- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
ZTP Models can be deployed as a traditional models?
- LIVEcommunity
- Discussions
- General Topics
- ZTP Models can be deployed as a traditional models?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
ZTP Models can be deployed as a traditional models?
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-19-2021
07:37 AM
- last edited on
06-03-2021
07:59 PM
by
![]() icharkashy@palo
icharkashy@palo
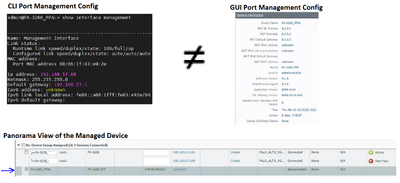
Hello guys, I want to know if someone has seen this behavior with Port Management Configuration on ZTP NGFW Models ... The IP address, Netmask and gateway shows an incorrect value 0.0.0.0 or Unknown, but the CLI shows the correct configuration parameters. We previously performed a "request disable-ztp" besides "Disable Device and Network Template" and "Disable Panorama Policy and Objects" on Panorama Settings. We thought that this behavior is causing problems when we trying to add a PA-3260-ZTP as a managed device on Panorama.
- Labels:
-
NGFW
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-21-2021 03:08 PM
So from th CLI you see that the firewall is configured correctly right and it has full configuration? I also see that you have GUI picture so you can access the managment ip even if the gui shows no IP? I am asking because when I see unknown fo interfaces I do a factory default reset on the firewall but first I save the config snapshot or/and device state (https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000Clkn) and load it again after the reset 🙂
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-22-2021 09:15 AM
Hi Nikolay
Thanks for your reply. Please let me know if you have seen this behavior of "Unknown Mgmt IP info on GUI" when you're deploying ZTP models in a traditional way. If I reset to factory default a ZTP Model, it comes back to the original ZTP state according to the notes in the procedure "Disable the ZTP state machine on the firewall" and I think the issue is related to this ZTP pre-configured template.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-22-2021 09:54 AM - edited 03-22-2021 10:20 AM
We had an issue like that without ZTP deployment but we seen it in the CLI as well so we did factory default reset.
Did you test restarting just the web service or managment server as it seems a GUI issue:
https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000ClaGCAS
https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000POIHCA4
Also you can run Validate Changes to see if the ZTP intoduced a bad config(you may need to make a small change before that to be able to validate)
There is a bug PAN-160870 when deploying the ZTP firewalls in the normal way so you can check it and test the workaround:
Otherwise of that check with the TAC.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-22-2021 12:57 PM
Hello Nikolay, thanks for your all advices , we're going to test those suggestions, until we can check with TAC in a Live Meeting. I'll let you know when we have more clues about the issue with these ZTP models.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-26-2021 12:51 PM
Any news about what is the issue as I am also interested in what it could be 🙂 ?
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-07-2021 01:37 PM
Hello Nikolay
We're still waiting for a fix in the next PAN-OS 9.1 release (9.1.9). Apparently, the WebUI Mgmt "Unknown" Issue is related to bug PAN-156264. This behavior doesn't permit add PAs as a managed devices on Panorama in a traditional way.
We tried the PAN-160870 Workaround to disable ZTP Pre-configuration but it didn't work after reboot the PAs. Using the ZTP plugin to deploy PAs works, but still keeping requiring the ZTP DG and Template configuration to avoid the PAN-160870 issue after finishing the deployment and it does not make much sense to me.
As soon as I have news I'll let you know.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-26-2021 09:33 AM - edited 04-26-2021 09:35 AM
I am having a similar issue. As the ISP doesn't provide any DHCP, in the site I am adding the device to, and I have access to the Management network I tried disabling ZTP and adding the Panorama servers manually, but they went into a weird state, where the management interface was still routing to the network, but they wouldn't send any traffic to the Panorama servers. I could still get on the interface to manage it, but it wouldn't respond to pings from panorama, but would from everything else. resetting to factory default and re-enabling DHCP on the management interface and it would respond.
I also tried removing the ZTP template by disabling the panorama templates and policies, but then it wouldn't commit any changes because of a very unhelpful message:
network is missing 'interface'
I didn't realize ZTP would be Mandatory and such a PITA. I wish I had bought the normal ones.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-30-2021 08:46 AM
Hi Rich
You're right, try to add the ZTP models on Panorama using a traditional way results in a weird "Disconnected" state. Try to remove the ZTP template by disabling the panorama templates and policies(as it says PAN-160870 workaround) causes an Autommit failure after a PA reboot due to "network is missing interface" and some other issues and you will need to do the factory reset to correct that. I figured out the only way to deploy those ZTP models was using the Panorama ZTP Plugin to register and add the PA as a managed device using DHCP via WAN (on eth1/1) and then disable the ztp state (request disable ztp) to be able to reach the PA from mgmt port (being careful to change locally on the PA the "Panorama service route" to mgmt port in the proper moment). Next, from the Panorama and locally on the PA, you should remove the ZTP template and DG from Panorama progressively until you get free the PA of that ZTP configuration.
- 13216 Views
- 8 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Exfiltration Shield - Prevent data exfiltration via DNS relay attack in Advanced Threat Prevention Discussions
- Json Error when sending POST request to https://api.prismacloud.io/search/config in Cortex Cloud Discussions
- Understanding Panorama Log Ingenstion & Sizing in General Topics
- Migration of Palo Alto VM series from one host to another in General Topics