014-04-23 09:26:02 [DEBUG]: algorithm.c:469:alg_oakley_hmacdef(): hmac(hmac_sha2_256)
2014-04-23 09:26:02 [DEBUG]: oakley.c:692:oakley_compute_hash1(): HASH computed:
2014-04-23 09:26:02 [DEBUG]: oakley.c:693:oakley_compute_hash1():
331c95e2 5bef0111 75f3f2b3 f38ef8a6 389bae63 1e6b46f5 d8ef87b6 3d33151c
2014-04-23 09:26:02 [DEBUG]: isakmp_inf.c:262:isakmp_info_recv(): hash validated.
2014-04-23 09:26:02 [DEBUG]: ikev1.c:2831:isakmp_parsewoh(): begin.
2014-04-23 09:26:02 [DEBUG]: ikev1.c:2858:isakmp_parsewoh(): seen nptype=8(hash)
2014-04-23 09:26:02 [DEBUG]: ikev1.c:2858:isakmp_parsewoh(): seen nptype=11(notify)
2014-04-23 09:26:02 [DEBUG]: ikev1.c:2897:isakmp_parsewoh(): succeed.
2014-04-23 09:26:02 [DEBUG]: isakmp_inf.c:1540:isakmp_info_recv_r_u(): DPD R-U-There received
2014-04-23 09:26:02 [DEBUG]: oakley.c:3028:oakley_newiv2(): compute IV for phase2
2014-04-23 09:26:02 [DEBUG]: oakley.c:3029:oakley_newiv2(): phase1 last IV:
2014-04-23 09:26:02 [DEBUG]: oakley.c:3030:oakley_newiv2():
01b02da7 af7ffffd 159c73f7 00c1a160 4fdb55e7
2014-04-23 09:26:02 [DEBUG]: algorithm.c:386:alg_oakley_hashdef(): hash(sha256)
2014-04-23 09:26:02 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-04-23 09:26:02 [DEBUG]: oakley.c:3063:oakley_newiv2(): phase2 IV computed:
2014-04-23 09:26:02 [DEBUG]: oakley.c:3064:oakley_newiv2():
f60e34d0 40c2eec0 50e5a29b f63d749f
2014-04-23 09:26:02 [DEBUG]: oakley.c:682:oakley_compute_hash1(): HASH with:
2014-04-23 09:26:02 [DEBUG]: oakley.c:683:oakley_compute_hash1():
4fdb55e7 00000020 00000001 01108d29 e83fbd85 4cba7233 621245d3 15bd2379
34b57d93
2014-04-23 09:26:02 [DEBUG]: algorithm.c:469:alg_oakley_hmacdef(): hmac(hmac_sha2_256)
2014-04-23 09:26:02 [DEBUG]: oakley.c:692:oakley_compute_hash1(): HASH computed:
2014-04-23 09:26:02 [DEBUG]: oakley.c:693:oakley_compute_hash1():
d0971385 50530427 2773358d 53316301 324f3e0e 8da6064f 24a6a89f 33131b79
2014-04-23 09:26:02 [DEBUG]: oakley.c:3234:oakley_do_encrypt(): begin encryption.
2014-04-23 09:26:02 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-04-23 09:26:02 [DEBUG]: oakley.c:3250:oakley_do_encrypt(): pad length = 12
2014-04-23 09:26:02 [DEBUG]: oakley.c:3280:oakley_do_encrypt():
0b000024 d0971385 50530427 2773358d 53316301 324f3e0e 8da6064f 24a6a89f
33131b79 00000020 00000001 01108d29 e83fbd85 4cba7233 621245d3 15bd2379
34b57d93 9ead0aa5 8c4549fd 1ed6300c
2014-04-23 09:26:02 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-04-23 09:26:02 [DEBUG]: oakley.c:3290:oakley_do_encrypt(): with key:
2014-04-23 09:26:02 [DEBUG]: oakley.c:3291:oakley_do_encrypt():
631a6335 2240d720 6e3977af 7383dd84 ef01871f 7d19c621 24d1228f 20966358
2014-04-23 09:26:02 [DEBUG]: oakley.c:3296:oakley_do_encrypt(): encrypted payload by IV:
2014-04-23 09:26:02 [DEBUG]: oakley.c:3297:oakley_do_encrypt():
f60e34d0 40c2eec0 50e5a29b f63d749f
2014-04-23 09:26:02 [DEBUG]: oakley.c:3303:oakley_do_encrypt(): save IV for next:
2014-04-23 09:26:02 [DEBUG]: oakley.c:3304:oakley_do_encrypt():
27c3e352 9b971805 ac8e3f3b 7dc1be55
2014-04-23 09:26:02 [DEBUG]: oakley.c:3320:oakley_do_encrypt(): encrypted.
2014-04-23 09:26:02 [DEBUG]: ikev1.c:2978:isakmp_send(): 108 bytes from 122.152.XX.XX[500] to 175.141.XX.XX[500]
2014-04-23 09:26:02 [DEBUG]: sockmisc.c:335:sendfromto(): sockname 122.152.XX.XX[500]
2014-04-23 09:26:02 [DEBUG]: sockmisc.c:337:sendfromto(): send packet from 122.152.XX.XX[500]
2014-04-23 09:26:02 [DEBUG]: sockmisc.c:339:sendfromto(): send packet to 175.141.XX.XX[500]
2014-04-23 09:26:02 [DEBUG]: sockmisc.c:524:sendfromto(): 1 times of 108 bytes message will be sent to 175.141.XX.XX[500]
2014-04-23 09:26:02 [DEBUG]: sockmisc.c:528:sendfromto():
e83fbd85 4cba7233 621245d3 15bd2379 08100501 4fdb55e7 0000006c 0eb9bb72
adc63881 ce76a334 a308e96d d18b323e 00736fc5 9e3820d1 82ed608f 05efae9d
03348416 ab154352 dbf6b241 4ecafa95 371febb2 c6f0f261 1b82b0d5 27c3e352
9b971805 ac8e3f3b 7dc1be55
2014-04-23 09:26:02 [DEBUG]: isakmp_inf.c:805:isakmp_info_send_common(): sendto Information notify.
2014-04-23 09:26:02 [DEBUG]: oakley.c:3088:oakley_delivm(): IV freed
2014-04-23 09:26:02 [DEBUG]: isakmp_inf.c:1569:isakmp_info_recv_r_u(): received a valid R-U-THERE, ACK sent
2014-04-23 09:26:02 [PROTO_NOTIFY]: isakmp_inf.c:1159:isakmp_info_recv_n(): notification message 36136:R-U-THERE, doi=1 proto_id=1 spi=e83fbd854cba7233 621245d315bd2379 (size=16).
Apr 23 09:26:04 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:26:04 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:26:04 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:26:04 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:26:04 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:26:04 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:26:04 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:26:04 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:26:04 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:26:04 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:26:10 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:26:10 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:26:10 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:26:10 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:26:10 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:26:10 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:26:10 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:26:10 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:26:10 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:26:10 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:26:14 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:26:14 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:26:14 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:26:14 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:26:14 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:26:14 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:26:14 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:26:14 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:26:14 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:26:14 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:26:18 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:26:18 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:26:18 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:26:18 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:26:18 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:26:18 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:26:18 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:26:18 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:26:18 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:26:18 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
2014-04-23 09:26:20 [DEBUG]: ikev1_natt.c:348:natt_keepalive_send(): KA: 122.152.XX.XX[4500]->195.243.XX.XX[4500]
2014-04-23 09:26:20 [DEBUG]: sockmisc.c:335:sendfromto(): sockname 122.152.XX.XX[4500]
2014-04-23 09:26:20 [DEBUG]: sockmisc.c:337:sendfromto(): send packet from 122.152.XX.XX[4500]
2014-04-23 09:26:20 [DEBUG]: sockmisc.c:339:sendfromto(): send packet to 195.243.XX.XX[4500]
2014-04-23 09:26:20 [DEBUG]: sockmisc.c:524:sendfromto(): 1 times of 1 bytes message will be sent to 195.243.XX.XX[4500]
2014-04-23 09:26:20 [DEBUG]: sockmisc.c:528:sendfromto():
ff
Apr 23 09:26:22 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:26:22 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:26:22 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:26:22 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:26:22 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:26:22 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:26:22 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:26:22 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:26:22 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:26:22 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:26:27 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:26:27 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:26:27 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:26:27 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:26:27 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:26:27 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:26:27 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:26:27 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:26:27 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:26:27 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:26:31 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:26:31 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:26:31 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:26:31 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:26:31 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:26:31 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:26:31 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:26:31 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:26:31 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:26:31 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
2014-04-23 09:26:34 [DEBUG]: isakmp.c:944:isakmp_handler(): ===
2014-04-23 09:26:34 [DEBUG]: isakmp.c:945:isakmp_handler(): 188 bytes message received from 175.141.XX.XX[500]
2014-04-23 09:26:34 [DEBUG]: isakmp.c:948:isakmp_handler():
e83fbd85 4cba7233 621245d3 15bd2379 08102001 041039ca 000000bc 370d7814
828f5e78 c6eafc50 331b5fc5 937f114a 7cea9903 33c9d0ed b2b859dd bf0b2ffc
554c9e81 2b396ca8 e0c3b3bf b89b8dba a9d716f8 2a8d9b7f e2687df4 9940ec65
8107c50c 76cb3d53 f5720cac cf5a9537 96dad681 cd46e259 5620b418 0d310a87
df8ea3aa 32ae00b6 505bf40d a3c41f86 d5131254 407ffb66 60776653 8f1809a9
e6f46fc8 0b96735b 99879b41 b766c104 93fe8817 213720e0 a71afef3
2014-04-23 09:26:34 [DEBUG]: oakley.c:3028:oakley_newiv2(): compute IV for phase2
2014-04-23 09:26:34 [DEBUG]: oakley.c:3029:oakley_newiv2(): phase1 last IV:
2014-04-23 09:26:34 [DEBUG]: oakley.c:3030:oakley_newiv2():
01b02da7 af7ffffd 159c73f7 00c1a160 041039ca
2014-04-23 09:26:34 [DEBUG]: algorithm.c:386:alg_oakley_hashdef(): hash(sha256)
2014-04-23 09:26:34 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-04-23 09:26:34 [DEBUG]: oakley.c:3063:oakley_newiv2(): phase2 IV computed:
2014-04-23 09:26:34 [DEBUG]: oakley.c:3064:oakley_newiv2():
e5788955 70a1f7f4 9f576935 6baea79e
2014-04-23 09:26:34 [PROTO_NOTIFY]: ikev1.c:2506:log_ph2started(): ====> PHASE-2 NEGOTIATION STARTED AS RESPONDER, (QUICK MODE) <====
====> Initiated SA: 122.152.XX.XX[500]-175.141.XX.XX[500] message id:0x041039CA <====
2014-04-23 09:26:34 [DEBUG]: oakley.c:3109:oakley_do_decrypt(): begin decryption.
2014-04-23 09:26:34 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-04-23 09:26:34 [DEBUG]: oakley.c:3123:oakley_do_decrypt(): IV was saved for next processing:
2014-04-23 09:26:34 [DEBUG]: oakley.c:3125:oakley_do_decrypt():
b766c104 93fe8817 213720e0 a71afef3
2014-04-23 09:26:34 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-04-23 09:26:34 [DEBUG]: oakley.c:3148:oakley_do_decrypt(): with key:
2014-04-23 09:26:34 [DEBUG]: oakley.c:3149:oakley_do_decrypt():
631a6335 2240d720 6e3977af 7383dd84 ef01871f 7d19c621 24d1228f 20966358
2014-04-23 09:26:34 [DEBUG]: oakley.c:3154:oakley_do_decrypt(): decrypted payload by IV:
2014-04-23 09:26:34 [DEBUG]: oakley.c:3155:oakley_do_decrypt():
e5788955 70a1f7f4 9f576935 6baea79e
2014-04-23 09:26:34 [DEBUG]: oakley.c:3157:oakley_do_decrypt(): decrypted payload, but not trimed.
2014-04-23 09:26:34 [DEBUG]: oakley.c:3159:oakley_do_decrypt():
01000024 8f2f2112 97ebccfc 8bb7f2ba 87445d60 58265732 28b21d08 ce030ab3
85120cd5 0a000040 00000001 00000001 00000034 01030401 e1420445 00000028
010c0000 80040001 80010001 80020e10 80010002 00020004 00465000 80050007
80060100 05000018 621d615e 541d371c 3d170ab2 6547fb28 13dd844e 05000010
04000000 00000000 00000000 00000010 04000000 00000000 00000000 00000000
2014-04-23 09:26:34 [DEBUG]: oakley.c:3168:oakley_do_decrypt(): padding len=0
2014-04-23 09:26:34 [DEBUG]: oakley.c:3199:oakley_do_decrypt(): decrypted.
2014-04-23 09:26:34 [DEBUG]: oakley.c:3200:oakley_do_decrypt():
e83fbd85 4cba7233 621245d3 15bd2379 08102001 041039ca 000000bc 01000024
8f2f2112 97ebccfc 8bb7f2ba 87445d60 58265732 28b21d08 ce030ab3 85120cd5
0a000040 00000001 00000001 00000034 01030401 e1420445 00000028 010c0000
80040001 80010001 80020e10 80010002 00020004 00465000 80050007 80060100
05000018 621d615e 541d371c 3d170ab2 6547fb28 13dd844e 05000010 04000000
00000000 00000000 00000010 04000000 00000000 00000000 00000000
2014-04-23 09:26:34 [DEBUG]: ikev1.c:2831:isakmp_parsewoh(): begin.
2014-04-23 09:26:34 [DEBUG]: ikev1.c:2858:isakmp_parsewoh(): seen nptype=8(hash)
2014-04-23 09:26:34 [DEBUG]: ikev1.c:2858:isakmp_parsewoh(): seen nptype=1(sa)
2014-04-23 09:26:34 [DEBUG]: ikev1.c:2858:isakmp_parsewoh(): seen nptype=10(nonce)
2014-04-23 09:26:34 [DEBUG]: ikev1.c:2858:isakmp_parsewoh(): seen nptype=5(id)
2014-04-23 09:26:34 [DEBUG]: ikev1.c:2858:isakmp_parsewoh(): seen nptype=5(id)
2014-04-23 09:26:34 [DEBUG]: ikev1.c:2897:isakmp_parsewoh(): succeed.
2014-04-23 09:26:34 [DEBUG]: isakmp_quick.c:1163:quick_r1recv(): received IDci2:2014-04-23 09:26:34 [DEBUG]: isakmp_quick.c:1164:quick_r1recv():
04000000 00000000 00000000
2014-04-23 09:26:34 [DEBUG]: isakmp_quick.c:1167:quick_r1recv(): received IDcr2:2014-04-23 09:26:34 [DEBUG]: isakmp_quick.c:1168:quick_r1recv():
04000000 00000000 00000000
2014-04-23 09:26:34 [DEBUG]: isakmp_quick.c:1182:quick_r1recv(): HASH(1) validate:2014-04-23 09:26:34 [DEBUG]: isakmp_quick.c:1183:quick_r1recv():
8f2f2112 97ebccfc 8bb7f2ba 87445d60 58265732 28b21d08 ce030ab3 85120cd5
2014-04-23 09:26:34 [DEBUG]: oakley.c:682:oakley_compute_hash1(): HASH with:
2014-04-23 09:26:34 [DEBUG]: oakley.c:683:oakley_compute_hash1():
041039ca 0a000040 00000001 00000001 00000034 01030401 e1420445 00000028
010c0000 80040001 80010001 80020e10 80010002 00020004 00465000 80050007
80060100 05000018 621d615e 541d371c 3d170ab2 6547fb28 13dd844e 05000010
04000000 00000000 00000000 00000010 04000000 00000000 00000000
2014-04-23 09:26:34 [DEBUG]: algorithm.c:469:alg_oakley_hmacdef(): hmac(hmac_sha2_256)
2014-04-23 09:26:34 [DEBUG]: oakley.c:692:oakley_compute_hash1(): HASH computed:
2014-04-23 09:26:34 [DEBUG]: oakley.c:693:oakley_compute_hash1():
8f2f2112 97ebccfc 8bb7f2ba 87445d60 58265732 28b21d08 ce030ab3 85120cd5
2014-04-23 09:26:34 [DEBUG]: ipsec_doi.c:1299:get_proppair(): total SA len=60
2014-04-23 09:26:34 [DEBUG]: ipsec_doi.c:1300:get_proppair():
00000001 00000001 00000034 01030401 e1420445 00000028 010c0000 80040001
80010001 80020e10 80010002 00020004 00465000 80050007 80060100
2014-04-23 09:26:34 [DEBUG]: ikev1.c:2831:isakmp_parsewoh(): begin.
2014-04-23 09:26:34 [DEBUG]: ikev1.c:2858:isakmp_parsewoh(): seen nptype=2(prop)
2014-04-23 09:26:34 [DEBUG]: ikev1.c:2897:isakmp_parsewoh(): succeed.
2014-04-23 09:26:34 [DEBUG]: ipsec_doi.c:1352:get_proppair(): proposal #1 len=52
2014-04-23 09:26:34 [DEBUG]: ikev1.c:2831:isakmp_parsewoh(): begin.
2014-04-23 09:26:34 [DEBUG]: ikev1.c:2858:isakmp_parsewoh(): seen nptype=3(trns)
2014-04-23 09:26:34 [DEBUG]: ikev1.c:2897:isakmp_parsewoh(): succeed.
2014-04-23 09:26:34 [DEBUG]: ipsec_doi.c:1498:get_transform(): transform #1 len=40
2014-04-23 09:26:34 [DEBUG]: ipsec_doi.c:2297:check_attr_ipsec(): type=Encryption Mode, flag=0x8000, lorv=Tunnel
2014-04-23 09:26:34 [DEBUG]: ipsec_doi.c:2297:check_attr_ipsec(): type=SA Life Type, flag=0x8000, lorv=seconds
2014-04-23 09:26:34 [DEBUG]: ipsec_doi.c:2297:check_attr_ipsec(): type=SA Life Duration, flag=0x8000, lorv=3600
2014-04-23 09:26:34 [DEBUG]: ipsec_doi.c:2412:check_attr_ipsec(): life duration was in TLV.
2014-04-23 09:26:34 [DEBUG]: ipsec_doi.c:2297:check_attr_ipsec(): type=SA Life Type, flag=0x8000, lorv=kilobytes
2014-04-23 09:26:34 [DEBUG]: ipsec_doi.c:2297:check_attr_ipsec(): type=SA Life Duration, flag=0x0000, lorv=4
2014-04-23 09:26:34 [DEBUG]: ipsec_doi.c:2297:check_attr_ipsec(): type=Authentication Algorithm, flag=0x8000, lorv=hmac-sha512
2014-04-23 09:26:34 [DEBUG]: ipsec_doi.c:2297:check_attr_ipsec(): type=Key Length, flag=0x8000, lorv=256
2014-04-23 09:26:34 [DEBUG]: ipsec_doi.c:1395:get_proppair(): pair 1:
2014-04-23 09:26:34 [DEBUG]: proposal.c:1124:print_proppair0(): 0x102acd60: next=(nil) tnext=(nil)
2014-04-23 09:26:34 [DEBUG]: ipsec_doi.c:1430:get_proppair(): proposal #1: 1 transform
2014-04-23 09:26:34 [DEBUG]: ipsec_doi.c:1128:get_ph2approval(): begin compare proposals.
