- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Zone Protection - to or from
- LIVEcommunity
- Discussions
- General Topics
- Re: Zone Protection - to or from
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-12-2018 01:11 PM
When you say specifically ingress do you mean it should be applied to ingress zones like the outside? And the DMZ is considered internal by the PA? We first started out by putting zone protection on the DMZ and it showed our external DNS (in the DMZ) servers in scanning (alerting on host sweep) out to the internet/outside for DNS. I had been looking for it to alert on traffic coming into the DMZ not the other way around. Have I got something configured incorrectly on my profile? I have taken the zone protection off of the DMZ and put it on the outside Zone instead
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-12-2018 02:04 PM
It will be traffic ingressing the specified zone. For example my 'outside/untrust' zone would be the ingress interface for everything shown under ( zone.src eq outside ) on my firewall. All of this traffic would count towards the zone protection profile allocated to the 'outside' zone.
For most situations if you are trying to protect your resources in the DMZ you would want the zone protection profile on your 'outside/untrust' zone. When traffic comes into the firewall the ingress zone is going to be 'outside/untrust', and the egress zone is going to be the 'dmz'.
An easier way of thinking of it would be like this:
ingress: The same as from or source.
egress: Same as to or destination.
Currently your configuration should be correct. If the zone protection is on the 'outside' zone it will protect your dmz resources from external traffic/attacks.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-13-2018 10:35 AM
Just so it's not lost in all of this. While Zone Protection will help the firewall keep the zone up and going and should protect from external users flooding your firewall with requests that could make it hit it's limits, it's also extremely important to protect public services living in your DMZ with a DoS Protection Profile.
Without a DoS Protection Profile assigned to a public facing device you could easily run into issues with an attacker flooding your web server or public DNS server and have then bring it down from a flood attack long before the limits for a Zone Protection profile are even close to triggering in most enviroments. This is why I always call Zone Protection 'Last Resort'. The DoS Protection profiles should prevent everything but a very large attack from ever getting the chance to trigger your Zone Protection 'Activate' or 'Maximum' values.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-15-2018 05:35 AM - edited 01-15-2018 05:37 AM
So it would be better to start with DoS protection around our DNS servers in the DMZ and then add Zone protection later? Is there a way to "whitelist" IP addresses that are related to our external DNS servers in the DMZ?
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-15-2018 05:38 AM
Correct. I would start with DoS profiles around public facing DMZ servers and then move towards Zone Protection once DoS profiles are properly configured.
You can whitelist addresses within DoS profiles by using the 'negate' option when you actually build out the DoS Policies. While I know there is a feature request for it, there is not currently a way to exclude addresses from Zone Protection profiles.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-15-2018 05:40 AM
"All of this traffic would count towards the zone protection profile allocated to the 'outside' zone." So I am correct in assuming that the zone protection profile cannot really tell which direction the traffic is going necessarily, it has more to do with the zone that you apply the zone protection too
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-15-2018 06:03 AM
Right, the ZP profile doesn't really care about ingress or egress. As long as it passes that zone and doesn't already have an active session on the session table it'll be evaluated by the ZP profile.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-15-2018 08:38 AM
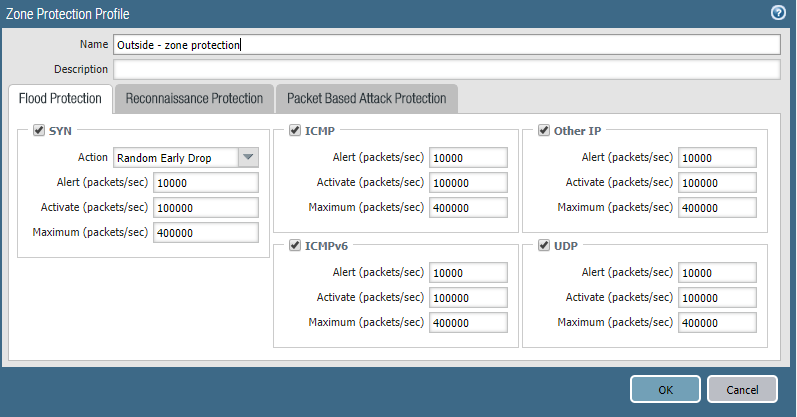
The activate and maximum values you would want to start artificially high, something you’ll know will never actually trigger. The alarm value is simply going to register an alert in the logs, so this you can set to pretty much anything to start off with.
