Incident classification considering multiple fields
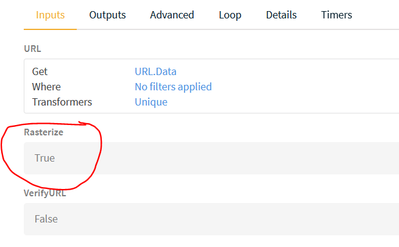
How can I classify an incident while taking multiple fields into consideration?Let's say I have a list of numbers. Whenever an incident is registered I would like to check whether the value of Field A is in that list, if Yes, then classify by Field A, if Not then classify by other Field B.