2014-04-23 09:26:34 [DEBUG]: ipsec_doi.c:1134:get_ph2approval(): pair[1]: 0x102acd60
2014-04-23 09:26:34 [DEBUG]: proposal.c:1124:print_proppair0(): 0x102acd60: next=(nil) tnext=(nil)
2014-04-23 09:26:34 [DEBUG]: proposal.c:913:aproppair2saprop(): prop#=1 prot-id=ESP spi-size=4 #trns=1 trns#=1 trns-id=AES
2014-04-23 09:26:34 [DEBUG]: ipsec_doi.c:3941:ipsecdoi_t2satrns(): type=Encryption Mode, flag=0x8000, lorv=Tunnel
2014-04-23 09:26:34 [DEBUG]: ipsec_doi.c:3941:ipsecdoi_t2satrns(): type=SA Life Type, flag=0x8000, lorv=seconds
2014-04-23 09:26:34 [DEBUG]: ipsec_doi.c:3941:ipsecdoi_t2satrns(): type=SA Life Duration, flag=0x8000, lorv=3600
2014-04-23 09:26:34 [DEBUG]: ipsec_doi.c:4002:ipsecdoi_t2satrns(): lifetime 3600 seconds
2014-04-23 09:26:34 [DEBUG]: ipsec_doi.c:3941:ipsecdoi_t2satrns(): type=SA Life Type, flag=0x8000, lorv=kilobytes
2014-04-23 09:26:34 [DEBUG]: ipsec_doi.c:3941:ipsecdoi_t2satrns(): type=SA Life Duration, flag=0x0000, lorv=4
2014-04-23 09:26:34 [DEBUG]: ipsec_doi.c:4023:ipsecdoi_t2satrns(): lifesize 4608000 KB
2014-04-23 09:26:34 [DEBUG]: ipsec_doi.c:3941:ipsecdoi_t2satrns(): type=Authentication Algorithm, flag=0x8000, lorv=hmac-sha512
2014-04-23 09:26:34 [DEBUG]: ipsec_doi.c:3941:ipsecdoi_t2satrns(): type=Key Length, flag=0x8000, lorv=256
2014-04-23 09:26:34 [DEBUG]: ipsec_doi.c:1172:get_ph2approvalx(): peer's single bundle:
2014-04-23 09:26:34 [DEBUG]: proposal.c:1057:printsaproto(): (proto_id=ESP spisize=4 spi=e1420445 spi_p=00000000 encmode=Tunnel reqid=0:0)
2014-04-23 09:26:34 [DEBUG]: proposal.c:1091:printsatrns(): (trns_id=AES encklen=256 authtype=hmac-sha512)
2014-04-23 09:26:34 [DEBUG]: ipsec_doi.c:1175:get_ph2approvalx(): my single bundle:
2014-04-23 09:26:34 [DEBUG]: proposal.c:1057:printsaproto(): (proto_id=ESP spisize=4 spi=00000000 spi_p=00000000 encmode=Tunnel reqid=0:0)
2014-04-23 09:26:34 [DEBUG]: proposal.c:1091:printsatrns(): (trns_id=AES encklen=256 authtype=hmac-sha512)
2014-04-23 09:26:34 [INFO]: proposal.c:280:cmpsaprop_alloc(): use own lifetime: my:600 peer:3600
2014-04-23 09:26:34 [DEBUG]: ipsec_doi.c:1194:get_ph2approvalx(): matched
2014-04-23 09:26:34 [DEBUG]: ikev1.c:1620:isakmp_ph2begin_r(): ===
2014-04-23 09:26:34 [DEBUG]: isakmp_quick.c:1306:quick_r1prep(): pfkey getspi sent.
2014-04-23 09:26:34 [DEBUG]: pfkey.c:696:pk_sendgetspi(): call pfkey_send_getspi
2014-04-23 09:26:34 [DEBUG]: pfkey.c:767:ikev1_getspi_response(): pfkey GETSPI succeeded: ESP/Tunnel 175.141.XX.XX[500]->122.152.XX.XX[500] spi=3482839041(0xcf97e801)
2014-04-23 09:26:34 [DEBUG]: ipsec_doi.c:1299:get_proppair(): total SA len=60
2014-04-23 09:26:34 [DEBUG]: ipsec_doi.c:1300:get_proppair():
00000001 00000001 00000034 01030401 00000000 00000028 010c0000 80040001
80010001 80020e10 80010002 00020004 00465000 80050007 80060100
2014-04-23 09:26:34 [DEBUG]: ikev1.c:2831:isakmp_parsewoh(): begin.
2014-04-23 09:26:34 [DEBUG]: ikev1.c:2858:isakmp_parsewoh(): seen nptype=2(prop)
2014-04-23 09:26:34 [DEBUG]: ikev1.c:2897:isakmp_parsewoh(): succeed.
2014-04-23 09:26:34 [DEBUG]: ipsec_doi.c:1352:get_proppair(): proposal #1 len=52
2014-04-23 09:26:34 [DEBUG]: ikev1.c:2831:isakmp_parsewoh(): begin.
2014-04-23 09:26:34 [DEBUG]: ikev1.c:2858:isakmp_parsewoh(): seen nptype=3(trns)
2014-04-23 09:26:34 [DEBUG]: ikev1.c:2897:isakmp_parsewoh(): succeed.
2014-04-23 09:26:34 [DEBUG]: ipsec_doi.c:1498:get_transform(): transform #1 len=40
2014-04-23 09:26:34 [DEBUG]: ipsec_doi.c:2297:check_attr_ipsec(): type=Encryption Mode, flag=0x8000, lorv=Tunnel
2014-04-23 09:26:34 [DEBUG]: ipsec_doi.c:2297:check_attr_ipsec(): type=SA Life Type, flag=0x8000, lorv=seconds
2014-04-23 09:26:34 [DEBUG]: ipsec_doi.c:2297:check_attr_ipsec(): type=SA Life Duration, flag=0x8000, lorv=3600
2014-04-23 09:26:34 [DEBUG]: ipsec_doi.c:2412:check_attr_ipsec(): life duration was in TLV.
2014-04-23 09:26:34 [DEBUG]: ipsec_doi.c:2297:check_attr_ipsec(): type=SA Life Type, flag=0x8000, lorv=kilobytes
2014-04-23 09:26:34 [DEBUG]: ipsec_doi.c:2297:check_attr_ipsec(): type=SA Life Duration, flag=0x0000, lorv=4
2014-04-23 09:26:34 [DEBUG]: ipsec_doi.c:2297:check_attr_ipsec(): type=Authentication Algorithm, flag=0x8000, lorv=hmac-sha512
2014-04-23 09:26:34 [DEBUG]: ipsec_doi.c:2297:check_attr_ipsec(): type=Key Length, flag=0x8000, lorv=256
2014-04-23 09:26:34 [DEBUG]: ipsec_doi.c:1395:get_proppair(): pair 1:
2014-04-23 09:26:34 [DEBUG]: proposal.c:1124:print_proppair0(): 0x102cd8d0: next=(nil) tnext=(nil)
2014-04-23 09:26:34 [DEBUG]: ipsec_doi.c:1430:get_proppair(): proposal #1: 1 transform
2014-04-23 09:26:34 [DEBUG]: ikev1.c:2248:set_isakmp_payload(): add payload of len 60, next type 10(nonce)
2014-04-23 09:26:34 [DEBUG]: ikev1.c:2248:set_isakmp_payload(): add payload of len 16, next type 5(id)
2014-04-23 09:26:34 [DEBUG]: ikev1.c:2248:set_isakmp_payload(): add payload of len 12, next type 5(id)
2014-04-23 09:26:34 [DEBUG]: ikev1.c:2248:set_isakmp_payload(): add payload of len 12, next type 0(none)
2014-04-23 09:26:34 [DEBUG]: oakley.c:682:oakley_compute_hash1(): HASH with:
2014-04-23 09:26:34 [DEBUG]: oakley.c:683:oakley_compute_hash1():
041039ca 621d615e 541d371c 3d170ab2 6547fb28 13dd844e 0a000040 00000001
00000001 00000034 01030401 cf97e801 00000028 010c0000 80040001 80010001
80020e10 80010002 00020004 00465000 80050007 80060100 05000014 0e239601
9dd029c7 ab0f3134 fc087f12 05000010 04000000 00000000 00000000 0b000010
04000000 00000000 00000000 0000001c 00000001 03046000 cf97e801 80010001
00020004 00000258
2014-04-23 09:26:34 [DEBUG]: algorithm.c:469:alg_oakley_hmacdef(): hmac(hmac_sha2_256)
2014-04-23 09:26:34 [DEBUG]: oakley.c:692:oakley_compute_hash1(): HASH computed:
2014-04-23 09:26:34 [DEBUG]: oakley.c:693:oakley_compute_hash1():
3b0e883c ac097f1b c939707a 6c771cf9 19f23998 8fb6fa7d a5a89423 7da2925f
2014-04-23 09:26:34 [DEBUG]: ikev1.c:2248:set_isakmp_payload(): add payload of len 32, next type 1(sa)
2014-04-23 09:26:34 [DEBUG]: oakley.c:3234:oakley_do_encrypt(): begin encryption.
2014-04-23 09:26:34 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-04-23 09:26:34 [DEBUG]: oakley.c:3250:oakley_do_encrypt(): pad length = 12
2014-04-23 09:26:34 [DEBUG]: oakley.c:3280:oakley_do_encrypt():
01000024 3b0e883c ac097f1b c939707a 6c771cf9 19f23998 8fb6fa7d a5a89423
7da2925f 0a000040 00000001 00000001 00000034 01030401 cf97e801 00000028
010c0000 80040001 80010001 80020e10 80010002 00020004 00465000 80050007
80060100 05000014 0e239601 9dd029c7 ab0f3134 fc087f12 05000010 04000000
00000000 00000000 0b000010 04000000 00000000 00000000 0000001c 00000001
03046000 cf97e801 80010001 00020004 00000258 dc428e94 953c2df4 2818380c
2014-04-23 09:26:34 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-04-23 09:26:34 [DEBUG]: oakley.c:3290:oakley_do_encrypt(): with key:
2014-04-23 09:26:34 [DEBUG]: oakley.c:3291:oakley_do_encrypt():
631a6335 2240d720 6e3977af 7383dd84 ef01871f 7d19c621 24d1228f 20966358
2014-04-23 09:26:34 [DEBUG]: oakley.c:3296:oakley_do_encrypt(): encrypted payload by IV:
2014-04-23 09:26:34 [DEBUG]: oakley.c:3297:oakley_do_encrypt():
b766c104 93fe8817 213720e0 a71afef3
2014-04-23 09:26:34 [DEBUG]: oakley.c:3303:oakley_do_encrypt(): save IV for next:
2014-04-23 09:26:34 [DEBUG]: oakley.c:3304:oakley_do_encrypt():
7281c0f6 4693c688 7fcd7db2 e62f9726
2014-04-23 09:26:34 [DEBUG]: oakley.c:3320:oakley_do_encrypt(): encrypted.
2014-04-23 09:26:34 [DEBUG]: ikev1.c:1747:isakmp_ph2resend(): resend phase2 packet e83fbd854cba7233:621245d315bd2379:041039CA
2014-04-23 09:26:34 [DEBUG]: ikev1.c:2978:isakmp_send(): 220 bytes from 122.152.XX.XX[500] to 175.141.XX.XX[500]
2014-04-23 09:26:34 [DEBUG]: sockmisc.c:335:sendfromto(): sockname 122.152.XX.XX[500]
2014-04-23 09:26:34 [DEBUG]: sockmisc.c:337:sendfromto(): send packet from 122.152.XX.XX[500]
2014-04-23 09:26:34 [DEBUG]: sockmisc.c:339:sendfromto(): send packet to 175.141.XX.XX[500]
2014-04-23 09:26:34 [DEBUG]: sockmisc.c:524:sendfromto(): 1 times of 220 bytes message will be sent to 175.141.XX.XX[500]
2014-04-23 09:26:34 [DEBUG]: sockmisc.c:528:sendfromto():
e83fbd85 4cba7233 621245d3 15bd2379 08102001 041039ca 000000dc 771b3ef2
f1eaa817 032b829b 8d4b7d45 8de13b4a 211903f5 2a501cbe 5a358da7 2326e527
f0244f7a 5d250e79 2951d1c3 0f0a1abe b843adc3 129bafb2 18db814d 92c6cb2f
611c50a3 df8a9296 69fed85d 173c51ec df35a5f7 96b7e59c 16ec604f d1b67a94
2a7b8ca8 aadeaadb e559b930 0fd5ae76 3f5d0836 19555c8d 1d9965a1 d278519f
1e8c2059 97677ecb b5e0e52b 7c5d4536 c06136e4 a1983353 2a179506 27bc253b
40e635b5 bb4ffaa1 a67391fb 7281c0f6 4693c688 7fcd7db2 e62f9726
2014-04-23 09:26:34 [DEBUG]: pfkey.c:722:pk_sendgetspi(): pfkey GETSPI sent: ESP/Tunnel 0.0.0.0[500]->122.152.XX.XX[500]
2014-04-23 09:26:34 [DEBUG]: isakmp.c:944:isakmp_handler(): ===
2014-04-23 09:26:34 [DEBUG]: isakmp.c:945:isakmp_handler(): 76 bytes message received from 175.141.XX.XX[500]
2014-04-23 09:26:34 [DEBUG]: isakmp.c:948:isakmp_handler():
e83fbd85 4cba7233 621245d3 15bd2379 08102001 041039ca 0000004c aa2c9411
55b6332c a10fa6d6 74ff81f6 e5fb06a3 03fce8aa f355b5a5 f3750e6f d6ef8b4d
fe2936e9 4781b5df 779c7239
2014-04-23 09:26:34 [DEBUG]: oakley.c:3109:oakley_do_decrypt(): begin decryption.
2014-04-23 09:26:34 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-04-23 09:26:34 [DEBUG]: oakley.c:3123:oakley_do_decrypt(): IV was saved for next processing:
2014-04-23 09:26:34 [DEBUG]: oakley.c:3125:oakley_do_decrypt():
d6ef8b4d fe2936e9 4781b5df 779c7239
2014-04-23 09:26:34 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-04-23 09:26:34 [DEBUG]: oakley.c:3148:oakley_do_decrypt(): with key:
2014-04-23 09:26:34 [DEBUG]: oakley.c:3149:oakley_do_decrypt():
631a6335 2240d720 6e3977af 7383dd84 ef01871f 7d19c621 24d1228f 20966358
2014-04-23 09:26:34 [DEBUG]: oakley.c:3154:oakley_do_decrypt(): decrypted payload by IV:
2014-04-23 09:26:34 [DEBUG]: oakley.c:3155:oakley_do_decrypt():
7281c0f6 4693c688 7fcd7db2 e62f9726
2014-04-23 09:26:34 [DEBUG]: oakley.c:3157:oakley_do_decrypt(): decrypted payload, but not trimed.
2014-04-23 09:26:34 [DEBUG]: oakley.c:3159:oakley_do_decrypt():
00000024 6e192dc5 4e62a50c 917574f6 29fbbe42 02271fa2 a8a379bb ede9f130
9e3590c4 00000000 00000000 00000000
2014-04-23 09:26:34 [DEBUG]: oakley.c:3168:oakley_do_decrypt(): padding len=0
2014-04-23 09:26:34 [DEBUG]: oakley.c:3199:oakley_do_decrypt(): decrypted.
2014-04-23 09:26:34 [DEBUG]: oakley.c:3200:oakley_do_decrypt():
e83fbd85 4cba7233 621245d3 15bd2379 08102001 041039ca 0000004c 00000024
6e192dc5 4e62a50c 917574f6 29fbbe42 02271fa2 a8a379bb ede9f130 9e3590c4
00000000 00000000 00000000
2014-04-23 09:26:34 [DEBUG]: ikev1.c:2831:isakmp_parsewoh(): begin.
2014-04-23 09:26:34 [DEBUG]: ikev1.c:2858:isakmp_parsewoh(): seen nptype=8(hash)
2014-04-23 09:26:34 [DEBUG]: ikev1.c:2897:isakmp_parsewoh(): succeed.
2014-04-23 09:26:34 [DEBUG]: isakmp_quick.c:1604:quick_r3recv(): HASH(3) validate:2014-04-23 09:26:34 [DEBUG]: isakmp_quick.c:1605:quick_r3recv():
6e192dc5 4e62a50c 917574f6 29fbbe42 02271fa2 a8a379bb ede9f130 9e3590c4
2014-04-23 09:26:34 [DEBUG]: oakley.c:626:oakley_compute_hash3(): HASH with:
2014-04-23 09:26:34 [DEBUG]: oakley.c:627:oakley_compute_hash3():
00041039 ca621d61 5e541d37 1c3d170a b26547fb 2813dd84 4e0e2396 019dd029
c7ab0f31 34fc087f 12
2014-04-23 09:26:34 [DEBUG]: algorithm.c:469:alg_oakley_hmacdef(): hmac(hmac_sha2_256)
2014-04-23 09:26:34 [DEBUG]: oakley.c:636:oakley_compute_hash3(): HASH computed:
2014-04-23 09:26:34 [DEBUG]: oakley.c:637:oakley_compute_hash3():
6e192dc5 4e62a50c 917574f6 29fbbe42 02271fa2 a8a379bb ede9f130 9e3590c4
2014-04-23 09:26:34 [DEBUG]: ikev1.c:1132:quick_main(): ===
2014-04-23 09:26:34 [DEBUG]: oakley.c:391:oakley_compute_keymat_x(): KEYMAT compute with
2014-04-23 09:26:34 [DEBUG]: oakley.c:392:oakley_compute_keymat_x():
03cf97e8 01621d61 5e541d37 1c3d170a b26547fb 2813dd84 4e0e2396 019dd029
c7ab0f31 34fc087f 12
2014-04-23 09:26:34 [DEBUG]: algorithm.c:469:alg_oakley_hmacdef(): hmac(hmac_sha2_256)
2014-04-23 09:26:34 [DEBUG]: algorithm.c:669:alg_ipsec_encdef(): encryption(aes)
2014-04-23 09:26:34 [DEBUG]: algorithm.c:712:alg_ipsec_hmacdef(): hmac(null)
2014-04-23 09:26:34 [DEBUG]: oakley.c:424:oakley_compute_keymat_x(): encklen=256 authklen=512
2014-04-23 09:26:34 [DEBUG]: oakley.c:431:oakley_compute_keymat_x(): generating 1280 bits of key (dupkeymat=5)
2014-04-23 09:26:34 [DEBUG]: oakley.c:449:oakley_compute_keymat_x(): generating K1...K5 for KEYMAT.