The alerts generated by the alarm value will let you electively baseline what your activate and maximum values should be.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-17-2018 05:28 AM
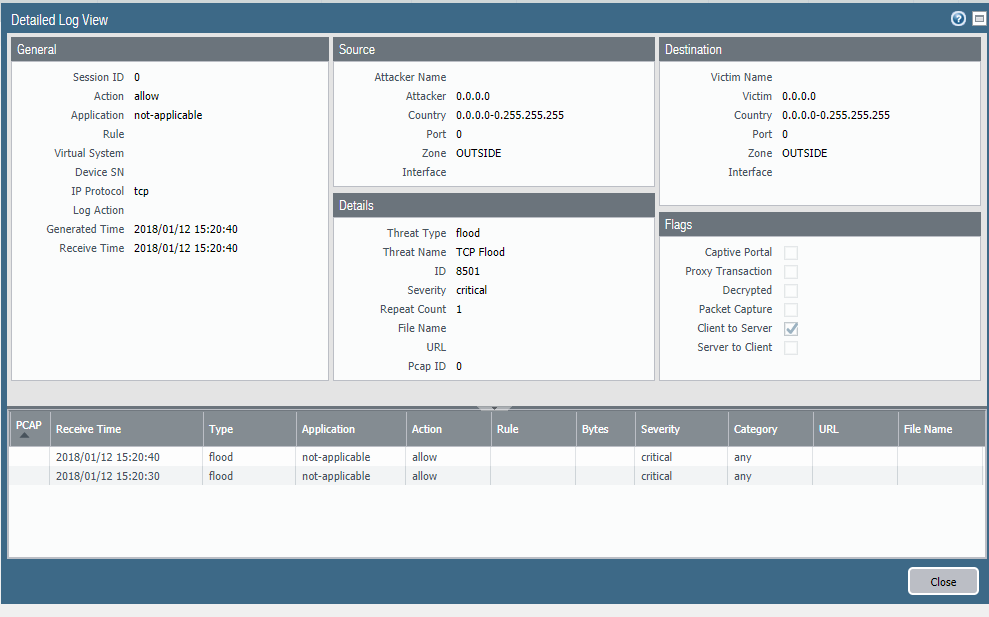
I wouldn't think that zone protection would interfer with the globalprotect VPN but it was failing at the same time I had zone protection applied to the outside/untrust zone. I checked the threat logs and the only alert I saw was for TCP fllood and scan: host sweep. It might be a conincidence but when I turned zone protection off the outside zone the VPN began working again. Any ideas would be appreciated?
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-17-2018 05:46 AM
If you are seeing TCP Flood and host sweeps showing up in your threat log the zone protection is likely the issue. What do you have your alert, activate, and maximum values to?
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-17-2018 05:51 AM
Reall because the threat log also shows that the TCP flood traffic is allowed and is the VPN traffice TCP or IPSec? Here is one of the logs for the TCP flood traffic. I will send my setting in the next post
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-17-2018 06:15 AM
While simply hitting the alarm rate shouldn't do anything to the traffic, your description of the issues seems to imply that something did indead cause VPN issues. We can't say for certain that it's zone protection simply because I can't see the rest of the logs, but if it went away as soon as your removed the ZP profile it's a safe enough bet.
GlobalProtect access is going to be seen the same as an AnyConnect session, they are by default SSL VPNs. The only time IPSec should be used is if you are not using the GlobalProtect Client and you are using a third-party or built-in VPN client to establish connections to the GlobalProtect gateway.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-17-2018 06:18 AM
Unfortunately the only way to know for sure is to try it again LOL. Which I will do at a later date, since classes start today, never a good time to try something new.
I am still playing with DoS trying to figure out what the best way to narrow it down to particular IP addresses and not full zones
- 14204 Views
- 47 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Updating Cortex Agent by MDM in Cortex XDR Discussions
- Cortex XDR FIM in Cortex XDR Discussions
- I'd like to download global protect 6.2.6-838 in General Topics
- MacOSX Tahoe 26.4.1 (25E253) / Global Protect 6.3.3: Network is unreachable in GlobalProtect Discussions
- Global Protect is having issues with newer MACOS version. in Next-Generation Firewall Discussions