2014-04-23 09:26:34 [DEBUG]: algorithm.c:469:alg_oakley_hmacdef(): hmac(hmac_sha2_256)
2014-04-23 09:26:34 [DEBUG]: algorithm.c:469:alg_oakley_hmacdef(): hmac(hmac_sha2_256)
2014-04-23 09:26:34 [DEBUG]: algorithm.c:469:alg_oakley_hmacdef(): hmac(hmac_sha2_256)
2014-04-23 09:26:34 [DEBUG]: algorithm.c:469:alg_oakley_hmacdef(): hmac(hmac_sha2_256)
2014-04-23 09:26:34 [DEBUG]: oakley.c:510:oakley_compute_keymat_x():
77934fc5 441e36f6 37940d8e 55e856d3 198b48a5 9401dddf cc29f787 84cad844
de154d3c 6bbe65f7 c3423e6b 9fc115d0 7aa5c9ba 566b32dc d303adc2 a45267c5
e28a306a 2e68b2c0 2515af02 f7f98da2 e767dec1 c2fc4938 328aa60d af9df7a6
332d85cd c04a7a4f 7f52c2e2 97eab879 dfc0d230 23a2cafd 11b0480a f635dc52
0a08e51c 9ee9c263 4445660c 239ea482 94023826 58e2074d 3850e3d4 3e29703a
2014-04-23 09:26:34 [DEBUG]: oakley.c:391:oakley_compute_keymat_x(): KEYMAT compute with
2014-04-23 09:26:34 [DEBUG]: oakley.c:392:oakley_compute_keymat_x():
03e14204 45621d61 5e541d37 1c3d170a b26547fb 2813dd84 4e0e2396 019dd029
c7ab0f31 34fc087f 12
2014-04-23 09:26:34 [DEBUG]: algorithm.c:469:alg_oakley_hmacdef(): hmac(hmac_sha2_256)
2014-04-23 09:26:34 [DEBUG]: algorithm.c:669:alg_ipsec_encdef(): encryption(aes)
2014-04-23 09:26:34 [DEBUG]: algorithm.c:712:alg_ipsec_hmacdef(): hmac(null)
2014-04-23 09:26:34 [DEBUG]: oakley.c:424:oakley_compute_keymat_x(): encklen=256 authklen=512
2014-04-23 09:26:34 [DEBUG]: oakley.c:431:oakley_compute_keymat_x(): generating 1280 bits of key (dupkeymat=5)
2014-04-23 09:26:34 [DEBUG]: oakley.c:449:oakley_compute_keymat_x(): generating K1...K5 for KEYMAT.
2014-04-23 09:26:34 [DEBUG]: algorithm.c:469:alg_oakley_hmacdef(): hmac(hmac_sha2_256)
2014-04-23 09:26:34 [DEBUG]: algorithm.c:469:alg_oakley_hmacdef(): hmac(hmac_sha2_256)
2014-04-23 09:26:34 [DEBUG]: algorithm.c:469:alg_oakley_hmacdef(): hmac(hmac_sha2_256)
2014-04-23 09:26:34 [DEBUG]: algorithm.c:469:alg_oakley_hmacdef(): hmac(hmac_sha2_256)
2014-04-23 09:26:34 [DEBUG]: oakley.c:510:oakley_compute_keymat_x():
b79d3e82 ef40040d aad0c7d3 89f85734 1f357258 c94da1e0 7064d5d2 f8bc99f7
a8ba1a1b 67597336 ae1f173f 6493e50f 17d20f06 2e4b0654 bdf20469 38373a5e
857edaff 4a27c1c7 bebb3ba1 c103fe36 44ee89f8 72709ccc d08b91f9 54a37e7e
669a0869 cea61809 5e32cff8 77e6165e e4f26981 80c462b2 a834e689 9aea805b
633c882d dddb713e 144be46e 3886dfc3 b93fff67 11ed08d9 daf7ceef 1984269f
2014-04-23 09:26:34 [DEBUG]: oakley.c:319:oakley_compute_keymat(): KEYMAT computed.
2014-04-23 09:26:34 [PROTO_NOTIFY]: ikev1.c:2548:log_ph2established(): ====> PHASE-2 NEGOTIATION SUCCEEDED AS RESPONDER, (QUICK MODE) <====
====> Established SA: 122.152.XX.XX[500]-175.141.XX.XX[500] message id:0x041039CA, SPI:0xCF97E801/0xE1420445 <====
2014-04-23 09:26:34 [DEBUG]: isakmp_quick.c:1824:quick_r3prep(): call pk_sendupdate
2014-04-23 09:26:34 [DEBUG]: algorithm.c:669:alg_ipsec_encdef(): encryption(aes)
2014-04-23 09:26:34 [DEBUG]: algorithm.c:712:alg_ipsec_hmacdef(): hmac(null)
2014-04-23 09:26:34 [INFO]: ike_pfkey.c:339:sadb_log_add(): SADB_UPDATE ul_proto=255 src=175.141.XX.XX[500] dst=122.152.XX.XX[500] satype=ESP samode=tunl spi=0xCF97E801 authtype=SHA512 enctype=AES256 lifetime soft time=600 bytes=47185
92000 hard time=600 bytes=4718592000
2014-04-23 09:26:34 [DEBUG]: isakmp_quick.c:1829:quick_r3prep(): pfkey update sent.
2014-04-23 09:26:34 [DEBUG]: algorithm.c:669:alg_ipsec_encdef(): encryption(aes)
2014-04-23 09:26:34 [DEBUG]: algorithm.c:712:alg_ipsec_hmacdef(): hmac(null)
2014-04-23 09:26:34 [INFO]: ike_pfkey.c:339:sadb_log_add(): SADB_ADD ul_proto=255 src=122.152.XX.XX[500] dst=175.141.XX.XX[500] satype=ESP samode=tunl spi=0xE1420445 authtype=SHA512 enctype=AES256 lifetime soft time=600 bytes=47185920
00 hard time=600 bytes=4718592000
Apr 23 09:26:34 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keymirror_add
2014-04-23 09:26:34 [DEBUG]: pfkey.c:1182:ikev1_update_response(): pfkey UPDATE succeeded: ESP/Tunnel 175.141.XX.XX[500]->122.152.XX.XX[500] spi=3482839041(0xcf97e801)
2014-04-23 09:26:34 [INFO]: pfkey.c:1187:ikev1_update_response(): IPsec-SA established: ESP/Tunnel 175.141.XX.XX[500]->122.152.XX.XX[500] spi=3482839041(0xcf97e801)
2014-04-23 09:26:34 [PROTO_NOTIFY]: ikev1.c:2597:log_ipseckeyinstalled(): ====> IPSEC KEY INSTALLATION SUCCEEDED <====
====> Installed SA: 122.152.XX.XX[500]-175.141.XX.XX[500] SPI:0xCF97E801/0xE1420445 lifetime 600 Sec lifesize 4608000 KB <====
2014-04-23 09:26:34 [DEBUG]: isakmp_quick.c:1836:quick_r3prep(): pfkey add sent.
Apr 23 09:26:34 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 4
Apr 23 09:26:34 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keymirror_add
2014-04-23 09:26:34 [INFO]: keymgr_keymirror.c:83:ike_do_keymirror_add(): keymirror add start ++++++++++++++++
Apr 23 09:26:34 keymgr_keydb_insert(ikemgr/keymgr_db.c:108): keymgr: key insert called for tid:8
2014-04-23 09:26:34 [INFO]: keymgr_keymirror.c:87:ike_do_keymirror_add(): keymirror add for gw 7, tn 8, selfSPI CF97E801, retcode 0.
Apr 23 09:26:35 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keymirror_del
Apr 23 09:26:35 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 5
Apr 23 09:26:35 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keymirror_del
2014-04-23 09:26:35 [INFO]: keymgr_keymirror.c:125:ike_do_keymirror_del(): keymirror del start ----------------
2014-04-23 09:26:35 [INFO]: keymgr_keymirror.c:130:ike_do_keymirror_del(): keymirror del for gw 7, tn 8, selfSPI B8739224, retcode 0.
2014-04-23 09:26:35 [DEBUG]: handler.c:1666:remove_ph2(): Deleting a Ph2... status 9
2014-04-23 09:26:35 [DEBUG]: oakley.c:3028:oakley_newiv2(): compute IV for phase2
2014-04-23 09:26:35 [DEBUG]: oakley.c:3029:oakley_newiv2(): phase1 last IV:
2014-04-23 09:26:35 [DEBUG]: oakley.c:3030:oakley_newiv2():
01b02da7 af7ffffd 159c73f7 00c1a160 dc7bf457
2014-04-23 09:26:35 [DEBUG]: algorithm.c:386:alg_oakley_hashdef(): hash(sha256)
2014-04-23 09:26:35 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-04-23 09:26:35 [DEBUG]: oakley.c:3063:oakley_newiv2(): phase2 IV computed:
2014-04-23 09:26:35 [DEBUG]: oakley.c:3064:oakley_newiv2():
ee16e16e c809f012 0a317bac ef2a3e60
2014-04-23 09:26:35 [DEBUG]: oakley.c:682:oakley_compute_hash1(): HASH with:
2014-04-23 09:26:35 [DEBUG]: oakley.c:683:oakley_compute_hash1():
dc7bf457 00000010 00000001 03040001 b8739224
2014-04-23 09:26:35 [DEBUG]: algorithm.c:469:alg_oakley_hmacdef(): hmac(hmac_sha2_256)
2014-04-23 09:26:35 [DEBUG]: oakley.c:692:oakley_compute_hash1(): HASH computed:
2014-04-23 09:26:35 [DEBUG]: oakley.c:693:oakley_compute_hash1():
a860956d 27b26484 681ec5fa cf077743 87a5fee6 b2f0be10 c5db9fd2 de8db97f
2014-04-23 09:26:35 [DEBUG]: oakley.c:3234:oakley_do_encrypt(): begin encryption.
2014-04-23 09:26:35 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-04-23 09:26:35 [DEBUG]: oakley.c:3250:oakley_do_encrypt(): pad length = 12
2014-04-23 09:26:35 [DEBUG]: oakley.c:3280:oakley_do_encrypt():
0c000024 a860956d 27b26484 681ec5fa cf077743 87a5fee6 b2f0be10 c5db9fd2
de8db97f 00000010 00000001 03040001 b8739224 11680afe 20be0173 413f5c0c
2014-04-23 09:26:35 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-04-23 09:26:35 [DEBUG]: oakley.c:3290:oakley_do_encrypt(): with key:
2014-04-23 09:26:35 [DEBUG]: oakley.c:3291:oakley_do_encrypt():
631a6335 2240d720 6e3977af 7383dd84 ef01871f 7d19c621 24d1228f 20966358
2014-04-23 09:26:35 [DEBUG]: oakley.c:3296:oakley_do_encrypt(): encrypted payload by IV:
2014-04-23 09:26:35 [DEBUG]: oakley.c:3297:oakley_do_encrypt():
ee16e16e c809f012 0a317bac ef2a3e60
2014-04-23 09:26:35 [DEBUG]: oakley.c:3303:oakley_do_encrypt(): save IV for next:
2014-04-23 09:26:35 [DEBUG]: oakley.c:3304:oakley_do_encrypt():
dd450156 6801495d f70b28e2 e87d385c
2014-04-23 09:26:35 [DEBUG]: oakley.c:3320:oakley_do_encrypt(): encrypted.
2014-04-23 09:26:35 [DEBUG]: ikev1.c:2978:isakmp_send(): 92 bytes from 122.152.XX.XX[500] to 175.141.XX.XX[500]
2014-04-23 09:26:35 [DEBUG]: sockmisc.c:335:sendfromto(): sockname 122.152.XX.XX[500]
2014-04-23 09:26:35 [DEBUG]: sockmisc.c:337:sendfromto(): send packet from 122.152.XX.XX[500]
2014-04-23 09:26:35 [DEBUG]: sockmisc.c:339:sendfromto(): send packet to 175.141.XX.XX[500]
2014-04-23 09:26:35 [DEBUG]: sockmisc.c:524:sendfromto(): 1 times of 92 bytes message will be sent to 175.141.XX.XX[500]
2014-04-23 09:26:35 [DEBUG]: sockmisc.c:528:sendfromto():
e83fbd85 4cba7233 621245d3 15bd2379 08100501 dc7bf457 0000005c 8a46b387
cec45d68 cff04fbd 02d2055f 0509affc a083873f e3fb00a1 1c6c90e2 c5ae24fe
bc30ed8a 550a8d19 420fdbf8 dd450156 6801495d f70b28e2 e87d385c
2014-04-23 09:26:35 [DEBUG]: isakmp_inf.c:805:isakmp_info_send_common(): sendto Information delete.
2014-04-23 09:26:35 [DEBUG]: oakley.c:3088:oakley_delivm(): IV freed
2014-04-23 09:26:35 [PROTO_NOTIFY]: ikev1.c:2620:log_ipseckeydeleted(): ====> IPSEC KEY DELETED <====
====> Deleted SA: 122.152.XX.XX[500]-175.141.XX.XX[500] SPI:0xB8739224/0x33DAADA8 <====
2014-04-23 09:26:35 [INFO]: ike_pfkey.c:446:sadb_delete(): SADB_DELETE ul_proto=0 src=122.152.XX.XX[500] dst=175.141.XX.XX[500] satype=ESP spi=0xB8739224
2014-04-23 09:26:35 [INFO]: ike_pfkey.c:693:sadb_delete_callback(): received PFKEY_DELETE seq=0 satype=ESP spi=0xB8739224
2014-04-23 09:26:35 [DEBUG]: oakley.c:3088:oakley_delivm(): IV freed
Apr 23 09:26:36 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:26:36 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:26:36 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:26:36 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:26:36 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:26:36 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:26:36 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:26:36 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:26:36 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:26:36 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:26:40 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:26:40 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:26:40 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:26:40 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:26:40 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
2014-04-23 09:26:40 [DEBUG]: ikev1_natt.c:348:natt_keepalive_send(): KA: 122.152.XX.XX[4500]->195.243.XX.XX[4500]
2014-04-23 09:26:40 [DEBUG]: sockmisc.c:335:sendfromto(): sockname 122.152.XX.XX[4500]
2014-04-23 09:26:40 [DEBUG]: sockmisc.c:337:sendfromto(): send packet from 122.152.XX.XX[4500]
2014-04-23 09:26:40 [DEBUG]: sockmisc.c:339:sendfromto(): send packet to 195.243.XX.XX[4500]
2014-04-23 09:26:40 [DEBUG]: sockmisc.c:524:sendfromto(): 1 times of 1 bytes message will be sent to 195.243.XX.XX[4500]
2014-04-23 09:26:40 [DEBUG]: sockmisc.c:528:sendfromto():
ff
Apr 23 09:26:40 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:26:40 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:26:40 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:26:40 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:26:40 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:26:44 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:26:44 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:26:44 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:26:44 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:26:44 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:26:44 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:26:44 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:26:44 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:26:44 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:26:44 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:26:48 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:26:48 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:26:48 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:26:48 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:26:48 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:26:48 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:26:48 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:26:48 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:26:48 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:26:48 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:26:52 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:26:52 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:26:52 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:26:52 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:26:52 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:26:52 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:26:52 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:26:52 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:26:52 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:26:52 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:26:57 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:26:57 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:26:57 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:26:57 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:26:57 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:26:57 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:26:57 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:26:57 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:26:57 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:26:57 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
2014-04-23 09:27:00 [DEBUG]: ikev1_natt.c:348:natt_keepalive_send(): KA: 122.152.XX.XX[4500]->195.243.XX.XX[4500]
2014-04-23 09:27:00 [DEBUG]: sockmisc.c:335:sendfromto(): sockname 122.152.XX.XX[4500]
2014-04-23 09:27:00 [DEBUG]: sockmisc.c:337:sendfromto(): send packet from 122.152.XX.XX[4500]
2014-04-23 09:27:00 [DEBUG]: sockmisc.c:339:sendfromto(): send packet to 195.243.XX.XX[4500]
2014-04-23 09:27:00 [DEBUG]: sockmisc.c:524:sendfromto(): 1 times of 1 bytes message will be sent to 195.243.XX.XX[4500]
2014-04-23 09:27:00 [DEBUG]: sockmisc.c:528:sendfromto():
ff
Apr 23 09:27:01 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:27:01 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:27:01 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:27:01 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:27:01 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:27:01 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:27:01 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:27:01 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:27:01 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:27:01 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:27:06 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:27:06 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:27:06 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:27:06 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:27:06 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:27:06 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:27:06 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:27:06 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:27:06 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:27:06 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:27:10 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:27:10 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:27:10 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:27:10 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:27:10 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:27:10 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:27:10 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:27:10 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:27:10 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL-OSPF-Router(Gateway-MEL-OSPF-Router)_out
2014-04-23 09:27:10 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
Apr 23 09:27:16 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:27:16 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:27:16 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
2014-04-23 09:27:16 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB-ACobiac(Gateway-BDB-ACobiac)_out
2014-04-23 09:27:16 [INFO]: ikev1.c:706:ikev1_initiate(): 0:122.152.XX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
Apr 23 09:27:16 ifmon_request_put(daemon/panike_sysd_if.c:860): 16 write to pipe: keyacquire
Apr 23 09:27:16 ifmon_request_get(daemon/panike_sysd_if.c:876): 16 read from pipe, msg type 3
Apr 23 09:27:16 pan_msg_process(daemon/panike_sysd_if.c:974): request from pipe: keyacquire
Hope you can help us. Thanks in advance.
- Labels:
-
Configuration
-
Networking
-
Troubleshooting
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-23-2014 02:07 AM
This could be an issue
remote Gateway-BDB-ACobiac passive mode specified for IKEv1, dropping acquire request
remote Gateway-MEL-OSPF-Router passive mode specified for IKEv1, dropping acquire request
It seems they are configured for passive mode only. Any specific reason for that ?
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-23-2014 07:01 AM
The PA is the passive site and normally the Cisco site is the active site.
May we did a misconfiguration at Cisco site. So you think the Cisco Site is configured in passive mode? If yes, you know how to change it?
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-23-2014 07:15 AM
Can you provide a screenshot of your PAN IKE Gateway Profile (showing advanced options) ?
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-23-2014 07:41 AM
Hello Hithead,
From the above screenshot, it looks like the other end device is having dynamic address, hence the other end device should be always a "INITIATOR" for VPN tunnel. It should not be a set as "RESPONDER" ( Passive mode).
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-23-2014 08:05 AM
okay, nice to know.
But do you have a idea what can this cause? Or do you know how to fix the remote site (Cisco) to be the initiator?
Here is a screenshot of my ike crypto profile:
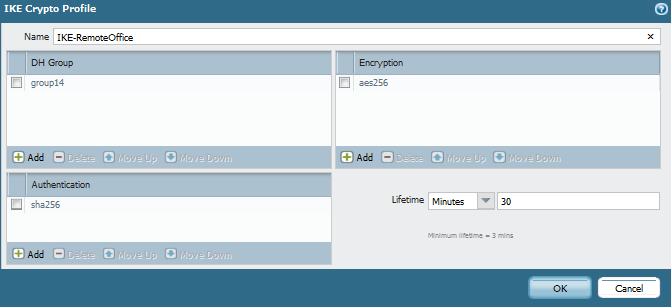
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-23-2014 08:09 AM
Since you are passive the remote side is already the initiator, otherwise there would never be a tunnel...
2014-04-23 09:22:04 [PROTO_NOTIFY]: ikev1.c:2446:log_ph1established(): ====> PHASE-1 NEGOTIATION SUCCEEDED AS RESPONDER, AGGRESSIVE MODE <====
From the debug logs you have provided one can see the lifetime was set to 600 Sec. Did you change that in the meantime ?
2014-04-23 09:26:34 [INFO]: proposal.c:280:cmpsaprop_alloc(): use own lifetime: my:600 peer:3600
====> Installed SA: 122.152.XX.XX[500]-175.141.XX.XX[500] SPI:0xCF97E801/0xE1420445 lifetime 600 Sec lifesize 4608000 KB <====
The tunnel expired every 600 Secs. and the Cisco needed to reestablish the tunnel every 600 Sec..... Not ideal I would say. Change it to 3600 Secs.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-23-2014 08:22 AM
IKE phase-I lifetime is not an essential parameter need to be match on both sides. During Phase-I negotiation, it will choose the lower value to established the tunnel.
But, as GAFROL said, it would not be a recomended setiings.
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-23-2014 10:45 PM
Hithead,
The default behavior of the Cisco ASA when there is no traffic to send through the VPN tunnel is to bring down the tunnel: please take a look at this document. IPSEC VPN Timeout Issue between Cisco ASA Router and Palo Alto Networks Firewall.
https://live.paloaltonetworks.com/docs/DOC-1675
Regards,
Gerard
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-23-2014 11:30 PM
hi all,
thank you all for your help. We don't have a Cisco ASA. Its a Cisco 871 Router per default. But lets see, may we can find a idle timeout setting on this device.
So I will first change the lifetime settings and check wherever I can set the idle time out. Will report the result.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-23-2014 11:48 PM
Hello, maybe this helps you for your cisco device:
Configuring the IPSec SA Idle Timer Globally
To configure the IPSec SA idle timer globally, enter the crypto ipsec security-association idle-time command in global configuration mode as follows: Router(config)# crypto ipsec security-association idle-time seconds
In this command, seconds specifies the time, in seconds, that the idle timer will allow an inactive peer to maintain an SA. Valid values range from 60 to 86400.
Configuring the IPSec SA Idle Timer per Crypto Map
To configure the IPSec SA idle timer for a specified crypto map, use the set security-association idle-time command within a crypto map configuration beginning in global configuration mode:
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-27-2014 05:44 AM
hi I'm again,
sorry for the delayed response (was busy with other projects).
The config you gave me helped us a little more. thank you all.
The outages are not more so often than before. But still happen sometimes. Would you please so kind and help me to identify the problem?
Here a example of two tunnels:
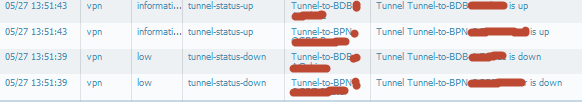
2014-05-27 13:51:00.083 +0200 debug: ifmon_request_put(daemon/panike_sysd_if.c:916): 16 write to pipe: keyacquire
2014-05-27 13:51:00.083 +0200 debug: ifmon_request_get(daemon/panike_sysd_if.c:932): 16 read from pipe, msg type 3
2014-05-27 13:51:00.083 +0200 debug: pan_msg_process(daemon/panike_sysd_if.c:1030): request from pipe: keyacquire
2014-05-27 13:51:00 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL1A(Gateway-MEL1A)_out
2014-05-27 13:51:00 [INFO]: ikev1.c:710:ikev1_initiate(): 0:122.152.XXX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL1A passive mode specified for IKEv1, dropping acquire request
2014-05-27 13:51:04.083 +0200 debug: ifmon_request_put(daemon/panike_sysd_if.c:916): 16 write to pipe: keyacquire
2014-05-27 13:51:04.083 +0200 debug: ifmon_request_get(daemon/panike_sysd_if.c:932): 16 read from pipe, msg type 3
2014-05-27 13:51:04.083 +0200 debug: pan_msg_process(daemon/panike_sysd_if.c:1030): request from pipe: keyacquire
2014-05-27 13:51:04 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL1A(Gateway-MEL1A)_out
2014-05-27 13:51:04 [INFO]: ikev1.c:710:ikev1_initiate(): 0:122.152.XXX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL1A passive mode specified for IKEv1, dropping acquire request
2014-05-27 13:51:08.083 +0200 debug: ifmon_request_put(daemon/panike_sysd_if.c:916): 16 write to pipe: keyacquire
2014-05-27 13:51:08.083 +0200 debug: ifmon_request_get(daemon/panike_sysd_if.c:932): 16 read from pipe, msg type 3
2014-05-27 13:51:08.083 +0200 debug: pan_msg_process(daemon/panike_sysd_if.c:1030): request from pipe: keyacquire
2014-05-27 13:51:08 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL1A(Gateway-MEL1A)_out
2014-05-27 13:51:08 [INFO]: ikev1.c:710:ikev1_initiate(): 0:122.152.XXX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL1A passive mode specified for IKEv1, dropping acquire request
2014-05-27 13:51:11 [DEBUG]: isakmp.c:982:isakmp_handler(): ===
2014-05-27 13:51:11 [DEBUG]: isakmp.c:983:isakmp_handler(): 140 bytes message received from 165.228.XXX.XXX[500]
2014-05-27 13:51:11 [DEBUG]: isakmp.c:986:isakmp_handler():
b6e8816f 09c21be4 50cce73b 3460ab8a 08100501 f9b31c8b 0000008c 9941a48b
f8f6e4fc 80a16d47 54b041f9 3623576b b9527c0b 1a5bbb8c 5829c7ba c8533b3b
0434b298 3accbb6a aa199fb9 91131da9 6498556b 2b000f59 3df2ab3c 87d2e4d1
98a75664 cd72eb33 c1afe678 c2c6a153 f80bbb3f 3ba63935 8b68b669 f386a647
b126020d f3819408 6f47de3d
2014-05-27 13:51:11 [DEBUG]: isakmp_inf.c:147:isakmp_info_recv(): receive Information.
2014-05-27 13:51:11 [DEBUG]: oakley.c:3811:oakley_newiv2(): compute IV for phase2
2014-05-27 13:51:11 [DEBUG]: oakley.c:3812:oakley_newiv2(): phase1 last IV:
2014-05-27 13:51:11 [DEBUG]: oakley.c:3813:oakley_newiv2():
7af22e17 a3c0ea53 db5a6e97 88e563f3 f9b31c8b
2014-05-27 13:51:11 [DEBUG]: algorithm.c:386:alg_oakley_hashdef(): hash(sha512)
2014-05-27 13:51:11 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-05-27 13:51:11 [DEBUG]: oakley.c:3846:oakley_newiv2(): phase2 IV computed:
2014-05-27 13:51:11 [DEBUG]: oakley.c:3847:oakley_newiv2():
e2d2c6dc edb2254f f4a5d69c c7bb329d
2014-05-27 13:51:11 [DEBUG]: oakley.c:3892:oakley_do_decrypt(): begin decryption.
2014-05-27 13:51:11 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-05-27 13:51:11 [DEBUG]: oakley.c:3906:oakley_do_decrypt(): IV was saved for next processing:
2014-05-27 13:51:11 [DEBUG]: oakley.c:3908:oakley_do_decrypt():
f386a647 b126020d f3819408 6f47de3d
2014-05-27 13:51:11 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-05-27 13:51:11 [DEBUG]: oakley.c:3931:oakley_do_decrypt(): with key:
2014-05-27 13:51:11 [DEBUG]: oakley.c:3932:oakley_do_decrypt():
d3afb025 07033c6c efa1e863 b4640243 e0b57508 bc394080 b1d13a42 7c271880
2014-05-27 13:51:11 [DEBUG]: oakley.c:3937:oakley_do_decrypt(): decrypted payload by IV:
2014-05-27 13:51:11 [DEBUG]: oakley.c:3938:oakley_do_decrypt():
e2d2c6dc edb2254f f4a5d69c c7bb329d
2014-05-27 13:51:11 [DEBUG]: oakley.c:3940:oakley_do_decrypt(): decrypted payload, but not trimed.
2014-05-27 13:51:11 [DEBUG]: oakley.c:3942:oakley_do_decrypt():
0b000044 dea2d538 75fefdf4 793a440e ed624add 58bcc605 8687be48 5b62388d
395038fd 9272e584 2845d20a e35d406b f08b29d4 76f2ee39 942f35ae 3431bfc3
bfc16856 00000020 00000001 01108d28 b6e8816f 09c21be4 50cce73b 3460ab8a
712c11c8 00000000 00000000 00000000
2014-05-27 13:51:11 [DEBUG]: oakley.c:3951:oakley_do_decrypt(): padding len=0
2014-05-27 13:51:11 [DEBUG]: oakley.c:3982:oakley_do_decrypt(): decrypted.
2014-05-27 13:51:11 [DEBUG]: oakley.c:3983:oakley_do_decrypt():
b6e8816f 09c21be4 50cce73b 3460ab8a 08100501 f9b31c8b 0000008c 0b000044
dea2d538 75fefdf4 793a440e ed624add 58bcc605 8687be48 5b62388d 395038fd
9272e584 2845d20a e35d406b f08b29d4 76f2ee39 942f35ae 3431bfc3 bfc16856
00000020 00000001 01108d28 b6e8816f 09c21be4 50cce73b 3460ab8a 712c11c8
00000000 00000000 00000000
2014-05-27 13:51:11 [DEBUG]: oakley.c:3871:oakley_delivm(): IV freed
2014-05-27 13:51:11 [DEBUG]: oakley.c:698:oakley_compute_hash1(): HASH with:
2014-05-27 13:51:11 [DEBUG]: oakley.c:699:oakley_compute_hash1():
f9b31c8b 00000020 00000001 01108d28 b6e8816f 09c21be4 50cce73b 3460ab8a
712c11c8
2014-05-27 13:51:11 [DEBUG]: algorithm.c:469:alg_oakley_hmacdef(): hmac(hmac_sha2_512)
2014-05-27 13:51:11 [DEBUG]: oakley.c:708:oakley_compute_hash1(): HASH computed:
2014-05-27 13:51:11 [DEBUG]: oakley.c:709:oakley_compute_hash1():
dea2d538 75fefdf4 793a440e ed624add 58bcc605 8687be48 5b62388d 395038fd
9272e584 2845d20a e35d406b f08b29d4 76f2ee39 942f35ae 3431bfc3 bfc16856
2014-05-27 13:51:11 [DEBUG]: isakmp_inf.c:262:isakmp_info_recv(): hash validated.
2014-05-27 13:51:11 [DEBUG]: ikev1.c:2843:isakmp_parsewoh(): begin.
2014-05-27 13:51:11 [DEBUG]: ikev1.c:2870:isakmp_parsewoh(): seen nptype=8(hash)
2014-05-27 13:51:11 [DEBUG]: ikev1.c:2870:isakmp_parsewoh(): seen nptype=11(notify)
2014-05-27 13:51:11 [DEBUG]: ikev1.c:2909:isakmp_parsewoh(): succeed.
2014-05-27 13:51:11 [DEBUG]: isakmp_inf.c:1546:isakmp_info_recv_r_u(): DPD R-U-There received
2014-05-27 13:51:11 [DEBUG]: oakley.c:3811:oakley_newiv2(): compute IV for phase2
2014-05-27 13:51:11 [DEBUG]: oakley.c:3812:oakley_newiv2(): phase1 last IV:
2014-05-27 13:51:11 [DEBUG]: oakley.c:3813:oakley_newiv2():
7af22e17 a3c0ea53 db5a6e97 88e563f3 47c30db6
2014-05-27 13:51:11 [DEBUG]: algorithm.c:386:alg_oakley_hashdef(): hash(sha512)
2014-05-27 13:51:11 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-05-27 13:51:11 [DEBUG]: oakley.c:3846:oakley_newiv2(): phase2 IV computed:
2014-05-27 13:51:11 [DEBUG]: oakley.c:3847:oakley_newiv2():
08ebdd81 a246ddc3 c1ea14c5 d1910c18
2014-05-27 13:51:11 [DEBUG]: oakley.c:698:oakley_compute_hash1(): HASH with:
2014-05-27 13:51:11 [DEBUG]: oakley.c:699:oakley_compute_hash1():
47c30db6 00000020 00000001 01108d29 b6e8816f 09c21be4 50cce73b 3460ab8a
712c11c8
2014-05-27 13:51:11 [DEBUG]: algorithm.c:469:alg_oakley_hmacdef(): hmac(hmac_sha2_512)
2014-05-27 13:51:11 [DEBUG]: oakley.c:708:oakley_compute_hash1(): HASH computed:
2014-05-27 13:51:11 [DEBUG]: oakley.c:709:oakley_compute_hash1():
3a3f77df 2231fb89 12ac4d39 3664edc8 d7f630cb f98f4465 2c32a72e a2a81a2f
00a9d4b2 0fefd248 f6c1d52b 67884f5a 83f3b79e df2bdab0 b6ce386f 4584b950
2014-05-27 13:51:11 [DEBUG]: oakley.c:4017:oakley_do_encrypt(): begin encryption.
2014-05-27 13:51:11 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-05-27 13:51:11 [DEBUG]: oakley.c:4033:oakley_do_encrypt(): pad length = 12
2014-05-27 13:51:11 [DEBUG]: oakley.c:4063:oakley_do_encrypt():
0b000044 3a3f77df 2231fb89 12ac4d39 3664edc8 d7f630cb f98f4465 2c32a72e
a2a81a2f 00a9d4b2 0fefd248 f6c1d52b 67884f5a 83f3b79e df2bdab0 b6ce386f
4584b950 00000020 00000001 01108d29 b6e8816f 09c21be4 50cce73b 3460ab8a
712c11c8 588810ea ef8db091 24ee320c
2014-05-27 13:51:11 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-05-27 13:51:11 [DEBUG]: oakley.c:4073:oakley_do_encrypt(): with key:
2014-05-27 13:51:11 [DEBUG]: oakley.c:4074:oakley_do_encrypt():
d3afb025 07033c6c efa1e863 b4640243 e0b57508 bc394080 b1d13a42 7c271880
2014-05-27 13:51:11 [DEBUG]: oakley.c:4079:oakley_do_encrypt(): encrypted payload by IV:
2014-05-27 13:51:11 [DEBUG]: oakley.c:4080:oakley_do_encrypt():
08ebdd81 a246ddc3 c1ea14c5 d1910c18
2014-05-27 13:51:11 [DEBUG]: oakley.c:4086:oakley_do_encrypt(): save IV for next:
2014-05-27 13:51:11 [DEBUG]: oakley.c:4087:oakley_do_encrypt():
70ac70bb 857a6869 6d4950a5 99dcc517
2014-05-27 13:51:11 [DEBUG]: oakley.c:4103:oakley_do_encrypt(): encrypted.
2014-05-27 13:51:11 [DEBUG]: ikev1.c:2990:isakmp_send(): 140 bytes from 122.152.XXX.XX[500] to 165.228.XXX.XXX[500]
2014-05-27 13:51:11 [DEBUG]: sockmisc.c:336:sendfromto(): sockname 122.152.XXX.XX[500]
2014-05-27 13:51:11 [DEBUG]: sockmisc.c:338:sendfromto(): send packet from 122.152.XXX.XX[500]
2014-05-27 13:51:11 [DEBUG]: sockmisc.c:340:sendfromto(): send packet to 165.228.XXX.XXX[500]
2014-05-27 13:51:11 [DEBUG]: sockmisc.c:525:sendfromto(): 1 times of 140 bytes message will be sent to 165.228.XXX.XXX[500]
2014-05-27 13:51:11 [DEBUG]: sockmisc.c:529:sendfromto():
b6e8816f 09c21be4 50cce73b 3460ab8a 08100501 47c30db6 0000008c eb651d0f
9430ce83 708741d1 e4a89130 507390e9 7347b879 4744c7ef 2ea5a2f5 fcb218eb
4aea4e33 b8b3f0d1 8f5f74f2 4665efc4 30bc0cb3 284e949f 026157fb 994161cf
55404d7a bbe1c004 92d5f3c9 d9f5c834 77f4ceef 69205228 348f0d8f 70ac70bb
857a6869 6d4950a5 99dcc517
2014-05-27 13:51:11 [DEBUG]: isakmp_inf.c:805:isakmp_info_send_common(): sendto Information notify.
2014-05-27 13:51:11 [DEBUG]: oakley.c:3871:oakley_delivm(): IV freed
2014-05-27 13:51:11 [DEBUG]: isakmp_inf.c:1575:isakmp_info_recv_r_u(): received a valid R-U-THERE, ACK sent
2014-05-27 13:51:11 [PROTO_NOTIFY]: isakmp_inf.c:1159:isakmp_info_recv_n(): notification message 36136:R-U-THERE, doi=1 proto_id=1 spi=b6e8816f09c21be4 50cce73b3460ab8a (size=16).
2014-05-27 13:51:15.083 +0200 debug: ifmon_request_put(daemon/panike_sysd_if.c:916): 16 write to pipe: keyacquire
2014-05-27 13:51:15.083 +0200 debug: ifmon_request_get(daemon/panike_sysd_if.c:932): 16 read from pipe, msg type 3
2014-05-27 13:51:15.083 +0200 debug: pan_msg_process(daemon/panike_sysd_if.c:1030): request from pipe: keyacquire
2014-05-27 13:51:15 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL1A(Gateway-MEL1A)_out
2014-05-27 13:51:15 [INFO]: ikev1.c:710:ikev1_initiate(): 0:122.152.XXX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL1A passive mode specified for IKEv1, dropping acquire request
2014-05-27 13:51:19.083 +0200 debug: ifmon_request_put(daemon/panike_sysd_if.c:916): 16 write to pipe: keyacquire
2014-05-27 13:51:19.083 +0200 debug: ifmon_request_get(daemon/panike_sysd_if.c:932): 16 read from pipe, msg type 3
2014-05-27 13:51:19.083 +0200 debug: pan_msg_process(daemon/panike_sysd_if.c:1030): request from pipe: keyacquire
2014-05-27 13:51:19 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL1A(Gateway-MEL1A)_out
2014-05-27 13:51:19 [INFO]: ikev1.c:710:ikev1_initiate(): 0:122.152.XXX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL1A passive mode specified for IKEv1, dropping acquire request
2014-05-27 13:51:19 [DEBUG]: ikev1_natt.c:348:natt_keepalive_send(): KA: 122.152.XXX.XX[4500]->60.231.XX.XXX[64951]
2014-05-27 13:51:19 [DEBUG]: sockmisc.c:336:sendfromto(): sockname 122.152.XXX.XX[4500]
2014-05-27 13:51:19 [DEBUG]: sockmisc.c:338:sendfromto(): send packet from 122.152.XXX.XX[4500]
2014-05-27 13:51:19 [DEBUG]: sockmisc.c:340:sendfromto(): send packet to 60.231.XX.XXX[64951]
2014-05-27 13:51:19 [DEBUG]: sockmisc.c:525:sendfromto(): 1 times of 1 bytes message will be sent to 60.231.XX.XXX[64951]
2014-05-27 13:51:19 [DEBUG]: sockmisc.c:529:sendfromto():
ff
2014-05-27 13:51:19 [DEBUG]: ikev1_natt.c:348:natt_keepalive_send(): KA: 122.152.XXX.XX[4500]->195.243.XXX.XXX[61006]
2014-05-27 13:51:19 [DEBUG]: sockmisc.c:336:sendfromto(): sockname 122.152.XXX.XX[4500]
2014-05-27 13:51:19 [DEBUG]: sockmisc.c:338:sendfromto(): send packet from 122.152.XXX.XX[4500]
2014-05-27 13:51:19 [DEBUG]: sockmisc.c:340:sendfromto(): send packet to 195.243.XXX.XXX[61006]
2014-05-27 13:51:19 [DEBUG]: sockmisc.c:525:sendfromto(): 1 times of 1 bytes message will be sent to 195.243.XXX.XXX[61006]
2014-05-27 13:51:19 [DEBUG]: sockmisc.c:529:sendfromto():
ff
2014-05-27 13:51:25.084 +0200 debug: ifmon_request_put(daemon/panike_sysd_if.c:916): 16 write to pipe: keyacquire
2014-05-27 13:51:25.084 +0200 debug: ifmon_request_get(daemon/panike_sysd_if.c:932): 16 read from pipe, msg type 3
2014-05-27 13:51:25.084 +0200 debug: pan_msg_process(daemon/panike_sysd_if.c:1030): request from pipe: keyacquire
2014-05-27 13:51:25 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL1A(Gateway-MEL1A)_out
2014-05-27 13:51:25 [INFO]: ikev1.c:710:ikev1_initiate(): 0:122.152.XXX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL1A passive mode specified for IKEv1, dropping acquire request
2014-05-27 13:51:29.083 +0200 debug: ifmon_request_put(daemon/panike_sysd_if.c:916): 16 write to pipe: keyacquire
2014-05-27 13:51:29.083 +0200 debug: ifmon_request_get(daemon/panike_sysd_if.c:932): 16 read from pipe, msg type 3
2014-05-27 13:51:29.083 +0200 debug: pan_msg_process(daemon/panike_sysd_if.c:1030): request from pipe: keyacquire
2014-05-27 13:51:29 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL1A(Gateway-MEL1A)_out
2014-05-27 13:51:29 [INFO]: ikev1.c:710:ikev1_initiate(): 0:122.152.XXX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL1A passive mode specified for IKEv1, dropping acquire request
2014-05-27 13:51:35.084 +0200 debug: ifmon_request_put(daemon/panike_sysd_if.c:916): 16 write to pipe: keyacquire
2014-05-27 13:51:35.084 +0200 debug: ifmon_request_get(daemon/panike_sysd_if.c:932): 16 read from pipe, msg type 3
2014-05-27 13:51:35.084 +0200 debug: pan_msg_process(daemon/panike_sysd_if.c:1030): request from pipe: keyacquire
2014-05-27 13:51:35 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL1A(Gateway-MEL1A)_out
2014-05-27 13:51:35 [INFO]: ikev1.c:710:ikev1_initiate(): 0:122.152.XXX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL1A passive mode specified for IKEv1, dropping acquire request
2014-05-27 13:51:39.085 +0200 debug: ifmon_request_put(daemon/panike_sysd_if.c:916): 16 write to pipe: keyacquire
2014-05-27 13:51:39.086 +0200 debug: ifmon_request_get(daemon/panike_sysd_if.c:932): 16 read from pipe, msg type 3
2014-05-27 13:51:39.086 +0200 debug: pan_msg_process(daemon/panike_sysd_if.c:1030): request from pipe: keyacquire
2014-05-27 13:51:39 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BPN2B(Gateway-BPN2B)_out
2014-05-27 13:51:39 [INFO]: ikev1.c:710:ikev1_initiate(): 0:122.152.XXX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BPN2B passive mode specified for IKEv1, dropping acquire request
2014-05-27 13:51:39 [DEBUG]: ikev1_natt.c:348:natt_keepalive_send(): KA: 122.152.XXX.XX[4500]->60.231.XX.XXX[64951]
2014-05-27 13:51:39 [DEBUG]: sockmisc.c:336:sendfromto(): sockname 122.152.XXX.XX[4500]
2014-05-27 13:51:39 [DEBUG]: sockmisc.c:338:sendfromto(): send packet from 122.152.XXX.XX[4500]
2014-05-27 13:51:39 [DEBUG]: sockmisc.c:340:sendfromto(): send packet to 60.231.XX.XXX[64951]
2014-05-27 13:51:39 [DEBUG]: sockmisc.c:525:sendfromto(): 1 times of 1 bytes message will be sent to 60.231.XX.XXX[64951]
2014-05-27 13:51:39 [DEBUG]: sockmisc.c:529:sendfromto():
ff
2014-05-27 13:51:39 [DEBUG]: ikev1_natt.c:348:natt_keepalive_send(): KA: 122.152.XXX.XX[4500]->195.243.XXX.XXX[61006]
2014-05-27 13:51:39 [DEBUG]: sockmisc.c:336:sendfromto(): sockname 122.152.XXX.XX[4500]
2014-05-27 13:51:39 [DEBUG]: sockmisc.c:338:sendfromto(): send packet from 122.152.XXX.XX[4500]
2014-05-27 13:51:39 [DEBUG]: sockmisc.c:340:sendfromto(): send packet to 195.243.XXX.XXX[61006]
2014-05-27 13:51:39 [DEBUG]: sockmisc.c:525:sendfromto(): 1 times of 1 bytes message will be sent to 195.243.XXX.XXX[61006]
2014-05-27 13:51:39 [DEBUG]: sockmisc.c:529:sendfromto():
ff
2014-05-27 13:51:39.090 +0200 debug: ifmon_request_put(daemon/panike_sysd_if.c:916): 16 write to pipe: keyacquire
2014-05-27 13:51:39.093 +0200 debug: ifmon_request_put(daemon/panike_sysd_if.c:916): 16 write to pipe: keyacquire
2014-05-27 13:51:39.094 +0200 debug: ifmon_request_get(daemon/panike_sysd_if.c:932): 16 read from pipe, msg type 3
2014-05-27 13:51:39.094 +0200 debug: pan_msg_process(daemon/panike_sysd_if.c:1030): request from pipe: keyacquire
2014-05-27 13:51:39 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-BDB3B(Gateway-BDB4A)_out
2014-05-27 13:51:39 [INFO]: ikev1.c:710:ikev1_initiate(): 0:122.152.XXX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-BDB4A passive mode specified for IKEv1, dropping acquire request
2014-05-27 13:51:39.094 +0200 debug: ifmon_request_get(daemon/panike_sysd_if.c:932): 16 read from pipe, msg type 3
2014-05-27 13:51:39.094 +0200 debug: pan_msg_process(daemon/panike_sysd_if.c:1030): request from pipe: keyacquire
2014-05-27 13:51:39 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL1A(Gateway-MEL1A)_out
2014-05-27 13:51:39 [INFO]: ikev1.c:710:ikev1_initiate(): 0:122.152.XXX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL1A passive mode specified for IKEv1, dropping acquire request
2014-05-27 13:51:41 [DEBUG]: isakmp.c:982:isakmp_handler(): ===
2014-05-27 13:51:41 [DEBUG]: isakmp.c:983:isakmp_handler(): 140 bytes message received from 165.228.XXX.XXX[500]
2014-05-27 13:51:41 [DEBUG]: isakmp.c:986:isakmp_handler():
b6e8816f 09c21be4 50cce73b 3460ab8a 08100501 5bad2888 0000008c cb35c8ab
44be8172 1fb33f92 be086c99 0a34ec8e 9ce53d3a 9d0e7c40 916f7c04 d400918e
18c895a2 d8e4fcf6 14a42749 0fee6f5c 25cc534b 8de6798b b2fb87c2 170073d9
ad7bacb0 0f3a8064 ed92c4a7 b559712a b263e460 8248f868 b5a6b441 b08e2789
7e6d93d5 a8725455 4ebf339f
2014-05-27 13:51:41 [DEBUG]: isakmp_inf.c:147:isakmp_info_recv(): receive Information.
2014-05-27 13:51:41 [DEBUG]: oakley.c:3811:oakley_newiv2(): compute IV for phase2
2014-05-27 13:51:41 [DEBUG]: oakley.c:3812:oakley_newiv2(): phase1 last IV:
2014-05-27 13:51:41 [DEBUG]: oakley.c:3813:oakley_newiv2():
7af22e17 a3c0ea53 db5a6e97 88e563f3 5bad2888
2014-05-27 13:51:41 [DEBUG]: algorithm.c:386:alg_oakley_hashdef(): hash(sha512)
2014-05-27 13:51:41 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-05-27 13:51:41 [DEBUG]: oakley.c:3846:oakley_newiv2(): phase2 IV computed:
2014-05-27 13:51:41 [DEBUG]: oakley.c:3847:oakley_newiv2():
5f0ea8ed 6b42564e 5f86f338 e9a27179
2014-05-27 13:51:41 [DEBUG]: oakley.c:3892:oakley_do_decrypt(): begin decryption.
2014-05-27 13:51:41 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-05-27 13:51:41 [DEBUG]: oakley.c:3906:oakley_do_decrypt(): IV was saved for next processing:
2014-05-27 13:51:41 [DEBUG]: oakley.c:3908:oakley_do_decrypt():
b08e2789 7e6d93d5 a8725455 4ebf339f
2014-05-27 13:51:41 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-05-27 13:51:41 [DEBUG]: oakley.c:3931:oakley_do_decrypt(): with key:
2014-05-27 13:51:41 [DEBUG]: oakley.c:3932:oakley_do_decrypt():
d3afb025 07033c6c efa1e863 b4640243 e0b57508 bc394080 b1d13a42 7c271880
2014-05-27 13:51:41 [DEBUG]: oakley.c:3937:oakley_do_decrypt(): decrypted payload by IV:
2014-05-27 13:51:41 [DEBUG]: oakley.c:3938:oakley_do_decrypt():
5f0ea8ed 6b42564e 5f86f338 e9a27179
2014-05-27 13:51:41 [DEBUG]: oakley.c:3940:oakley_do_decrypt(): decrypted payload, but not trimed.
2014-05-27 13:51:41 [DEBUG]: oakley.c:3942:oakley_do_decrypt():
0b000044 257f7a23 8de37f13 54a2b585 90a920a9 0c1ad032 8c7d0599 40191d8a
1def89d7 080d3094 5bd85e4f 4f9263a3 119c86b6 8dc367b9 6798b04c 40e8873f
629deee0 00000020 00000001 01108d28 b6e8816f 09c21be4 50cce73b 3460ab8a
712c11cb 00000000 00000000 00000000
2014-05-27 13:51:41 [DEBUG]: oakley.c:3951:oakley_do_decrypt(): padding len=0
2014-05-27 13:51:41 [DEBUG]: oakley.c:3982:oakley_do_decrypt(): decrypted.
2014-05-27 13:51:41 [DEBUG]: oakley.c:3983:oakley_do_decrypt():
b6e8816f 09c21be4 50cce73b 3460ab8a 08100501 5bad2888 0000008c 0b000044
257f7a23 8de37f13 54a2b585 90a920a9 0c1ad032 8c7d0599 40191d8a 1def89d7
080d3094 5bd85e4f 4f9263a3 119c86b6 8dc367b9 6798b04c 40e8873f 629deee0
00000020 00000001 01108d28 b6e8816f 09c21be4 50cce73b 3460ab8a 712c11cb
00000000 00000000 00000000
2014-05-27 13:51:41 [DEBUG]: oakley.c:3871:oakley_delivm(): IV freed
2014-05-27 13:51:41 [DEBUG]: oakley.c:698:oakley_compute_hash1(): HASH with:
2014-05-27 13:51:41 [DEBUG]: oakley.c:699:oakley_compute_hash1():
5bad2888 00000020 00000001 01108d28 b6e8816f 09c21be4 50cce73b 3460ab8a
712c11cb
2014-05-27 13:51:41 [DEBUG]: algorithm.c:469:alg_oakley_hmacdef(): hmac(hmac_sha2_512)
2014-05-27 13:51:41 [DEBUG]: oakley.c:708:oakley_compute_hash1(): HASH computed:
2014-05-27 13:51:41 [DEBUG]: oakley.c:709:oakley_compute_hash1():
257f7a23 8de37f13 54a2b585 90a920a9 0c1ad032 8c7d0599 40191d8a 1def89d7
080d3094 5bd85e4f 4f9263a3 119c86b6 8dc367b9 6798b04c 40e8873f 629deee0
2014-05-27 13:51:41 [DEBUG]: isakmp_inf.c:262:isakmp_info_recv(): hash validated.
2014-05-27 13:51:41 [DEBUG]: ikev1.c:2843:isakmp_parsewoh(): begin.
2014-05-27 13:51:41 [DEBUG]: ikev1.c:2870:isakmp_parsewoh(): seen nptype=8(hash)
2014-05-27 13:51:41 [DEBUG]: ikev1.c:2870:isakmp_parsewoh(): seen nptype=11(notify)
2014-05-27 13:51:41 [DEBUG]: ikev1.c:2909:isakmp_parsewoh(): succeed.
2014-05-27 13:51:41 [DEBUG]: isakmp_inf.c:1546:isakmp_info_recv_r_u(): DPD R-U-There received
2014-05-27 13:51:41 [DEBUG]: oakley.c:3811:oakley_newiv2(): compute IV for phase2
2014-05-27 13:51:41 [DEBUG]: oakley.c:3812:oakley_newiv2(): phase1 last IV:
2014-05-27 13:51:41 [DEBUG]: oakley.c:3813:oakley_newiv2():
7af22e17 a3c0ea53 db5a6e97 88e563f3 fb68d376
2014-05-27 13:51:41 [DEBUG]: algorithm.c:386:alg_oakley_hashdef(): hash(sha512)
2014-05-27 13:51:41 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-05-27 13:51:41 [DEBUG]: oakley.c:3846:oakley_newiv2(): phase2 IV computed:
2014-05-27 13:51:41 [DEBUG]: oakley.c:3847:oakley_newiv2():
67f7c4a9 f86bf49e 957f44d1 a54c8127
2014-05-27 13:51:41 [DEBUG]: oakley.c:698:oakley_compute_hash1(): HASH with:
2014-05-27 13:51:41 [DEBUG]: oakley.c:699:oakley_compute_hash1():
fb68d376 00000020 00000001 01108d29 b6e8816f 09c21be4 50cce73b 3460ab8a
712c11cb
2014-05-27 13:51:41 [DEBUG]: algorithm.c:469:alg_oakley_hmacdef(): hmac(hmac_sha2_512)
2014-05-27 13:51:41 [DEBUG]: oakley.c:708:oakley_compute_hash1(): HASH computed:
2014-05-27 13:51:41 [DEBUG]: oakley.c:709:oakley_compute_hash1():
9cddf373 2998146a a716af6f 53281d3e be6bc11c 326f9578 aec8fa0a 1a1d5590
f4393332 7c18314f 8230a9db 4f36817f bd32b38c 874e66d3 e1625fed 26c77edc
2014-05-27 13:51:41 [DEBUG]: oakley.c:4017:oakley_do_encrypt(): begin encryption.
2014-05-27 13:51:41 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-05-27 13:51:41 [DEBUG]: oakley.c:4033:oakley_do_encrypt(): pad length = 12
2014-05-27 13:51:41 [DEBUG]: oakley.c:4063:oakley_do_encrypt():
0b000044 9cddf373 2998146a a716af6f 53281d3e be6bc11c 326f9578 aec8fa0a
1a1d5590 f4393332 7c18314f 8230a9db 4f36817f bd32b38c 874e66d3 e1625fed
26c77edc 00000020 00000001 01108d29 b6e8816f 09c21be4 50cce73b 3460ab8a
712c11cb f1a8f6ba b2fe9c40 e915dc0c
2014-05-27 13:51:41 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-05-27 13:51:41 [DEBUG]: oakley.c:4073:oakley_do_encrypt(): with key:
2014-05-27 13:51:41 [DEBUG]: oakley.c:4074:oakley_do_encrypt():
d3afb025 07033c6c efa1e863 b4640243 e0b57508 bc394080 b1d13a42 7c271880
2014-05-27 13:51:41 [DEBUG]: oakley.c:4079:oakley_do_encrypt(): encrypted payload by IV:
2014-05-27 13:51:41 [DEBUG]: oakley.c:4080:oakley_do_encrypt():
67f7c4a9 f86bf49e 957f44d1 a54c8127
2014-05-27 13:51:41 [DEBUG]: oakley.c:4086:oakley_do_encrypt(): save IV for next:
2014-05-27 13:51:41 [DEBUG]: oakley.c:4087:oakley_do_encrypt():
8173eedd 64fe576a 151274e8 dd508421
2014-05-27 13:51:41 [DEBUG]: oakley.c:4103:oakley_do_encrypt(): encrypted.
2014-05-27 13:51:41 [DEBUG]: ikev1.c:2990:isakmp_send(): 140 bytes from 122.152.XXX.XX[500] to 165.228.XXX.XXX[500]
2014-05-27 13:51:41 [DEBUG]: sockmisc.c:336:sendfromto(): sockname 122.152.XXX.XX[500]
2014-05-27 13:51:41 [DEBUG]: sockmisc.c:338:sendfromto(): send packet from 122.152.XXX.XX[500]
2014-05-27 13:51:41 [DEBUG]: sockmisc.c:340:sendfromto(): send packet to 165.228.XXX.XXX[500]
2014-05-27 13:51:41 [DEBUG]: sockmisc.c:525:sendfromto(): 1 times of 140 bytes message will be sent to 165.228.XXX.XXX[500]
2014-05-27 13:51:41 [DEBUG]: sockmisc.c:529:sendfromto():
b6e8816f 09c21be4 50cce73b 3460ab8a 08100501 fb68d376 0000008c 25a3c8b3
1ace4c9d e4c88a94 85528a8e 431fcbaf fcb2a1cb b375a8be 45aca317 22b0d05e
9428417e db1634f6 43e98f91 5c43cba2 4ff409dc 89a51afb 257132ed 56e16981
d56ecb05 ea4760eb 548c115e e3011ac4 871e9822 183e2051 792926dd 8173eedd
64fe576a 151274e8 dd508421
2014-05-27 13:51:41 [DEBUG]: isakmp_inf.c:805:isakmp_info_send_common(): sendto Information notify.
2014-05-27 13:51:41 [DEBUG]: oakley.c:3871:oakley_delivm(): IV freed
2014-05-27 13:51:41 [DEBUG]: isakmp_inf.c:1575:isakmp_info_recv_r_u(): received a valid R-U-THERE, ACK sent
2014-05-27 13:51:41 [PROTO_NOTIFY]: isakmp_inf.c:1159:isakmp_info_recv_n(): notification message 36136:R-U-THERE, doi=1 proto_id=1 spi=b6e8816f09c21be4 50cce73b3460ab8a (size=16).
2014-05-27 13:51:43.085 +0200 debug: ifmon_request_put(daemon/panike_sysd_if.c:916): 16 write to pipe: keyacquire
2014-05-27 13:51:43.086 +0200 debug: ifmon_request_get(daemon/panike_sysd_if.c:932): 16 read from pipe, msg type 3
2014-05-27 13:51:43.086 +0200 debug: pan_msg_process(daemon/panike_sysd_if.c:1030): request from pipe: keyacquire
2014-05-27 13:51:43 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL1A(Gateway-MEL1A)_out
2014-05-27 13:51:43 [INFO]: ikev1.c:710:ikev1_initiate(): 0:122.152.XXX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL1A passive mode specified for IKEv1, dropping acquire request
2014-05-27 13:51:43 [DEBUG]: isakmp.c:982:isakmp_handler(): ===
2014-05-27 13:51:43 [DEBUG]: isakmp.c:983:isakmp_handler(): 492 bytes message received from 175.184.XXX.XXX[500]
2014-05-27 13:51:43 [DEBUG]: isakmp.c:986:isakmp_handler():
145d0809 f142b7d7 e9f6b280 36b395b8 08102001 b940d104 000001ec 6dbb2b8e
3114d6e6 bcf850be 8f218a99 6546c2a4 df0a250e de15b3ee c2231c02 b9759956
0323f9a4 0eea8a6f 0a1ce9ff 890c6c5a 40ba1fe6 9a519581 6ade5c14 147b3356
8c32520e e6b6ba27 8331b8c2 e8f51a48 1fef18d9 ca138ca2 905bf85e 7c4305db
5ce3b8f0 c310e1b5 5b5cd9a7 051b5277 7a4f41f0 96c1969b c2f8db38 3ab4a503
f2643623 b33f057a bf5d5ce9 6147d765 c63c1396 1c48a20a 48fb46fb 51cc3042
8ea0506e b244f1e1 492a65cd 00e8c230 44150663 79a920c3 82d78d66 29a48ec6
e3e8f951 8da619ae 970699f7 08d1e530 b482c5c8 1d5dd221 9976ddee a95ab21d
2b72e9e6 95a9fab3 ddf1695c 2fc70398 10ab3c6a c8158115 e53a30dd fa1405b4
a295f116 41608986 8dce3b8f c363f0a2 d80fb004 bae42480 4a80e0ea 0c2441bd
19ee1d70 d47da9de f0b05e2f a32ed4a2 32b21eda 268b5aaf 615719fe 28736c43
7e0eab30 509c89c4 efea490b 2cfd37e1 d9d9853d 5b7d318c 446f0e2b 0d5ecd88
5c9fec39 ef13e9b6 64a46e30 6f446488 2b067829 9fa44b83 f3d6d172 e239fd4b
5c61d417 4d5322c2 4f1f221c2014-05-27 13:51:43 [DEBUG]: oakley.c:3811:oakley_newiv2(): compute IV for phase2
2014-05-27 13:51:43 [DEBUG]: oakley.c:3812:oakley_newiv2(): phase1 last IV:
2014-05-27 13:51:43 [DEBUG]: oakley.c:3813:oakley_newiv2():
dfc5ede0 0f13942d fec6b0e9 c729bc43 b940d104
2014-05-27 13:51:43 [DEBUG]: algorithm.c:386:alg_oakley_hashdef(): hash(sha512)
2014-05-27 13:51:43 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-05-27 13:51:43 [DEBUG]: oakley.c:3846:oakley_newiv2(): phase2 IV computed:
2014-05-27 13:51:43 [DEBUG]: oakley.c:3847:oakley_newiv2():
9786ce5e 136ef42a 9f849af0 a3cdeb52
2014-05-27 13:51:43 [PROTO_NOTIFY]: ikev1.c:2518:log_ph2started(): ====> PHASE-2 NEGOTIATION STARTED AS RESPONDER, (QUICK MODE) <====
====> Initiated SA: 122.152.XXX.XX[500]-175.184.XXX.XXX[500] message id:0xB940D104 <====
2014-05-27 13:51:43 [DEBUG]: oakley.c:3892:oakley_do_decrypt(): begin decryption.
2014-05-27 13:51:43 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-05-27 13:51:43 [DEBUG]: oakley.c:3906:oakley_do_decrypt(): IV was saved for next processing:
2014-05-27 13:51:43 [DEBUG]: oakley.c:3908:oakley_do_decrypt():
4abe1bbd accdd8e6 14f44f61 2cb174da
2014-05-27 13:51:43 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-05-27 13:51:43 [DEBUG]: oakley.c:3931:oakley_do_decrypt(): with key:
2014-05-27 13:51:43 [DEBUG]: oakley.c:3932:oakley_do_decrypt():
97ce00c8 5f714f8a a13a1bb9 9898eaf0 e204f110 4144f29b 52e58c88 c8b2597f
2014-05-27 13:51:43 [DEBUG]: oakley.c:3937:oakley_do_decrypt(): decrypted payload by IV:
2014-05-27 13:51:43 [DEBUG]: oakley.c:3938:oakley_do_decrypt():
9786ce5e 136ef42a 9f849af0 a3cdeb52
2014-05-27 13:51:43 [DEBUG]: oakley.c:3940:oakley_do_decrypt(): decrypted payload, but not trimed.
2014-05-27 13:51:43 [DEBUG]: oakley.c:3942:oakley_do_decrypt():
01000044 b7be03bd efa58771 daf4a893 df248544 5fb2a34c 8fa8f5bc 6b0ccf81
7d5cd0a1 1b15d554 7dc7de00 cf5e8f72 fda4a7e1 14120312 5db942fd 5710f835
0a2187fb 0a000044 00000001 00000001 00000038 01030401 fdc7c4b0 0000002c
010c0000 80040001 80010001 80020e10 80010002 00020004 00465000 80050007
80060100 8003000e 04000018 3eafd04d 837cec24 3ab9bf06 82cb0b6f b8182ce4
05000104 779b84ef 9c106976 e2dd3520 20929dd4 a6073037 417c513d d50cda25
79e5aba9 62a66718 86f9cf25 27d7d98e 056146f7 92e87823 644c689c 043ff109
4580a0ee 59cbec23 06ed1d0e fdbbce1f 896cd588 622bee94 368c89b9 7e0ba279
74516b8b fda493f5 0cfbbea4 7f1744f8 53eb73c2 1120608b 4af5300f eb712805
e8d0f62e 4edb9500 73e83027 c50a5113 d7051d09 e3f02682 526945ac 0bbf90aa
bad622a3 0feaf4f8 b4baa853 ca77557c 0c3685da f6edf307 ec0003f0 6d674d0e
9984a353 52b6555d 25c8e95d 1d71c51f af779aaf d9c8e4d7 31d07de6 fb499345
6c9c6f6e 46fb0d3e 30f5eedb 3686b022 a75d11ea e73d1424 c5ab9e1f 1eb9e815
9e040b4e 05000010 04002014-05-27 13:51:43 [DEBUG]: oakley.c:3951:oakley_do_decrypt(): padding len=0
2014-05-27 13:51:43 [DEBUG]: oakley.c:3982:oakley_do_decrypt(): decrypted.
2014-05-27 13:51:43 [DEBUG]: oakley.c:3983:oakley_do_decrypt():
145d0809 f142b7d7 e9f6b280 36b395b8 08102001 b940d104 000001ec 01000044
b7be03bd efa58771 daf4a893 df248544 5fb2a34c 8fa8f5bc 6b0ccf81 7d5cd0a1
1b15d554 7dc7de00 cf5e8f72 fda4a7e1 14120312 5db942fd 5710f835 0a2187fb
0a000044 00000001 00000001 00000038 01030401 fdc7c4b0 0000002c 010c0000
80040001 80010001 80020e10 80010002 00020004 00465000 80050007 80060100
8003000e 04000018 3eafd04d 837cec24 3ab9bf06 82cb0b6f b8182ce4 05000104
779b84ef 9c106976 e2dd3520 20929dd4 a6073037 417c513d d50cda25 79e5aba9
62a66718 86f9cf25 27d7d98e 056146f7 92e87823 644c689c 043ff109 4580a0ee
59cbec23 06ed1d0e fdbbce1f 896cd588 622bee94 368c89b9 7e0ba279 74516b8b
fda493f5 0cfbbea4 7f1744f8 53eb73c2 1120608b 4af5300f eb712805 e8d0f62e
4edb9500 73e83027 c50a5113 d7051d09 e3f02682 526945ac 0bbf90aa bad622a3
0feaf4f8 b4baa853 ca77557c 0c3685da f6edf307 ec0003f0 6d674d0e 9984a353
52b6555d 25c8e95d 1d71c51f af779aaf d9c8e4d7 31d07de6 fb499345 6c9c6f6e
46fb0d3e 30f5eedb 36862014-05-27 13:51:43 [DEBUG]: ikev1.c:2843:isakmp_parsewoh(): begin.
2014-05-27 13:51:43 [DEBUG]: ikev1.c:2870:isakmp_parsewoh(): seen nptype=8(hash)
2014-05-27 13:51:43 [DEBUG]: ikev1.c:2870:isakmp_parsewoh(): seen nptype=1(sa)
2014-05-27 13:51:43 [DEBUG]: ikev1.c:2870:isakmp_parsewoh(): seen nptype=10(nonce)
2014-05-27 13:51:43 [DEBUG]: ikev1.c:2870:isakmp_parsewoh(): seen nptype=4(ke)
2014-05-27 13:51:43 [DEBUG]: ikev1.c:2870:isakmp_parsewoh(): seen nptype=5(id)
2014-05-27 13:51:43 [DEBUG]: ikev1.c:2870:isakmp_parsewoh(): seen nptype=5(id)
2014-05-27 13:51:43 [DEBUG]: ikev1.c:2909:isakmp_parsewoh(): succeed.
2014-05-27 13:51:43 [DEBUG]: isakmp_quick.c:1163:quick_r1recv(): received IDci2:2014-05-27 13:51:43 [DEBUG]: isakmp_quick.c:1164:quick_r1recv():
04000000 00000000 00000000
2014-05-27 13:51:43 [DEBUG]: isakmp_quick.c:1167:quick_r1recv(): received IDcr2:2014-05-27 13:51:43 [DEBUG]: isakmp_quick.c:1168:quick_r1recv():
04000000 00000000 00000000
2014-05-27 13:51:43 [DEBUG]: isakmp_quick.c:1182:quick_r1recv(): HASH(1) validate:2014-05-27 13:51:43 [DEBUG]: isakmp_quick.c:1183:quick_r1recv():
b7be03bd efa58771 daf4a893 df248544 5fb2a34c 8fa8f5bc 6b0ccf81 7d5cd0a1
1b15d554 7dc7de00 cf5e8f72 fda4a7e1 14120312 5db942fd 5710f835 0a2187fb
2014-05-27 13:51:43 [DEBUG]: oakley.c:698:oakley_compute_hash1(): HASH with:
2014-05-27 13:51:43 [DEBUG]: oakley.c:699:oakley_compute_hash1():
b940d104 0a000044 00000001 00000001 00000038 01030401 fdc7c4b0 0000002c
010c0000 80040001 80010001 80020e10 80010002 00020004 00465000 80050007
80060100 8003000e 04000018 3eafd04d 837cec24 3ab9bf06 82cb0b6f b8182ce4
05000104 779b84ef 9c106976 e2dd3520 20929dd4 a6073037 417c513d d50cda25
79e5aba9 62a66718 86f9cf25 27d7d98e 056146f7 92e87823 644c689c 043ff109
4580a0ee 59cbec23 06ed1d0e fdbbce1f 896cd588 622bee94 368c89b9 7e0ba279
74516b8b fda493f5 0cfbbea4 7f1744f8 53eb73c2 1120608b 4af5300f eb712805
e8d0f62e 4edb9500 73e83027 c50a5113 d7051d09 e3f02682 526945ac 0bbf90aa
bad622a3 0feaf4f8 b4baa853 ca77557c 0c3685da f6edf307 ec0003f0 6d674d0e
9984a353 52b6555d 25c8e95d 1d71c51f af779aaf d9c8e4d7 31d07de6 fb499345
6c9c6f6e 46fb0d3e 30f5eedb 3686b022 a75d11ea e73d1424 c5ab9e1f 1eb9e815
9e040b4e 05000010 04000000 00000000 00000000 00000010 04000000 00000000
00000000
2014-05-27 13:51:43 [DEBUG]: algorithm.c:469:alg_oakley_hmacdef(): hmac(hmac_sha2_512)
2014-05-27 13:51:43 [DEBUG]: oakley.c:708:oakley_compute_hash1(): HASH computed:
2014-05-27 13:51:43 [DEBUG]: oakley.c:709:oakley_compute_hash1():
b7be03bd efa58771 daf4a893 df248544 5fb2a34c 8fa8f5bc 6b0ccf81 7d5cd0a1
1b15d554 7dc7de00 cf5e8f72 fda4a7e1 14120312 5db942fd 5710f835 0a2187fb
2014-05-27 13:51:43 [DEBUG]: ipsec_doi.c:1299:get_proppair(): total SA len=64
2014-05-27 13:51:43 [DEBUG]: ipsec_doi.c:1300:get_proppair():
00000001 00000001 00000038 01030401 fdc7c4b0 0000002c 010c0000 80040001
80010001 80020e10 80010002 00020004 00465000 80050007 80060100 8003000e
2014-05-27 13:51:43 [DEBUG]: ikev1.c:2843:isakmp_parsewoh(): begin.
2014-05-27 13:51:43 [DEBUG]: ikev1.c:2870:isakmp_parsewoh(): seen nptype=2(prop)
2014-05-27 13:51:43 [DEBUG]: ikev1.c:2909:isakmp_parsewoh(): succeed.
2014-05-27 13:51:43 [DEBUG]: ipsec_doi.c:1352:get_proppair(): proposal #1 len=56
2014-05-27 13:51:43 [DEBUG]: ikev1.c:2843:isakmp_parsewoh(): begin.
2014-05-27 13:51:43 [DEBUG]: ikev1.c:2870:isakmp_parsewoh(): seen nptype=3(trns)
2014-05-27 13:51:43 [DEBUG]: ikev1.c:2909:isakmp_parsewoh(): succeed.
2014-05-27 13:51:43 [DEBUG]: ipsec_doi.c:1498:get_transform(): transform #1 len=44
2014-05-27 13:51:43 [DEBUG]: ipsec_doi.c:2297:check_attr_ipsec(): type=Encryption Mode, flag=0x8000, lorv=Tunnel
2014-05-27 13:51:43 [DEBUG]: ipsec_doi.c:2297:check_attr_ipsec(): type=SA Life Type, flag=0x8000, lorv=seconds
2014-05-27 13:51:43 [DEBUG]: ipsec_doi.c:2297:check_attr_ipsec(): type=SA Life Duration, flag=0x8000, lorv=3600
2014-05-27 13:51:43 [DEBUG]: ipsec_doi.c:2412:check_attr_ipsec(): life duration was in TLV.
2014-05-27 13:51:43 [DEBUG]: ipsec_doi.c:2297:check_attr_ipsec(): type=SA Life Type, flag=0x8000, lorv=kilobytes
2014-05-27 13:51:43 [DEBUG]: ipsec_doi.c:2297:check_attr_ipsec(): type=SA Life Duration, flag=0x0000, lorv=4
2014-05-27 13:51:43 [DEBUG]: ipsec_doi.c:2297:check_attr_ipsec(): type=Authentication Algorithm, flag=0x8000, lorv=hmac-sha512
2014-05-27 13:51:43 [DEBUG]: ipsec_doi.c:2297:check_attr_ipsec(): type=Key Length, flag=0x8000, lorv=256
2014-05-27 13:51:43 [DEBUG]: ipsec_doi.c:2297:check_attr_ipsec(): type=Group Description, flag=0x8000, lorv=14
2014-05-27 13:51:43 [DEBUG]: algorithm.c:770:alg_oakley_dhdef(): dh(modp2048)
2014-05-27 13:51:43 [DEBUG]: ipsec_doi.c:1395:get_proppair(): pair 1:
2014-05-27 13:51:43 [DEBUG]: proposal.c:1124:print_proppair0(): 0x105a7bb8: next=(nil) tnext=(nil)
2014-05-27 13:51:43 [DEBUG]: ipsec_doi.c:1430:get_proppair(): proposal #1: 1 transform
2014-05-27 13:51:43 [DEBUG]: ipsec_doi.c:1128:get_ph2approval(): begin compare proposals.
2014-05-27 13:51:43 [DEBUG]: ipsec_doi.c:1134:get_ph2approval(): pair[1]: 0x105a7bb8
2014-05-27 13:51:43 [DEBUG]: proposal.c:1124:print_proppair0(): 0x105a7bb8: next=(nil) tnext=(nil)
2014-05-27 13:51:43 [DEBUG]: proposal.c:913:aproppair2saprop(): prop#=1 prot-id=ESP spi-size=4 #trns=1 trns#=1 trns-id=AES
2014-05-27 13:51:43 [DEBUG]: ipsec_doi.c:4165:ipsecdoi_t2satrns(): type=Encryption Mode, flag=0x8000, lorv=Tunnel
2014-05-27 13:51:43 [DEBUG]: ipsec_doi.c:4165:ipsecdoi_t2satrns(): type=SA Life Type, flag=0x8000, lorv=seconds
2014-05-27 13:51:43 [DEBUG]: ipsec_doi.c:4165:ipsecdoi_t2satrns(): type=SA Life Duration, flag=0x8000, lorv=3600
2014-05-27 13:51:43 [DEBUG]: ipsec_doi.c:4226:ipsecdoi_t2satrns(): lifetime 3600 seconds
2014-05-27 13:51:43 [DEBUG]: ipsec_doi.c:4165:ipsecdoi_t2satrns(): type=SA Life Type, flag=0x8000, lorv=kilobytes
2014-05-27 13:51:43 [DEBUG]: ipsec_doi.c:4165:ipsecdoi_t2satrns(): type=SA Life Duration, flag=0x0000, lorv=4
2014-05-27 13:51:43 [DEBUG]: ipsec_doi.c:4247:ipsecdoi_t2satrns(): lifesize 4608000 KB
2014-05-27 13:51:43 [DEBUG]: ipsec_doi.c:4165:ipsecdoi_t2satrns(): type=Authentication Algorithm, flag=0x8000, lorv=hmac-sha512
2014-05-27 13:51:43 [DEBUG]: ipsec_doi.c:4165:ipsecdoi_t2satrns(): type=Key Length, flag=0x8000, lorv=256
2014-05-27 13:51:43 [DEBUG]: ipsec_doi.c:4165:ipsecdoi_t2satrns(): type=Group Description, flag=0x8000, lorv=14
2014-05-27 13:51:43 [DEBUG]: ipsec_doi.c:1172:get_ph2approvalx(): peer's single bundle:
2014-05-27 13:51:43 [DEBUG]: proposal.c:1057:printsaproto(): (proto_id=ESP spisize=4 spi=fdc7c4b0 spi_p=00000000 encmode=Tunnel reqid=0:0)
2014-05-27 13:51:43 [DEBUG]: proposal.c:1091:printsatrns(): (trns_id=AES encklen=256 authtype=hmac-sha512)
2014-05-27 13:51:43 [DEBUG]: ipsec_doi.c:1175:get_ph2approvalx(): my single bundle:
2014-05-27 13:51:43 [DEBUG]: proposal.c:1057:printsaproto(): (proto_id=ESP spisize=4 spi=00000000 spi_p=00000000 encmode=Tunnel reqid=0:0)
2014-05-27 13:51:43 [DEBUG]: proposal.c:1091:printsatrns(): (trns_id=AES encklen=256 authtype=hmac-sha512)
2014-05-27 13:51:43 [DEBUG]: ipsec_doi.c:1194:get_ph2approvalx(): matched
2014-05-27 13:51:43 [DEBUG]: ikev1.c:1632:isakmp_ph2begin_r(): ===
2014-05-27 13:51:43 [DEBUG]: isakmp_quick.c:1306:quick_r1prep(): pfkey getspi sent.
2014-05-27 13:51:43 [DEBUG]: pfkey.c:696:pk_sendgetspi(): call pfkey_send_getspi
2014-05-27 13:51:43 [DEBUG]: pfkey.c:767:ikev1_getspi_response(): pfkey GETSPI succeeded: ESP/Tunnel 175.184.XXX.XXX[500]->122.152.XXX.XX[500] spi=2679721626(0x9fb94e9a)
2014-05-27 13:51:43 [DEBUG]: ipsec_doi.c:1299:get_proppair(): total SA len=64
2014-05-27 13:51:43 [DEBUG]: ipsec_doi.c:1300:get_proppair():
00000001 00000001 00000038 01030401 00000000 0000002c 010c0000 80040001
80010001 80020e10 80010002 00020004 00465000 80050007 80060100 8003000e
2014-05-27 13:51:43 [DEBUG]: ikev1.c:2843:isakmp_parsewoh(): begin.
2014-05-27 13:51:43 [DEBUG]: ikev1.c:2870:isakmp_parsewoh(): seen nptype=2(prop)
2014-05-27 13:51:43 [DEBUG]: ikev1.c:2909:isakmp_parsewoh(): succeed.
2014-05-27 13:51:43 [DEBUG]: ipsec_doi.c:1352:get_proppair(): proposal #1 len=56
2014-05-27 13:51:43 [DEBUG]: ikev1.c:2843:isakmp_parsewoh(): begin.
2014-05-27 13:51:43 [DEBUG]: ikev1.c:2870:isakmp_parsewoh(): seen nptype=3(trns)
2014-05-27 13:51:43 [DEBUG]: ikev1.c:2909:isakmp_parsewoh(): succeed.
2014-05-27 13:51:43 [DEBUG]: ipsec_doi.c:1498:get_transform(): transform #1 len=44
2014-05-27 13:51:43 [DEBUG]: ipsec_doi.c:2297:check_attr_ipsec(): type=Encryption Mode, flag=0x8000, lorv=Tunnel
2014-05-27 13:51:43 [DEBUG]: ipsec_doi.c:2297:check_attr_ipsec(): type=SA Life Type, flag=0x8000, lorv=seconds
2014-05-27 13:51:43 [DEBUG]: ipsec_doi.c:2297:check_attr_ipsec(): type=SA Life Duration, flag=0x8000, lorv=3600
2014-05-27 13:51:43 [DEBUG]: ipsec_doi.c:2412:check_attr_ipsec(): life duration was in TLV.
2014-05-27 13:51:43 [DEBUG]: ipsec_doi.c:2297:check_attr_ipsec(): type=SA Life Type, flag=0x8000, lorv=kilobytes
2014-05-27 13:51:43 [DEBUG]: ipsec_doi.c:2297:check_attr_ipsec(): type=SA Life Duration, flag=0x0000, lorv=4
2014-05-27 13:51:43 [DEBUG]: ipsec_doi.c:2297:check_attr_ipsec(): type=Authentication Algorithm, flag=0x8000, lorv=hmac-sha512
2014-05-27 13:51:43 [DEBUG]: ipsec_doi.c:2297:check_attr_ipsec(): type=Key Length, flag=0x8000, lorv=256
2014-05-27 13:51:43 [DEBUG]: ipsec_doi.c:2297:check_attr_ipsec(): type=Group Description, flag=0x8000, lorv=14
2014-05-27 13:51:43 [DEBUG]: algorithm.c:770:alg_oakley_dhdef(): dh(modp2048)
2014-05-27 13:51:43 [DEBUG]: ipsec_doi.c:1395:get_proppair(): pair 1:
2014-05-27 13:51:43 [DEBUG]: proposal.c:1124:print_proppair0(): 0x10597098: next=(nil) tnext=(nil)
2014-05-27 13:51:43 [DEBUG]: ipsec_doi.c:1430:get_proppair(): proposal #1: 1 transform
2014-05-27 13:51:43 [DEBUG]: algorithm.c:770:alg_oakley_dhdef(): dh(modp2048)
2014-05-27 13:51:43 [DEBUG]: ikev1.c:2260:set_isakmp_payload(): add payload of len 64, next type 10(nonce)
2014-05-27 13:51:43 [DEBUG]: ikev1.c:2260:set_isakmp_payload(): add payload of len 16, next type 4(ke)
2014-05-27 13:51:43 [DEBUG]: ikev1.c:2260:set_isakmp_payload(): add payload of len 256, next type 5(id)
2014-05-27 13:51:43 [DEBUG]: ikev1.c:2260:set_isakmp_payload(): add payload of len 12, next type 5(id)
2014-05-27 13:51:43 [DEBUG]: ikev1.c:2260:set_isakmp_payload(): add payload of len 12, next type 0(none)
2014-05-27 13:51:43 [DEBUG]: oakley.c:698:oakley_compute_hash1(): HASH with:
2014-05-27 13:51:43 [DEBUG]: oakley.c:699:oakley_compute_hash1():
b940d104 3eafd04d 837cec24 3ab9bf06 82cb0b6f b8182ce4 0a000044 00000001
00000001 00000038 01030401 9fb94e9a 0000002c 010c0000 80040001 80010001
80020e10 80010002 00020004 00465000 80050007 80060100 8003000e 04000014
387286dd cf384c7b 47b0c3c5 d609c7f8 05000104 e1402d0a 2dcc98a4 41dbfc1c
5ba32e51 27bea61e 51092aba 647c1e28 ea6a3867 4f8345e0 cd54fc66 077f674b
16dfe5b5 1d7724b2 16f43634 08547b96 8a278f66 8b1c2659 c34ee9ee ea0db751
52e9f59a 6b7ada30 1f16ab75 58f8aa11 82c6eb47 9f79fe61 d57f512c 7d9cc82b
2baae0b5 d1a0e0a9 1cfa871c 9ffd112b 0f39a3f0 6fd6b6fe 2cfe3bdf 273d905d
3f411ea8 045db4cf 3553a34a 7c79eaf5 fb4365d2 1431d969 3dd86643 81a708d6
d44b98f4 f589c523 8ff75530 5c842fa8 b76f5812 5eb45da0 60a85f08 248c5e80
147846f9 58466c4c 9ea4ab2a cc690bd6 9b32e359 3e39afaf 01031ef7 d3428265
70e6372d 7700131b 53adc46b 25334f6e 6bf4c9f3 05000010 04000000 00000000
00000000 00000010 04000000 00000000 00000000
2014-05-27 13:51:43 [DEBUG]: algorithm.c:469:alg_oakley_hmacdef(): hmac(hmac_sha2_512)
2014-05-27 13:51:43 [DEBUG]: oakley.c:708:oakley_compute_hash1(): HASH computed:
2014-05-27 13:51:43 [DEBUG]: oakley.c:709:oakley_compute_hash1():
e0bad1ec 90da1773 f220fcb1 81c35c1e 275b4549 38797764 6d6e5085 ebf6c24d
a95e30bf c4d1004e 4c490267 fd878ae4 f34628af 0f1bf497 24892409 3e109a04
2014-05-27 13:51:43 [DEBUG]: ikev1.c:2260:set_isakmp_payload(): add payload of len 64, next type 1(sa)
2014-05-27 13:51:43 [DEBUG]: oakley.c:4017:oakley_do_encrypt(): begin encryption.
2014-05-27 13:51:43 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-05-27 13:51:43 [DEBUG]: oakley.c:4033:oakley_do_encrypt(): pad length = 16
2014-05-27 13:51:43 [DEBUG]: oakley.c:4063:oakley_do_encrypt():
01000044 e0bad1ec 90da1773 f220fcb1 81c35c1e 275b4549 38797764 6d6e5085
ebf6c24d a95e30bf c4d1004e 4c490267 fd878ae4 f34628af 0f1bf497 24892409
3e109a04 0a000044 00000001 00000001 00000038 01030401 9fb94e9a 0000002c
010c0000 80040001 80010001 80020e10 80010002 00020004 00465000 80050007
80060100 8003000e 04000014 387286dd cf384c7b 47b0c3c5 d609c7f8 05000104
e1402d0a 2dcc98a4 41dbfc1c 5ba32e51 27bea61e 51092aba 647c1e28 ea6a3867
4f8345e0 cd54fc66 077f674b 16dfe5b5 1d7724b2 16f43634 08547b96 8a278f66
8b1c2659 c34ee9ee ea0db751 52e9f59a 6b7ada30 1f16ab75 58f8aa11 82c6eb47
9f79fe61 d57f512c 7d9cc82b 2baae0b5 d1a0e0a9 1cfa871c 9ffd112b 0f39a3f0
6fd6b6fe 2cfe3bdf 273d905d 3f411ea8 045db4cf 3553a34a 7c79eaf5 fb4365d2
1431d969 3dd86643 81a708d6 d44b98f4 f589c523 8ff75530 5c842fa8 b76f5812
5eb45da0 60a85f08 248c5e80 147846f9 58466c4c 9ea4ab2a cc690bd6 9b32e359
3e39afaf 01031ef7 d3428265 70e6372d 7700131b 53adc46b 25334f6e 6bf4c9f3
05000010 04000000 00002014-05-27 13:51:43 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-05-27 13:51:43 [DEBUG]: oakley.c:4073:oakley_do_encrypt(): with key:
2014-05-27 13:51:43 [DEBUG]: oakley.c:4074:oakley_do_encrypt():
97ce00c8 5f714f8a a13a1bb9 9898eaf0 e204f110 4144f29b 52e58c88 c8b2597f
2014-05-27 13:51:43 [DEBUG]: oakley.c:4079:oakley_do_encrypt(): encrypted payload by IV:
2014-05-27 13:51:43 [DEBUG]: oakley.c:4080:oakley_do_encrypt():
4abe1bbd accdd8e6 14f44f61 2cb174da
2014-05-27 13:51:43 [DEBUG]: oakley.c:4086:oakley_do_encrypt(): save IV for next:
2014-05-27 13:51:43 [DEBUG]: oakley.c:4087:oakley_do_encrypt():
964778c0 07b90c44 c71c1768 c01d78ef
2014-05-27 13:51:43 [DEBUG]: oakley.c:4103:oakley_do_encrypt(): encrypted.
2014-05-27 13:51:43 [DEBUG]: ikev1.c:1759:isakmp_ph2resend(): resend phase2 packet 145d0809f142b7d7:e9f6b28036b395b8:B940D104
2014-05-27 13:51:43 [DEBUG]: ikev1.c:2990:isakmp_send(): 492 bytes from 122.152.XXX.XX[500] to 175.184.XXX.XXX[500]
2014-05-27 13:51:43 [DEBUG]: sockmisc.c:336:sendfromto(): sockname 122.152.XXX.XX[500]
2014-05-27 13:51:43 [DEBUG]: sockmisc.c:338:sendfromto(): send packet from 122.152.XXX.XX[500]
2014-05-27 13:51:43 [DEBUG]: sockmisc.c:340:sendfromto(): send packet to 175.184.XXX.XXX[500]
2014-05-27 13:51:43 [DEBUG]: sockmisc.c:525:sendfromto(): 1 times of 492 bytes message will be sent to 175.184.XXX.XXX[500]
2014-05-27 13:51:43 [DEBUG]: sockmisc.c:529:sendfromto():
145d0809 f142b7d7 e9f6b280 36b395b8 08102001 b940d104 000001ec abfae145
8f7fbfac be5de3d8 52f5f58b 5cf09b64 ea47975c 537f5290 e44a50b5 6e86b2d3
1ad08865 cbe8e4b1 1ff833e2 bed2eea6 8e3bf1ef 47c87af4 0b752c1b 328d1b6a
fa8a6630 62e120fe 6682a9a3 0cef3b96 7d4e641d 27ac3e85 3be8d218 52f667f3
8899b3b6 ae02274c d90b812b d0b43859 0cba9e98 4993c35c 5bb81710 42969426
96b786f6 ad20623b f1d4613a 1e398c79 a0fe74d3 3f48dda7 d0a9a70d 6aa2b04b
9eb70d3b ec158b49 7c9d8cef 68bdfdf7 aa716e43 539dc90f 0a050552 ffc87cdf
9de6d8f0 2066635f 285ba5a2 7c484ed4 72f9865c 7c8dc223 6fb994e0 7c034d7e
6f10acb5 5bbce145 13fb54dc 2e3171d4 8538357a 17532626 9502cb83 5c3c647f
449606b9 cde80190 cf01b570 ac5599ab e5a1d131 957b78a8 c104f456 e1c31c0d
a669c05a 6598489d 70ec45e0 d7bc0abc 64b473fe 3b841941 8eee4b2a c7aa4589
5fd8e6db 8b4c021a 4ac2c170 1d265cb8 8965f6e8 542e54cd 96e4a313 34f15c8d
e002aace 64c07059 8008f8c8 99c4ff90 67474f2a df607055 c876feb8 21b7439d
beccf8e8 3d04f088 631f7629 22014-05-27 13:51:43 [DEBUG]: pfkey.c:722:pk_sendgetspi(): pfkey GETSPI sent: ESP/Tunnel 0.0.0.0[500]->122.152.XXX.XX[500]
2014-05-27 13:51:43 [DEBUG]: isakmp.c:982:isakmp_handler(): ===
2014-05-27 13:51:43 [DEBUG]: isakmp.c:983:isakmp_handler(): 108 bytes message received from 175.184.XXX.XXX[500]
2014-05-27 13:51:43 [DEBUG]: isakmp.c:986:isakmp_handler():
145d0809 f142b7d7 e9f6b280 36b395b8 08102001 b940d104 0000006c e035bfe6
66896dce 6b209c1d 3da4b305 ca0d8dc0 4b42654f 0041f4ff e331c9a2 012bdb22
2d3e31cb 2df5ac4e 6105689c 77594d68 337e5796 65b4451b 445b9831 b8b2cf23
db5f8d75 a05d4cfc 3bb72e39
2014-05-27 13:51:43 [DEBUG]: oakley.c:3892:oakley_do_decrypt(): begin decryption.
2014-05-27 13:51:43 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-05-27 13:51:43 [DEBUG]: oakley.c:3906:oakley_do_decrypt(): IV was saved for next processing:
2014-05-27 13:51:43 [DEBUG]: oakley.c:3908:oakley_do_decrypt():
b8b2cf23 db5f8d75 a05d4cfc 3bb72e39
2014-05-27 13:51:43 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-05-27 13:51:43 [DEBUG]: oakley.c:3931:oakley_do_decrypt(): with key:
2014-05-27 13:51:43 [DEBUG]: oakley.c:3932:oakley_do_decrypt():
97ce00c8 5f714f8a a13a1bb9 9898eaf0 e204f110 4144f29b 52e58c88 c8b2597f
2014-05-27 13:51:43 [DEBUG]: oakley.c:3937:oakley_do_decrypt(): decrypted payload by IV:
2014-05-27 13:51:43 [DEBUG]: oakley.c:3938:oakley_do_decrypt():
964778c0 07b90c44 c71c1768 c01d78ef
2014-05-27 13:51:43 [DEBUG]: oakley.c:3940:oakley_do_decrypt(): decrypted payload, but not trimed.
2014-05-27 13:51:43 [DEBUG]: oakley.c:3942:oakley_do_decrypt():
00000044 93c5402c 8b2a6b1f de37531d 7f309941 7855f566 bd19d673 59c5ab81
fdd70412 68c21815 5dad5523 c70ff2d7 f06754f6 40561b18 2d67db16 5c5f8038
dcf1b337 00000000 00000000 00000000
2014-05-27 13:51:43 [DEBUG]: oakley.c:3951:oakley_do_decrypt(): padding len=0
2014-05-27 13:51:43 [DEBUG]: oakley.c:3982:oakley_do_decrypt(): decrypted.
2014-05-27 13:51:43 [DEBUG]: oakley.c:3983:oakley_do_decrypt():
145d0809 f142b7d7 e9f6b280 36b395b8 08102001 b940d104 0000006c 00000044
93c5402c 8b2a6b1f de37531d 7f309941 7855f566 bd19d673 59c5ab81 fdd70412
68c21815 5dad5523 c70ff2d7 f06754f6 40561b18 2d67db16 5c5f8038 dcf1b337
00000000 00000000 00000000
2014-05-27 13:51:43 [DEBUG]: ikev1.c:2843:isakmp_parsewoh(): begin.
2014-05-27 13:51:43 [DEBUG]: ikev1.c:2870:isakmp_parsewoh(): seen nptype=8(hash)
2014-05-27 13:51:43 [DEBUG]: ikev1.c:2909:isakmp_parsewoh(): succeed.
2014-05-27 13:51:43 [DEBUG]: isakmp_quick.c:1604:quick_r3recv(): HASH(3) validate:2014-05-27 13:51:43 [DEBUG]: isakmp_quick.c:1605:quick_r3recv():
93c5402c 8b2a6b1f de37531d 7f309941 7855f566 bd19d673 59c5ab81 fdd70412
68c21815 5dad5523 c70ff2d7 f06754f6 40561b18 2d67db16 5c5f8038 dcf1b337
2014-05-27 13:51:43 [DEBUG]: oakley.c:642:oakley_compute_hash3(): HASH with:
2014-05-27 13:51:43 [DEBUG]: oakley.c:643:oakley_compute_hash3():
00b940d1 043eafd0 4d837cec 243ab9bf 0682cb0b 6fb8182c e4387286 ddcf384c
7b47b0c3 c5d609c7 f8
2014-05-27 13:51:43 [DEBUG]: algorithm.c:469:alg_oakley_hmacdef(): hmac(hmac_sha2_512)
2014-05-27 13:51:43 [DEBUG]: oakley.c:652:oakley_compute_hash3(): HASH computed:
2014-05-27 13:51:43 [DEBUG]: oakley.c:653:oakley_compute_hash3():
93c5402c 8b2a6b1f de37531d 7f309941 7855f566 bd19d673 59c5ab81 fdd70412
68c21815 5dad5523 c70ff2d7 f06754f6 40561b18 2d67db16 5c5f8038 dcf1b337
2014-05-27 13:51:43 [DEBUG]: ikev1.c:1136:quick_main(): ===
2014-05-27 13:51:43 [DEBUG]: oakley.c:407:oakley_compute_keymat_x(): KEYMAT compute with
2014-05-27 13:51:43 [DEBUG]: oakley.c:408:oakley_compute_keymat_x():
586c803e 8a25a3fc dbde67bf f9f3f8ca 11fcf226 b97ebdf6 2590f5f2 f2d77625
e0b8c508 e40ed2bb b2dc18bf 810b40fe a0f7372e fad257af 9704895c a75220a2
7336eb43 1fdcd664 f21313a2 086e2f09 2d964811 b8bed111 6a7b1ef7 dae68c35
417b4edf 822c9a13 306972b6 9d235d54 525bb6ea 336c3418 f9a02d4d a6961204
ffdfb139 ff7a94c1 5d50f1e5 54a3fedc 18c8a104 6230e567 90b4c0f2 211b4fd0
a383bb3f 26e210ae 4ce83f1c c9429ebe e5e40a2d 85a941dc 29277d7a 962be086
1ac59c78 8f6c87c5 f25cd40a 44e2624a fe10d6c2 5af2874e f5e1e821 5e48ab50
79b55a79 7c4a4558 c870c614 5059af27 1cf8d976 064bf229 8ca8ee02 01bc7db2
039fb94e 9a3eafd0 4d837cec 243ab9bf 0682cb0b 6fb8182c e4387286 ddcf384c
7b47b0c3 c5d609c7 f8
2014-05-27 13:51:43 [DEBUG]: algorithm.c:469:alg_oakley_hmacdef(): hmac(hmac_sha2_512)
2014-05-27 13:51:43 [DEBUG]: algorithm.c:669:alg_ipsec_encdef(): encryption(aes)
2014-05-27 13:51:43 [DEBUG]: algorithm.c:712:alg_ipsec_hmacdef(): hmac(null)
2014-05-27 13:51:43 [DEBUG]: oakley.c:440:oakley_compute_keymat_x(): encklen=256 authklen=512
2014-05-27 13:51:43 [DEBUG]: oakley.c:447:oakley_compute_keymat_x(): generating 1536 bits of key (dupkeymat=3)
2014-05-27 13:51:43 [DEBUG]: oakley.c:465:oakley_compute_keymat_x(): generating K1...K3 for KEYMAT.
2014-05-27 13:51:43 [DEBUG]: algorithm.c:469:alg_oakley_hmacdef(): hmac(hmac_sha2_512)
2014-05-27 13:51:43 [DEBUG]: algorithm.c:469:alg_oakley_hmacdef(): hmac(hmac_sha2_512)
2014-05-27 13:51:43 [DEBUG]: oakley.c:526:oakley_compute_keymat_x():
615e859b e2851d1d 8fedb0ba 66ff111a 6d72bc32 216877c0 86f52832 c47404c9
8cccbcdc bf21309e d3f15f84 8ede06c4 b064ccfe f178d00d 5beac694 41a2625e
65152001 8663b589 19da562f 832670ea 3975fd07 96c681ad f6a61925 992feab9
45e73dd6 cb9b21d9 ef55e76d 88953bc7 7595134c ea97761d 77d1c50e 0ea0f67a
0f695343 39fd70e0 1f6557c7 16757e88 1566652e 235f5e89 c4f54827 56261c5a
e03a6aaa 22adc039 239c1ef4 bdee3a8b bad3c598 b8b0a01c f4c1f35d a545125e
2014-05-27 13:51:43 [DEBUG]: oakley.c:407:oakley_compute_keymat_x(): KEYMAT compute with
2014-05-27 13:51:43 [DEBUG]: oakley.c:408:oakley_compute_keymat_x():
586c803e 8a25a3fc dbde67bf f9f3f8ca 11fcf226 b97ebdf6 2590f5f2 f2d77625
e0b8c508 e40ed2bb b2dc18bf 810b40fe a0f7372e fad257af 9704895c a75220a2
7336eb43 1fdcd664 f21313a2 086e2f09 2d964811 b8bed111 6a7b1ef7 dae68c35
417b4edf 822c9a13 306972b6 9d235d54 525bb6ea 336c3418 f9a02d4d a6961204
ffdfb139 ff7a94c1 5d50f1e5 54a3fedc 18c8a104 6230e567 90b4c0f2 211b4fd0
a383bb3f 26e210ae 4ce83f1c c9429ebe e5e40a2d 85a941dc 29277d7a 962be086
1ac59c78 8f6c87c5 f25cd40a 44e2624a fe10d6c2 5af2874e f5e1e821 5e48ab50
79b55a79 7c4a4558 c870c614 5059af27 1cf8d976 064bf229 8ca8ee02 01bc7db2
03fdc7c4 b03eafd0 4d837cec 243ab9bf 0682cb0b 6fb8182c e4387286 ddcf384c
7b47b0c3 c5d609c7 f8
2014-05-27 13:51:43 [DEBUG]: algorithm.c:469:alg_oakley_hmacdef(): hmac(hmac_sha2_512)
2014-05-27 13:51:43 [DEBUG]: algorithm.c:669:alg_ipsec_encdef(): encryption(aes)
2014-05-27 13:51:43 [DEBUG]: algorithm.c:712:alg_ipsec_hmacdef(): hmac(null)
2014-05-27 13:51:43 [DEBUG]: oakley.c:440:oakley_compute_keymat_x(): encklen=256 authklen=512
2014-05-27 13:51:43 [DEBUG]: oakley.c:447:oakley_compute_keymat_x(): generating 1536 bits of key (dupkeymat=3)
2014-05-27 13:51:43 [DEBUG]: oakley.c:465:oakley_compute_keymat_x(): generating K1...K3 for KEYMAT.
2014-05-27 13:51:43 [DEBUG]: algorithm.c:469:alg_oakley_hmacdef(): hmac(hmac_sha2_512)
2014-05-27 13:51:43 [DEBUG]: algorithm.c:469:alg_oakley_hmacdef(): hmac(hmac_sha2_512)
2014-05-27 13:51:43 [DEBUG]: oakley.c:526:oakley_compute_keymat_x():
51a89fb3 9abeaa15 90b5123f e344f5b8 aa6d4a60 60f53bce e80ae76d 86050c74
2c52d064 78498b47 c3569c37 84e0f59a e19af447 60357bdd 2533dadc e06508a5
3ad41e56 e83204a8 cb6fb021 972c46de 1fea8211 5de90b84 4cb1cb35 d38aa763
16216c20 e3a54b2e 93a2ae75 a9405da6 21b95dae f0a3e1ad bd2dc274 671cf9e0
3c357437 e0427c2a 1e045182 636d4138 1f559612 c53a07e3 7e3bc8d7 c69cbaee
2dd960a7 6ee4af35 85adc895 5f39bf63 163fd9e6 b3771a4c 12b5adb8 39102693
2014-05-27 13:51:43 [DEBUG]: oakley.c:335:oakley_compute_keymat(): KEYMAT computed.
2014-05-27 13:51:43 [PROTO_NOTIFY]: ikev1.c:2560:log_ph2established(): ====> PHASE-2 NEGOTIATION SUCCEEDED AS RESPONDER, (QUICK MODE) <====
====> Established SA: 122.152.XXX.XX[500]-175.184.XXX.XXX[500] message id:0xB940D104, SPI:0x9FB94E9A/0xFDC7C4B0 <====
2014-05-27 13:51:43 [DEBUG]: isakmp_quick.c:1824:quick_r3prep(): call pk_sendupdate
2014-05-27 13:51:43 [DEBUG]: algorithm.c:669:alg_ipsec_encdef(): encryption(aes)
2014-05-27 13:51:43 [DEBUG]: algorithm.c:712:alg_ipsec_hmacdef(): hmac(null)
2014-05-27 13:51:43 [INFO]: ike_pfkey.c:339:sadb_log_add(): SADB_UPDATE ul_proto=255 src=175.184.XXX.XXX[500] dst=122.152.XXX.XX[500] satype=ESP samode=tunl spi=0x9FB94E9A authtype=SHA512 enctype=AES256 lifetime soft time=3600 bytes=4718
592000 hard time=3600 bytes=4718592000
2014-05-27 13:51:43 [DEBUG]: isakmp_quick.c:1829:quick_r3prep(): pfkey update sent.
2014-05-27 13:51:43 [DEBUG]: algorithm.c:669:alg_ipsec_encdef(): encryption(aes)
2014-05-27 13:51:43 [DEBUG]: algorithm.c:712:alg_ipsec_hmacdef(): hmac(null)
2014-05-27 13:51:43 [INFO]: ike_pfkey.c:339:sadb_log_add(): SADB_ADD ul_proto=255 src=122.152.XXX.XX[500] dst=175.184.XXX.XXX[500] satype=ESP samode=tunl spi=0xFDC7C4B0 authtype=SHA512 enctype=AES256 lifetime soft time=3600 bytes=4718592
000 hard time=3600 bytes=4718592000
2014-05-27 13:51:43.409 +0200 debug: ifmon_request_put(daemon/panike_sysd_if.c:916): 16 write to pipe: keymirror_add
2014-05-27 13:51:43 [DEBUG]: pfkey.c:1182:ikev1_update_response(): pfkey UPDATE succeeded: ESP/Tunnel 175.184.XXX.XXX[500]->122.152.XXX.XX[500] spi=2679721626(0x9fb94e9a)
2014-05-27 13:51:43 [INFO]: pfkey.c:1187:ikev1_update_response(): IPsec-SA established: ESP/Tunnel 175.184.XXX.XXX[500]->122.152.XXX.XX[500] spi=2679721626(0x9fb94e9a)
2014-05-27 13:51:43 [PROTO_NOTIFY]: ikev1.c:2609:log_ipseckeyinstalled(): ====> IPSEC KEY INSTALLATION SUCCEEDED <====
====> Installed SA: 122.152.XXX.XX[500]-175.184.XXX.XXX[500] SPI:0x9FB94E9A/0xFDC7C4B0 lifetime 3600 Sec lifesize 4608000 KB <====
2014-05-27 13:51:43 [DEBUG]: isakmp_quick.c:1836:quick_r3prep(): pfkey add sent.
2014-05-27 13:51:43.415 +0200 debug: ifmon_request_get(daemon/panike_sysd_if.c:932): 16 read from pipe, msg type 4
2014-05-27 13:51:43.415 +0200 debug: pan_msg_process(daemon/panike_sysd_if.c:1030): request from pipe: keymirror_add
2014-05-27 13:51:43 [INFO]: keymgr_keymirror.c:83:ike_do_keymirror_add(): keymirror add start ++++++++++++++++
2014-05-27 13:51:43.415 +0200 debug: keymgr_keydb_insert(ikemgr/keymgr_db.c:108): keymgr: key insert called for tid:7
2014-05-27 13:51:43 [INFO]: keymgr_keymirror.c:87:ike_do_keymirror_add(): keymirror add for gw 6, tn 7, selfSPI 9FB94E9A, retcode 0.
2014-05-27 13:51:44.099 +0200 debug: ifmon_request_put(daemon/panike_sysd_if.c:916): 16 write to pipe: keymirror_del
2014-05-27 13:51:44.100 +0200 debug: ifmon_request_get(daemon/panike_sysd_if.c:932): 16 read from pipe, msg type 5
2014-05-27 13:51:44.100 +0200 debug: pan_msg_process(daemon/panike_sysd_if.c:1030): request from pipe: keymirror_del
2014-05-27 13:51:44 [INFO]: keymgr_keymirror.c:125:ike_do_keymirror_del(): keymirror del start ----------------
2014-05-27 13:51:44 [INFO]: keymgr_keymirror.c:130:ike_do_keymirror_del(): keymirror del for gw 6, tn 7, selfSPI B255F30F, retcode 0.
2014-05-27 13:51:44 [DEBUG]: handler.c:1710:remove_ph2(): Deleting a Ph2... status 9
2014-05-27 13:51:44 [DEBUG]: oakley.c:3811:oakley_newiv2(): compute IV for phase2
2014-05-27 13:51:44 [DEBUG]: oakley.c:3812:oakley_newiv2(): phase1 last IV:
2014-05-27 13:51:44 [DEBUG]: oakley.c:3813:oakley_newiv2():
dfc5ede0 0f13942d fec6b0e9 c729bc43 f5deef46
2014-05-27 13:51:44 [DEBUG]: algorithm.c:386:alg_oakley_hashdef(): hash(sha512)
2014-05-27 13:51:44 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-05-27 13:51:44 [DEBUG]: oakley.c:3846:oakley_newiv2(): phase2 IV computed:
2014-05-27 13:51:44 [DEBUG]: oakley.c:3847:oakley_newiv2():
d9c2329e 16054b7a 9f6a8ed8 5d5be2e1
2014-05-27 13:51:44 [DEBUG]: oakley.c:698:oakley_compute_hash1(): HASH with:
2014-05-27 13:51:44 [DEBUG]: oakley.c:699:oakley_compute_hash1():
f5deef46 00000010 00000001 03040001 b255f30f
2014-05-27 13:51:44 [DEBUG]: algorithm.c:469:alg_oakley_hmacdef(): hmac(hmac_sha2_512)
2014-05-27 13:51:44 [DEBUG]: oakley.c:708:oakley_compute_hash1(): HASH computed:
2014-05-27 13:51:44 [DEBUG]: oakley.c:709:oakley_compute_hash1():
f59bfe8c 35a4b8a8 85e5035b 418e38ee d3e206f2 84bbd907 473b6b5c f59fdadd
c85d504f 920da931 d3476a75 ed46c4fb 76283738 c489ee91 18bc35a7 6ca181c5
2014-05-27 13:51:44 [DEBUG]: oakley.c:4017:oakley_do_encrypt(): begin encryption.
2014-05-27 13:51:44 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-05-27 13:51:44 [DEBUG]: oakley.c:4033:oakley_do_encrypt(): pad length = 12
2014-05-27 13:51:44 [DEBUG]: oakley.c:4063:oakley_do_encrypt():
0c000044 f59bfe8c 35a4b8a8 85e5035b 418e38ee d3e206f2 84bbd907 473b6b5c
f59fdadd c85d504f 920da931 d3476a75 ed46c4fb 76283738 c489ee91 18bc35a7
6ca181c5 00000010 00000001 03040001 b255f30f d7784e92 5c4e0226 b7bf140c
2014-05-27 13:51:44 [DEBUG]: algorithm.c:529:alg_oakley_encdef(): encryption(aes)
2014-05-27 13:51:44 [DEBUG]: oakley.c:4073:oakley_do_encrypt(): with key:
2014-05-27 13:51:44 [DEBUG]: oakley.c:4074:oakley_do_encrypt():
97ce00c8 5f714f8a a13a1bb9 9898eaf0 e204f110 4144f29b 52e58c88 c8b2597f
2014-05-27 13:51:44 [DEBUG]: oakley.c:4079:oakley_do_encrypt(): encrypted payload by IV:
2014-05-27 13:51:44 [DEBUG]: oakley.c:4080:oakley_do_encrypt():
d9c2329e 16054b7a 9f6a8ed8 5d5be2e1
2014-05-27 13:51:44 [DEBUG]: oakley.c:4086:oakley_do_encrypt(): save IV for next:
2014-05-27 13:51:44 [DEBUG]: oakley.c:4087:oakley_do_encrypt():
74bfc887 5f0b2df9 09bf2f66 6d6a60ed
2014-05-27 13:51:44 [DEBUG]: oakley.c:4103:oakley_do_encrypt(): encrypted.
2014-05-27 13:51:44 [DEBUG]: ikev1.c:2990:isakmp_send(): 124 bytes from 122.152.XXX.XX[500] to 175.184.XXX.XXX[500]
2014-05-27 13:51:44 [DEBUG]: sockmisc.c:336:sendfromto(): sockname 122.152.XXX.XX[500]
2014-05-27 13:51:44 [DEBUG]: sockmisc.c:338:sendfromto(): send packet from 122.152.XXX.XX[500]
2014-05-27 13:51:44 [DEBUG]: sockmisc.c:340:sendfromto(): send packet to 175.184.XXX.XXX[500]
2014-05-27 13:51:44 [DEBUG]: sockmisc.c:525:sendfromto(): 1 times of 124 bytes message will be sent to 175.184.XXX.XXX[500]
2014-05-27 13:51:44 [DEBUG]: sockmisc.c:529:sendfromto():
145d0809 f142b7d7 e9f6b280 36b395b8 08100501 f5deef46 0000007c 86fe2a98
fd597097 9fec3f35 df039276 d08f05a8 8e8c2b3f 2169016b 804ae135 b444b13e
fa29352c f073c9aa 8818a667 3d557186 bc0c8c29 bf420e7c f7a8acfe 8043f286
d1535c44 7e6d3b05 9303acd7 74bfc887 5f0b2df9 09bf2f66 6d6a60ed
2014-05-27 13:51:44 [DEBUG]: isakmp_inf.c:805:isakmp_info_send_common(): sendto Information delete.
2014-05-27 13:51:44 [DEBUG]: oakley.c:3871:oakley_delivm(): IV freed
2014-05-27 13:51:44 [PROTO_NOTIFY]: ikev1.c:2632:log_ipseckeydeleted(): ====> IPSEC KEY DELETED <====
====> Deleted SA: 122.152.XXX.XX[500]-175.184.XXX.XXX[500] SPI:0xB255F30F/0xFDAC699A <====
2014-05-27 13:51:44 [INFO]: ike_pfkey.c:446:sadb_delete(): SADB_DELETE ul_proto=0 src=122.152.XXX.XX[500] dst=175.184.XXX.XXX[500] satype=ESP spi=0xB255F30F
2014-05-27 13:51:44 [INFO]: ike_pfkey.c:693:sadb_delete_callback(): received PFKEY_DELETE seq=0 satype=ESP spi=0xB255F30F
2014-05-27 13:51:44 [DEBUG]: oakley.c:3871:oakley_delivm(): IV freed
2014-05-27 13:51:47.083 +0200 debug: ifmon_request_put(daemon/panike_sysd_if.c:916): 16 write to pipe: keyacquire
2014-05-27 13:51:47.083 +0200 debug: ifmon_request_get(daemon/panike_sysd_if.c:932): 16 read from pipe, msg type 3
2014-05-27 13:51:47.083 +0200 debug: pan_msg_process(daemon/panike_sysd_if.c:1030): request from pipe: keyacquire
2014-05-27 13:51:47 [DEBUG]: if_spmd.c:912:parserep_slid(): SLID ok: 250 Tunnel-to-MEL1A(Gateway-MEL1A)_out
2014-05-27 13:51:47 [INFO]: ikev1.c:710:ikev1_initiate(): 0:122.152.XXX.XX[0] - 0.0.0.0[0]:(nil):remote Gateway-MEL1A passive mode specified for IKEv1, dropping acquire request
thank you in advance.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-27-2014 06:04 AM
It looks like something sends the request to delete the SA:
2014-05-27 13:51:44 [DEBUG]: isakmp_inf.c:805:isakmp_info_send_common(): sendto Information delete.
Could you try to capture the IKE packets with "debug ike pcap on"?
You can look into the file with "debug ike pcap view" or export it via tftp/scp and look into it wiht wireshark for more information.
How much traffic goes through the tunnel? The lifetime is pretty big but if someone sends an image or bigger files over the tunnel it could be the reason. Did you create the tunnel?
- 17260 Views
- 24 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- PA1420 IKE packet disappear between receive (ingress) and firewall session state in General Topics
- Prisma Access Service Connection to Palo Alto FW in HA-AA in Prisma Access Discussions
- Geo blocking after GP login in GlobalProtect Discussions
- Playbook stuck after upgrade in Cortex XSOAR Discussions
- Management IP address is getting changed in Panorama Discussions